고정된 트윗
h1p 🇨🇴
9.1K posts


h1p 🇨🇴
@hipdead010
scripter ►infosec ► cybersecurity all the time ►bugbounty programs ►Ethical Hacking ►Security Researcher►Threat Intelligence
가입일 Nisan 2011
744 팔로잉6.5K 팔로워
h1p 🇨🇴 리트윗함
h1p 🇨🇴 리트윗함

🛑 WARNING: Bitwarden CLI was compromised in a supply chain attack.
@bitwarden/cli@2026.4.0 included malicious code after attackers hijacked GitHub Actions, stole secrets, and pushed a tampered version to npm.
🔗 Learn how the attack worked → thehackernews.com/2026/04/bitwar…
English
h1p 🇨🇴 리트윗함

🔴🇨🇴El grupo de ransomware The Gentlemen publica:
A la Corporación para el Desarrollo Sostenible del Archipiélago de San Andrés, Providencia y Santa Catalina (CORALINA) @coralina_sai en su sitio DarkWeb.
🔗coralina.gov.co
#Colombia #DarkWeb #Gentlemen #ciberataque #ciberseguridad #ransomware #government
Español
h1p 🇨🇴 리트윗함

I reviewed a JS file several times. Found nothing.
Fed it to Claude Desktop (free version). It mapped hidden endpoints in seconds.
That led me to:
• PII of high-profile users
• Fund redirection to any bank account
• Balance manipulation
Check it ↓
medium.com/p/how-i-found-…
English
h1p 🇨🇴 리트윗함

🇨🇴 NEW: Financial Data from Colombian Money Transfer Service Allegedly for Sale
A threat actor is offering data linked to Banco Unión (Giros y Finanzas), a Colombian financial service provider and authorized Western Union agent.
According to the listing:
• 1M+ customer records
• Data tied to money transfer operations
• Associated with EmergiaCC datasets
The post also references collaboration with another group, suggesting ongoing coordinated data sales activity.
⚠️ Sensitive data and access points are not shared here.
At this stage:
– Claim status: Unverified
– Impact (if confirmed): High risk to financial customers
Potential risks include:
• Financial fraud & account abuse
• Identity theft
• Targeted social engineering leveraging transaction data
Notably, this is the second Colombian dataset linked to the same actors in a short timeframe — indicating possible systematic targeting or access reuse.
DDW is monitoring for validation and attribution.
#DataBreach #CyberThreat #DarkWeb #Infosec #CTI #CyberSecurity

