Faraday
13 posts
Faraday
@0xffaraday
Security Analyst @Huntresslabs | SGF2ZSBhIG5pY2UgZGF5IQ== | Personal opinions and research are my own and don’t represent my employer
Katılım Mayıs 2022
156 Takip Edilen146 Takipçiler
Faraday retweetledi

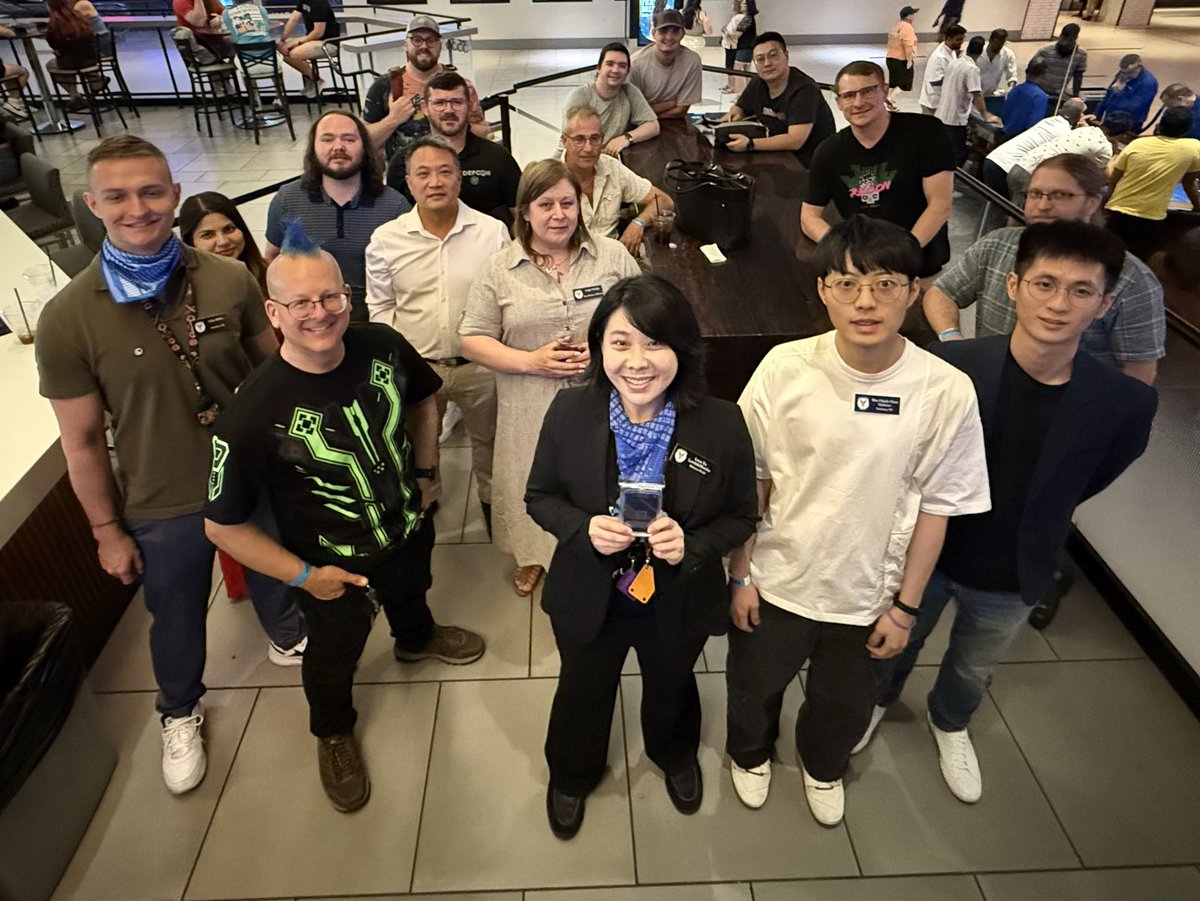
That wraps up #MalwareVillage
@DEFCON 33! 🥳
Special thanks to all the organizers, sponsors, volunteers, speakers, workshoppers, collaborators, attendees, and everyone involved, for making this event absolutely legendary! 🤩
Thank you all! 🙏



