Omar
49 posts


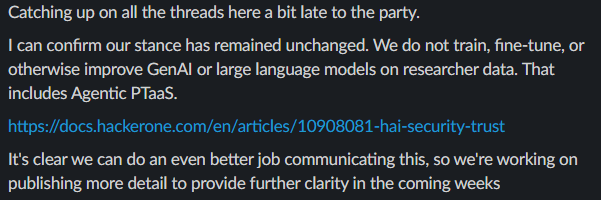

Point-in-time pentests can’t keep up, while fully autonomous testing creates noise. The solution? HackerOne Agentic PTaaS pairs specially trained AI agents with elite human validation to deliver results based on real-world exploitability, not theory. This 50-second video shows you how it works.

Security researcher ily2 has just earned a staggering $3,000,000 from submitting a critical smart contract bug via Immunefi. That's the largest single payout in web3 security in recent memory. In total, he's submitted 3 reports. All 3 were paid. 100% accuracy. His leaderboard update is coming soon, but you can pledge IMU to him now and earn when he finds the next one: immunefi.com/pledge/ily2











When a single ID fails, a pair might pass. IDOR bypasses can be that simple 🔥 - Victim's ID: 5200 - Attacker's ID: 5233 GET /api/users/5200/info → Access Denied ❌ GET /api/users/5200,5233/info → Bypassed ✅ #bugbountytips #PenetrationTesting