Sabitlenmiş Tweet
Adebola Ayobami
3.8K posts


Adebola Ayobami
@Adebhay
Network & Security Engineer | Cybersecurity | IT Consultant | Forex Trader | Man UTD🛑
192.168.0.1 Katılım Mart 2015
1K Takip Edilen1.5K Takipçiler

Love the creativity behind this!!!
Akeem olayiwola@Akeemolayiwola9
Introducing LEO Assistant — Your AI-Powered Study Partner Tired of re-reading the same articles/documentations/notes over and over? LEO flips the script. hello-bot--akeemolayiwola9.replit.app #Buildhathon #EdTech #AI #StudySmart #LEOAssistant #Replit #FranciscoJacome @web3bridge
English

@the__tomiwa Okay.. But Tinubu can be ?
Na all of us dey suffer am sha
English

@OnijeC Network Engineer but grey hair is already playing around my head 😞
English
Adebola Ayobami retweetledi

I love what the networking community has been doing in terms of building relationships and helping network engineers have a sense of belonging
Kudos to @Adebhay and co❤️
English

@akintunero @OnijeC I will be there..
I will gladly choose ThousandEyes over solarwinds abeg. Meraki is a good food to try as well
English

How far @OnijeC make we cook Meraki and ThousandEyes food soon big Idan… what do you say?
English

@Archimeokey @trigottista @dayoisreal I think you should check the meaning of forensic..
He has more understanding of the concept than your claim..
He explicitly explained the loopholes in the so-called forensic and you are here acting like a prof with zero knowledge and understanding...
English

@trigottista @dayoisreal You are ode
Do you know what forensic means
Investigation from the deep or background not from what you can see.
Victory is sure was not the original comment
English

