Sabitlenmiş Tweet

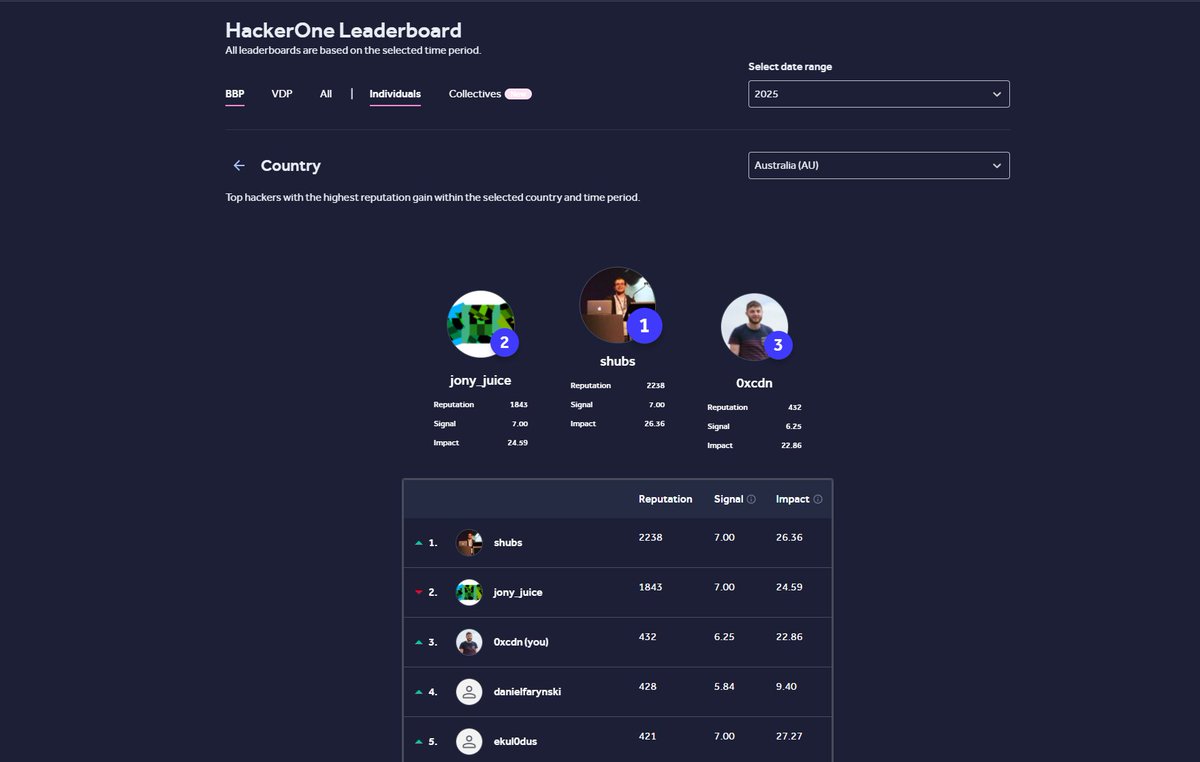
Still learning every day. The climb in mid December and finishing #3 (bbp) in Australia feels unreal. Very grateful for the journey.
Accomplished this year:
- XXE on a major social platform
- ATO on a major AI
- PII leaks
- CPDoS across 50+ programs
- A valid Google report which affected thousands of domains
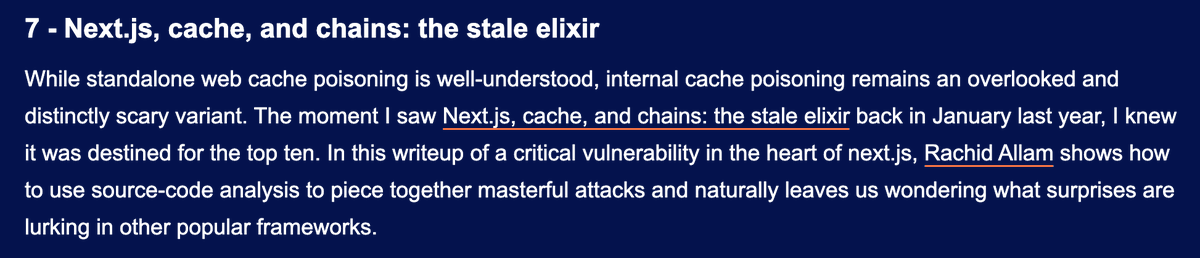
In 2026 I’m finally reading all my writeups so I can clear all my bookmarks, because this is getting ridiculous😄
English