English
h1p 🇨🇴 리트윗함

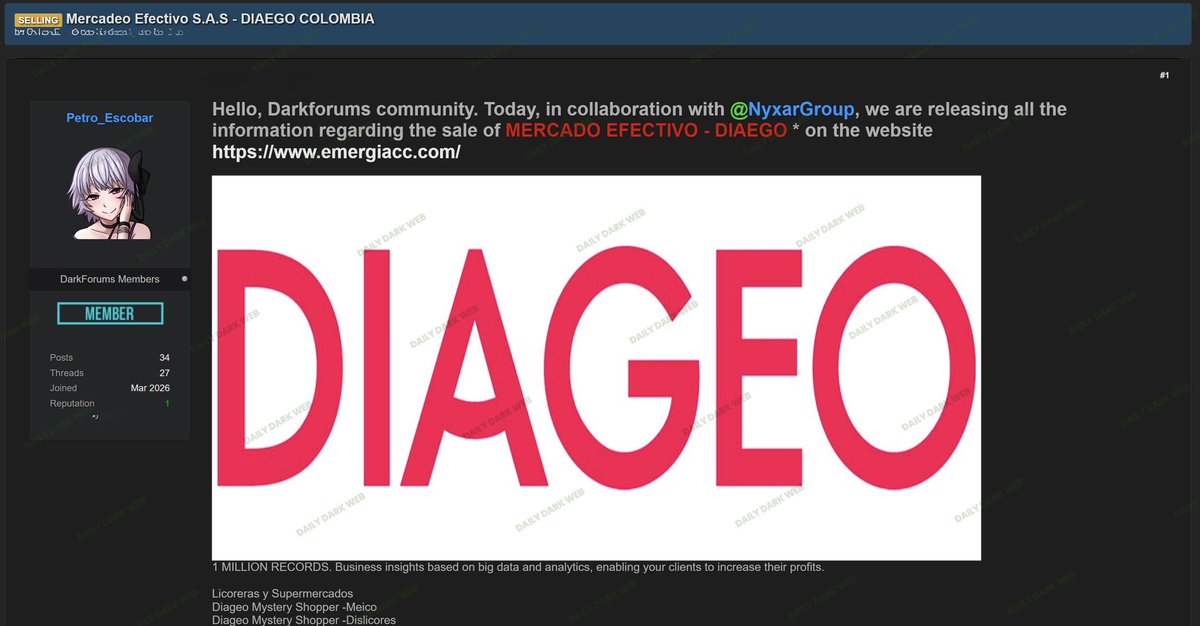
🇨🇴 NEW: 1M Records from Colombian Firm Allegedly Listed for Sale
A threat actor is offering data linked to Mercadeo Efectivo (DIAEGO Colombia), a company focused on business intelligence and analytics.
According to the listing:
• ~1 million records exposed
• Data tied to retail & commercial analytics
• Includes insights used by supermarkets and liquor retailers
The post also references collaboration with another group, suggesting possible shared data brokerage activity.
⚠️ Raw data and access points are not shared here due to sensitivity.
At this stage:
– Claim status: Unverified
– Dataset type: Commercial intelligence / consumer data
If validated, risks may include:
• Targeted marketing abuse
• Data resale in underground markets
• Profiling and social engineering campaigns
DDW is monitoring for confirmation and potential attribution.
#DataBreach #DarkWeb #CyberThreat #Infosec #CTI #CyberSecurity
English
h1p 🇨🇴 리트윗함

🚨 CYBERSECURITY ALERT: WAVE OF BREACHES TARGETING FINANCIAL AND COMMERCIAL ENTITIES IN COLOMBIA 🇨🇴⚠️
Coordinated offensive activity has been detected targeting the financial and commercial sectors in Colombia. The threat actor "Petro_Escobar" has claimed responsibility for exfiltrating data from two major entities, which were allegedly compromised through the infrastructure of their debt collection and portfolio management partners.
🏢 Multipagas and Reval (Case #5244): * Sector: Industry / Financial Services (Collection and money transfer network).
Impact: High risk of exposure of transactional data and user identification information for individuals utilizing these mass payment points.
🏍️ SERVIMOTOS YAMAHA -- EmergiaCC Conalcreditos (Case #5243):
Sector: Finance / Commercial.
Impact: The leak appears to stem from a breach within the debt collection supply chain (EmergiaCC / Conalcreditos). The compromised data could include credit histories, customer contact details, and specific details regarding vehicle financing portfolios.
👤 Threat Actor: Petro_Escobar.
📂 Nature of Data: Personally Identifiable Information (PII), customer databases, and portfolio management records.
📅 Publication Date: April 22, 2026.
🛡️ Immediate Response Recommendations
🔒 Vendor Audits: Colombian companies utilizing outsourced services for debt collection or customer support must demand immediate security audits from the vendors identified in these breaches.
👁️ Phishing Monitoring: Users of these services are advised to remain vigilant regarding any suspicious communications referencing outstanding debts or pending administrative procedures.
Intelligence Monitor: analyzer.vecert.io
🛡️ "Information obtained through the monitoring of data marketplaces and threat intelligence reports. VECERT issues this alert to facilitate the proactive mitigation of risks for both corporations and citizens."
#CyberSecurity #Colombia #DataBreach #Multipagas #YamahaColombia #PetroEscobar #VECERT #Cybersecurity #InfoSec #Conalcreditos 🇨🇴🛡️⚠️

