Seppe
3.8K posts


Wist je dat de Vlaamse regering het brillenmerk Odette Lunettes runt met belastinggeld? Wie het de taak vindt van de overheid om een brillenmerk uit te baten met belastinggeld die is behoorlijk van het padje af. staatsbladmonitor.be/bedrijfsfiche.…




🇧🇪 400K Belgium Bol.com Dataset Allegedly for Sale A dark web post claims the sale of a 400,000-record dataset linked to Bol.com users, one of the largest e-commerce platforms in Belgium and the Netherlands. 📊 Key Claims: • Dataset size: ~400K users • Data types allegedly include: Full names Email addresses Phone numbers Dates of birth, gender, nationality ID numbers (high risk if true) Full address details Additional shipping & order data: Order history, delivery status Tracking numbers Payment/shipping metadata Sample data shared via paste sites Seller offering escrow-based transaction 🧠 Threat Intelligence Insight: • This is rich, structured e-commerce data, which is highly valuable for: Account takeover campaigns Targeted phishing (order-themed lures) Identity fraud (if ID numbers confirmed) Presence of order + shipping data increases risk: Enables highly convincing scams (“your package”, “delivery issue”) Could originate from: Third-party vendor / logistics partner Credential stuffing + aggregation Or direct breach (less certain) ⚠️ Assessment: • Medium credibility: Data structure looks realistic But no confirmation of direct breach vs. aggregation Sample links suggest: At least partial dataset exists ⚠️ Risk Implications: • Large-scale phishing campaigns targeting customers • Identity theft and fraud • Increased success rate of social engineering attacks • Potential regulatory exposure (GDPR implications) 📊 Status: Unverified — but high exploitation potential due to data richness ⸻ 💬 When attackers have both identity and order history, phishing becomes personalization at scale. #CyberSecurity #DataBreach #Ecommerce #Bolcom #ThreatIntel #DarkWeb #DDW

🇧🇪 400K Belgium Bol.com Dataset Allegedly for Sale A dark web post claims the sale of a 400,000-record dataset linked to Bol.com users, one of the largest e-commerce platforms in Belgium and the Netherlands. 📊 Key Claims: • Dataset size: ~400K users • Data types allegedly include: Full names Email addresses Phone numbers Dates of birth, gender, nationality ID numbers (high risk if true) Full address details Additional shipping & order data: Order history, delivery status Tracking numbers Payment/shipping metadata Sample data shared via paste sites Seller offering escrow-based transaction 🧠 Threat Intelligence Insight: • This is rich, structured e-commerce data, which is highly valuable for: Account takeover campaigns Targeted phishing (order-themed lures) Identity fraud (if ID numbers confirmed) Presence of order + shipping data increases risk: Enables highly convincing scams (“your package”, “delivery issue”) Could originate from: Third-party vendor / logistics partner Credential stuffing + aggregation Or direct breach (less certain) ⚠️ Assessment: • Medium credibility: Data structure looks realistic But no confirmation of direct breach vs. aggregation Sample links suggest: At least partial dataset exists ⚠️ Risk Implications: • Large-scale phishing campaigns targeting customers • Identity theft and fraud • Increased success rate of social engineering attacks • Potential regulatory exposure (GDPR implications) 📊 Status: Unverified — but high exploitation potential due to data richness ⸻ 💬 When attackers have both identity and order history, phishing becomes personalization at scale. #CyberSecurity #DataBreach #Ecommerce #Bolcom #ThreatIntel #DarkWeb #DDW

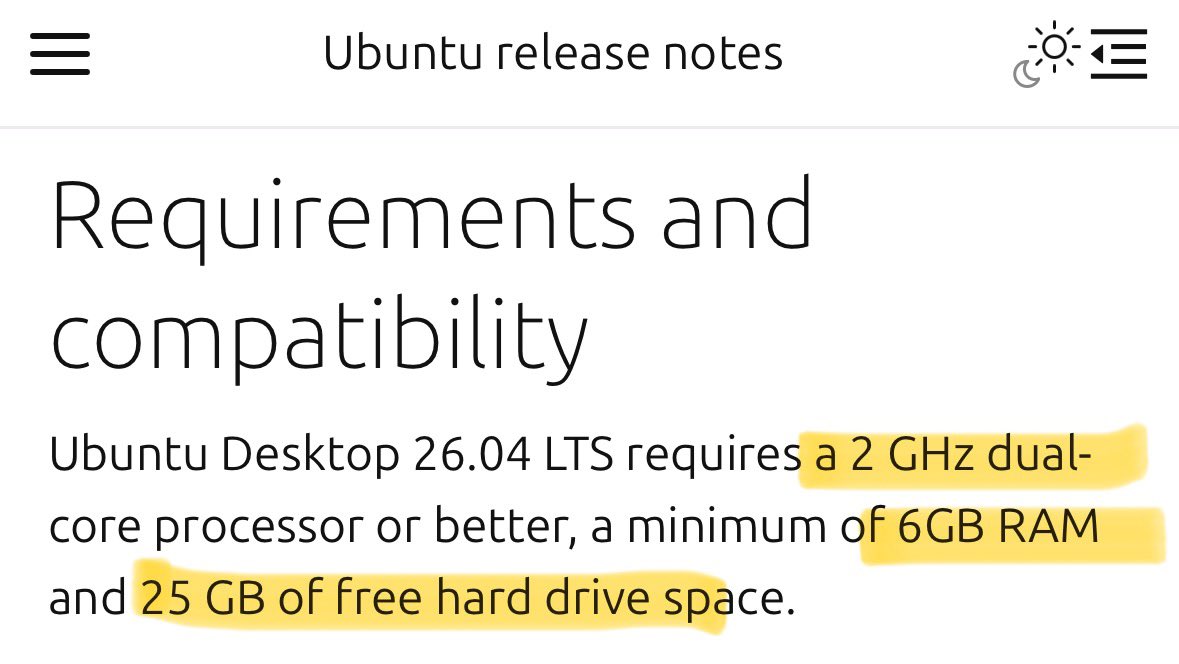
.@vonderleyen "The European #AgeVerification app is technically ready. It respects the highest privacy standards in the world. It's open-source, so anyone can check the code..." I did. It didn't take long to find what looks like a serious #privacy issue. The app goes to great lengths to protect the AV data AFTER collection (is_over_18: true is AES-GCM'd); it does so pretty well. But, the source image used to collect that data is written to disk without encryption and not deleted correctly. For NFC biometric data: It pulls DG2 and writes a lossless PNG to the filesystem. It's only deleted on success. If it fails for any reason (user clicks back, scan fails & retries, app crashes etc), the full biometric image remains on the device in cache. This is protected with CE keys at the Android level, but the app makes no attempt to encrypt/protect them. For selfie pictures: Different scenario. These images are written to external storage in lossless PNG format, but they're never deleted. Not a cache... long-term storage. These are protected with DE keys at the Android level, but again, the app makes no attempt to encrypt/protect them. This is akin to taking a picture of your passport/government ID using the camera app and keeping it just in case. You can encrypt data taken from it until you're blue in the face... leaving the original image on disk is crazy & unnecessary. From a #GDPR standpoint: Biometric data collected is special category data. If there's no lawful basis to retain it after processing, that's potentially a material breach. youtube.com/watch?v=4VRRri…