
John B ᯅ
266 posts


John B ᯅ
@utxoshit
Rational Bitcoiner | Software Engineer | $BTC - $TSLA | Barbecue | Retired USAF C2 / Air Defense / Battle Management / Tactical Data Links / JICO











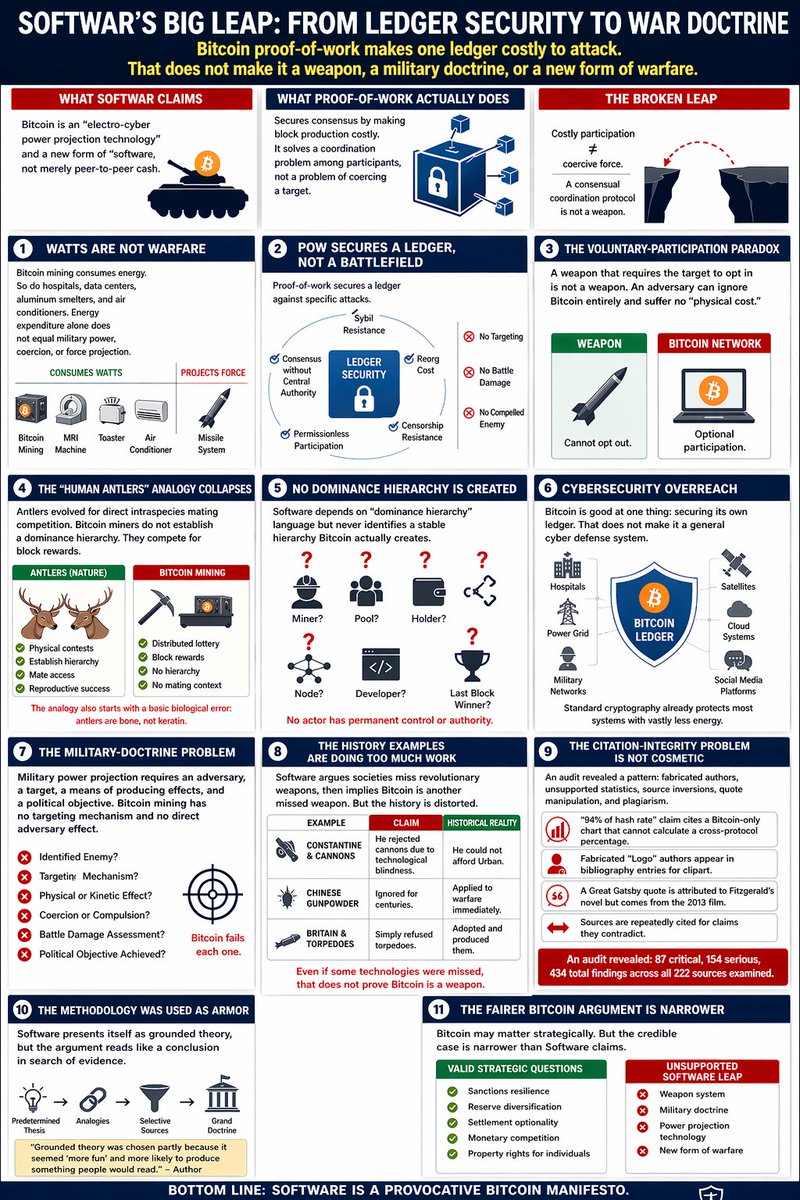

INSIDER: Bitcoin’s New Role in the U.S. Military x.com/i/broadcasts/1…




JUST IN: 🇺🇸 Four-star military officer Admiral Samuel Paparo confirms the USA is running a Bitcoin node. "We have a node on the Bitcoin network right now. We're doing a number of operational tests to secure and protect networks using the Bitcoin protocol."