English
h1p 🇨🇴 리트윗함

‼️🇨🇴 Servimotos Yamaha (servimotosyamaha.com), an authorized Yamaha motorcycle dealer and distributor in Colombia, has allegedly had data from its collections operations put up for sale on a popular cybercrime forum at $100 USD.
⠀
‣ Threat Actor: Petro_Escobar (in collaboration with NyxarGroup)
‣ Category: Data Breach / Data Sale
‣ Victim: Servimotos Yamaha Colombia
‣ Industry: Retail / Motorcycles / Debt Collection
⠀
Servimotos Yamaha operates as an authorized Yamaha dealer offering new motorcycle sales, genuine spare parts, accessories, and specialized technical service. The leaked data appears to be drawn from the company's debt collection / financing operations, possibly connected to the previously mentioned EmergiaCC Conalcreditos system. The listing allegedly contains:
⠀
▪️ 1,000,000 records
⠀
Fields in the leak:
⠀
▪️ Número producto (product number)
▪️ Número identificación (Colombian ID)
▪️ Nombre completo (full name)
▪️ Usuario (agent username)
▪️ Hora gestión and Fecha gestión (contact time and date)
▪️ Teléfono, Dirección
▪️ Canal contacto (contact channel)
▪️ Estado contacto, Estado cliente (contact and customer status)
▪️ Guion 1 through 5 (call script responses)
▪️ Fecha acuerdo, Valor acuerdo (agreement date and amount)
▪️ Observación (free text notes)
▪️ Capital libros (book capital / outstanding balance)
▪️ Tipo reparto, Gestión
▪️ Panel Causal de no pago (non-payment reason)
▪️ Fecha perfil, Actividad Económica (profile date, economic activity)
⠀
The sample shows individual customer contact attempts, including named customers, outstanding balances (amounts shown in Colombian pesos, e.g. 700,000 COP), partial payment records, and free text agent notes recording specifics of debtor circumstances. The fields and samples indicate this is a call center / collections dataset rather than a standard customer database, exposing vulnerable debtors being pursued for motorcycle financing payments.


English

@red_darkin Huele a un CVE de esos recientes por ahí que fue explotado y los dueños no se dieron cuenta
Español

@hipdead010
Dark Web Informer@DarkWebInformer
‼️🇨🇴 A threat actor identified as GhostByte is selling "super" admin access to a Colombian companys FortiGate VPN and firewall infrastructure for $700. The compromised environment includes an Active Directory network, and the victim organization reportedly has annual revenue of $49.3 million.
QME
h1p 🇨🇴 리트윗함

🚨 FINANCIAL SECURITY ALERT: MASSIVE DATA EXFILTRATION AT BANCO UNIÓN (COLOMBIA) 🇨🇴🏦
A critical security breach affecting Banco Unión S.A. has been detected. The incident was publicized by the threat actor Petro_Escobar, in collaboration with the group NyxarGroup.
🏢 Affected Entity: Banco Unión (Giros y Finanzas) Colombia.
👤 Threat Actors: Petro_Escobar / NyxarGroup.
📂 Leak Volume: Over 1,000,000 customer records.
📅 Publication Date: April 22, 2026.
📊 Breach Scope (Exposed Data)
The leaked database is extremely detailed and contains records regarding transactions and debt collection management (Conalcréditos Portfolio), including:
Identity Information: Full names and national ID numbers.
Contact Data: Phone numbers (mobile and landline) and physical addresses.
Financial Information: Obligation numbers, payment commitment amounts, days past due, billing cycles, and account statements.
Operational Details: Call history, detailed notes from debt collectors, economic activity status (e.g., "Employee," "Self-Employed," "Pensioner"), and reasons for non-payment.
Intelligence Monitor: analyzer.vecert.io
🛡️ "Information obtained through the monitoring of data marketplaces and cybercrime forums. VECERT provides this alert for the protection of the Colombian financial sector."
#CyberSecurity #Colombia #BancoUnion #GirosYFinanzas #DataBreach #WesternUnion #VECERT #Ciberseguridad #InfoSec #Hacking 🇨🇴🛡️⚠️

