la cabesa
23 posts


la cabesa retweetledi
la cabesa retweetledi

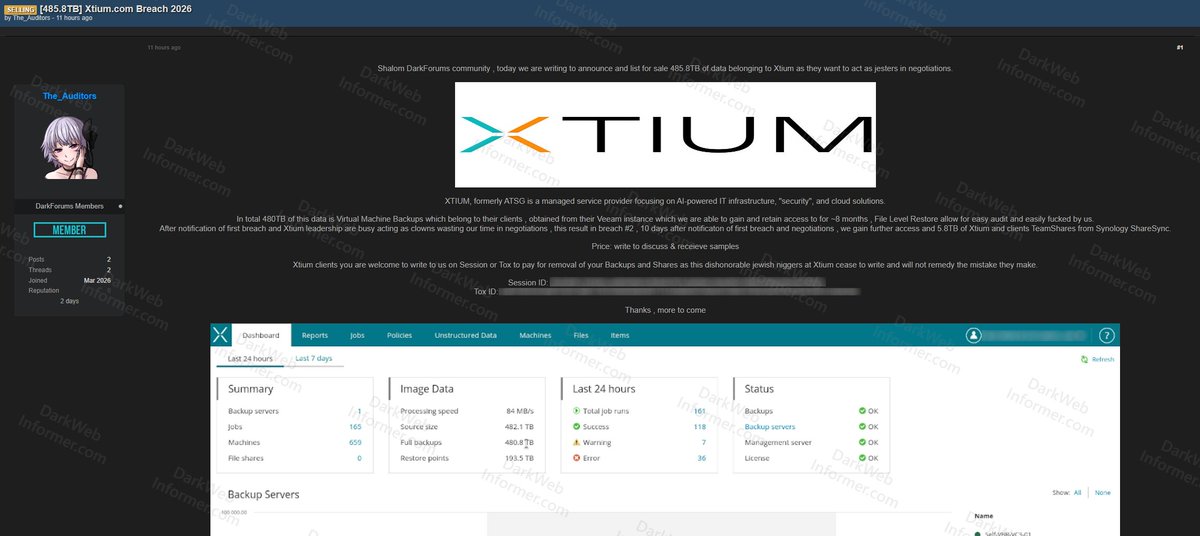
‼️🇺🇸 MASSIVE CLAIM: Xtium (formerly ATSG) allegedly has data exposed on a popular cybercrime forum with 485.8TB of data allegedly stolen.
Threat Actor: The_Auditors
Category: Breach
Victim: Xtium
Industry: Managed IT Services / Cloud Solutions
Site: xtium.com
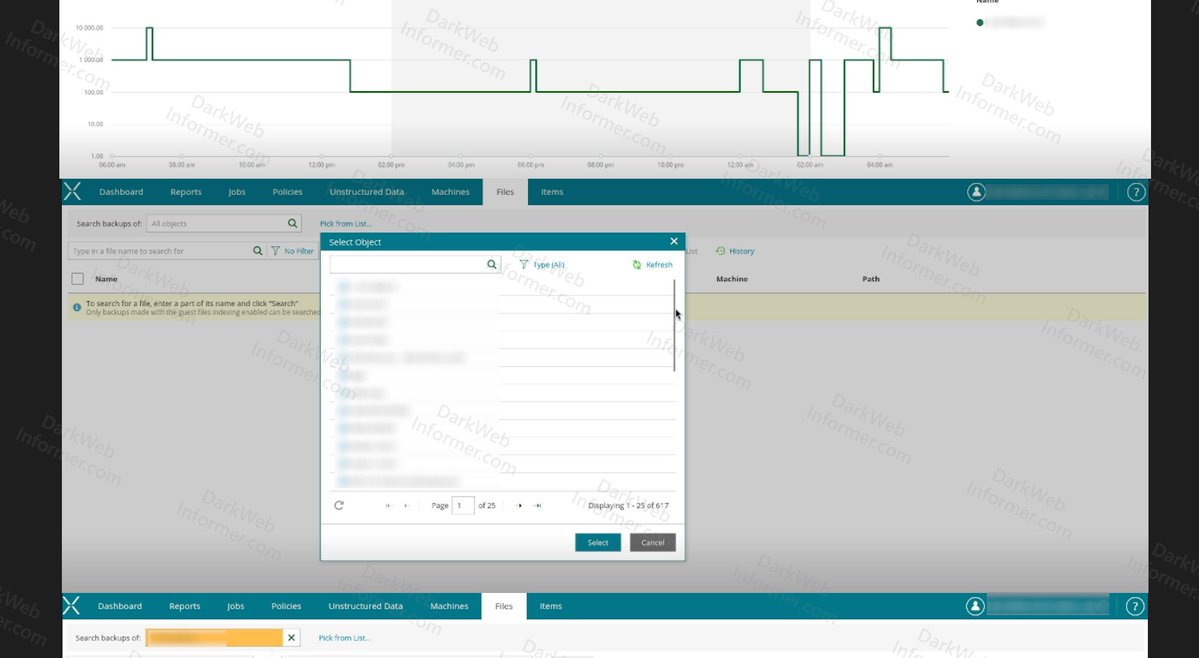
Threat actor claims to have obtained 485.8TB of data from Xtium's Veeam backup instance, which they maintained access to for approximately 8 months. The data consists of virtual machine backups belonging to Xtium's clients.
After the first breach was disclosed and negotiations allegedly stalled, the threat actor claims to have conducted a second breach 10 days later, gaining further access to an additional 5.8TB of Xtium and client TeamShares from Synology ShareSync.
Proof includes screenshots of the Veeam dashboard showing 659 machines, 482.1TB source size, 480.8TB full backups, and 193.5TB of restore points. Additional screenshots show access to Xtium's Sync Synergy file sharing platform with 912 accounts, 56 organizations, 3,579,156 files, and client organizations including BC2, Atlantic Fall Protection, Indecom, and Premier Mounts.
A negotiation chat screenshot shows Xtium's management responding to the threat actor's demands.


