Arsenal Recon
1.3K posts


Arsenal Recon
@ArsenalRecon
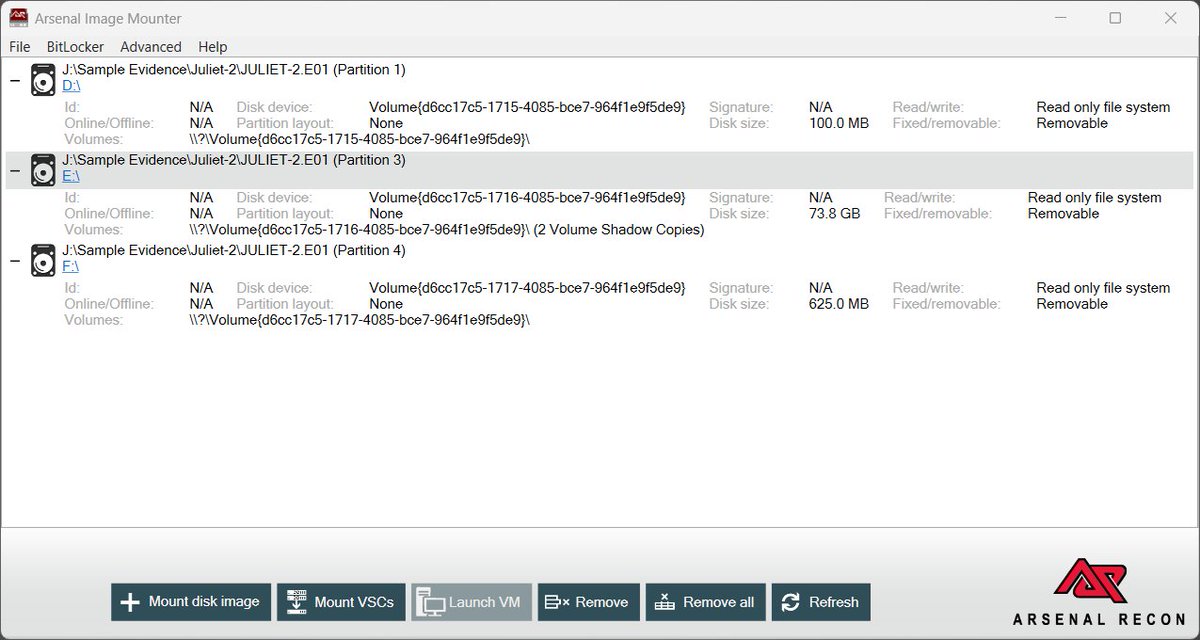
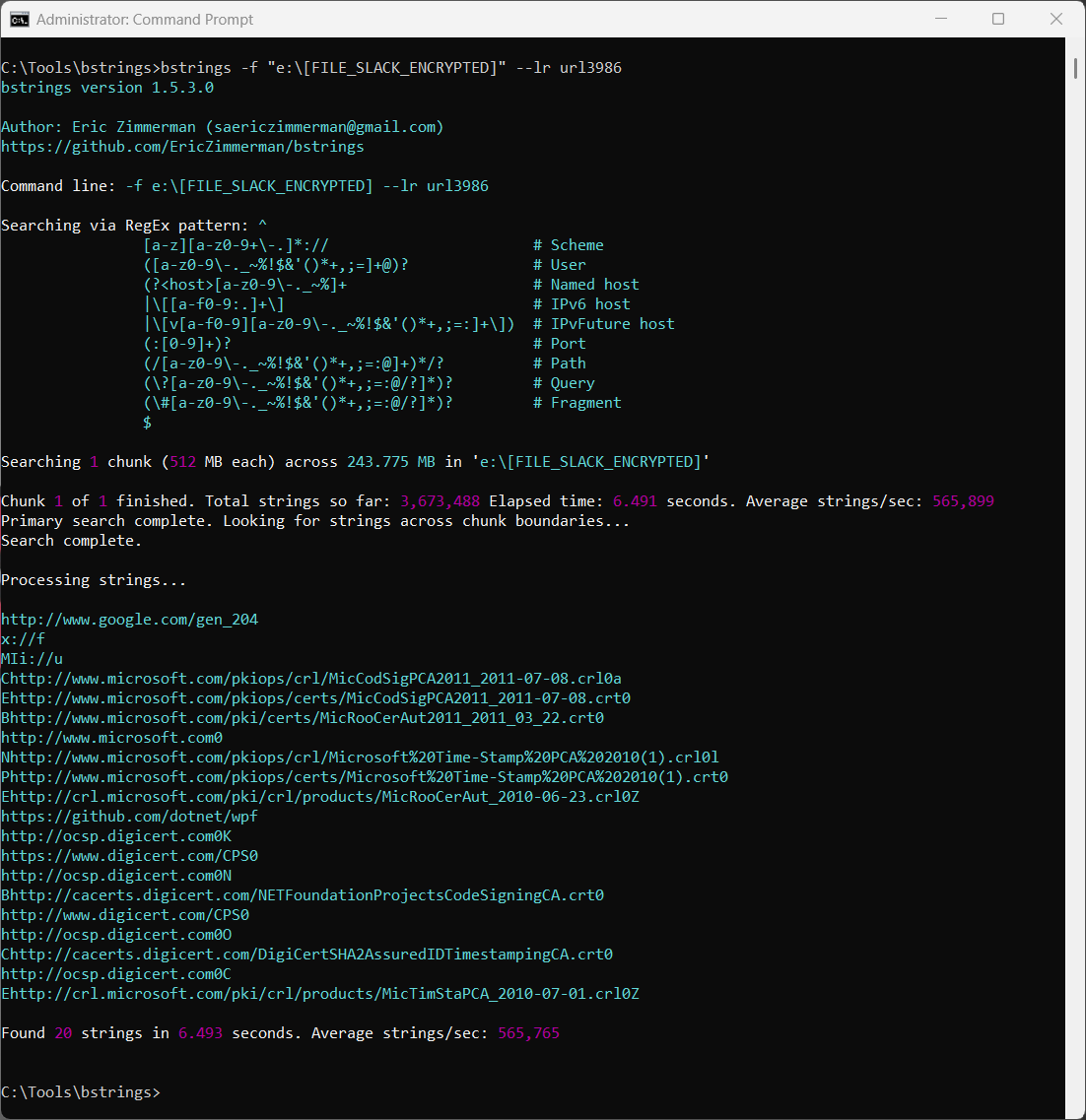
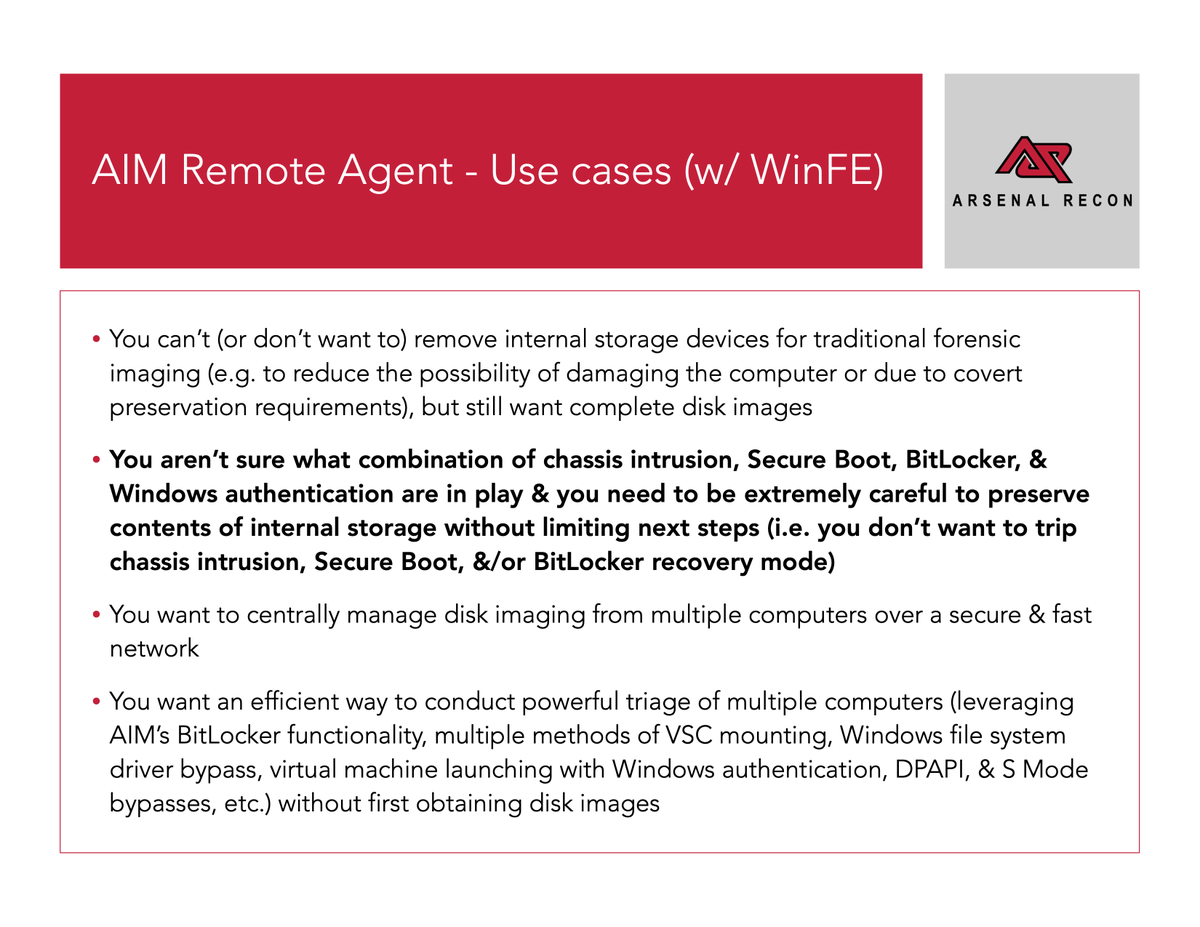
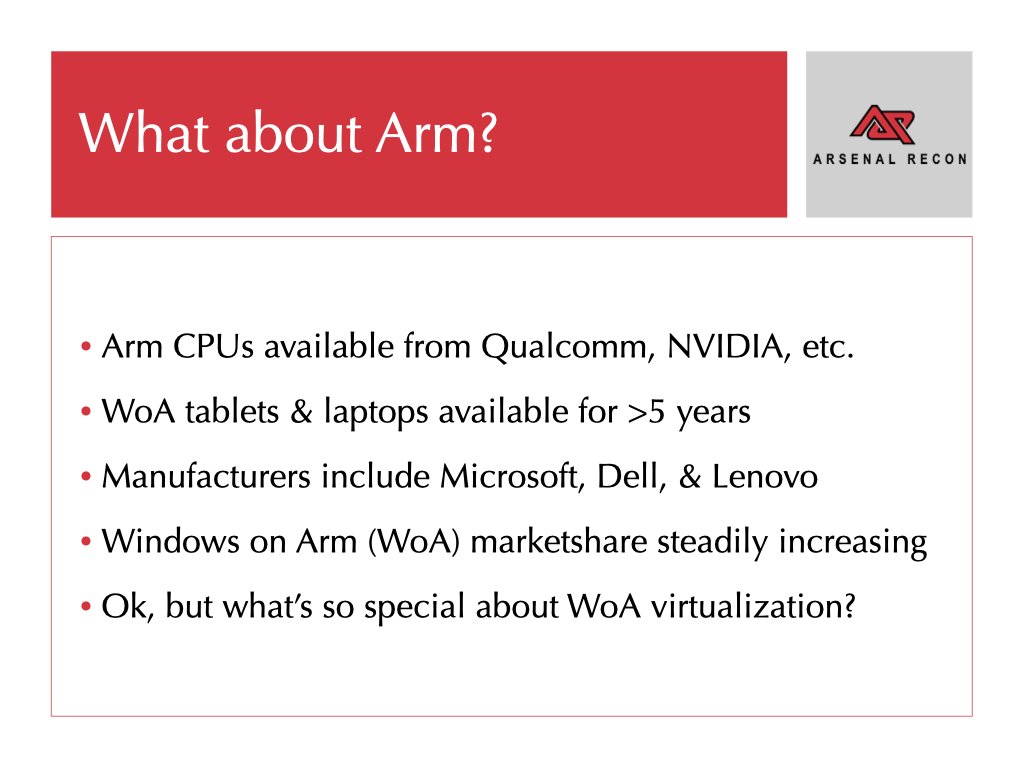
Developers of digital forensics weapons which include Arsenal Image Mounter, Hibernation Recon, LevelDB Recon, HBIN