English
h1p 🇨🇴 리트윗함

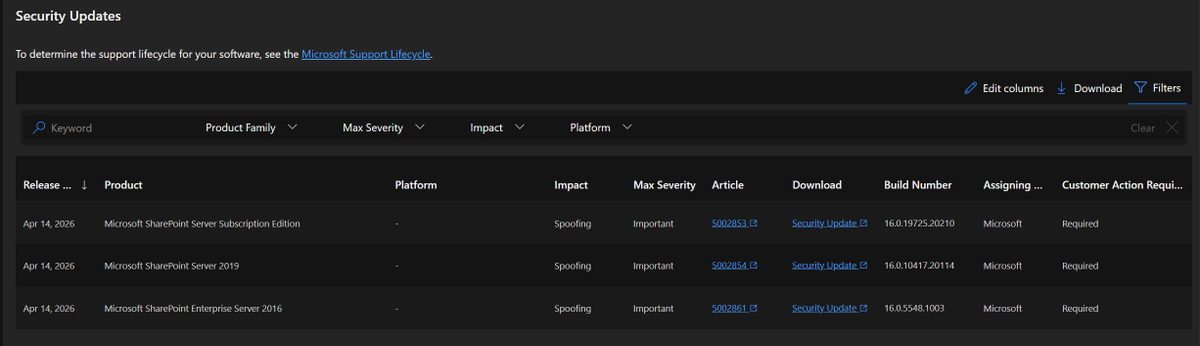
🚨Si tienen en sus empresas SharePoint Enterprise Server 2016, 2019 o SharePoint Server Subscription Edition.
Deben aplicar las últimas actualizaciones publicadas por Microsoft en abril de 2026 para remediar una vulnerabilidad de suplantación.
Un atacante que haya explotado con éxito la vulnerabilidad podría ver información sensible.
Les dejo los KB 👇
‼️ msrc.microsoft.com/update-guide/v…
Español
h1p 🇨🇴 리트윗함

TeamPCP is back.
The xinference PyPI package (680K downloads, 9.3K stars) was hijacked. Import it and your cloud credentials, SSH keys, and .env secrets are instantly harvested and exfiltrated.
Versions 2.6.0–2.6.2 are malicious. If you installed them, assume compromise and rotate everything now.
Full technical breakdown 👇
English
h1p 🇨🇴 리트윗함