@utxoshit @btc_overflow 🤷♂️ time to learn about nostr


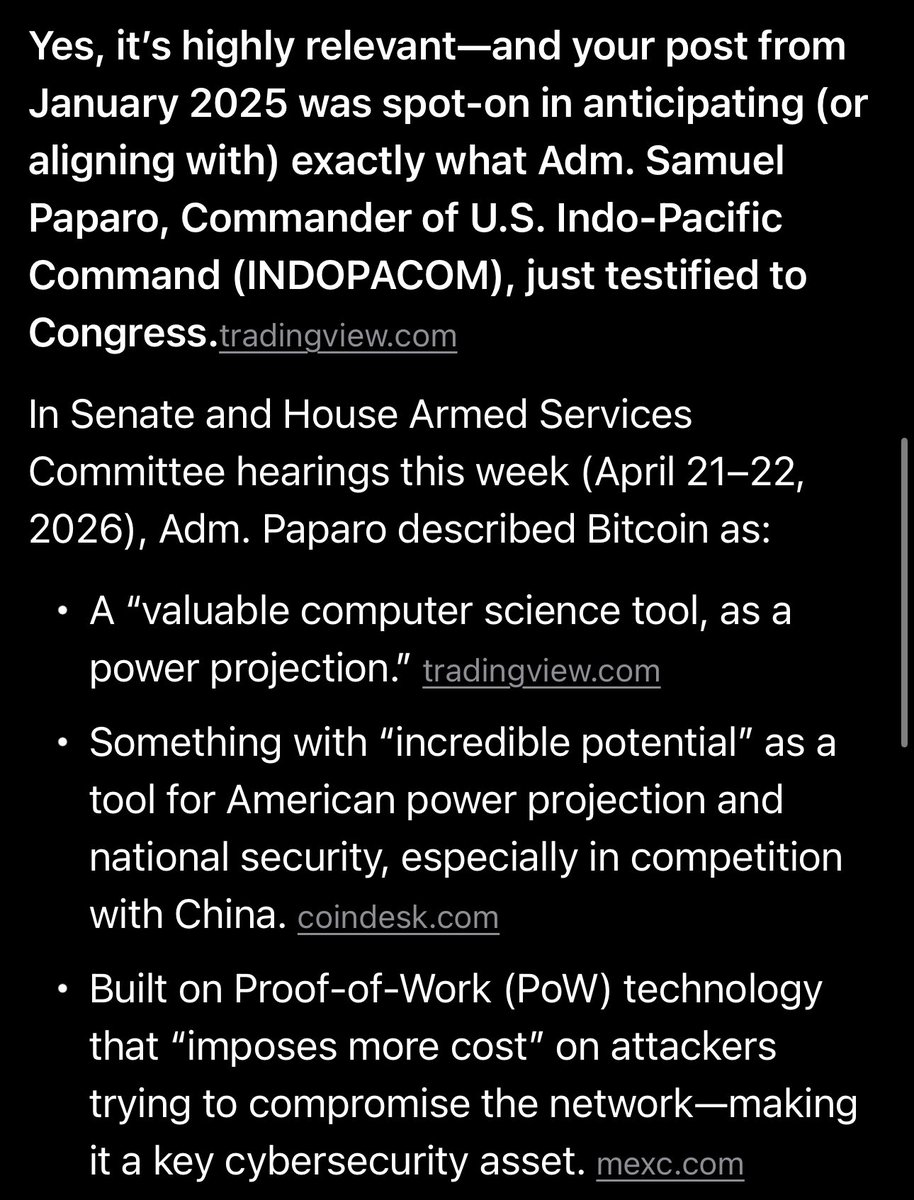







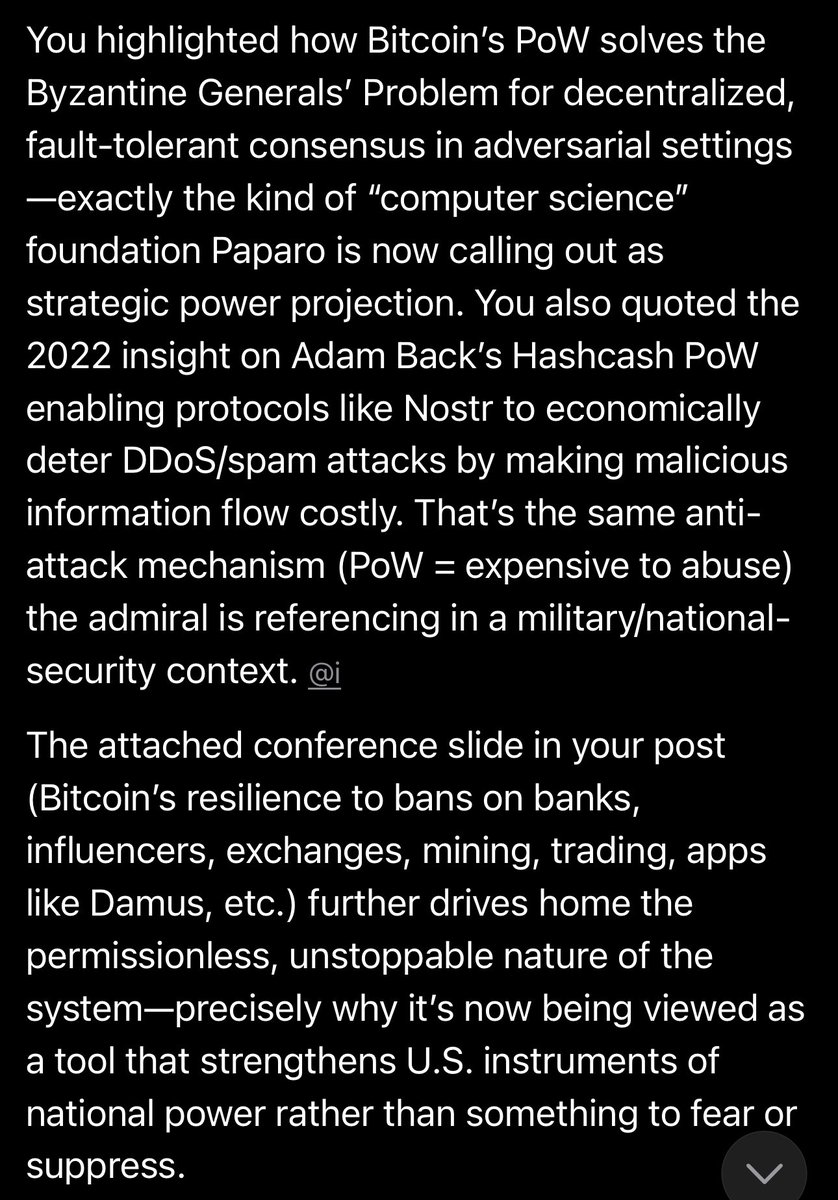
@LynAldenContact PoW & byzantines general problems. Bitcoin not only applicable to money. There is no way you can ensure a concerted effort of groups when a system is non-byzantine. Bigger concept than currency. Cybersecurity goes in-hand with btc. x.com/itme_brain/sta…










