estrellas
548 posts


estrellas
@CryptDeriveKey
Reverse engineer mostly interested in SAT/SMT solvers, Program Analysis, and Obfuscation. Views are my own.
가입일 Mart 2020
847 팔로잉363 팔로워

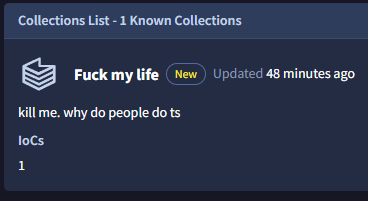
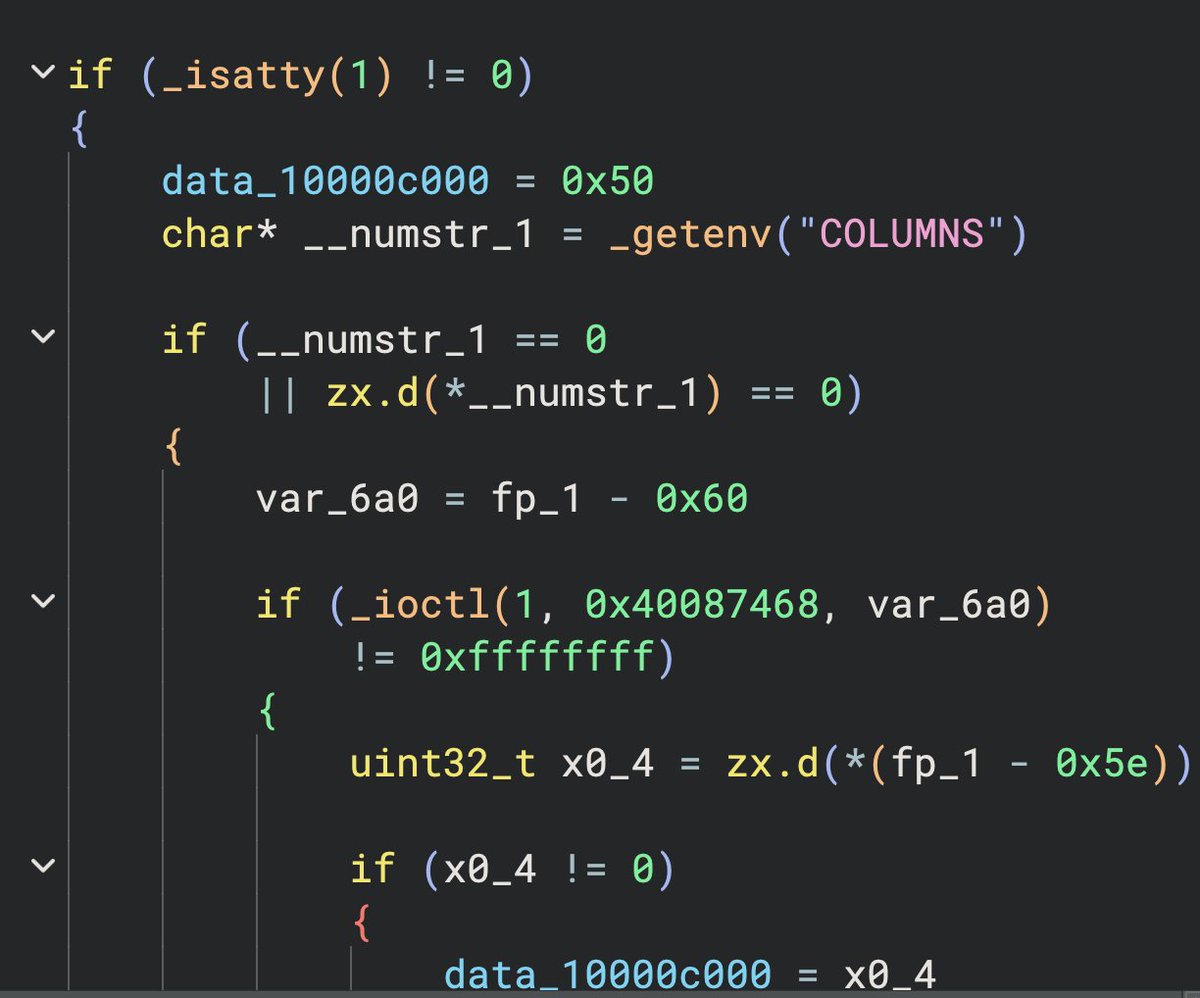
Let's now take a look at the .bat file.
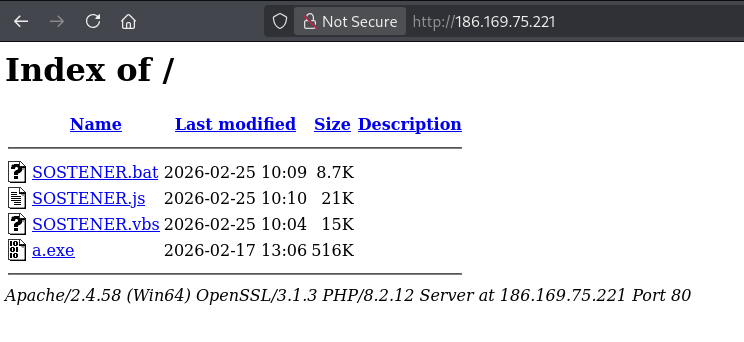
#malware
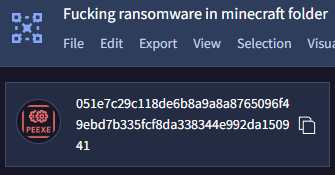
sha256:dbe95eb55c806cad0b0914da8a5003cb464e23a4c8c8289c97d514be76823f24
bazaar.abuse.ch/sample/dbe95eb…
This uses a kind of set/goto obfuscation. In the end, a PowerShell script comes out of it.
English

