Labman retweetledi
Labman
16.6K posts


Labman
@Amarjit_Labu
Lover of breaking things | Cybersec researcher with a wide taste in music genres!! https://t.co/AOHvviQE9r ||| chr°ᶰ1k |||
Ring3 making my way to Ring0 Katılım Temmuz 2009
1.6K Takip Edilen2.4K Takipçiler
Labman retweetledi

[RELEASE] Better late than never! Part 3 is out! Fantastic unwind information and where to find them. We went digging through .pdata, RTF Lookups, and a few ntdll internals that probably weren't meant to be touched. BYOUD dropping alongside. Enjoy 😉
klezvirus.github.io/posts/Byoud/
English
Labman retweetledi

Using Crystal Palace and AdaptixC2
maorsabag.github.io/posts/adaptix-…
English
Labman retweetledi

Built an evasive CS RL with Crystal Palace that bypasses Elastic EDR.
The evasion lives inside the blob. Not in how it got there.
Blog: lorenzomeacci.com/bypassing-edr-… Source: github.com/kapla0011/Kapl…
English
Labman retweetledi

@filip_dragovic Exploit code available here - github.com/mdsecactivebre…
Français
Labman retweetledi

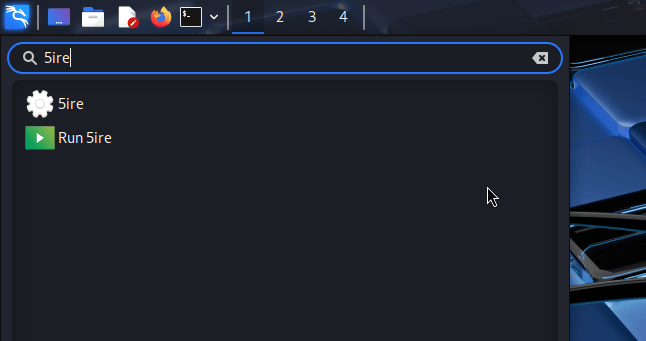
Kali & LLM: Completely local with Ollama & 5ire: We are extending our LLM-driven Kali series, where natural language replaces manual command input. This time however, we are doing everything locally and offline. We are using our own hardware and not… kali.org/blog/kali-llm-…
English
Labman retweetledi
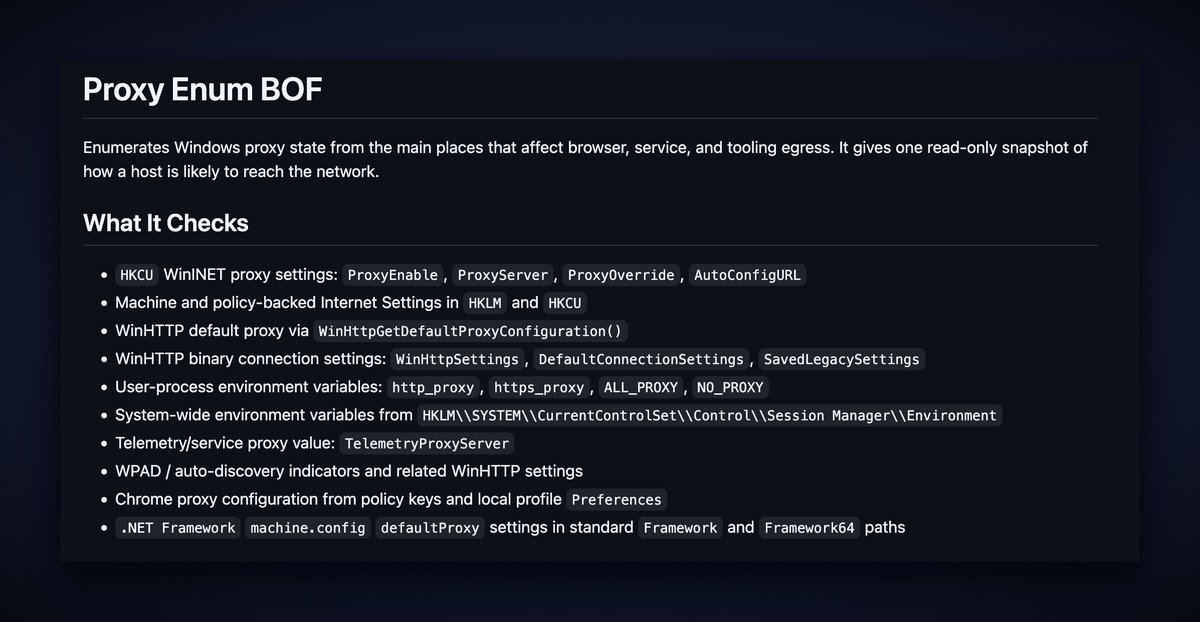
proxy_enum – a BOF that enumerates Windows proxy configuration states: WinINET, WinHTTP, policy keys, environment variables, WPAD indicators, Chrome settings, and .NET defaultProxy values get checked.
Shows how a host is likely to reach the network. Useful for finding egress paths during operations.
BOF in Adrenaline Repo:
github.com/atomiczsec/Adr…
English
Labman retweetledi