I am back again my dear INEC 😂
Your point 2 on screenshot one says and I quote “Timestamp analysis shows the alleged 2026 reply,
'Victory is sure', was posted 13 minutes before the original post by @dayoisreal. This is physically impossible on any digital platform”(screenshot attached) 😂
LEMME PROVE THAT TO YOU AND DESTROY YOUR “Forensic Claim number 2”
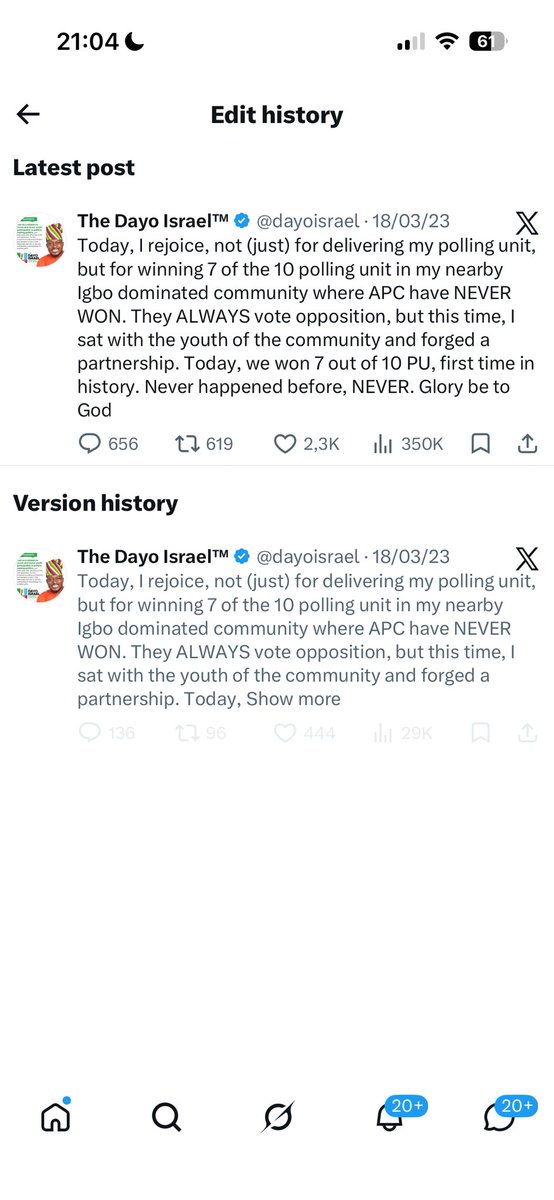
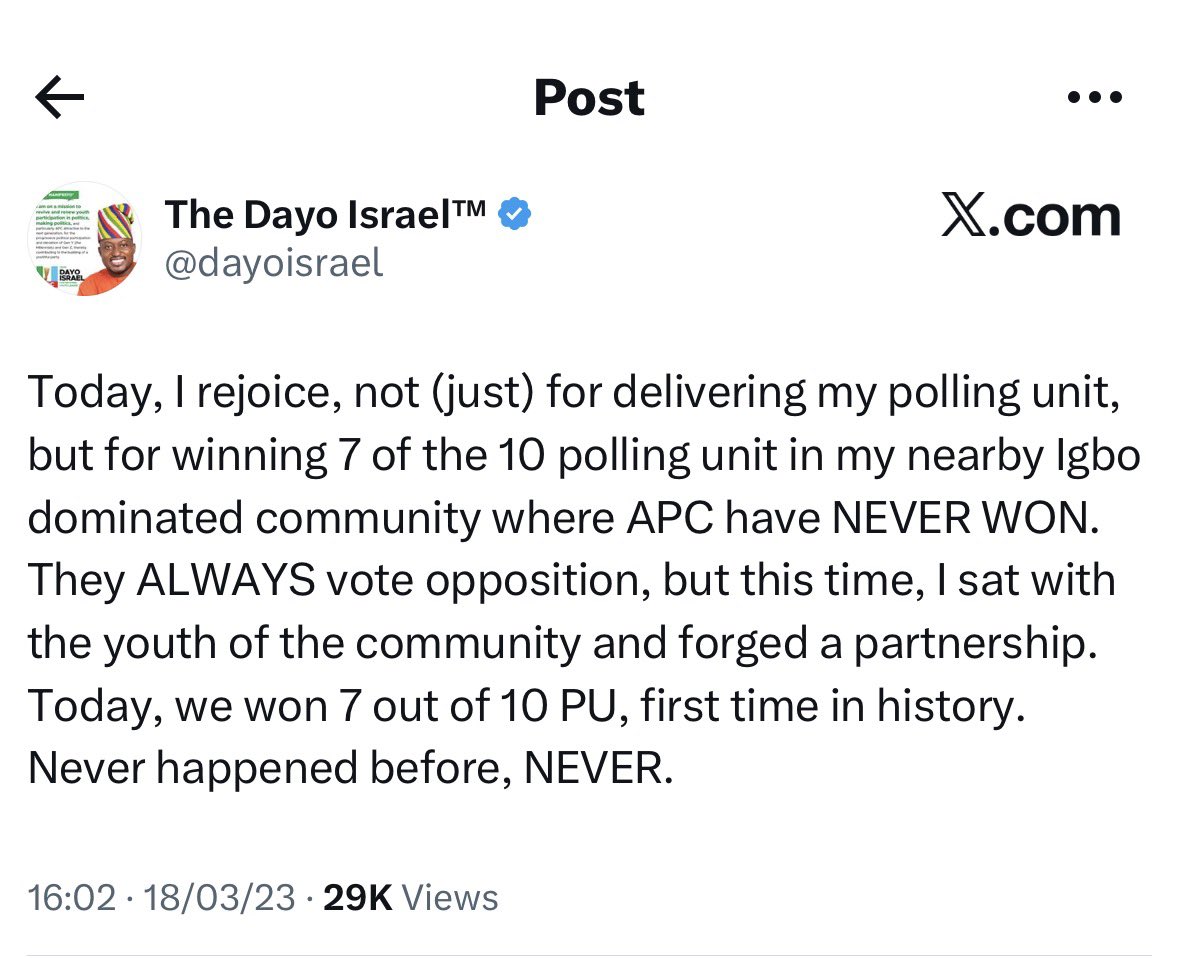
Well, your “forensic experts” didn’t tell you that @dayoisrael made the post on 18/03/2023 at 16:02, @joashamupitan commented at 16:05(screenshot 2 attached)
At 16:18, @dayoisrael edited the tweet and added the following words “Glory be to God” to his initial tweet at 16:02, which ended with the following “Never happened before, NEVER. (Screenshot 3 shows edit history”
You can take a look at @dayoisrael’s original tweet at 16:02 in screenshot 4

