Sabitlenmiş Tweet

Bakuchi | Napier
4.4K posts


@0xbakuchi
dev / @NapierFinance



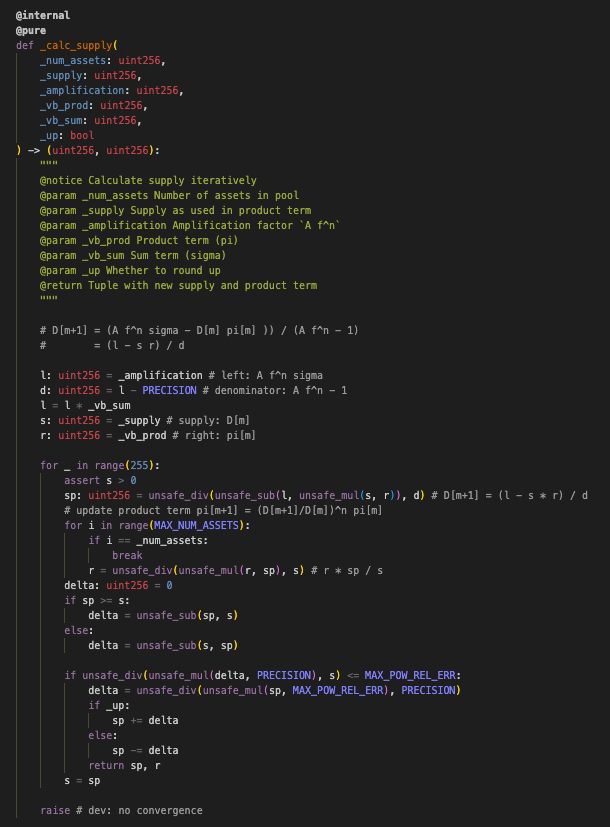
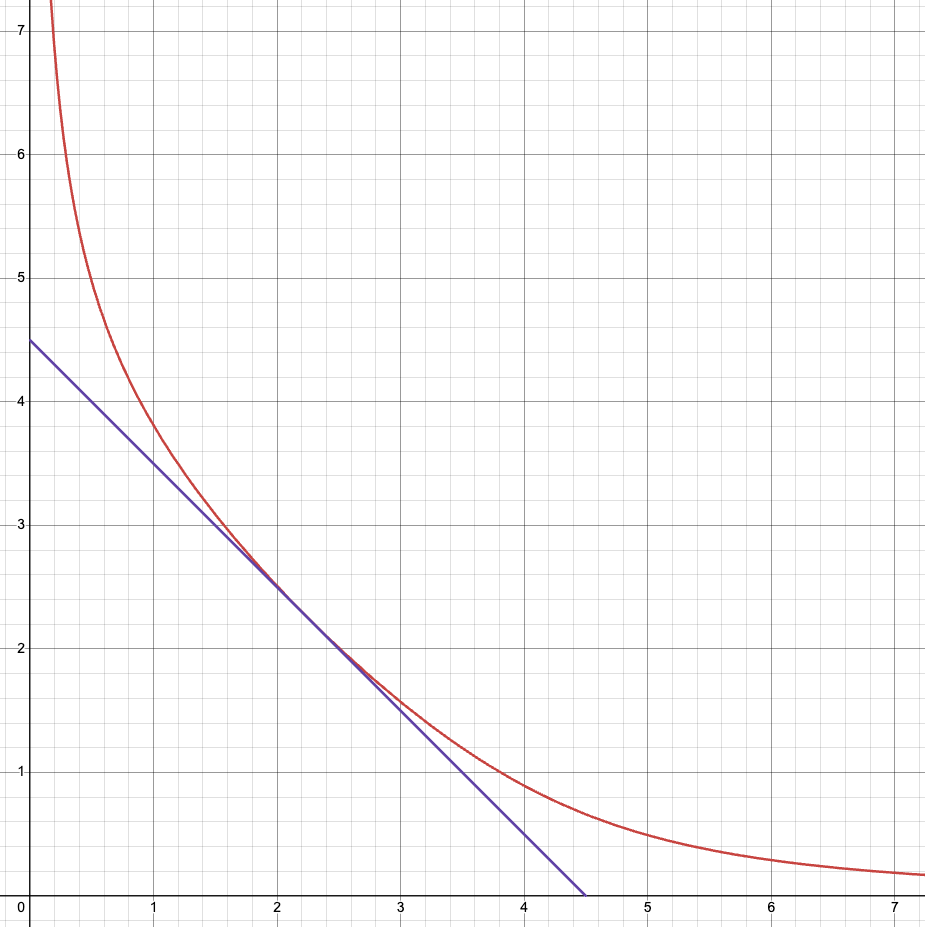
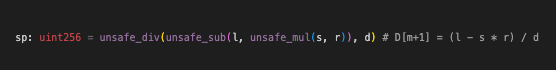



1/ Today, we unveil Napier AMM. A liquidity network optimized for yield trading featuring concentrated liquidity, JIT liquidity, rehypothecation, time-adaptive curves. Designed to liberate the potential of yield tokenization.





uniswap v4 hookの解説向けに、aave貸し出しカスタムカーブhookのsolidityと sdk v4を使ってリワード狙いで流動性をなろーレンジに突っ込むコードを作ったので、来週のどこかそれぞれのライブラリとか諸々解説したい。