English
Faraday retweetledi

Got a new @HuntressLabs blog out today taking a look at some intrusion analysis methodology with practical examples - check it out!
huntress.com/blog/intrusion…
English
Faraday retweetledi
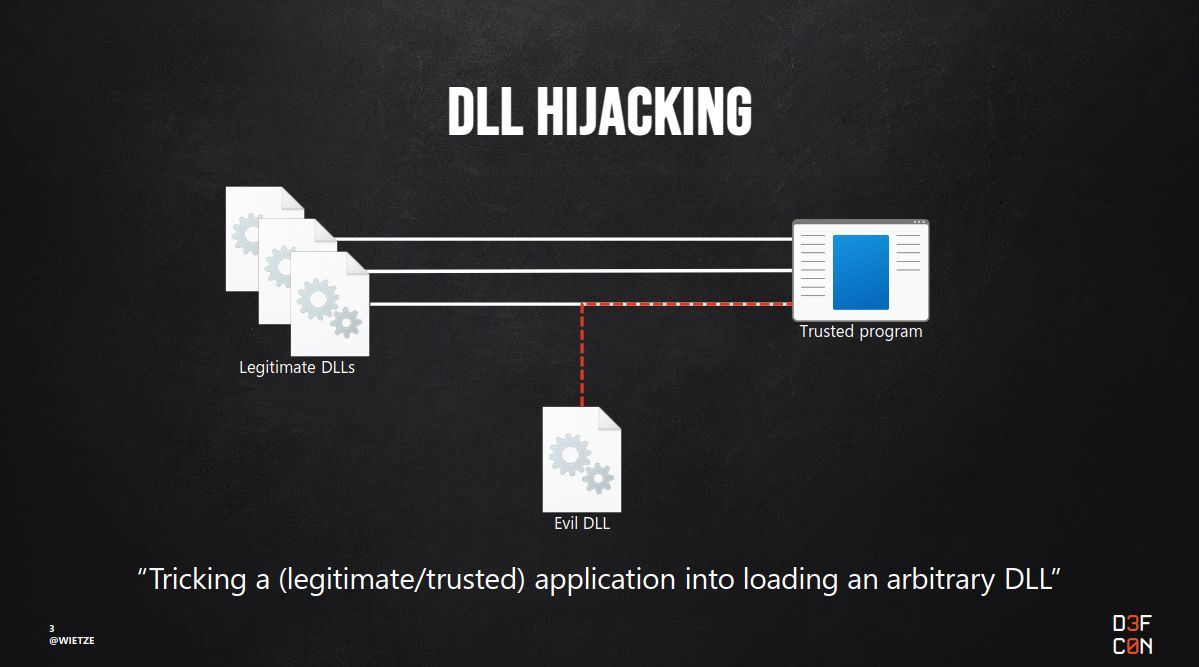
ATT&CK v17 is out! It contains an update I have campaigned for since 2022: DLL Hijacking is now a single sub-technique, merging Search Order Hijacking & Sideloading, plus supporting related techniques.
Huge thanks & congrats to the @MitreATTACK team on this release 🎉
