

Defimon Alerts
478 posts


@DefimonAlerts
Real-time security alerts for DeFi ⚠️ Alerts: https://t.co/p5MHTe5S0Q 💎 Signals: https://t.co/70vuWap7y0









💬 Onchain Message: We have identified you and are working with the U.S. Department of Homeland Security - Cyber 1 Darkweb & Cryptocurrency unit. Return 70% of stolen funds to 0x45e2663E0FEE4ABDf1EA7943eC527d6101bE5E34 within 48 hours and keep 30% as a whitehat bounty. No further action will be taken. Ignore this and we will pursue all legal avenues. - Keom Protocol Team etherscan.io/tx/0x8501e3631…


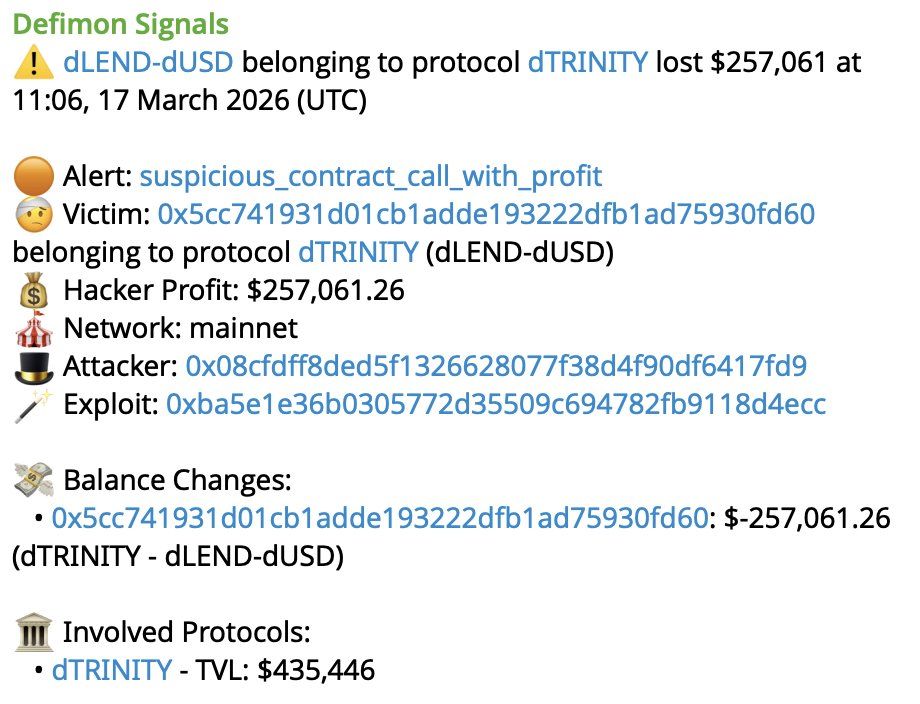
🚨 @dTRINITY_DeFi has been exploited for $257K The attacker flash-loaned USDC from Morpho, deposited ~$772 USDC which was valued as ~$4.8M collateral due to the inflated index, then borrowed 257K dUSD against this phantom collateral. Remaining USDC in the aToken was drained via 127 repeated deposit/withdraw cycles through a helper contract. TX: etherscan.io/tx/0xbec4c8ae1… Victim: etherscan.io/address/0x5cc7… Pool: etherscan.io/address/0x6598…





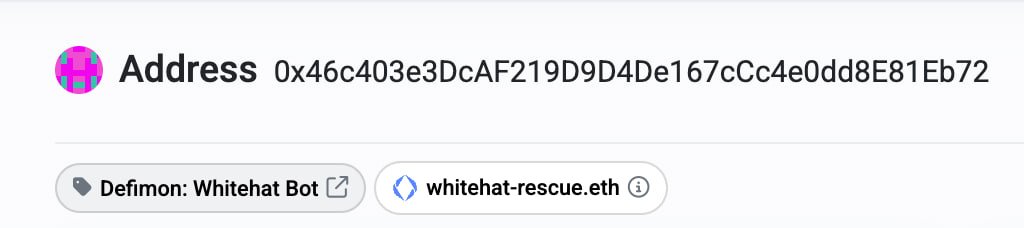
Onchain monitoring and incident response is crucial for DeFi Since 2022 we have been working on defimon.xyz to detect DeFi exploits by analyzing transactions in real-time. There is a constant stream of DeFi exploits that are barely noticed. You can get access to these instant alerts by subscribing to the exploits feed for just 50$/mo. For protocol teams we offer a Websocket subscription to act on the alerts automatically. Native Telegram subscription: t.me/+m9BMRKlMuW5iM… Tribute mini-app: t.me/tribute/app?st… Contact: t.me/DecurityHQ







