Sabitlenmiş Tweet
International Cyber Digest
5.7K posts


International Cyber Digest
@IntCyberDigest
Your weekly go-to cybersecurity newsletter, curated and commented on by our senior analysts. Got tips? Signal: IntCyberDigest.20
Katılım Eylül 2024
298 Takip Edilen145K Takipçiler

@ishowcybersec @L1v1ng0ffTh3L4N Indeed. People should take that into account when using Edge.
English

@IntCyberDigest @L1v1ng0ffTh3L4N Edge loads every saved password as cleartext into memory at launch, even for sites you never visit that session. Microsoft's response when reported: "by design."
In shared environments, that's not a design choice. That's a liability.
English

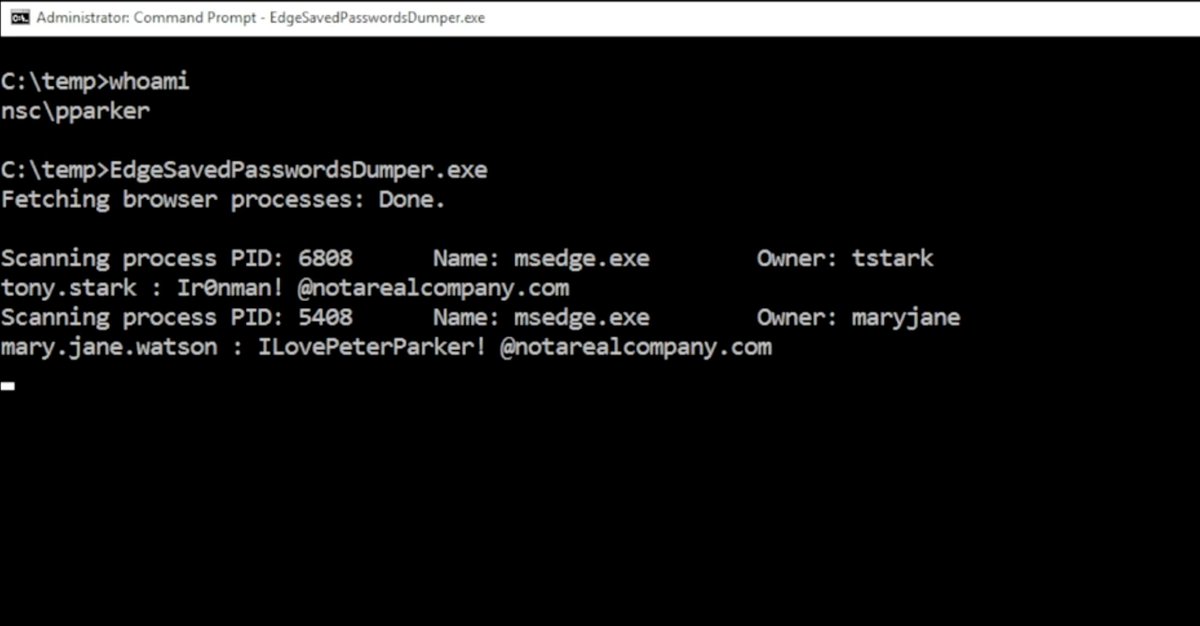
❗️🚨 Microsoft Edge keeps every saved password in process memory as cleartext from the moment it launches. Microsoft's responsed when reported: "by design."
All of them. Including credentials for sites you won't open this session.
Researcher @L1v1ng0ffTh3L4N tested every major Chromium browser. Edge is the only one that behaves this way.
Chrome decrypts credentials on demand, and App-Bound Encryption locks the keys to an authenticated Chrome process so other processes can't reuse them.
In Chrome, plaintext surfaces only during autofill or when a password is viewed, making memory scraping far less useful.
What makes this extra weird is that Edge still demands re-authentication before revealing those passwords in its Password Manager UI, while the same browser process already holds every one of them in plaintext.
In shared environments, this turns into a credential harvest. On a terminal server, an attacker with admin rights can read the memory of every logged-on user process. In the published PoC video, a compromised admin account lifts stored credentials from two other logged-on (and even disconnected) users with Edge running.
Microsoft's official response when notified: "by design."
The finding was disclosed April 29 at BigBiteOfTech by PaloAltoNtwks Norway, alongside a small educational tool that lets anyone verify the cleartext storage for themselves.