INEC Nigeria@inecnigeria
PUBLIC STATEMENT FABRICATED X (TWITTER) ACCOUNT OF PROF. JOASH AMUPITAN, SAN
English

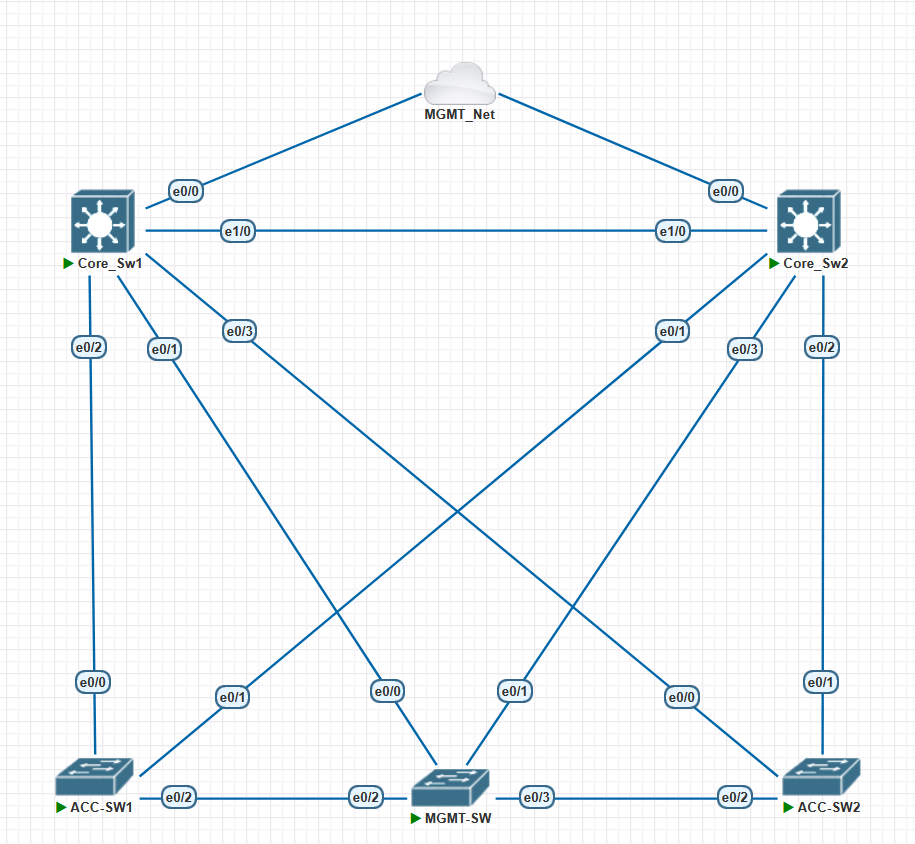
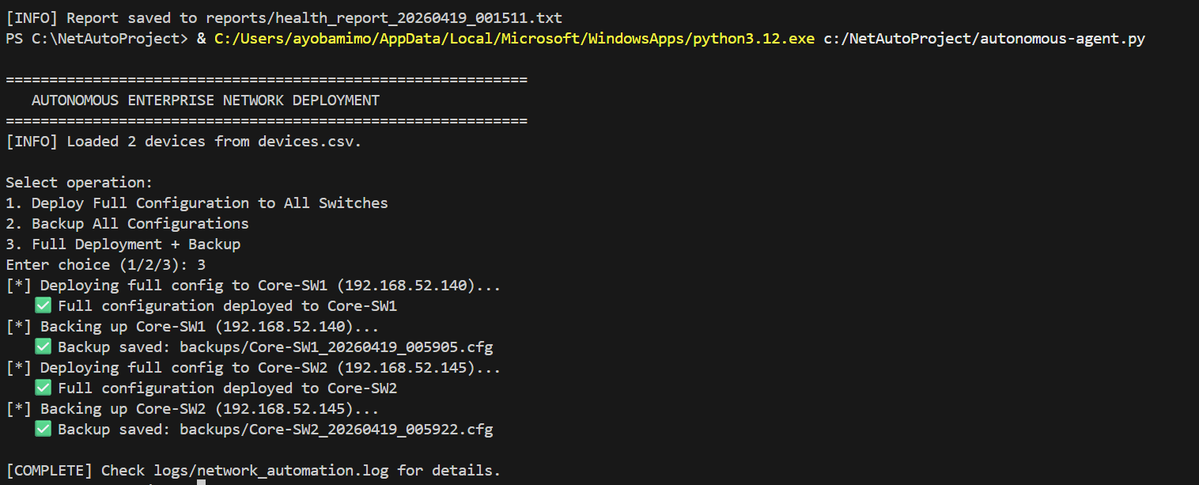
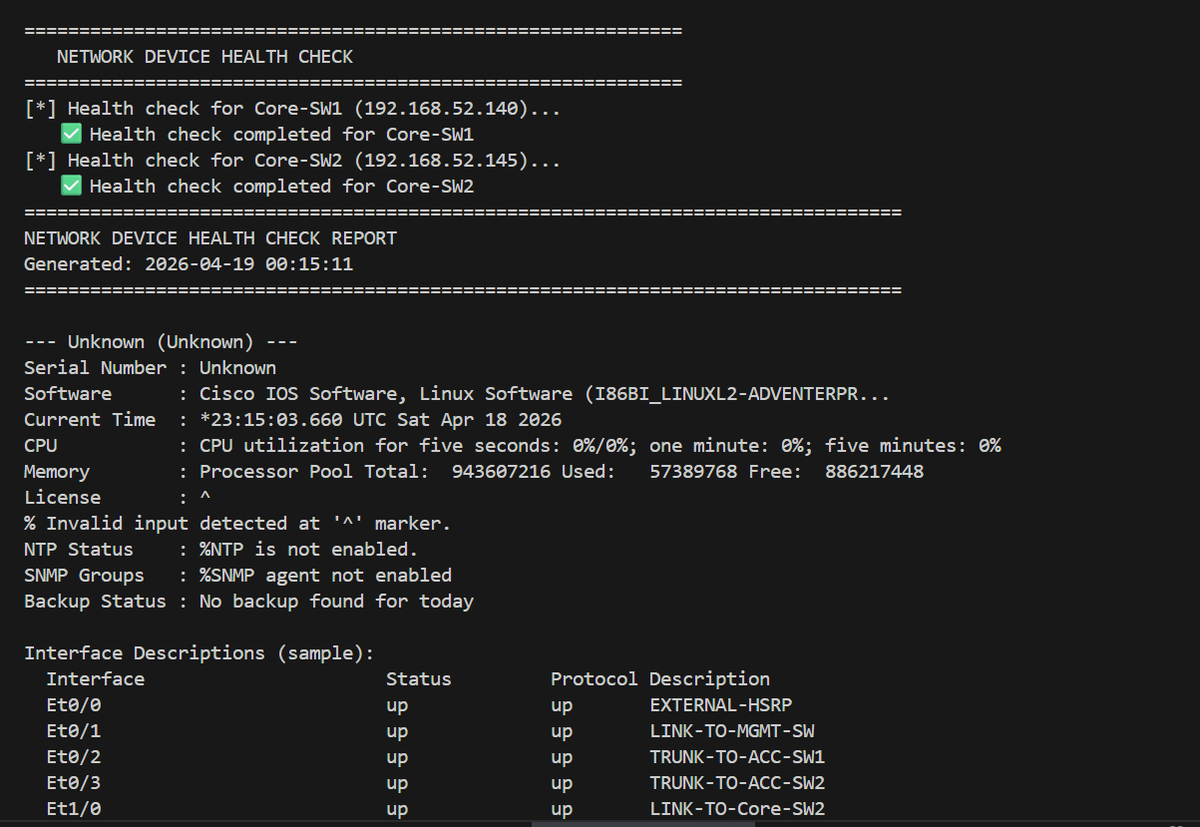
* The hardest part isn't the code, it's designing the workflow and handling edge cases.
* Out‑of‑band management is non‑negotiable for true operational resilience.
🔗 You can get the full project walkthrough on GitHub 👇 lnkd.in/eK5d-R_2
English
Adebola Ayobami retweetledi

