

StubZero: $148,337 RCE in Google Cloud Production brutecat.com/articles/googl…
turb0
69 posts

@7urb01
CTBB Full-Time Hunters' Guild Member | JavaScript Survivor | /((de)?bu(g+)?(ing)?)?/i Bits, bytes, and bad ideas https://t.co/0iE5bU4CjX


StubZero: $148,337 RCE in Google Cloud Production brutecat.com/articles/googl…

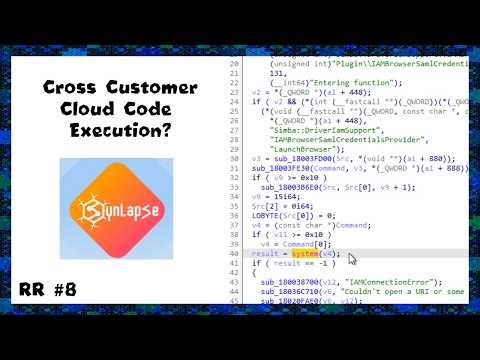
One attacker vector closed, addt’l hardening recommended for #SynLapse. Here’s the full technical details in our latest post. Special thanks to Orca Security Researcher @TzahPahima for this important discovery that improves cloud security! orca.security/resources/blog…

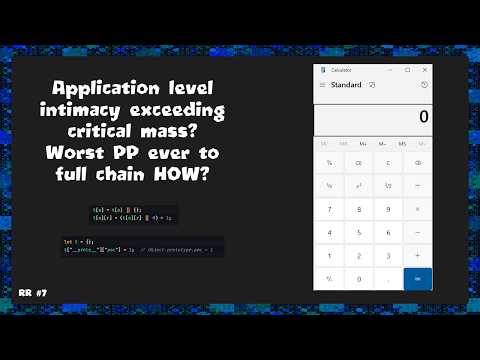
Running a Figma plugin is enough to land cross-platform zero-click RCE on Figma Desktop... Read the writeup on the Critical Research Lab lab.ctbb.show/research/figma… And thanks @Dav3nn for the incredible post, what an amazing chain! =)

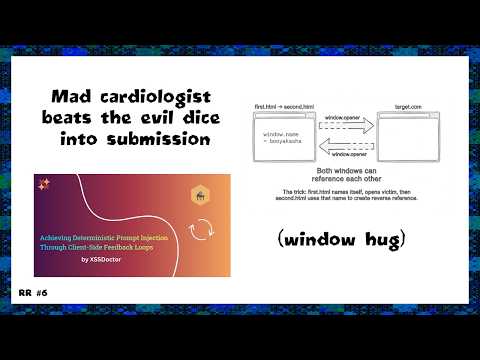
This time we have a guest blog from @xssdoctor, showcasing a new technique in AI hacking to achieve more consistent exploitation. This was initially a research collision, but XSSDoctor masterfully exploited this in the wild. Link below 👇

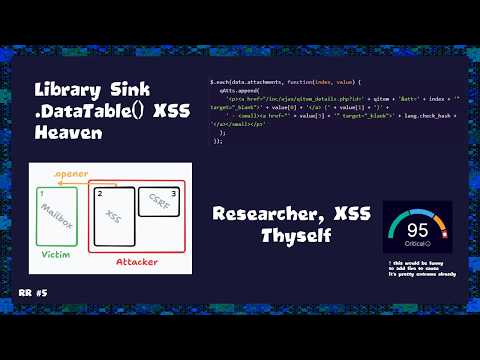
New blog post is out! A few vulnerabilities in Mailcow. A critical unauthenticated XSS, and another interesting Self-XSS escalation involving a Login CSRF with a leftover tab. Check it out: aikido.dev/blog/xss-vulne…




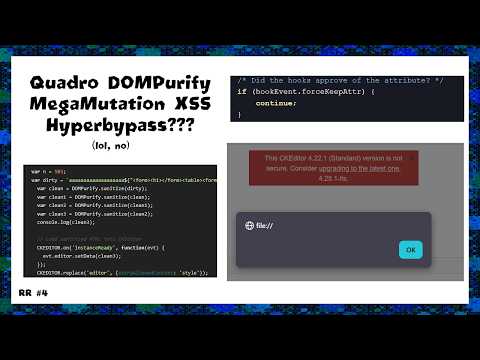
Last year I found a MXSS (dream) bug in a Mail app,it involved bypassing 2 consecutive sanitizers recursive Dompurify calls plus CKEditor.Hope you will like it sudistark.github.io/2026/04/07/mxs… All thanks to @kevin_mizu for putting such great content around mxss and those bypasses🙇♀️