English
la cabesa retweetledi

🚨 CRITICAL ALERT: Massive Leak of Identity Documents and KYC Data (Global) 🌍📂
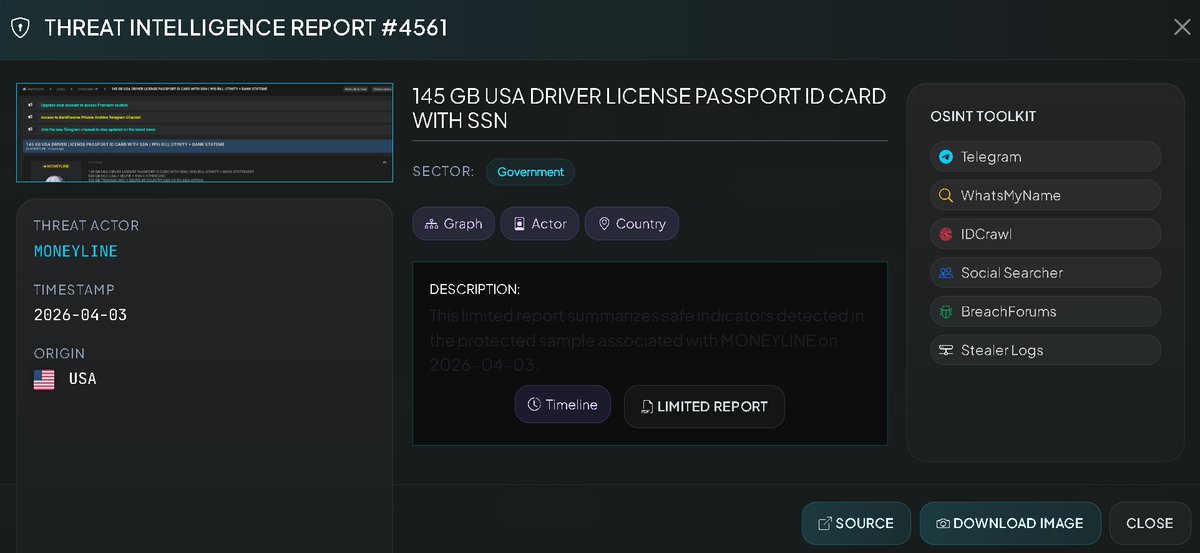
Analyzer has detected one of the largest releases of identity and verification (KYC) documents so far in 2026. The threat actor MONEYLINE has released nearly a Terabyte of sensitive information that compromises the financial and personal security of citizens in over 45 countries, with a massive focus on the United States.
🎭 Threat Actor: MONEYLINE.
📂 Total Volume: Approximately 965 GB of documents.
🗓️ Detection Date: April 3, 2026.
🔹 Passports, Licenses, and SSNs (W-9s).
🔹 Verification selfies and bank statements.
🔹 300 GB of exposed Transak user data.
🌍 Scope: Global (45 countries, including the USA, UK, European Union, Asia, and Africa).
🛠️ Compromised Information (Critical-Level PII)
The leak is divided into three main packages of extremely sensitive data:
🇺🇸 USA ID & Bank Package (145 GB):
Driver's licenses, passports, and ID cards.
Social Security Numbers (SSNs) and W-9 forms.
Utility bills and bank statements.
📸 USA Selfie & Doc Package (520 GB):
Selfie-style photographs linked to identity documents and SSNs.
Additional unspecified documentation for identity verification.
🌐 Global Transak Package (300 GB):
Documents and selfies belonging to users of the Transak platform.
Affects citizens of 45 countries across multiple continents.
Monitor: analyzer.vecert.io
#Cybersecurity #IdentityTheft #Transak #SSN #DataBreach #KYC #InfoSec #CyberAlert #BreakingNews
English
la cabesa retweetledi