English
IOCs:
SC domain:
virustotal.com/gui/domain/soc…
Domain involved with scheduled task:
http[:]//shopeasy.giize[.]com/dashboard/bor3y/update[.]php
SC installer:
Recently_S_S_A_Statement9030773.exe
VBS file from SC:
C:\Users\Public\Music\//n5R79uzirhL2.vbs
English
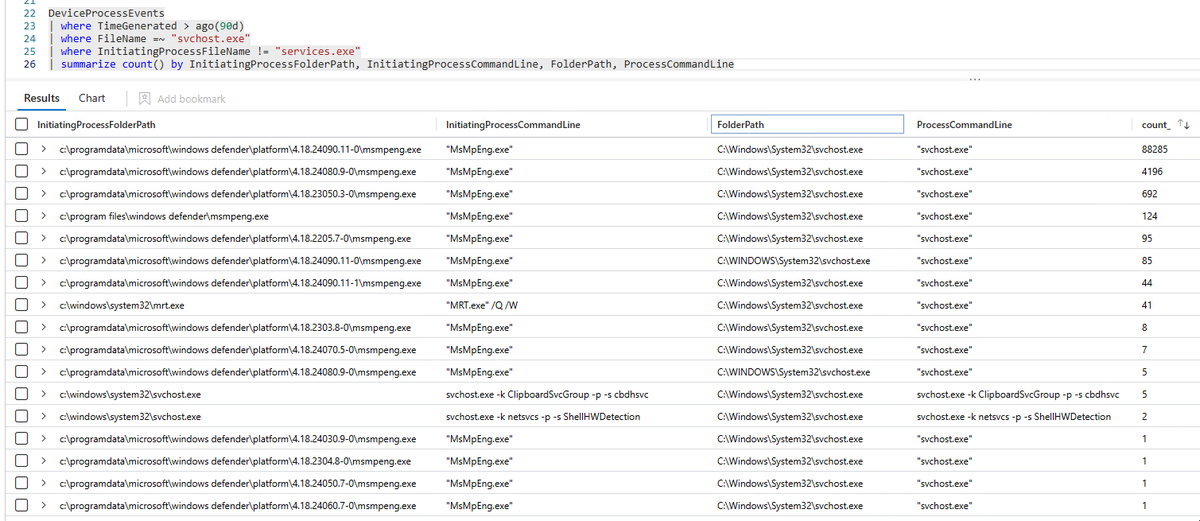
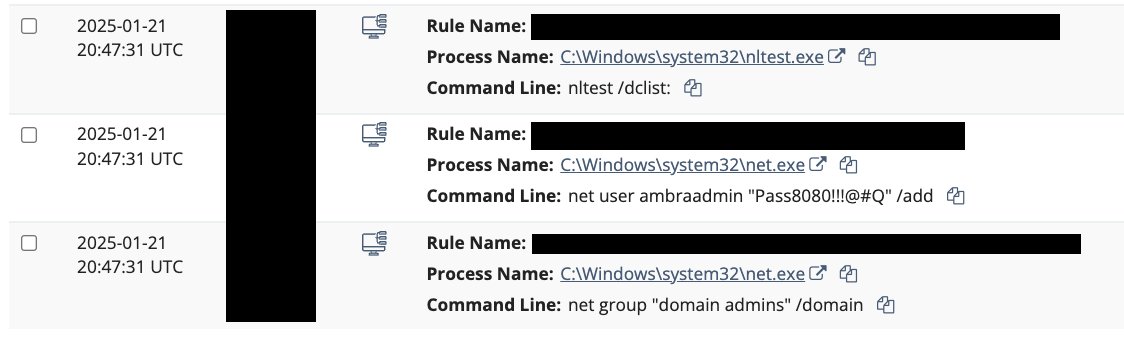
@HuntressLabs SOC is seeing a newly suspected KoiLoader/KoiStealer attack chain. Details below:
English
Faraday retweetledi

