Sabitlenmiş Tweet
Bhaskar
365 posts


Bhaskar
@0xPSB
Blockchain Developer (Solidity, Rust, Move) | Web3 Security Researcher | Ethereum • Solana • Aptos | IIITN | prev: @quillaudits_ai
Space Katılım Ağustos 2022
611 Takip Edilen180 Takipçiler
Bhaskar retweetledi

While you slept last night, completely motionless in your bed, our galaxy shifted millions of kilometers through the cosmos.
You woke up in the same room, on the same planet, but unimaginably far from where you were the night before.
The Milky Way does not glide silently through the universe. It is racing through space at about 600 kilometers per second, carrying with it billions of stars, planets, and everything they contain on the journey. It is a good reminder that, even when life seems motionless, you are always in motion.
English
Bhaskar retweetledi

Hot take: There isn’t lack of VC money in crypto. In fact I’d argue there’s still oversupply of capital.
What’s lacking is courage. Courage to build something that defines a new unproven category.
Right now I’m mostly seeing copycats chasing what’s already working. But no one cares about the 69th prediction market, 69th yield vault, 69th stablecoin neobank, etc.
Polymarket, Morpho, Redotpay, etc. won because they were early to new categories before they became obvious.
English
Bhaskar retweetledi
Bhaskar retweetledi

🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages.
The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise.
This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now.
Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that:
• Deobfuscates embedded payloads and operational strings at runtime
• Dynamically loads fs, os, and execSync to evade static analysis
• Executes decoded shell commands
• Stages and copies payload files into OS temp and Windows ProgramData directories
• Deletes and renames artifacts post-execution to destroy forensic evidence
If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.
English
Bhaskar retweetledi

A partial liquidation can leave bad debt and drain a borrower's entire collateral, even at HF = 0.99, if LT * (1 + bonus) >= 1.
@D4r3_D3v1L_ checked 22 protocols using partial liquidation. 4 are vulnerable, 6 have on-chain constraint.
I wrote two posts breaking this down:
English
Bhaskar retweetledi
Bhaskar retweetledi
Bhaskar retweetledi
Bhaskar retweetledi

a hacker uses claude to find a bug -> reports it.
the triager uses claude to validate it -> confirmed.
the developer uses claude to verify, agrees -> patch shipped.
and all of them did thier job except it wasn't a vulnerability, there was no job, all of them consulted one oracle to validate the information and had shared psychosis together because their source of information is one in different layers.
now apply this everywhere, programming, governemnts, medicine, etc. different people asking the same oracle independently, and all grounding their reality to an LLM.
there is a good chance whole new startups are in this shared delusion spinning out of these llms, even their customers using llm to make their buying decision.
we once built religions out of information scarcity. now it seems we have information abundance but lacking comprehension, and we’re building new kind of religions?
English

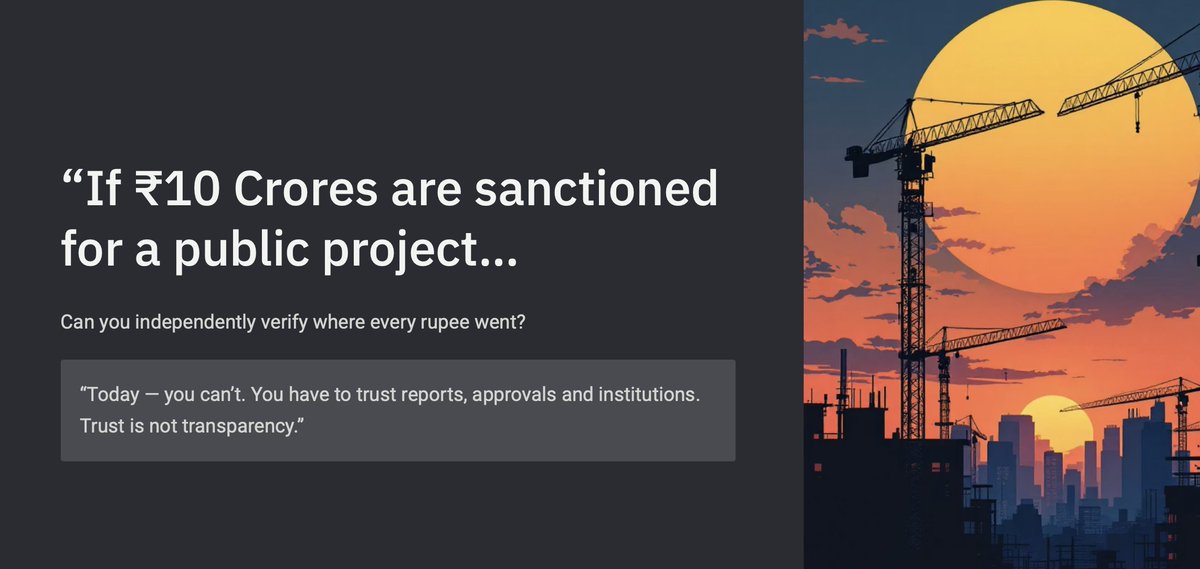
If ₹10 Crores are sanctioned for a public project, can you independently verify where every rupee went?
Today, most public spending is hidden behind reports and manual approvals that citizens cannot easily audit.
@BhushanHem58814
@geeky_kartikey @piyushJha__ @itsNikku876

Bhaskar@0xPSB
Every document generates a QR code for instant public verification — tamper-proof, transparent, and independently verifiable public records ⚡ #Monad #MonadBlitz #Blockchain #PublicGoods #Web3 cc: @geeky_kartikey @piyushJha__ @itsNikku876
English

Every document generates a QR code for instant public verification — tamper-proof, transparent, and independently verifiable public records ⚡
#Monad #MonadBlitz #Blockchain #PublicGoods #Web3
cc:
@geeky_kartikey
@piyushJha__
@itsNikku876
English

Building CivicProof with @BhushanHem58814
A blockchain-based government project document verification system built on
@monad_xyz
where the platform securely manages document uploads to IPFS, coordinates digital signatures from the relevant authorities
English