
AegisWeb3
1.4K posts


AegisWeb3
@AegisWeb3
AegisWeb3• A @PeckShield Formation| Guard your assets with multi-dimensional protection



Software horror: litellm PyPI supply chain attack. Simple `pip install litellm` was enough to exfiltrate SSH keys, AWS/GCP/Azure creds, Kubernetes configs, git credentials, env vars (all your API keys), shell history, crypto wallets, SSL private keys, CI/CD secrets, database passwords. LiteLLM itself has 97 million downloads per month which is already terrible, but much worse, the contagion spreads to any project that depends on litellm. For example, if you did `pip install dspy` (which depended on litellm>=1.64.0), you'd also be pwnd. Same for any other large project that depended on litellm. Afaict the poisoned version was up for only less than ~1 hour. The attack had a bug which led to its discovery - Callum McMahon was using an MCP plugin inside Cursor that pulled in litellm as a transitive dependency. When litellm 1.82.8 installed, their machine ran out of RAM and crashed. So if the attacker didn't vibe code this attack it could have been undetected for many days or weeks. Supply chain attacks like this are basically the scariest thing imaginable in modern software. Every time you install any depedency you could be pulling in a poisoned package anywhere deep inside its entire depedency tree. This is especially risky with large projects that might have lots and lots of dependencies. The credentials that do get stolen in each attack can then be used to take over more accounts and compromise more packages. Classical software engineering would have you believe that dependencies are good (we're building pyramids from bricks), but imo this has to be re-evaluated, and it's why I've been so growingly averse to them, preferring to use LLMs to "yoink" functionality when it's simple enough and possible.

We’re currently investigating a potential malicious event affecting the Neutrl front end. Our team is actively investigating. Out of an abundance of caution, please do not interact with the website until further updates are provided.

🚨 GM all, we’re detecting unusual activities from our legacy account @binancelabs. For your safety, please unfollow the old account and avoid interacting with any posts, links, or DMs from that handle. ✅ @yzilabs and @easyresidency remain fully secure and are your verified sources for all comms & updates from us on X. Your security is our top priority. Stay SAFU everyone.




NEW: Major investigation dropping February 26 on one of crypto’s most profitable businesses where multiple employees abused internal data to insider trade over a prolonged period of time.





🚨 Scam Alert: $Animals — Same Rug Pull Factory as $Horse & $VC ⚠️ A new token called $Animals just popped up, and the on-chain fingerprints are obvious. 🔍 Here’s the link: solscan.io/token/98uAmduq…





To all X-Player players: The platform was maliciously attacked by a flash loan today. We are deeply sorry and take full responsibility for this incident. The platform will make every effort to recover all losses caused by the attack and minimize player losses as much as possible



