
"Bad News for the Average Pentester" ... But who wants to be average?
Here's some thoughts from Shawn on why Human-Powered Pentesting is here to stay.
atredis.com/blog/2026/5/15…

English
Atredis Partners
626 posts


@Atredis
Atredis is a 100% worker-owned team of world-class security researchers and consultants. We do risk-centric, research-driven security testing and consulting.









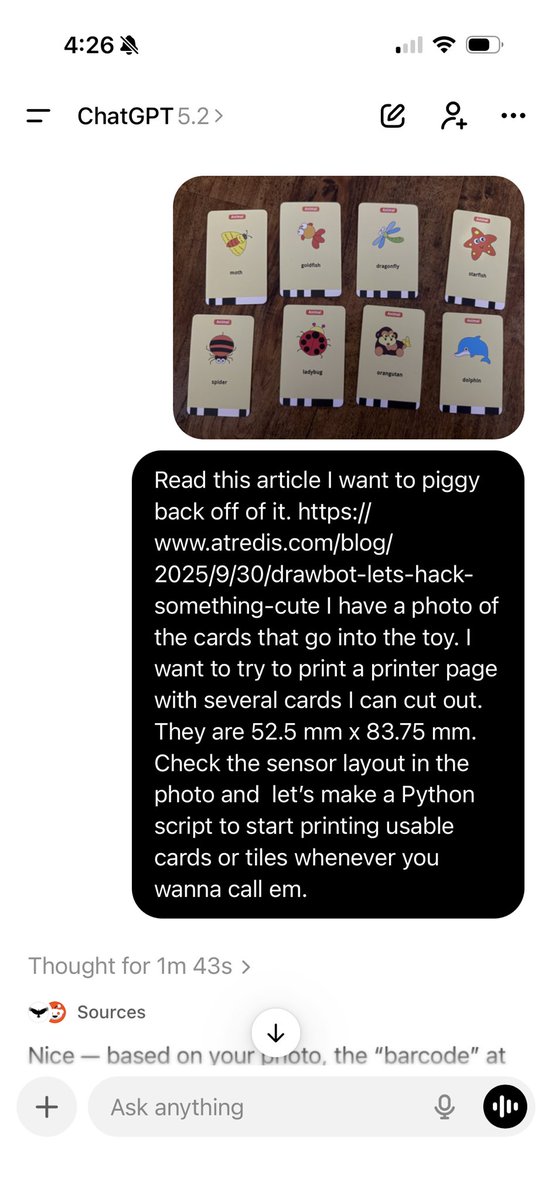


Begging to be hacked…




