English

@aitization @L1v1ng0ffTh3L4N Good question. I think most people are used to it. Myself included. I only use it for gaming now.
English

@IntCyberDigest @L1v1ng0ffTh3L4N Why are ppl still using Microsoft 🤷🏻♂️
English

Tool to demonstrate this behaviour by Edge is live: github.com/L1v1ng0ffTh3L4…
English

Video of @L1v1ng0ffTh3L4N's tool in action.
In the published PoC video, a compromised admin account lifts stored credentials from two other logged-on (and even disconnected) users with Edge running.
English

@CharlesS0228 Kids will always find ways to outsmart us.
English

@IntCyberDigest Imagine kids outsmarting government policy and AI by drawing on their faces.
English

🇬🇧 The first major assessment of the UK's Online Safety Act is out. Turns out kids are fooling the age checks by drawing moustaches on their faces.
"I did catch my son using an eyebrow pencil to draw a moustache on his face, and it verified him as 15 years old." Mum of a 12-year-old, in a new report from Internet Matters, the UK's leading online-safety NGO.
That single line tells you almost everything you need to know about how the UK's Online Safety Act is going.
This is the law that:
🔴 Forced UK platforms to demand government IDs, facial scans, and credit-card checks from adults to access ordinary websites
🔴 Drove a 1,800%+ spike in VPN downloads the week the porn-site age checks went live in July 2025
🔴 Pushed millions of users into handing biometric data to private third-party verification vendors
🔴 Sits at the front of a global wave: Greece's anonymity ban, France's "VPNs are next" comments, Utah's VPN crackdown, and the EU's 27-state rollout deadline of December 2026
The headline numbers from the assessment:
🔴 46% of children say age checks are easy to bypass. Only 17% say they are difficult.
🔴 32% of children have already bypassed them in the past two months
🔴 49% of children still report experiencing harm online in the past month
The bypass methods kids reported, in their own words:
🔴 Drawing on facial hair with eyebrow pencil to fool facial age estimation
🔴 Holding up a video game character's head turning during the face-scan
🔴 Submitting a video of a different person's face entirely
🔴 Using a parent's ID (often with parental consent)
🔴 Entering a fake birthday (still works on most platforms)
🔴 Using someone else's login or device
🔴 In a small minority of cases, VPNs
One 12-year-old girl explained the system to researchers: "Every time I go live on TikTok, it tells me I have to be 18, but when the AI detects that I'm not 18 they ban me. But they only ban me for 10 minutes and then I can go live again." That is the entire enforcement model.
A 14-year-old summed up the broader picture: "It's not practical because the more you restrict it, the more people are going to want to get past that age restriction." A 16-year-old, more bluntly: "I think it's a great idea in theory and I applaud its intentions, but I don't see how that's feasible, because kids will always find a way."
Even when verification works, it works against the children. A 12-year-old boy on Roblox: "I put my face in and I got 15 when I'm 12, so I'm chatting with people older than me when I shouldn't be." A 13-year-old non-binary child: "Adults can very easily use a face they searched on the internet to trick it into thinking you're someone you're not, so there might be adults in kids' age groups trying to groom them." Recent reporting confirms exactly that. Underage Roblox accounts are now being sold online to predators precisely because they bypass the new "safety" measures.
One detail in the report stops you cold. Multiple children described being unintentionally exposed through their feeds to the assassination of Charlie Kirk. A 14-year-old: "I saw it on Snapchat. I broke down into tears and then told my mum immediately." Violent content, racist content, content promoting unrealistic body types: all explicitly prohibited under the Children's Safety Codes. All still landing in feeds at scale.
Parents told researchers about the day-to-day reality of trying to enforce the rules at home. A father of a 14-year-old: "What you'll find now is that the kids know more than we know in terms of how to disable [parental controls]. We've got the parental controls on, but they probably unlock them." A mother of a 13-year-old: "We do what we can, but our kids are all clever and savvy and they can get around stuff." A mother of a 12-year-old: "I can put all the checks and measures in, and I can be keeping an eye open on what she's watching, listening to, who she's chatting to. And then she could go to a house down the road and visit somebody whose parents don't care, and they've got zero checks and measures."
Both children and parents expressed real concerns about handing over biometric data to verification platforms they do not trust. One father warned: "Kids don't know the difference between a genuine website and a website that isn't genuine. If all websites have facial verifications and they go on a website that is not genuine, their face and their documents could be used to do illegal stuff."
The father is right. The Discord vendor breach in October 2025 already exposed roughly 70,000 government IDs uploaded purely for age verification. The EU's own age verification app was reportedly hacked within minutes of launch.
The report's most uncomfortable finding sits inside the parental data. 26% of parents are not just aware their kids bypass age checks, they are actively complicit. Some logged into their child's account with their own ID to "go live" on TikTok. Others approved circumvention so their child could play a specific game. The reasoning is rarely malicious. Parents told researchers they only help when they personally judged the activity safe. But the structural problem is fatal: a verification system that treats parents as the last line of defence collapses the moment parents themselves become the bypass.
Even children who follow the rules end up disadvantaged by them. A 15-year-old: "There are websites that are support websites to help with things such as eating disorders and suicide, and they've all been censored." A 12-year-old: "Before you could talk to anybody, but they added age group limits so you can only talk to people in your age group. So if my friends are younger or older than me I wouldn't be able to talk to them." The blunt instrument of age-gating breaks legitimate connection and support without measurably reducing harm.


