AppSecEngineer
5.4K posts


AppSecEngineer
@AppSecEngineer
Painless Application Security Training for Enterprises. Empower Your Teams. Build Secure Applications.
United States Katılım Mart 2018
208 Takip Edilen4.8K Takipçiler

Everyone’s debating whether MCP is “dead.”
That’s the wrong conversation.
MCP gives AI agents access to tools.
Skills tell them how to use those tools safely, efficiently, and consistently.
And that’s exactly why MCP security matters.
As AI agents gain deeper access to codebases, databases, and environments, risks like Tool Poisoning, Agent Goal Hijacking, Command Injection, Shadow MCP Servers, and Secret Exposure become very real.
That’s why we launched new hands-on MCP OWASP Top 10 courses—to help security engineers understand how these attacks actually work in modern AI systems.
🎯 Learn the risks. Practice the defenses. Build real AI security skills.
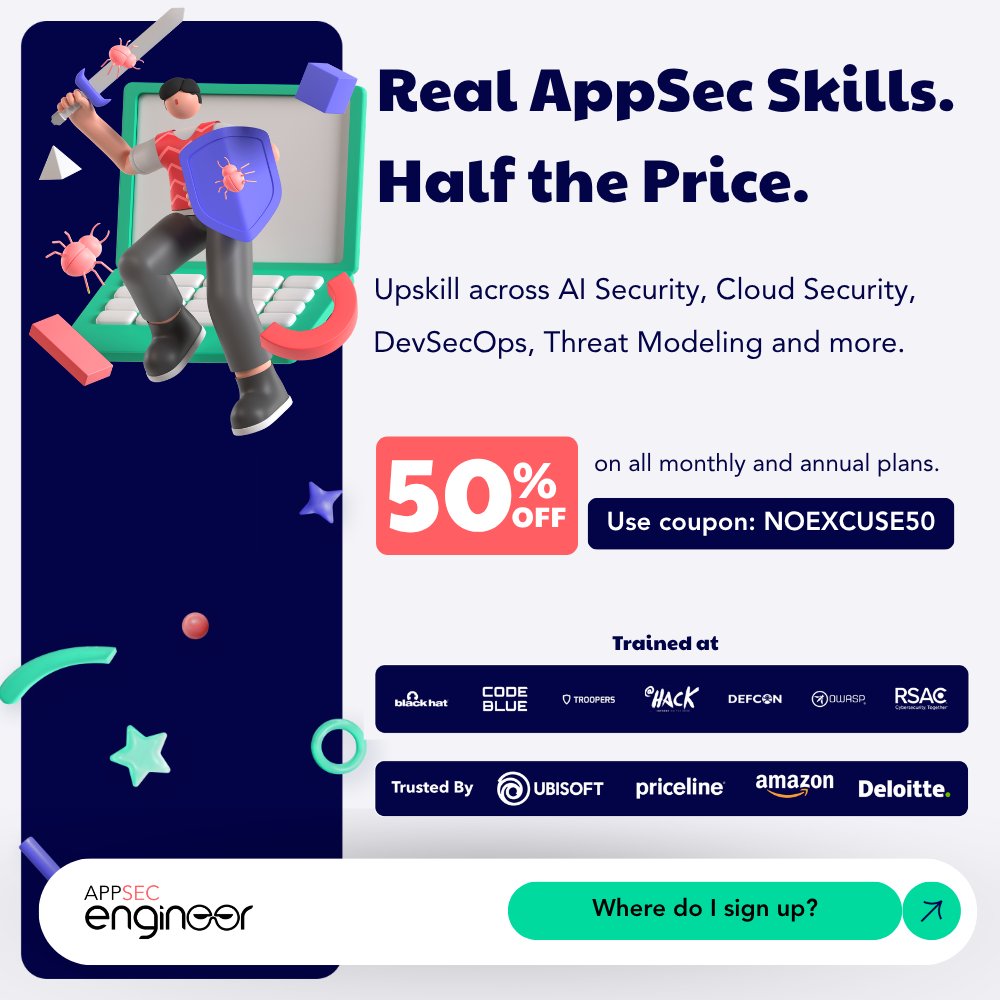
🔥 50% OFF sitewide
Use code: NOEXCUSES50
🔗 Link in comments
English

The scariest AI failure mode right now?
Not prompt injection.
Not model compromise.
It’s when the model works perfectly…
…but the context feeding it is wrong.
That’s where things get dangerous.
Watch how this happens in modern AI pipelines.
Learn how to secure AI systems today on AppSecEngineer.
English

Get the full guide here: appsecengineer.com/enterprises/hi…
English

Healthcare software is one of the few environments where small security mistakes can scale into systemic risk.
Developers aren’t just writing code — they’re shaping how patient data flows across systems, APIs, and clinical workflows.
Secure coding becomes far more effective when teams move beyond generic guidance and start working with patterns that reflect the realities of healthcare systems.
The goal isn’t perfection.
It’s making the secure way the easiest way to build.
Learn more in the full guide (link in reply).

English

“Process this invoice.”
→ Agent issues a refund instead.
@abhaybhargav breaks down goal hijacking—an indirect prompt injection hidden in trusted data.
Watch 👇
English

A chatbot bug in e-commerce is annoying.
A chatbot bug in healthcare can expose protected health information (PHI).
Or surface internal claims data.
Or leak privileged medical records.
AI is powerful.
But in healthcare, it also expands the attack surface.
Watch the full webinar on healthcare security.
Link in the reply.
English

If you don’t know your dependencies, you can’t secure them.
That’s why SBOMs are becoming essential in DevSecOps.
They provide a structured inventory of every open-source component in your application — including versions, licenses, and providers.
And they power SCA tools to detect real vulnerabilities.
Join the DevSecOps Bootcamp — link in description
📺 Watch the full webinar on our YouTube channel
English

The biggest challenge in threat modeling?
No one owns the full picture.
Application architecture, cloud infrastructure, deployment pipelines — the knowledge is scattered across teams.
Yet security teams are expected to identify every possible threat.
Learn a practical way to tackle this in the Threat Modeling Bootcamp.
Join the Threat Modeling Bootcamp — link in description
Watch the full webinar on our YouTube channel
English