고정된 트윗

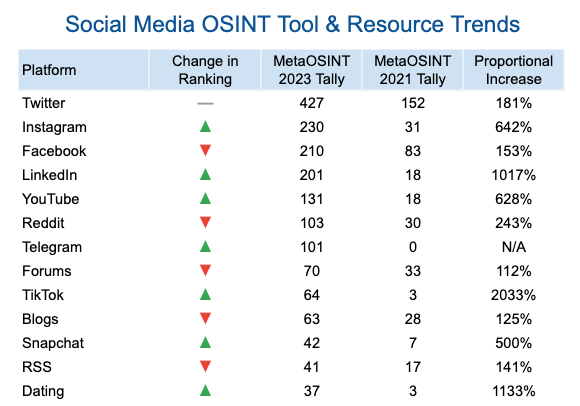
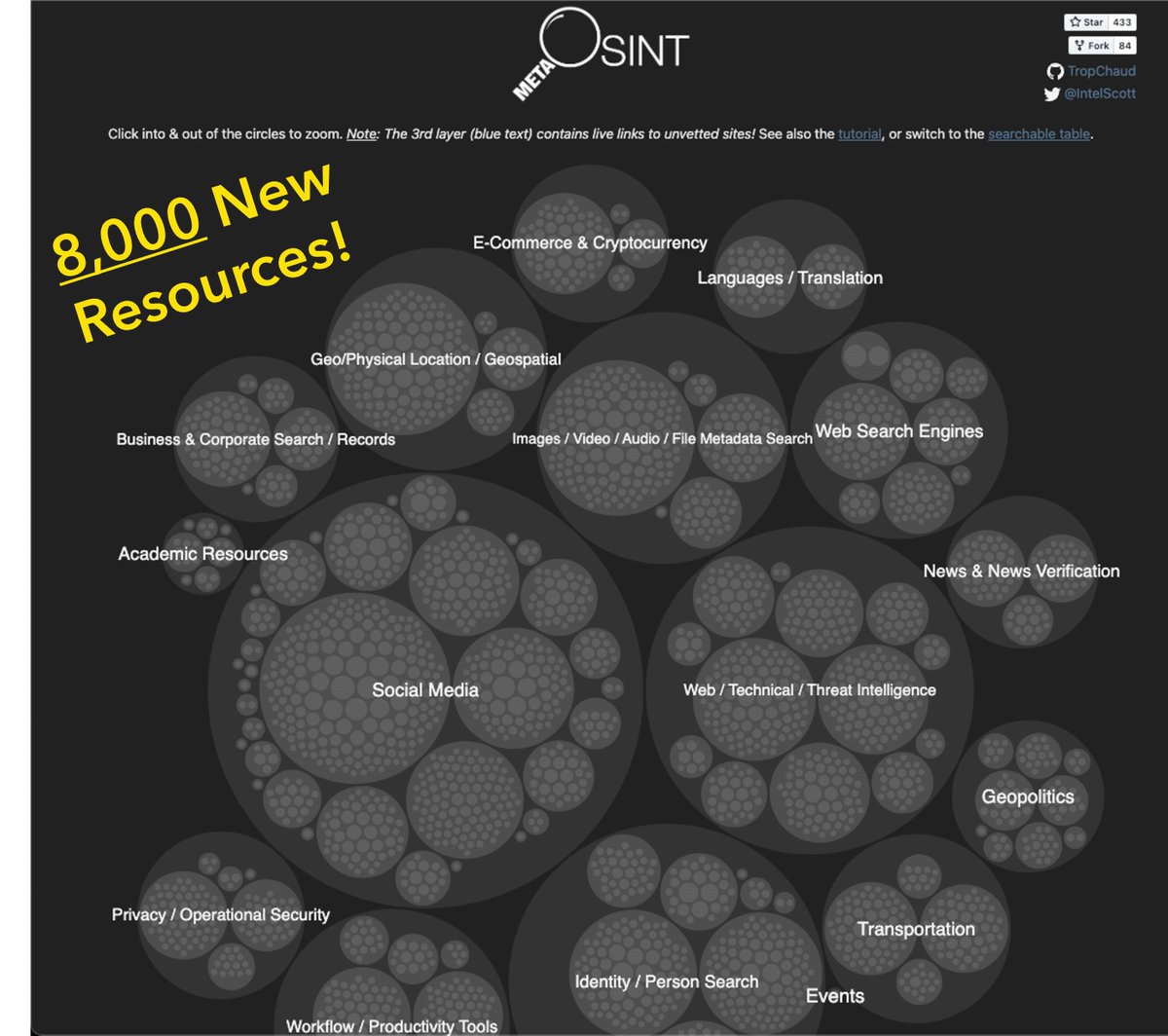
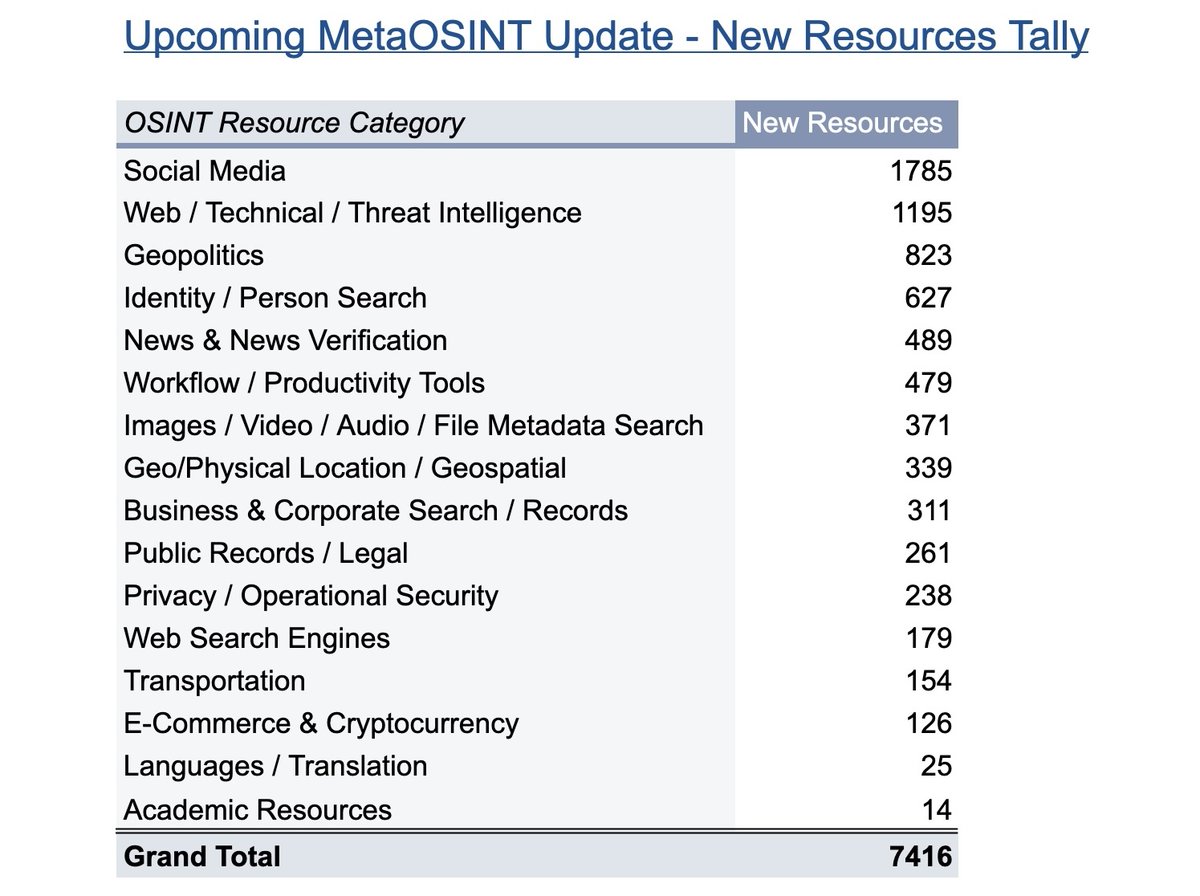
On its 1st anniversary, excited to announce the re-launch of MetaOSINT, the #OSINT tool & resource aggregator! v2 contains 900 new resources (5,700+ total) wrapped in an improved UI. The best news? A method for ongoing updates, so stay tuned for more ~weekly additions!
GIF
English