The Live Terminal feature of Cortex XDR can be abused by attackers as a pre-installed, EDR-trusted C2 channel
labs.infoguard.ch/posts/abusing_…
#infosec #cybersecurity #redteam #pentest
English
Labman retweetledi

I am releasing a new toolkit I built for IIS-based lateral movement and code execution within IIS worker pool process's memory.
Phantom ASPX Loader & PhantomLink -- a two-part toolkit for reflectively loading native DLLs into IIS w3wp.exe worker processes via ASPX.
github.com/zux0x3a/Phanto…
GIF
English
Labman retweetledi

When you try to harden Windows PrintNotify callbacks, you end up exposing vulnerabilities in other protocols like EPMAP that have been sitting around (or even more) for 20 years
msrc.microsoft.com/update-guide/v…
English
Labman retweetledi

Are one-way trusts really one way? @lowercase_drm sums up how the TDO password lets you turn a one-way AD forest trust into bidirectional access, and releases a new tool to remotely extract these secrets.
offsec.almond.consulting/trust-no-one_a…

English
Labman retweetledi

🔥🐉 New GOAD Lab: DRACARYS
I’ve just released a new free lab environment on GOAD: DRACARYS.
The challenge includes 3 VMs and the objective is simple:
Start with no authentication and work your way up to Domain Admin.
Have fun exploiting it! 🔥🐉
mayfly277.github.io/posts/Dracarys…
English
Labman retweetledi
Giveaway - Our instructor-led advanced bootcamps for sharpening your Red Team skills start this weekend.
Attacking and Defending Active Directory - Advanced Edition (CRTE) starts this Friday.
Advanced Windows Tradecraft - Evasion Techniques for Red Teams (CETP) starts this Saturday.
I am giving away one seat for each of the bootcamps. To participate, please Follow @nikhil_mitt and @AlteredSecurity, Like, Comment and Repost.
We will announce the random winners on Wednesday.
alteredsecurity.com/bootcamps?utm_…
#RedTeam #Evasion

English

@trevorsaudi What's the use case? Are you streaming audio via this setup?
English

Anyone worked with audio before. What’s the cheapest and most efficient way to solve this
stockfish@trevorsaudi
Playing around with STUN/TURN servers with PeerJS. A bit stressful implementing realtime audio relay on the browser
English
Labman retweetledi

Your EDR just coerced itself. 🫠
Drop a crafted LNK → MsSense.exe makes a CreateFile call → machine account hands over its Net-NTLMv2 hash over WebDAV → relay to LDAP → Shadow Credentials or RBCD.
No user interaction. No exotic exploit. Just vibes and a shortcut file.
If you're running Microsoft Defender for Endpoint, this one is literally about you. 👀
Full attack + detection breakdown 👇 youtu.be/30Qiq_Gt_bA
#purpleteam #MDE #NTLMcoercion #detectionengineering

YouTube
English
Labman retweetledi

Chrome 137+ added a CNG wrinkle to App-Bound Encryption.
@harmj0y + @tifkin_ walk through how Nemesis 2.2 handles it, automating DPAPI decryption from SYSTEM + user masterkeys through Chromekey1 to cookie/login recovery, w/ retroactive artifact linking. ghst.ly/3ZU2vZ7
English
Labman retweetledi

WinGet can be more than a package manager. We show how .winget configs + a self-referencing LNK become a viable initial access payload when Microsoft Store is enabled. Includes detection queries & mitigation tips.
blog.compass-security.com/2026/03/winget…
#RedTeam #Windows #LOLBins #InitialAccess
English
Labman retweetledi
Labman retweetledi

#SilverDragon is a new threat cluster with ties to #APT41.
🎯Activity across Asia & Europe, exploiting internet-facing servers and running targeted phishing.
☁️New .NET implants alongside Cobalt Strike and abuse of cloud services for C2.
Read more ->
research.checkpoint.com/2026/silver-dr…
English