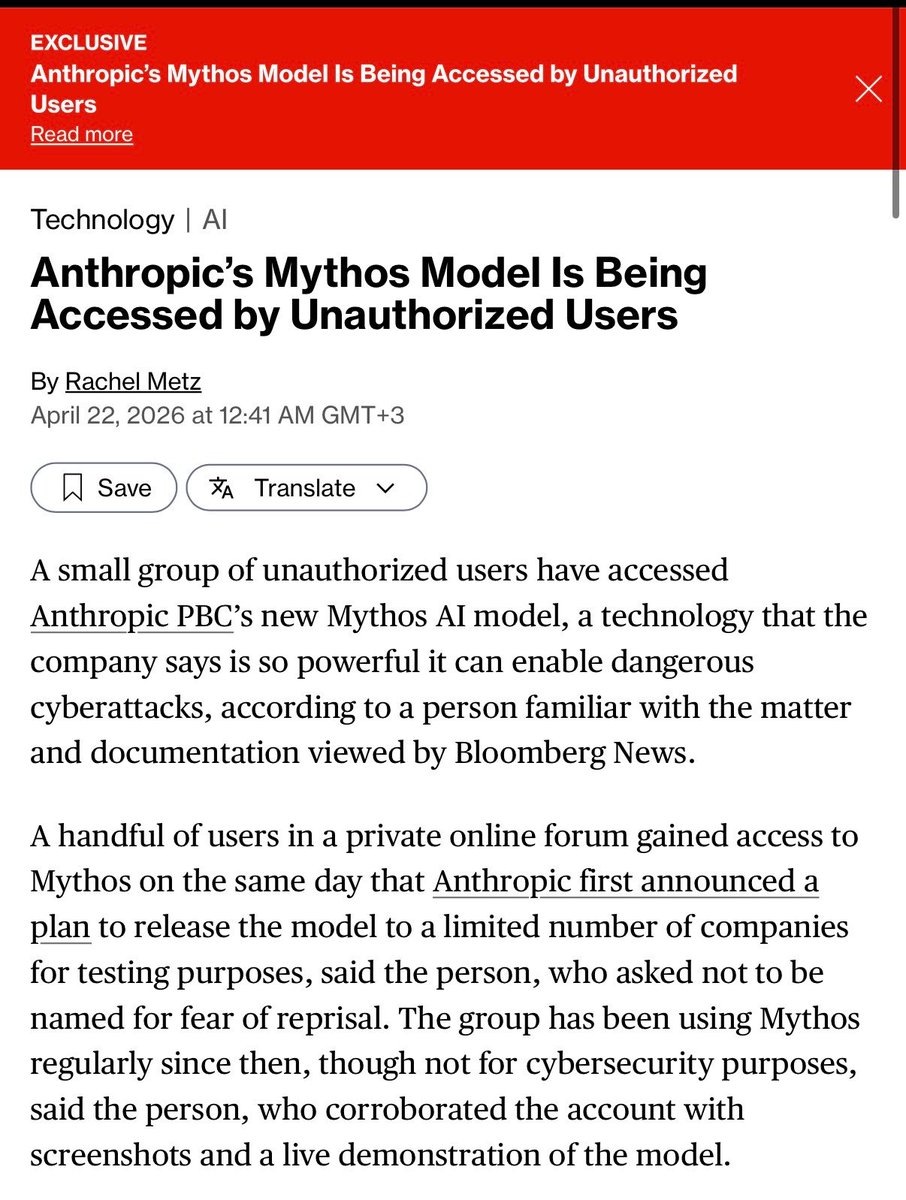
🚨 BREAKING: Anthropic’s Most Dangerous Model Ever Breached By Hackers
> anthropic builds a cyberweapon
> calls it mythos
> “can hack every major OS and browser”
> dario: “we’re the safe & responsible ai lab”
> “can’t release it to the public”
> Mercor (their training contractor) gets breached
> leaks anthropic’s model naming conventions
> hackers guess the URL pattern
> contractor credentials still work
> they’re inside
The group also has access to other unreleased Anthropic models.
Not just Mythos. The whole pipeline.
Anthropic’s statement: “investigating a report of access through one of our third-party vendor environments.”
Mythos got breached on day one 💀


English

Nueva campaña Lazarus ClickFix para macOS kit de malware Mach-o. MAN any.run/cybersecurity-…
Español

I’ve officially launched my startup. To kick things off, I'm offering a free 72-hour full blackbox pentest for startup/org digital assets. If you're interested, say "hello," and I'll reach out.
DorkixAI@DorkixAI
DorkixAI An autonomous pentest agent for offensive security researchers. $0.00 — Free security assessment ( 2 scans only & it's under control of the company ) $200 — Full blackbox pentest ( lifetime access & it's under your control )
English
h1p 🇨🇴 리트윗함

Antrophic instala en secreto spyware cuando instalas Claude Desktop
thatprivacyguy.com/blog/anthropic…