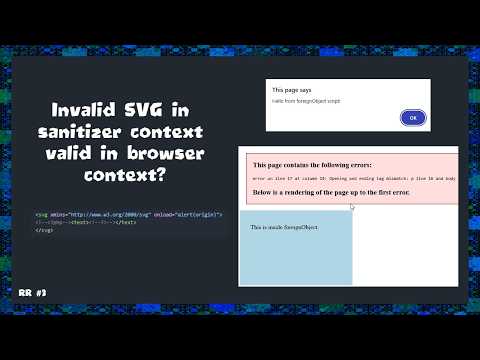
Fun parser differential to fallback SVG sanitizer bypass: github.com/freescout-help…

🗣️ ʜᴀᴘᴘᴇɴɪɴɢ ᴛʜɪ𝘴 ᴡᴇᴇᴋ! 𝗧𝗵𝗲 𝗕𝘂𝗴 𝗛𝘂𝗻𝘁𝗲𝗿’𝘀 𝗠𝗲𝘁𝗵𝗼𝗱𝗼𝗹𝗼𝗴𝘆 (𝗧𝗕𝗛𝗠) — 𝗟𝗜𝗩𝗘 Join Jason Haddix as he shares on what’s actually working in 2026. Inside: • Live testing against real-world targets • Automation + workflow optimization • Direct access to experienced bug hunters • Ongoing Discord community 📅 April 8–10 ⏰ 10AM–5PM MST Last chance to jump in. 🔗 arcanum-sec.com/training/the-b…



@xssdoctor's CSPT research covers eight frameworks: lab.ctbb.show/research/the-d… React Router's .replace(/%2F/g, "/") in matchPath has no i flag, so double-decode only works when the F in %252F is uppercase. This was reintroduced after a previous fix and is still in the codebase. Splat routes (path="files/*") match with (.*) instead of ([^\\/]+), so ../../admin works with zero encoding. Next.js uses the same await params API in page components and route handlers but they do opposite things. Page components re-encode through getParamValue(), route handlers fully decode through getRouteMatcher(). The traversal lands server-side. Ember's normalizePath() re-encodes % after decoding, which accidentally kills double-encoding. Wildcard params skip the final decodeURIComponent entirely, so they need literal ../ instead of encoded payloads. SvelteKit's param matchers reject bad values at the routing level before any load function even runs. Server load functions in +page.server.ts bypass hooks.server.ts, so auth middleware won't protect you. Nuxt's island component payload revival (revive-payload.client.js) is a stored CSPT sink. If you can poison window.__NUXT__, the key traverses the $fetch URL. (CVE-2025-59414)

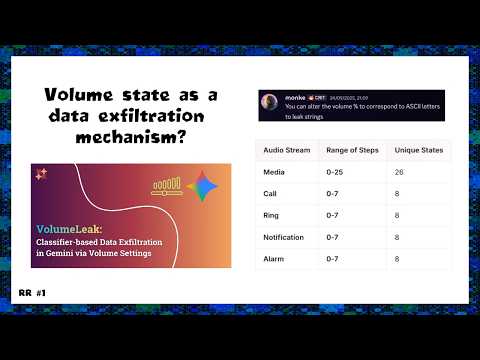
We took things further in hacking Gemini, and exfiltrated data via... volume settings! We also present a new technique for data exfiltration in LLM-based systems. Enjoy 🔥 Link in comments:


Just wait until they figure out what else is buried there

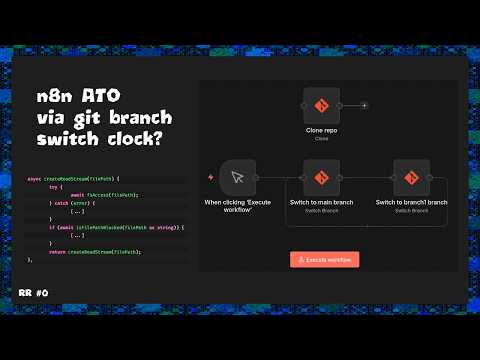
The Research Lab is on fire this week, we just got a new writeup from SharkazFR: - TOCTOU race condition leads to full ATO on popular open source automation platform n8n lab.ctbb.show/writeups/tocto…