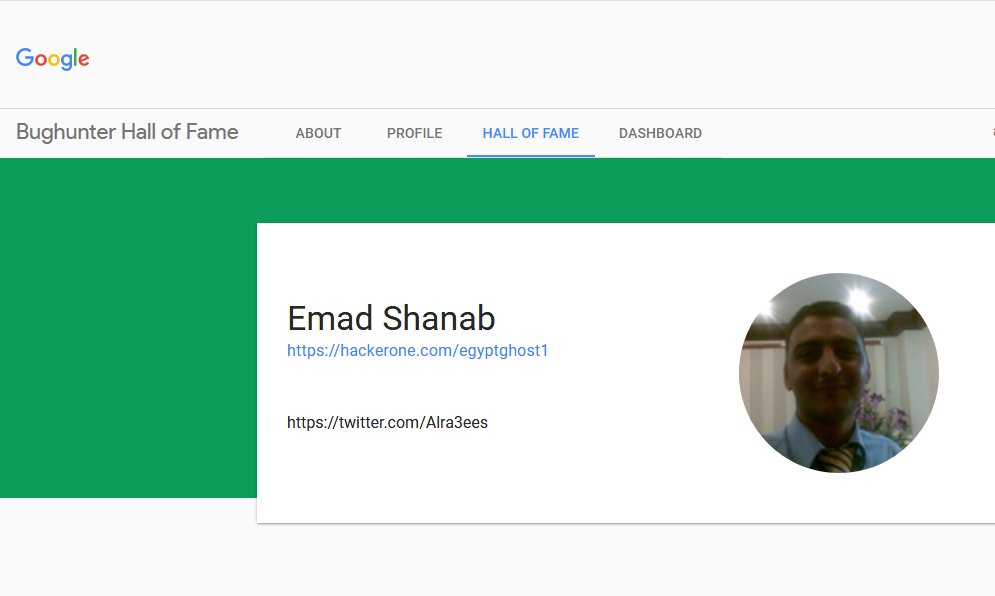
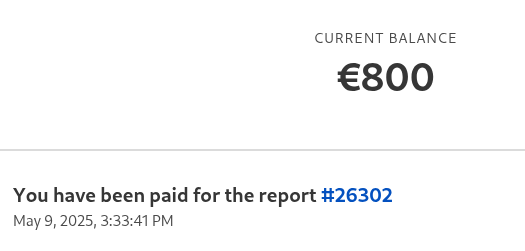
Emad Shanab - أبو عبد الله
16.4K posts
Emad Shanab - أبو عبد الله
@Alra3ees
Father | Lawyer | Bug Bounty Hunter | Complete newbie | Every Law has its own Bugs. https://t.co/Cwuy2zfF8N https://t.co/Bd9ltJWS5X
If you have found port 8009 opened,try Ghostcat read file/code execute,CNVD-2020-10487(CVE-2020-1938) You can read and write files on the server. Run nmap on your targets file to find port 8009. The exploit is available here:- Best of luck. #bugbountytips github.com/00theway/Ghost…
New reports submitted today. 5 SQLi. 1 DOM-based XSS. 1 XSS-reflected. 3 Information Disclouser.



I have submitted three SQLi reports today to a self hosted bug bounty program. Hopefully they can fix it soon. If you can’t find anything on bug bounty platforms, try external programs, to avoid burnout.
Automate bug bounty. SQLI - XSS - LFI waymore -i urls | tee urls-his cat urls-his | gf sqli |urless| anew sqli cat urls-his | gf xss | urless|anew xss cat urls-his | gf lfi | urless|anew lfi ghauri -m sqli --confirm --batch --level=3 -b knoxnl -i xss -X BOTH python3 lfimap.py -F lfi --use-long -a --no-stop Use -x Exploit and send reverse shell if RCE is available Tools:- github.com/xnl-h4ck3r/way… github.com/r0oth3x49/ghau… github.com/xnl-h4ck3r/kno… github.com/hansmach1ne/LF… github.com/xnl-h4ck3r/url… knoxss.pro



Vibe coding? Nah, Hacking with a vibe 🌆🗽