Windows audit policies, some common events they enable, and the volume of events they produce.
#ThreatHunting #DFIR #Cybersecurity

English
Faraday retweetledi

Who says #Python Malware is out of style? In our new #blog,@GuhnooPlusLinux revisits an old technique he believes is a prime candidate to host #malware payloads—Python for Windows. Read it now! hubs.la/Q033Jvyq0
English
Faraday retweetledi

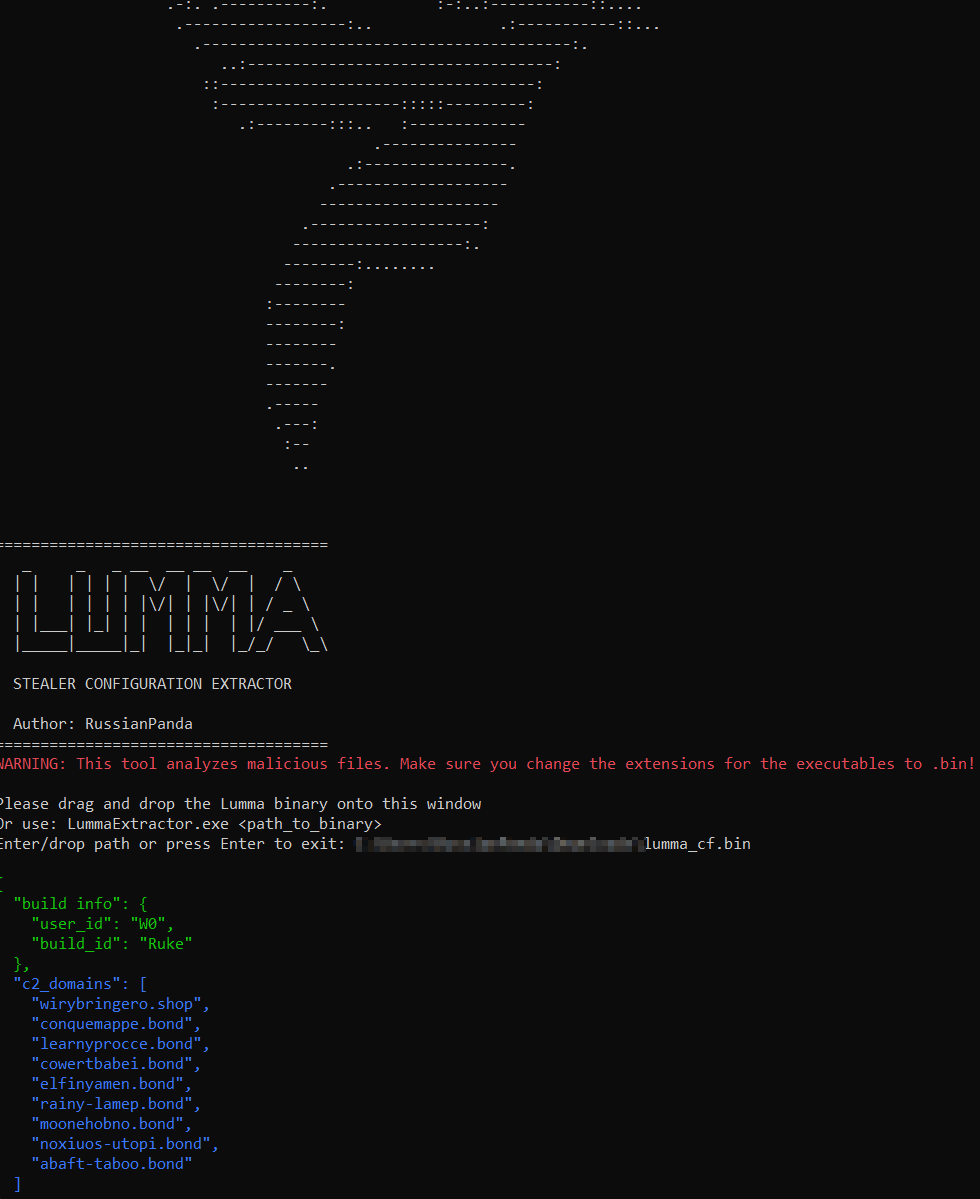
Happy Friday, everyone! With recent changes in #LummaStealer - using ChaCha20 for C2 encryption, here is the new config extractor in C/C++. We will try a different approach this time 🐦
Enjoy!
github.com/RussianPanda95…
English
Faraday retweetledi
Ensure the client config "c:\programdata\jwrapper-remote access\jwappssharedconfig\serviceconfig.xml" does not have malicious entries within the <ConnectTo> tag. This allows the agent to be used remotely from multiple domains/IPs.
virustotal.com/gui/ip-address…
English
@HuntressLabs SOC is seeing further malicious activity from SimpleHelp RMM. Please update your SimpleHelp instance to its latest version!
IOCs in replies:

English