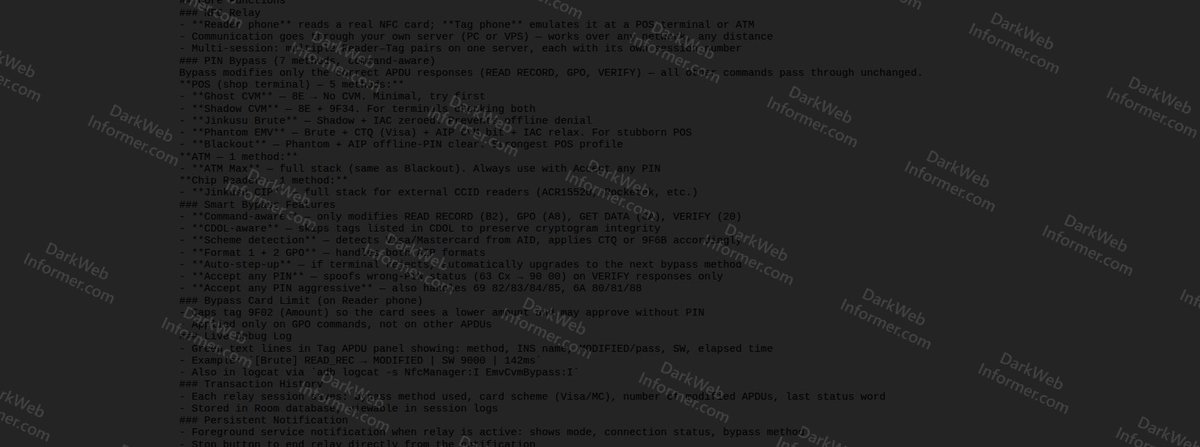
‼️ I have posted about this tool before, but this is a new forum post.
A threat actor advertising NFC RIPPER, an Android toolkit for conducting NFC relay attacks against payment terminals and ATMs.
The tool enables PIN bypass through multiple methods and allows remote card emulation for fraudulent transactions.

English

Payload of the Week // Enigma-XSS tool
Quite technical this week but understanding HOW XSS works is the secret... blind fuzzing is a lottery.
So... this is a genuine XSS from one of my older reports.
Input reflected inside a , inject a new element OUTSIDE the JS context:
 The browser's HTML parser sees first — it terminates the script block before the JS engine ever evaluates the string.
The
The browser's HTML parser sees first — it terminates the script block before the JS engine ever evaluates the string.
The ![]() tag is parsed as fresh HTML. onerror fires. Game over.
524 events. 33 seconds. Fully autonomous, adapting at every turn.
Takeaway: quote encoding protects the JS context but not the HTML context. Defence needs both — or better yet, don't use innerHTML.
labs.trace37.com/posts/enigma-x…
tag is parsed as fresh HTML. onerror fires. Game over.
524 events. 33 seconds. Fully autonomous, adapting at every turn.
Takeaway: quote encoding protects the JS context but not the HTML context. Defence needs both — or better yet, don't use innerHTML.
labs.trace37.com/posts/enigma-x…

English
la cabesa retweetledi

Hunting for IDORs: How I Accessed PII on a Popular Ticketing Site by Vansh Rathore @vanshrathore64/hunting-for-idors-how-i-accessed-pii-on-a-popular-ticketing-site-d7aa5f9542f2" target="_blank" rel="nofollow noopener">medium.com/@vanshrathore6… #bugbounty #bugbountytips #bugbountytip
English
la cabesa retweetledi