English
h1p 🇨🇴 리트윗함

🚨 CRITICAL SECURITY ALERT: "SUPER ADMIN" ACCESS DETECTED AT COLOMBIAN COMPANY 🇨🇴⚠️
An unconfirmed post has been detected on the BreachForums platform, in which threat actor "gh0stbyte" offers full access to the perimeter infrastructure of a Colombia-based company. The compromise includes "Super Admin" level privileges, granting absolute control over the organization's network.
🏢 Affected Entity: Colombian company (identity undisclosed pending investigation).
👤 Threat Actor: gh0stbyte.
📂 Compromised Assets:
VPN (FortiGate): Full access for remote users.
Firewall Admin: Control over perimeter security policies.
Internal Network: Direct access to Active Directory (AD), facilitating lateral movement and the compromise of all user accounts.
📊 Victim Profile: A company with reported revenue of $49.3 million USD.
📅 Publication Date: April 20, 2026.
⚠️ Extreme Risk Implications
"Super Admin" level access to a FortiGate firewall—combined with access to Active Directory—represents the precursor scenario to a massive ransomware attack:
Total Network Control: The attacker can create new administrator accounts, disable antivirus software and firewalls, and exfiltrate data undetected.
Malware Deployment: With access to Active Directory, an attacker can simultaneously distribute ransomware to every computer within the company.
Data Exfiltration: Prior to encryption, this type of access is typically used to steal sensitive information regarding customers and employees, as well as trade secrets.
🛡️ Mitigation Recommendations (VECERT)
Critical Patching: Verify that FortiGate devices are updated to the latest version to mitigate known code execution vulnerabilities.
AD Review: Monitor for the creation of any new, unauthorized "Domain Admin" accounts.
🛡️ Status: Active. This is a case involving an "Initial Access Broker" (IAB), which typically results in a ransomware deployment within less than 48 hours.
Monitor: analyzer.vecert.io
🛡️ "Information obtained exclusively through the monitoring of public cybercrime forums. VECERT does not conduct intrusions nor does it endorse unauthorized access to systems. This report is provided for informational and proactive protection purposes."
#CyberSecurity #Colombia #Fortigate #InitialAccess #ActiveDirectory #Hacking #VECERT #Ciberseguridad #InfoSec #BreachForums #DataProtection 🇨🇴🛡️⚠️

