L
778 posts

















Big news: We are back!



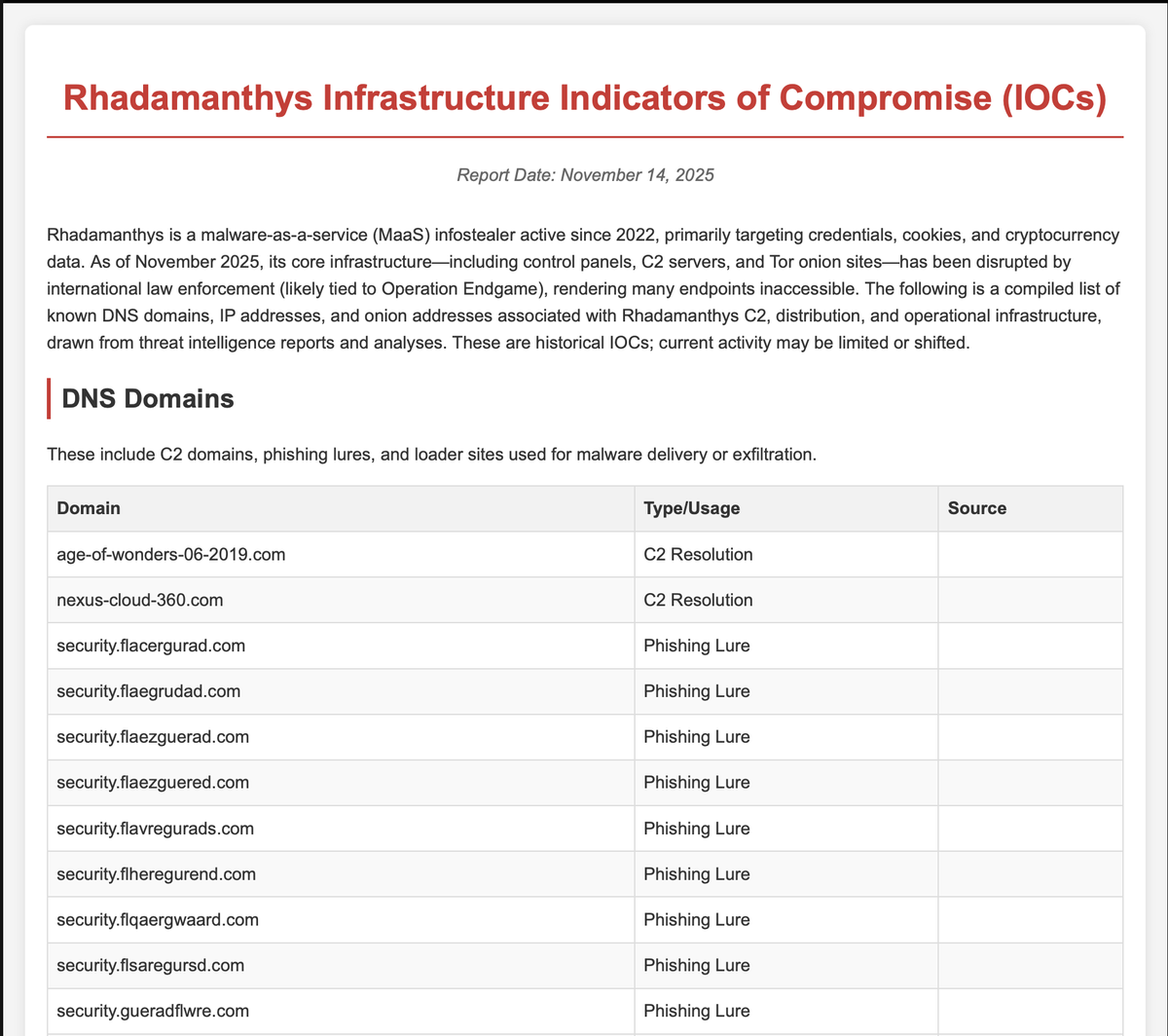
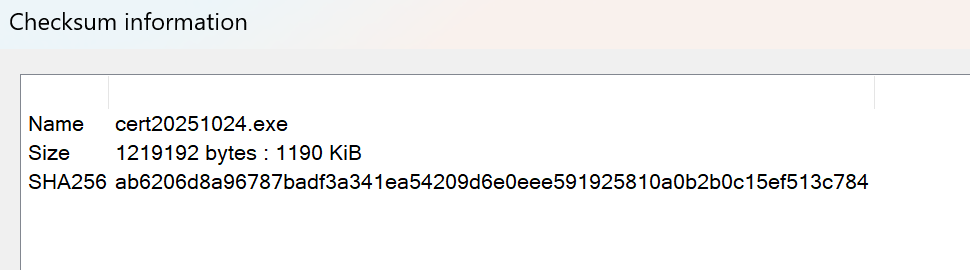
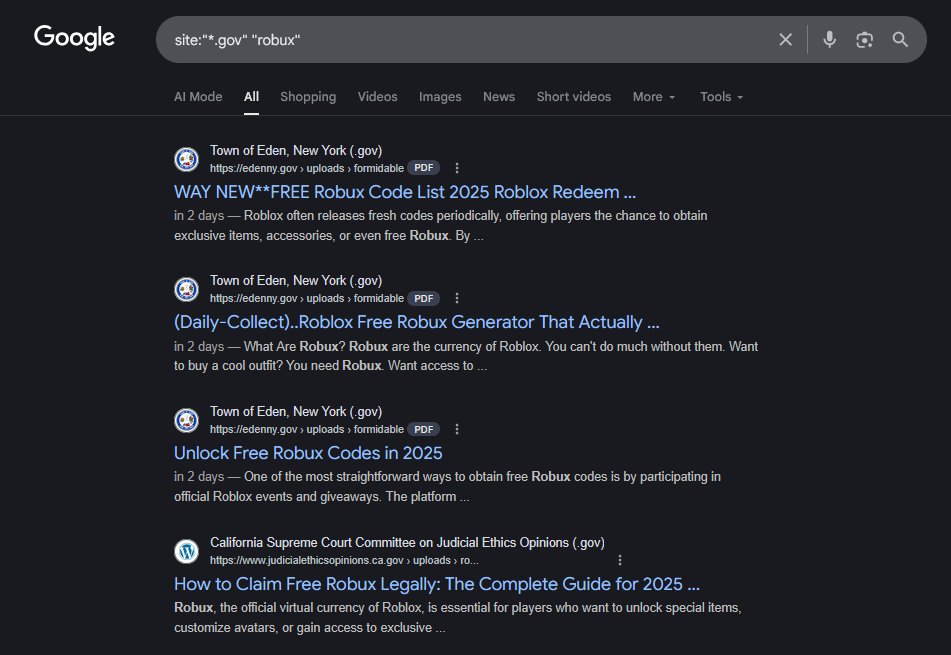
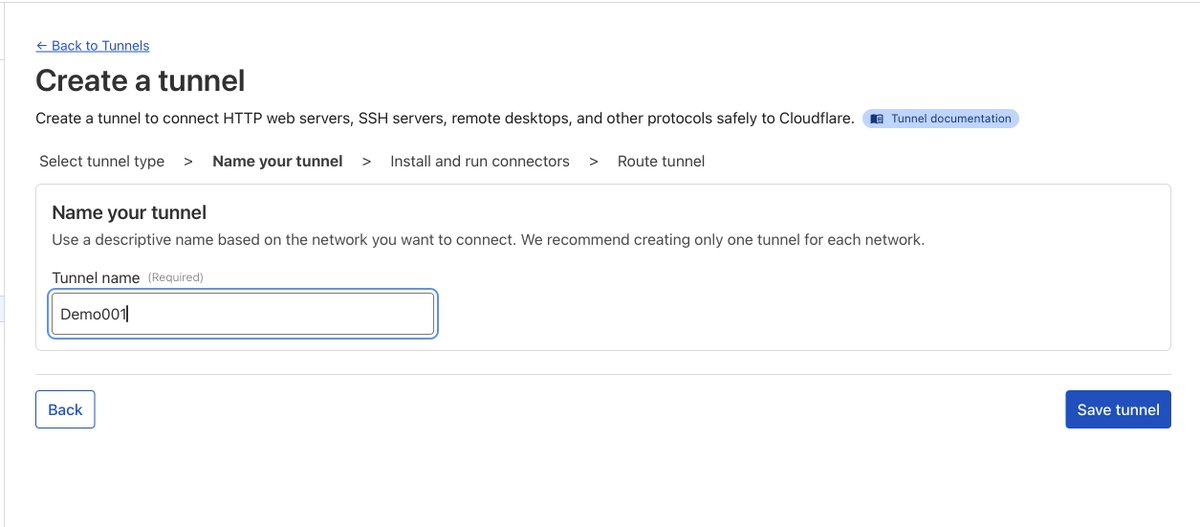
Mr. Manley was kind enough to share the DMCA takedown notice he received. He indicated in the attached post that he believed it to be malicious (a scam of some sort) and his assumptions were correct. I only briefly skimmed the malware he sent me because I'm very sleepy, but from a high level overview this "DMCA takedown" is very silly. The DMCA takedown website generates a "password" to review the DMCA takedown report. This is made to masquerade and/or mimic legitimate legal documents which may password protect PDF files which may contain sensitive data. When you click download report, the DMCA report is a .exe file which pulls from a disposable GitHub profile. The .exe file when executed has a standard GUI. It opens, it sits there, it looks pretty. The .exe stops execution until you provide the "password" which was generated from the DMCA takedown website. I have not performed testing to determine if the "password" is uniquely generated each time or if it's static. I'm going to assume it's static because that's the easier option and they're probably lazy. Anyway, until that "password" is provided nothing happens. The binary itself has some cool stuff. While I only briefly skimmed over it, it is interesting that it was compiled using Visual Studio and the Manifest file is written in Cyrillic. That is totally normal (no, it's not). While not always hard evidence, the