English

Read the full report: internetmatters.org/hub/research/o…
English

@IntCyberDigest Those who left school and got success actually came from rich families so have a rich family or cope lol
English

@IntCyberDigest Let's all also realise the "school" they left was Harvard, and not some random ass community college.
English

It could actually be a significant problem that Europe doesn't have enough garages. This sounds like a joke, but I'm serious. Garages let you work on stuff that doesn't matter yet, which is how big things often start. The outliers of ideas need the outliers of space.
Jon Erlichman@JonErlichman
First offices of 6 companies worth a combined $21 trillion.
English

@IntCyberDigest No wonder his name is hoe. Hate the app and the founder.
English

❗️ There is a fake "Notepad++ for Mac" website making the rounds, and it has already fooled tech media into reporting it as an official release.
🔴 Notepad++ has never released a macOS version
🔴 Site uses the trademark + the founder's name and bio without permission
🔴 Founder Don Ho has contacted the site owner. No reply yet.


English

Read Oracle's announcement: blogs.oracle.com/security/accel…
English

🚨 Frontier AI models are forcing Oracle to move from quarterly to monthly critical security patches.
Starting May 2026, Oracle will release a monthly Critical Security Patch Update for high-priority vulnerabilities, breaking with the quarterly cadence the company has used for nearly two decades. Quarterly Critical Patch Updates will continue, but they will now bundle the prior monthly them into one cumulative drop.
The reason Oracle gave is AI, it is changing how fast vulnerabilities are found and how fast they need to be patched. Oracle confirmed it is using Anthropic's Claude Mythos Preview and OpenAI's most capable models, accessed through Trusted Access for Cyber, to identify vulnerabilities across Oracle-developed software, Oracle Health, and the open-source components built into their products.
This is the same trend that surfaced last week with Theori's Xint Code finding the Copy Fail kernel bug after about one hour of AI scan time. Defenders are now finding bugs faster than the old patch cycles can deliver them.
Summarized:
🔴 Oracle has historically been one of the slowest of the major vendors to ship security fixes. Critical bugs disclosed early in a quarter could sit unpatched for up to three months...
🔴 Adobe and Microsoft have been on monthly cycles for years. Oracle was the holdout
🔴 Oracle still acknowledges the same problem at every patch round: customers who got breached because they did not install available updates
🔴 The CSPU patches are smaller and more targeted, which Oracle says will make them easier to apply quickly
What this means for defenders:
🔴 If you run on-premises Oracle, get ready for monthly patch nights instead of quarterly ones
🔴 Plan testing pipelines that can validate small, targeted patches in days, not weeks
🔴 The old "we patch quarterly" risk model is officially obsolete across most of the industry
AI-assisted vulnerability research is now a permanent fixture in the stack, and the bugs it finds do not wait for the next quarterly window.