Recon, & Registry Recon. Arm Yourself! #DFIR




















Hi, I'm Garrett, Principal PM on the Windows Hardware Program. If you're a partner having trouble regaining access to Hardware Dev Center after account verification, we've put a temporary process in place to speed up reinstatement. You can learn more at aka.ms/HDC-Account-Ve…

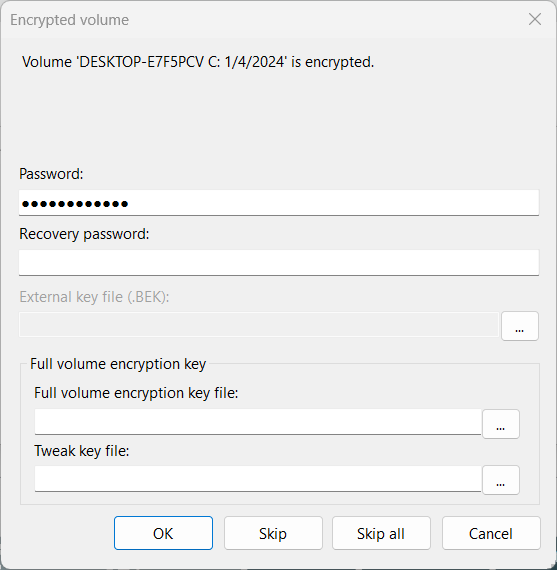
Just Microsoft things... Recently they terminated the VeraCrypt developer's Microsoft account. VeraCrypt is a free and open-source disk encryption software that performs on-the-fly encryption (OTFE) to create virtual encrypted disks, encrypt partitions, or secure entire storage devices.