
Ngo Wei Lin
115 posts

Ngo Wei Lin
@Creastery
www = web web web · Staff Security Engineer @praetorianlabs · Previously 🌐 Security Researcher @starlabs_sg · Plays CTFs with HATS SG. Opinions are my own.
Singapore 가입일 Mayıs 2012
534 팔로잉1.1K 팔로워
고정된 트윗

Check out my write-up on a seemingly harmless and limited send() in GitHub (CVE-2024-0200) and how it could be used to obtain environment variables from a production container and to achieve remote code execution in GitHub Enterprise Server:
starlabs.sg/blog/2024/04-s…
English

@ttaka_66 @DennisPacewicz @rubykaigi @GitHubSecurity Hi @ttaka_66, thanks for enjoying the talk! The slides/resources are available at gh.io/rubykaigi-2025.
English

@Creastery @DennisPacewicz @rubykaigi @GitHubSecurity Thank you for sharing your very interesting story with us!
Do you plan to share this slide with us?
English

Happy to announce that I'll be speaking alongside @DennisPacewicz at @rubykaigi next week!
We'll be sharing some secret stories on how I gained access to production GitHub credentials using CVE-2024-0200 as well as @GitHubSecurity's remediation efforts.
rubykaigi.org/2025/presentat…
English
Ngo Wei Lin 리트윗함

I just published a new blog post sharing an improved Deserialization Gadget Chain for Ruby!
It builds on the work of others, including Leonardo Giovanni, Peter Stöckli @GHSecurityLab and @wcbowling
nastystereo.com/security/ruby-…

English
Ngo Wei Lin 리트윗함

Thrilled to release my latest research on Apache HTTP Server, revealing several architectural issues! blog.orange.tw/2024/08/confus…
Highlights include:
⚡ Escaping from DocumentRoot to System Root
⚡ Bypassing built-in ACL/Auth with just a '?'
⚡ Turning XSS into RCE with legacy code from 1996
English
Ngo Wei Lin 리트윗함

🚨 New Blog Alert! 🚨
Can an attacker execute commands by sending JSON? Learn how unsafe deserialization vulnerabilities in Ruby can be exploited and how they can be detected with CodeQL.
🔗 Read the full post: github.blog/2024-06-20-exe…
Stay safe and code responsibly! 🛡️💻
English
Ngo Wei Lin 리트윗함

My colleague @hash_kitten and I discovered a full-read SSRF vulnerability in Next.js (CVE-2024-34351). We published our research today on @assetnote's blog: assetnote.io/resources/rese…. Thank you to the Vercel team for a smooth disclosure process.

English
Ngo Wei Lin 리트윗함

Here is my deep-dive post on #github Actions cache poisoning. This is a powerful build pipeline lateral movement and privilege escalation technique and I used it to earn several thousand💰in #bugbounty rewards.
adnanthekhan.com/2024/05/06/the…
English
Ngo Wei Lin 리트윗함

Send()-ing Myself Belated Christmas Gifts - GitHub's Environment Variables & GHES Shell
starlabs.sg/blog/2024/04-s…
Read about how one of our talented researchers, @Creastery , found it, exploited it and reported it in a fast and professional manner:
English

Huge thanks to @GitHubSecurity for coordinating, investigating and fixing!
English

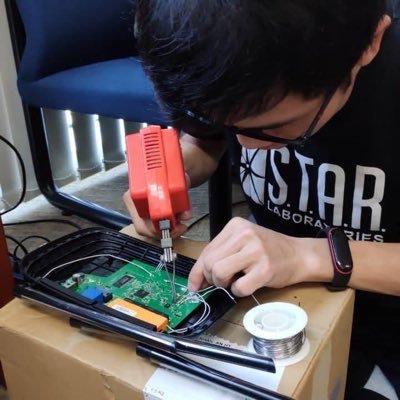
Check out my write-up on a seemingly harmless and limited send() in GitHub (CVE-2024-0200) and how it could be used to obtain environment variables from a production container and to achieve remote code execution in GitHub Enterprise Server:
starlabs.sg/blog/2024/04-s…
English
Ngo Wei Lin 리트윗함

Earlier this year I found a pretty cool vuln, an arbitrary file write in GitLab.
Here’s the details gitlab-com.gitlab.io/gl-security/se…
English
Ngo Wei Lin 리트윗함

Route to Safety: Navigating Router Pitfalls is the swansong from @daniellimws
starlabs.sg/blog/2024/rout…
We hope everyone enjoyed his informative post and wish him all the best in his future endeavours.
English
Ngo Wei Lin 리트윗함
Off-by-One 2024 Conference CFP is now opened! Be part of a historical event and shape the future of offensive security in this region.
Submission and speaker benefits offbyone.sg/cfp/
If you like to talk to us, drop us a line at info@offbyone.sg

English
Just want to announce that I’m officially a part of @dfsec_com today!
English

@adnanthekhan Thanks! Yep, code review. A very unexpected bug with a wild story to share at end April!
English

@Creastery What a cool find! Did you discover it by REing GHES? That’s one heck of a codebase.
Can’t wait for a write up!
English

@adnanthekhan @infernosec @GitHubSecurity Seconded on fixing this insecure default config -- I've already tried pushing for this multiple times but to no avail.
English

@infernosec @PyTorch @GitHubSecurity @infernosec my gut feeling is that there is some messy code between the ruby side of GitHub and the .NET part of Actions that makes such a change quite tricky at GitHub’s scale. Seems like a no-brainer otherwise.
English

This supply chain attack on @PyTorch shows an insecure use of custom/self-hosted github runners and insecure default config ("Require approval for first-time contributors"; anyone can submit a typo fix) gone wrong together. @GitHubSecurity - have you considered changing default to "Require approval for all outside collaborators" for custom runner usecases? - johnstawinski.com/2024/01/11/pla…
English

@joernchen Hey Joern, the current coordinated disclosure date is set at late April 2024. Hope to share more details and insights then!
English

This is one of the most insane bugs I've discovered, but it all happened at a really inopportune time. 😥
Shoutout to all the Hubbers who got involved and had been working tirelessly on this since the Christmas/New Year period! 🙏
GitHub Security@GitHubSecurity
We received a bug bounty report of a vulnerability which, if exploited, allowed access to credentials within a production container. We have patched GitHub.com and rotated all affected credentials, and patches for GHES are available today. github.blog/2024-01-16-rot…
English

@albinowax There is still one more duplicate entry for "Compromising F5 BIGIP with Request Smuggling", but other than that, I think you got them all.
English

We've updated this post with another ~50 nominations! Many thanks, keep them coming!
twitter.com/PortSwiggerRes…
PortSwigger Research@PortSwiggerRes
Nominations are now open for the top 10 new web hacking techniques of 2023! Check out the nominations so far, and make your own here -> portswigger.net/research/top-1…
English