English


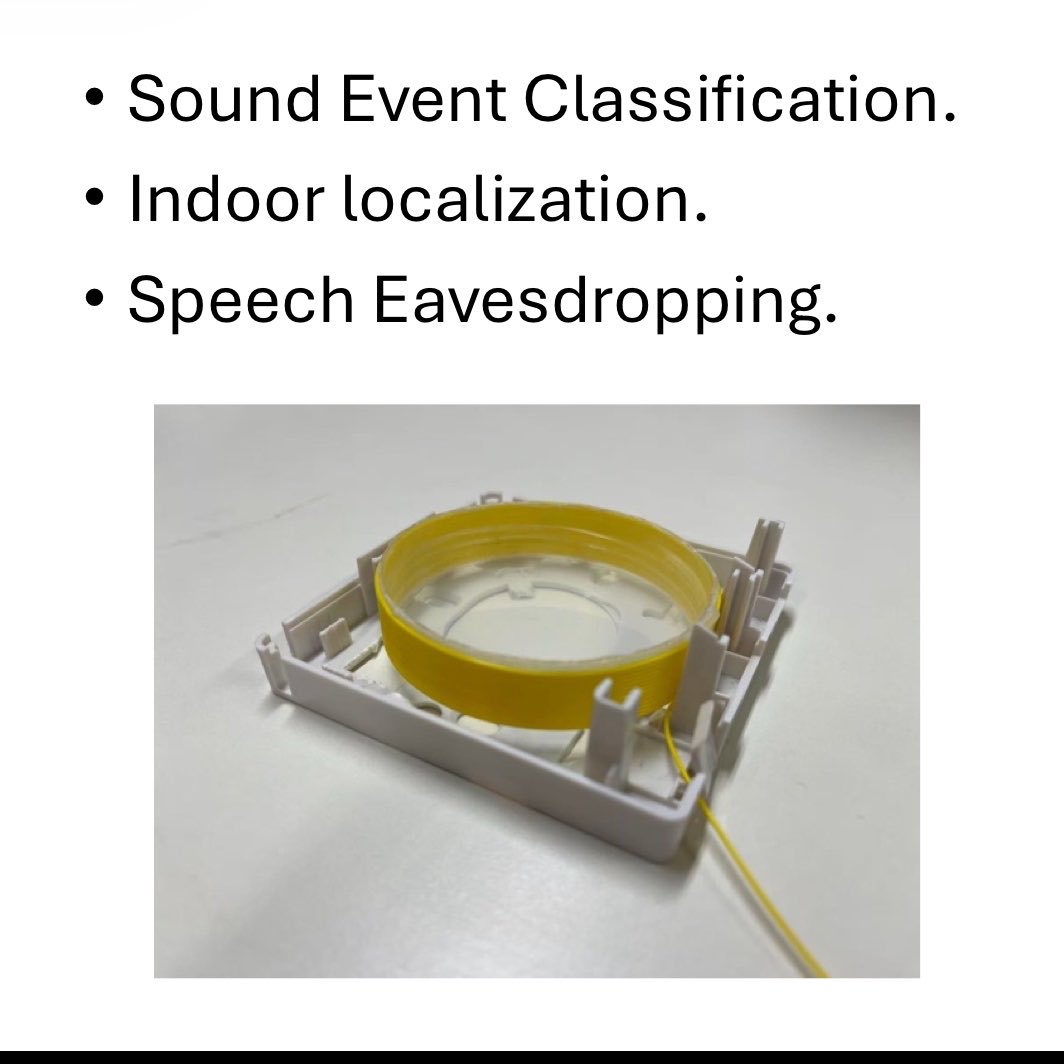
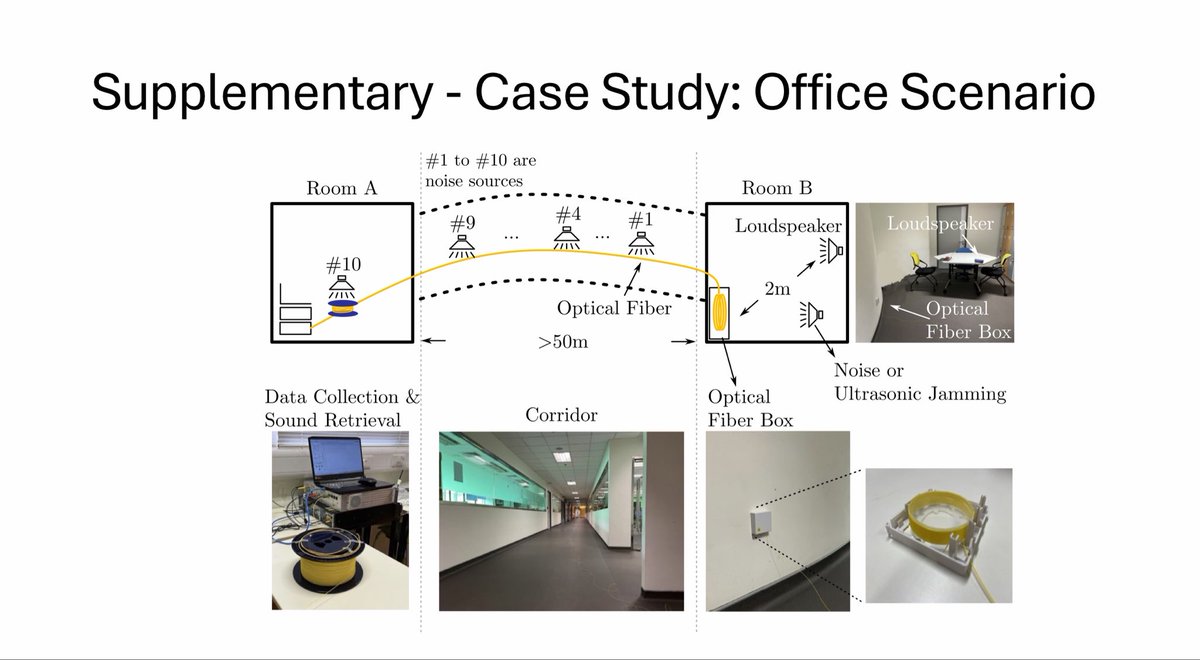
‼️🚨 NEW RESEARCH: Fiber-optic cables can be turned into a hidden microphone and used for eavesdropping.
Researchers from Hong Kong's PolyU and CUHK just proved it works in real conditions. The paper was presented at NDSS 2026, one of the top cybersecurity conferences in the world.
When someone talks in a room, the sound waves cause tiny vibrations in everything around them, including the thin glass fiber that runs into your apartment from your internet provider. Those vibrations slightly disturb the laser light traveling through the cable. If an attacker plugs the other end of that cable into a special device called a Distributed Acoustic Sensing system, they can read those tiny disturbances and turn them back into recognizable speech.
The problem for the attacker: a normal fiber lying along your baseboard is not sensitive enough on its own. Sound fades too fast in the air, and the fiber is too thin to pick it up.
So the researchers built a small device they call a "Sensory Receptor." It is basically a 65mm plastic cylinder with about 15 meters of fiber wound around it. The cylinder catches and amplifies sound waves enough for the fiber to register them. Crucially, it is small enough to hide inside the same little plastic junction box your internet installer leaves on the wall to manage extra cable.
What the attack can actually pick up:
🔴 Daily activities (typing, walking, snoring, washing dishes): 83% recognition accuracy
🔴 Where in the room a sound is coming from: accurate to within about one meter
🔴 Spoken words at meters from the receptor
🔴 In a real office test, with the receptor hidden in a fiber box and the attacker 50+ meters away in another room, around 80% of the conversation was recoverable