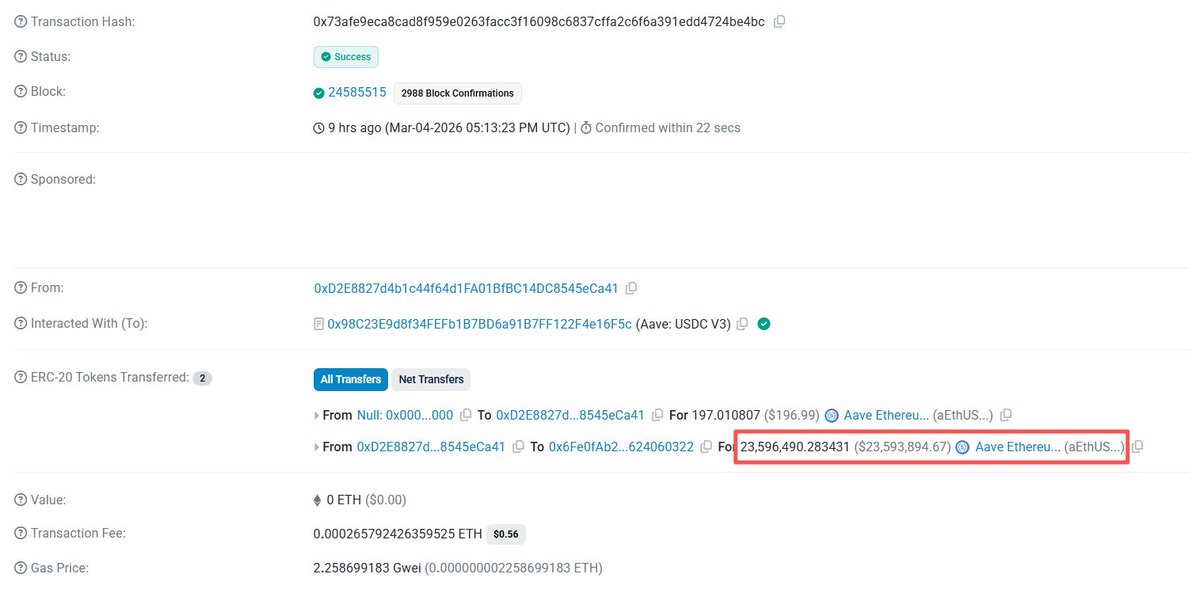
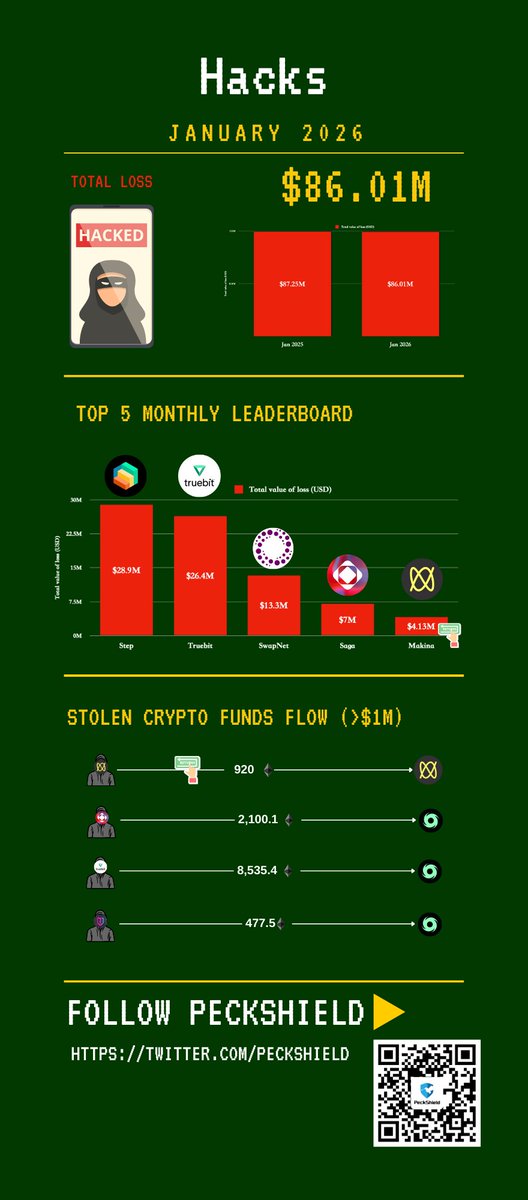
Jan 22, 2026, 13:15 UTC: Funds held by the MEV builder have been returned net of a 10% bounty awarded under the SEAL Whitehat Safe Harbor. This represents approximately 920 ETH of the 1,023 ETH received by the MEV builder, out of a total exploit amount of roughly 1,299 ETH. This is a very positive step toward recovery. etherscan.io/tx/0x0d23fea54… Recovered funds have been transferred to a dedicated recovery multi-sig: 0xc22F7346eaF4340f51513bF9f01e5d722E558AB9 Our priority remains to actively pursue recovery of the additional funds. We will announce the distribution method and timeline for any recovered funds as soon as practical. We are still working at establishing contact with 0x573Db3Aed219EfD4D2cDABC0D00366E7B80F910E, the @Rocket_Pool Validator that received approximately 276 ETH as a result of the exploit. If you possess any information on how to get in direct contact with this person/entity then please direct a message through official channels to the Makina Team or email us as security@makina.finance. This remains an ongoing process and additional updates will be shared as more information becomes available. Special thanks to the MEV builder (0xbed) for being prompt in communication and helping those affected in the DUSD/USDC Curve pool exploit.


Today, we became aware of a security incident involving one or more malicious actors. The affected smart contract is 0x764C64b2A09b09Acb100B80d8c505Aa6a0302EF2 and we strongly advise the public not to interact with this contract until further notice. We are in contact with law enforcement and taking all available measures to address the situation. We will share updates through our official channels as they become available.

Update: Only $230k in user funds were affected. Patches and audits will be live by the weekend. Until then, the bot will be offline. Once the bot is online, affected users will see their balances return to pre-hack levels.



Ethereum added $4.2B to lead 2025 net flows