𝗘𝗣𝗜𝗦𝗢𝗗𝗘 𝟮𝟭 (𝗙𝗜𝗡𝗔𝗟)
𝗣𝗖𝗜-𝗗𝗦𝗦 𝗶𝗻 𝗢𝗻𝗲 𝗦𝗶𝗺𝗽𝗹𝗲 𝗦𝘁𝗼𝗿𝘆: 𝗙𝗿𝗼𝗺 𝗖𝗵𝗮𝗼𝘀 𝘁𝗼 𝗖𝗼𝗻𝘁𝗿𝗼𝗹
This is the final episode of the PCI-DSS Deep Dive Series. Over the past few weeks, we've covered:
• The chaos before PCI-DSS
• Why it was created (December 2004)
• What card data actually is
• Who must follow the rules
• The 12 essential security habits
• Real-world breaches & how attackers operate
• How companies protect data
• The professional roles behind the standard
𝗧𝗵𝗲 𝗢𝗿𝗶𝗴𝗶𝗻 𝗦𝘁𝗼𝗿𝘆
PCI-DSS was born because, when businesses first started accepting credit card payments, they faced a massive challenge: they didn't know how to protect them.
Attackers didn't wait for anyone to get organized. They exploited the weakness, stole information, and sold it. Customers lost money, banks lost trust, and businesses faced total chaos.
Then, in December 2004, the major brands like Visa, Mastercard, American Express, Discover, and JCB did something unexpected. They stopped competing and started collaborating to combat this threat. After all, "the enemy of my enemy is my friend." They created one shared rulebook: PCI-DSS.
𝗧𝗵𝗲 𝗥𝘂𝗹𝗲𝗯𝗼𝗼𝗸
PCI-DSS came with one simple, but non-negotiable rule: If you handle credit card data, protect it like the money in your vault.
This proved to be a game-changer as businesses began to:
• Lock their systems: Firewalls and strong passwords.
• Hide data: Robust encryption.
• Replace sensitive data: Tokenization.
• Limit access: Only the right people get in.
• Monitor activity: Logs and real-time alerts.
• Train employees: Building a human firewall.
Security finally became structured.
𝗧𝗵𝗲 𝗥𝗲𝗮𝗹𝗶𝘁𝘆 𝗖𝗵𝗲𝗰𝗸
However, despite the rules, breaches still happen. Why? Usually, it’s the human factor. People love shortcuts, and to some, security is just too tiring. Systems that are supposed to be maintained are ignored. Data is stored unnecessarily, and access is left too wide open.
PCI-DSS is not just a standard, it’s a mindset:
• Protect only what you need.
• Limit who can access it.
• Watch everything.
• Never get comfortable.
Attackers only need you to make one mistake. PCI-DSS exists to protect your card, your money, and your trust by moving us from a world with no rules to a system built on shared responsibility.
𝗪𝗵𝗮𝘁’𝘀 𝗡𝗲𝘅𝘁?
I’ll be dropping an extensive article very soon, combining everything we’ve covered with deep technicalities. This will serve as a resource for anyone in GRC, those looking to break into the field, or anyone who wants to master PCI-DSS truly.
The Next Standard: We will be shifting gears from protecting card data to protecting all data. Our next deep dive will be the powerhouse standard: ISO 27001. While PCI-DSS focuses on specific organizations, ISO 27001 touches almost every establishment on earth. Its importance cannot be overstated.
Stay tuned for the article and the commencement of the ISO 27001 Deep Dive Series!
If you are interested in reading all the episodes, you can find them here: x.com/Damm_cyber/sta…
#CyberSecurity #PCIDSS #GRC #InfoSec #DataPrivacy

English
Adebola Ayobami retweetledi

Don't let THIS Monday be the one you regret.
Secure your week!
#Cybersecurity
#Cyberadnation

English