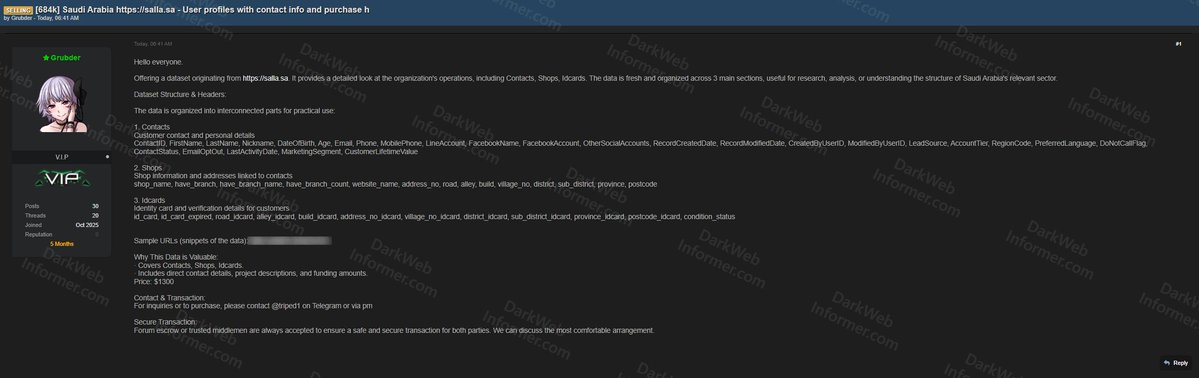
‼️🇸🇦 A dataset allegedly originating from Salla.sa, a Saudi Arabian e-commerce platform, containing 684,000 records is being sold on a popular cybercrime forum.
▪️ Records: 684K
▪️ Price: $1,300
The data is organized across three main sections:
▪️ Contacts (Customer Personal Details): ContactID, first/last name, nickname, DOB, age, email, phone, mobile phone, Line account, Facebook name/account, other social accounts, record created/modified dates, created/modified by UserID, lead source, account tier, region code, preferred language, DoNotCallFlag, contact status, email opt-out, last activity date, marketing segment, customer lifetime value
▪️ Shops (Shop Info & Addresses): Shop name, branch status/name/count, website name, address number, road, alley, build, village number, district, sub-district, province, postcode
▪️ ID Cards (Identity & Verification): ID card number, expiry, road/alley/build/address/village/district/sub-district/province/postcode (all ID card specific), condition status
English