@0x6D6172636F Is it a publicly available podcast? Would definitely take a listen.
English

@belabs_james Appreciate the feedback! Do you have any resources on doing so? I've also been thinking about implementing value tracking for tail call detection purposes.
English

@CryptDeriveKey Neat. Careful with that ‘is_stack_access’ function though. That segment is not useful on x64, and certainly does not indicate stack access. You’ll need real value tracking across the whole cfg to implement a function like that.
English

Lately I've been working in my very own binary lifter... As part of the documentation process, I decided to write a few words about my implementation of static recovery of a given function's control flow graph. Hope you enjoy it!
deobfuscation.club/blog/on-static…
English

@netspooky Pyarmor's BCC mode transpiles python to C, producing an ELF afterwards (even for Windows applications). The ELF can also be a wrapper around GNU Lightning (JIT assembler) if certain options are marked in the obfuscation process
English

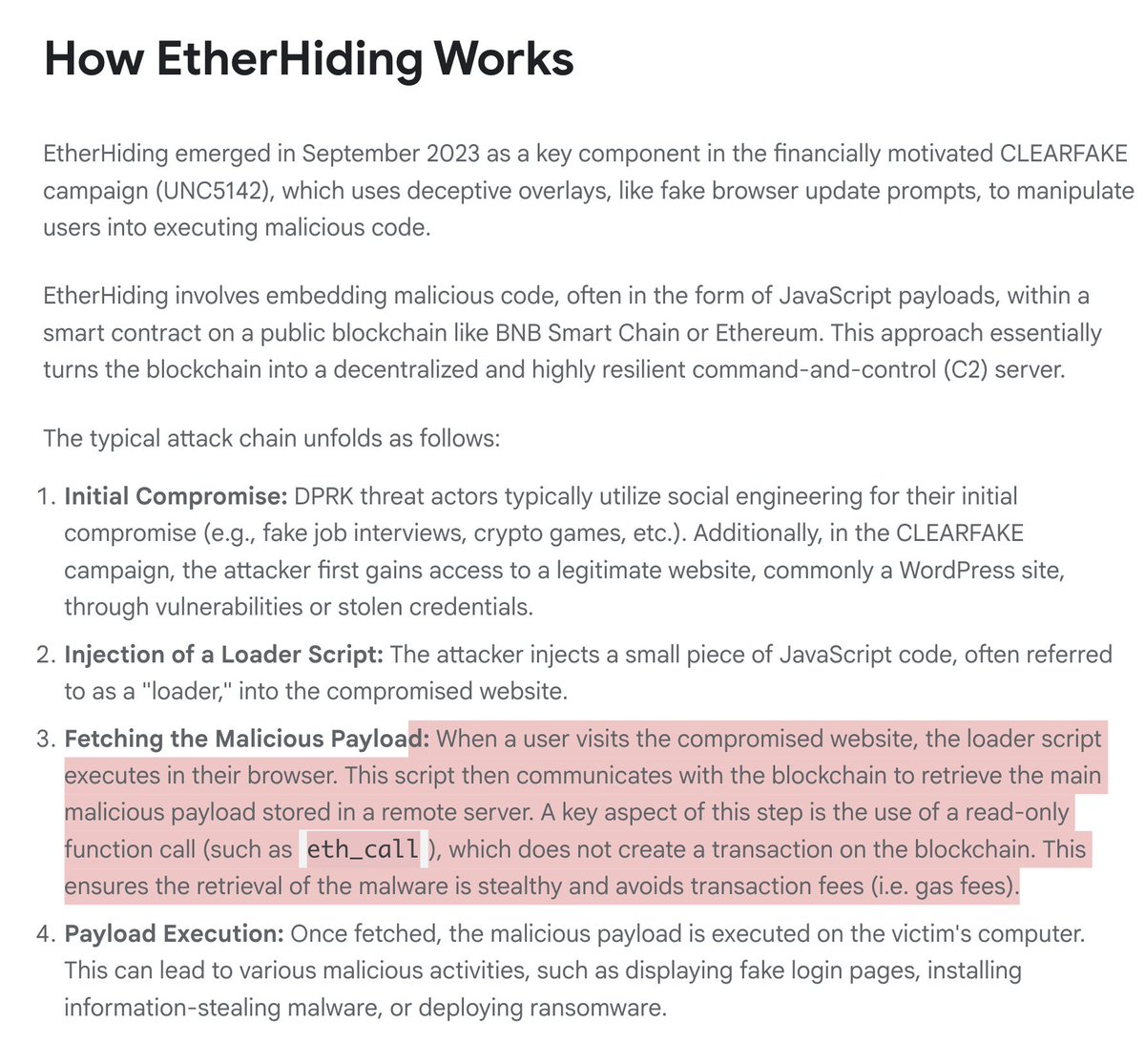
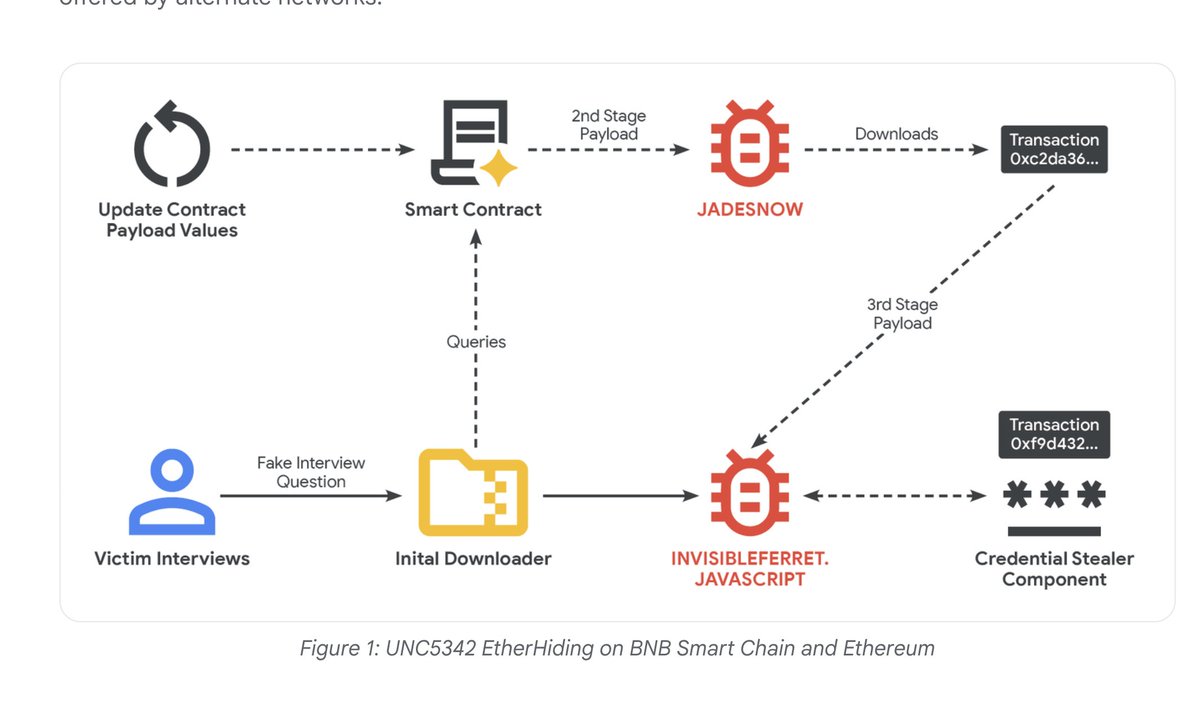
NEW: 🇰🇵DPRK has begun hiding malware on blockchain.
Result, decentralized, immutable malware.
Nearly impossible to remove.
Research by @Mandiant

English
estrellas 리트윗함

Additional info on the Fancy Bear kit being reported on. Cheers to @Laughing_Mantis for writing backdoors so good that APTs plagiarize it.
kroll.com/en/publication…
English

My latest analysis of #XWORM's new delivery method just got published! You can read it at:
kroll.com/en/publication…
English

@vector35 @RussianPanda9xx Mostly these. They are: Search options (text, byte pattern, imm), Segments view, Graphs editor (zoom, fit to window, proximity browser), Graphs view (XREFs, Function calls), and "Windows management" (Imports, Exports, Strings)

English

@CryptDeriveKey @RussianPanda9xx Which icons in the toolbar do you use most often? Have you tried using the command-palette as an alternative?
Variable naming is good feedback -- definitely something we can change to make the transition easier.
English


@vector35 @RussianPanda9xx I am honestly not a big fan of the r64_N syntax for variables, the lack of icons for functionalities, as well as not having brackets😅... But I do appreciate being able to go through many different IL's, and IL forms
English

@CryptDeriveKey @RussianPanda9xx Are there features you find yourself missing from the UI in BN? Or workflows you haven't been able to recreate?
English