Why this attack is different from a hidden microphone:
🔴 No electricity, no batteries, no radio signals
🔴 Cannot be found by professional bug sweeps that look for hidden mics or cameras
🔴 Cannot be jammed by ultrasonic jammers (the kind some boardrooms use against phone microphones)
🔴 Looks identical to a normal fiber cable
The researchers tested a commercial ultrasonic jammer right next to their device and it had zero effect. The defenses meant to protect sensitive meetings simply do not see this attack coming.
What you can do:
🔴 If you run a sensitive office or meeting room, ask your IT team about polished fiber connectors and optical isolators. Both make this attack much harder.
🔴 Do not let your internet installer leave excess fiber coiled up inside the room. Have them coil it inside the wall or in a sealed box outside the room.
🔴 Keep fiber cable runs away from desks and walls that resonate with conversation.
🔴 In high-security spaces, soundproof the walls and ceilings where fiber runs.
English

@nexusloops True, some organisations use fibre optic cables because they transfer confidential data. Those should be concerned.
English

@IntCyberDigest it's a really interesting paper, still it only works with dark fibers..easier in an office setting than houses..
the "house" setting is a bit complicated and the test results arren't (luckily) great for speech.
at home, the safest thing is having only 1 fiber, the one you use 🤷🏼♀️
English

@Geecube3 This is a proof of concept. Imagine what can be done with years of research and AI…
English

Honestly this would take a lot of inside job to pull off, and the longer the optical cable the more you lose the signal, so you'll either use more amplifier which can only do so much or have to be close which would just take us back to the inside job thing and if it's a high building good luck lol
English