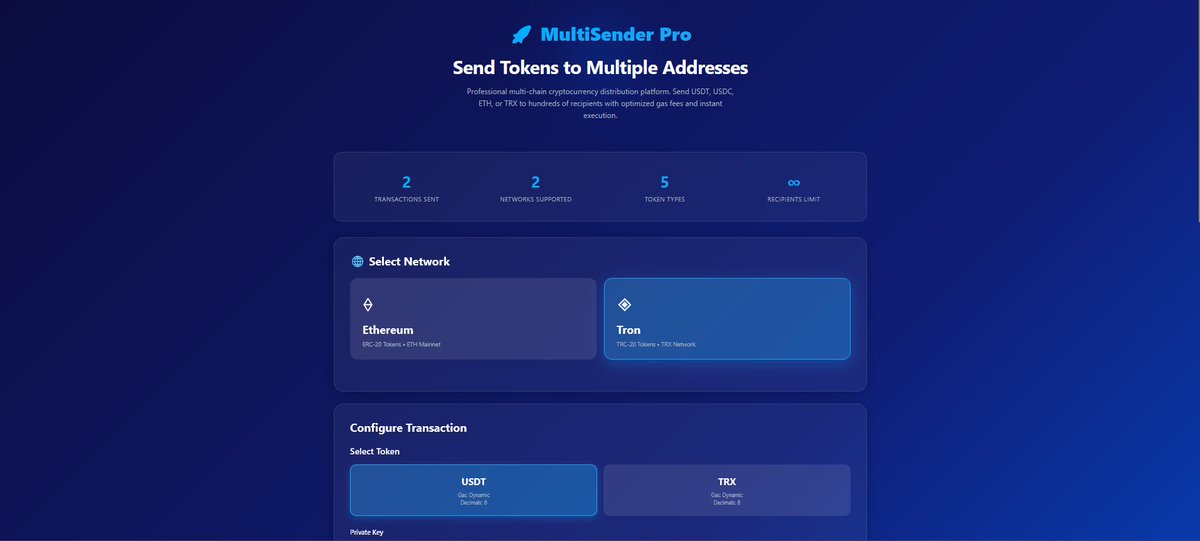
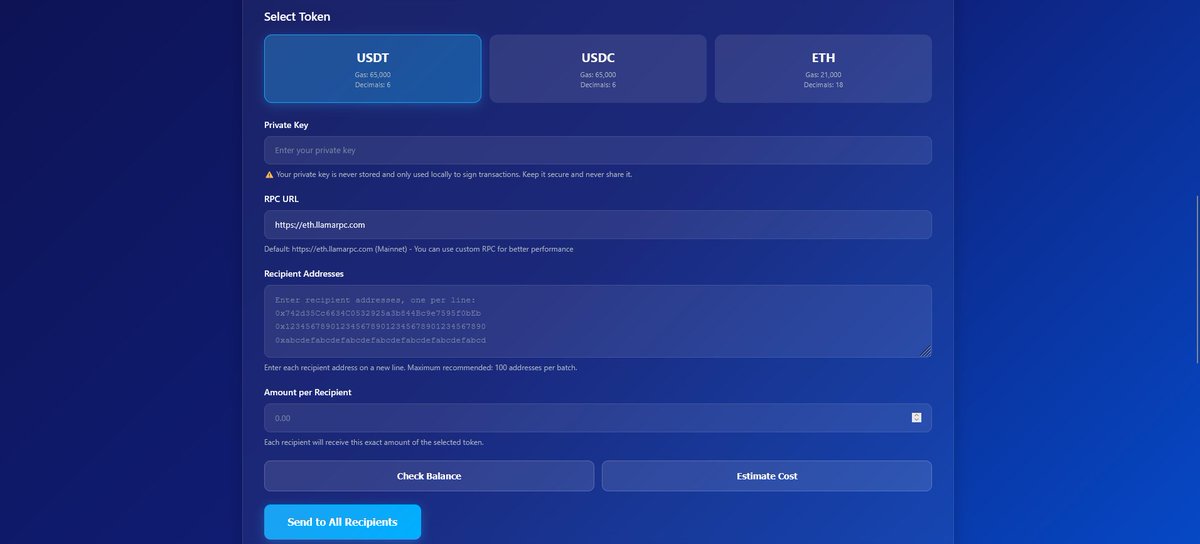
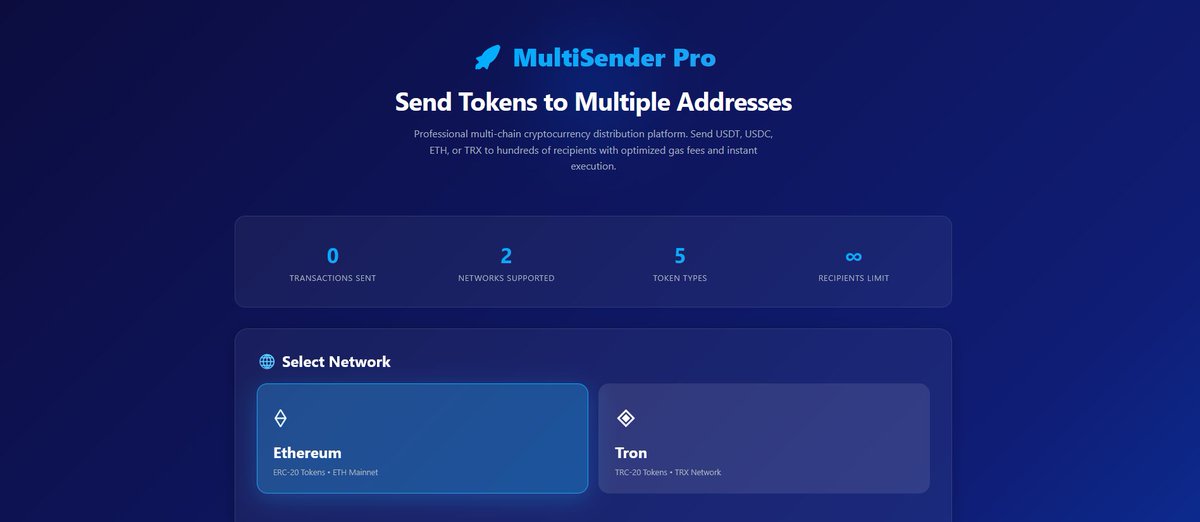
Hello Web3 investors, DAOs, and NFT creators 👋
#Web3
#Crypto
#Blockchain
#Ethereum
#Tron
#VanityWallet
#MultiSend
#TokenDistribution
#NFTCommunity
#DAOs
English