English

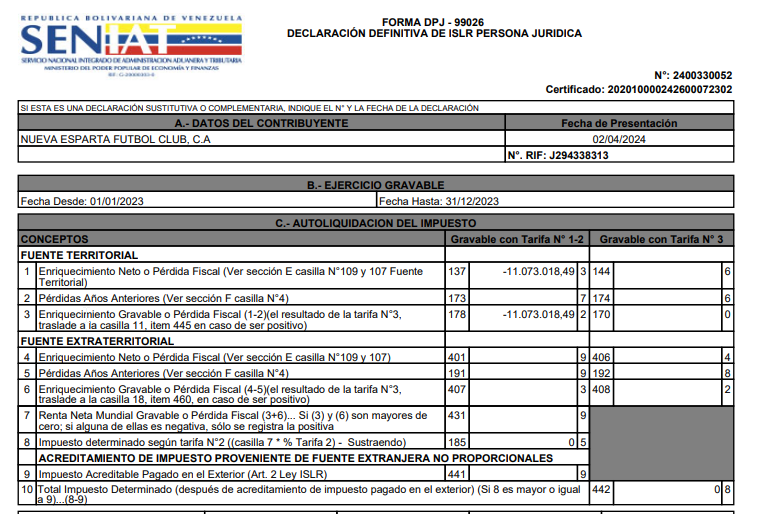
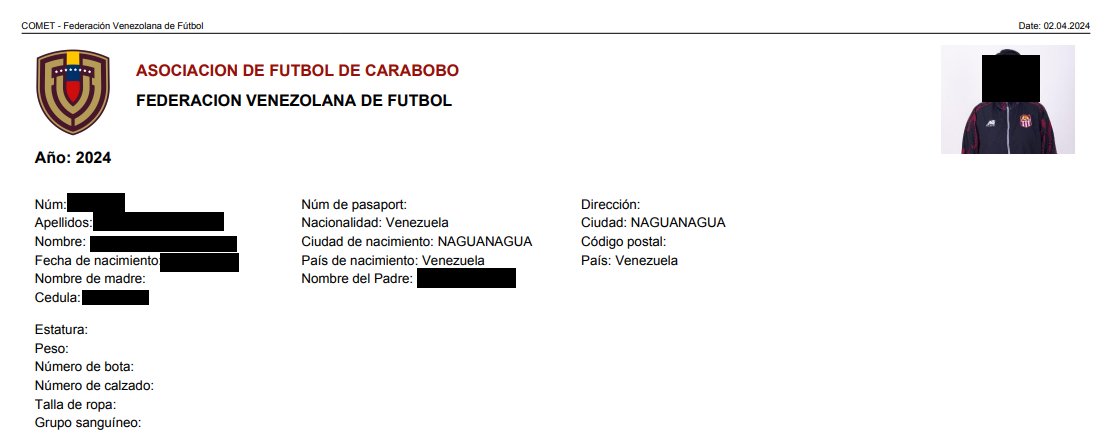
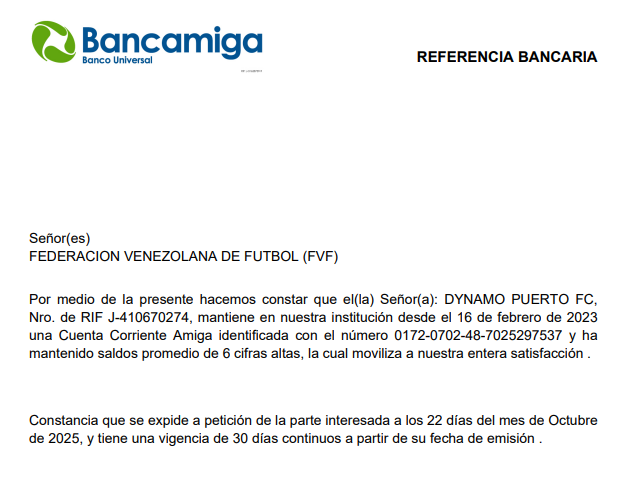
🔴🇻🇪Exposición de datos sensibles en la Federación Venezolana de Fútbol (FVF):
La Federación Venezolana de Fútbol mantenía públicamente accesible un storage que exponía información sensible de varios clubes, entre ellos:
Licencias de clubes como Club Carabobo FC, Dynamo Puerto F.C. y Titanes FC.
Fichas COMET del Club Carabobo FC.
Declaraciones de rentas y contratos.
¿Qué datos quedaron expuestos en las fichas COMET?
Nombres completos, cédulas de identidad, números de teléfono, correos electrónicos, direcciones.
Esta vulnerabilidad fue reportada de forma responsable el 6 de abril mediante correo electrónico y a través de la sección de denuncias de su página web. El almacenamiento fue bloqueado el 17 de abril.
Sin embargo, hasta la fecha no he recibido ninguna respuesta por parte de la FVF. @Canal_Televen
@NTN24ve @VPITV @TVVnoticias
#ciberseguridad #Venezuela #FVF #ResponsibleDisclosure #DataExposure
@Carabobo_FC @DynamoPuertoFC @FVF_Oficial @SeleVinotinto