Manifest file being in Cyrillic is an indicator that the authors are probably from Russia, Ukraine, Kazakhstan, or some other country in the Commonwealth of Independent States (ex-Soviet). In other words, whoever wrote this program is running Windows with the Russian language pack set to default (their computer is in Russian). Cool. The binary also invokes UAC when it runs (wants to run as Admin). All of this is designed to trick the user who has executed the file into believing this is a legitimate DMCA takedown request and this .exe will contain sensitive legal information. When you actually enter the "password" which is provided, the DMCA takedown .exe does some interesting things which are totally normal (no, it's not) For example: - Invokes Powershell - Excludes a bunch of .exe files from Windows Defender - Downloads some other .exe files This is where I stopped because it's bed time. Some of the files downloaded look like "hack" tools. One of them is named "Index.exe". But I'm not sure. I'll keep poking it with a stick when I wake up. I'm curious what this actually delivers. I'm impressed by how far and targeted this is to YouTubers (assuming it has been sent to other YouTubers). The amount of tailoring is probably 40, maybe 50, minutes of work with a fake domain name, shit web hosting, and ChatGPT slop website. This is far more effort than what you typically see with shit slop malware campaigns. I'm curious if it delivers an existing information stealer payload, a custom made information stealer payload, ... does it deploy ransomware? I don't know! Find out next time on Dragon Ball Z