Español
h1p 🇨🇴 리트윗함

h1p 🇨🇴 리트윗함

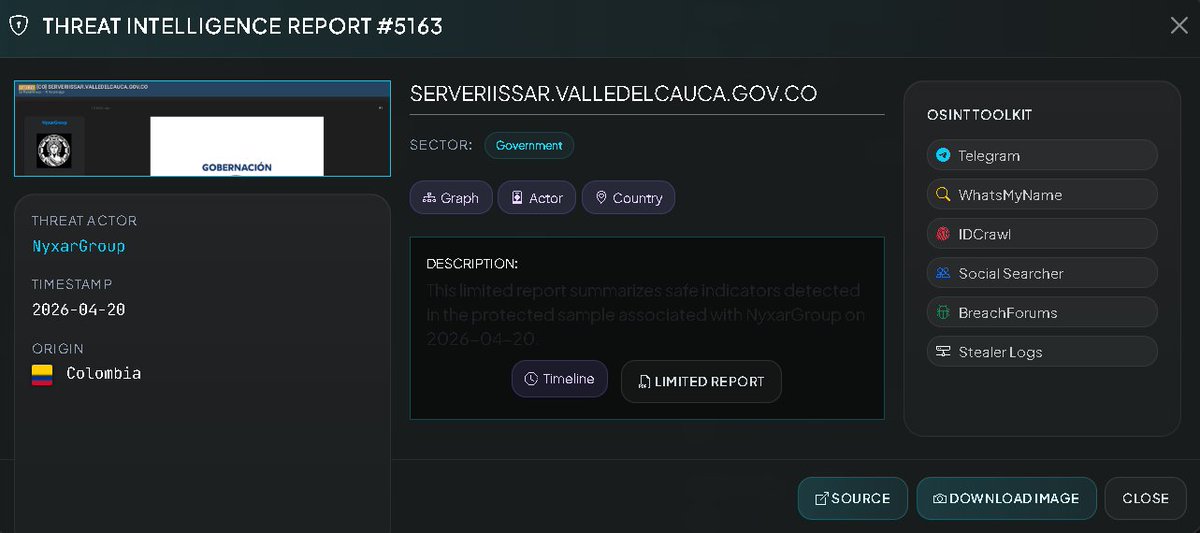
🚨 CYBERSECURITY ALERT: CRITICAL GOVERNMENT AND BANKING DATA LEAK (COLOMBIA) 🇨🇴
The sale of a massive database belonging to the management portal of the Valle del Cauca Governor's Office (serveriissar.valledelcauca.gov.co) has been detected. This incident compromises extremely sensitive information regarding citizens, teachers, and applicants for public office within the region.
🏢 Affected Entity: Valle del Cauca Governor's Office 🇨🇴.
👤 Threat Actors: NyxarGroup
📂 Compromised Assets: * Banking Information: Account numbers, account types, and financial institutions (BanColombia, Davivienda, etc.).
Personnel Records: Lists of active users, teachers, and ethno-educators.
Employment Management: Detailed lists of applicants and appointments (spanning from 2014 to 2025).
Confidential Documentation: Internal files and corporate/government documents.
📊 Exposed Sensitive Data: Full names, National ID (Cédula de Ciudadanía) numbers, genders, educational levels, professional qualifications, and employment status details.
📅 Recency: Transactional records from late 2023 and projected appointments extending through February 2025 have been observed.
⚠️ Security Implications
The combined exposure of National ID numbers alongside banking information and professional profiles poses a critical risk of:
Financial Identity Theft: Attackers possess the necessary data to attempt to compromise bank accounts or apply for fraudulent loans.
Targeted Social Engineering: By knowing appointment histories and the locations of educational institutions, criminals can execute targeted scams against teachers and public officials within the department.
Monitor: analyzer.vecert.io
🛡️ "Information obtained exclusively through the monitoring of public cybercrime forums." VECERT does not engage in intrusions nor does it endorse unauthorized access to systems. This report is provided for informational and proactive protection purposes.
#CyberSecurity #Colombia #ValleDelCauca #DataBreach #GobernacionValle #Hacking #InfoSec #VECERT #Ciberseguridad #DataLeak #ValleHacked #NyxarGroup 🇨🇴🛡️⚠️
English