BadPods Series: Everything Allowed on AWS EKS
By: Kiran Dawadi
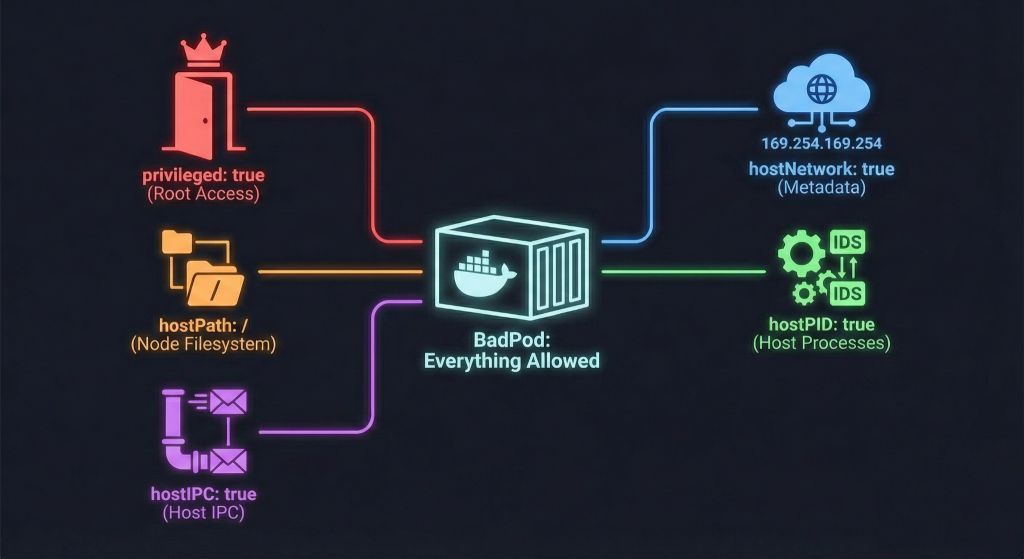
Kiran Dawadi’s “BadPods” series dives into how default configurations in AWS EKS can let attackers do far more than most teams realize, turning cluster misconfigurations into full-blown compromise.
🔍 Why this is worth reading:
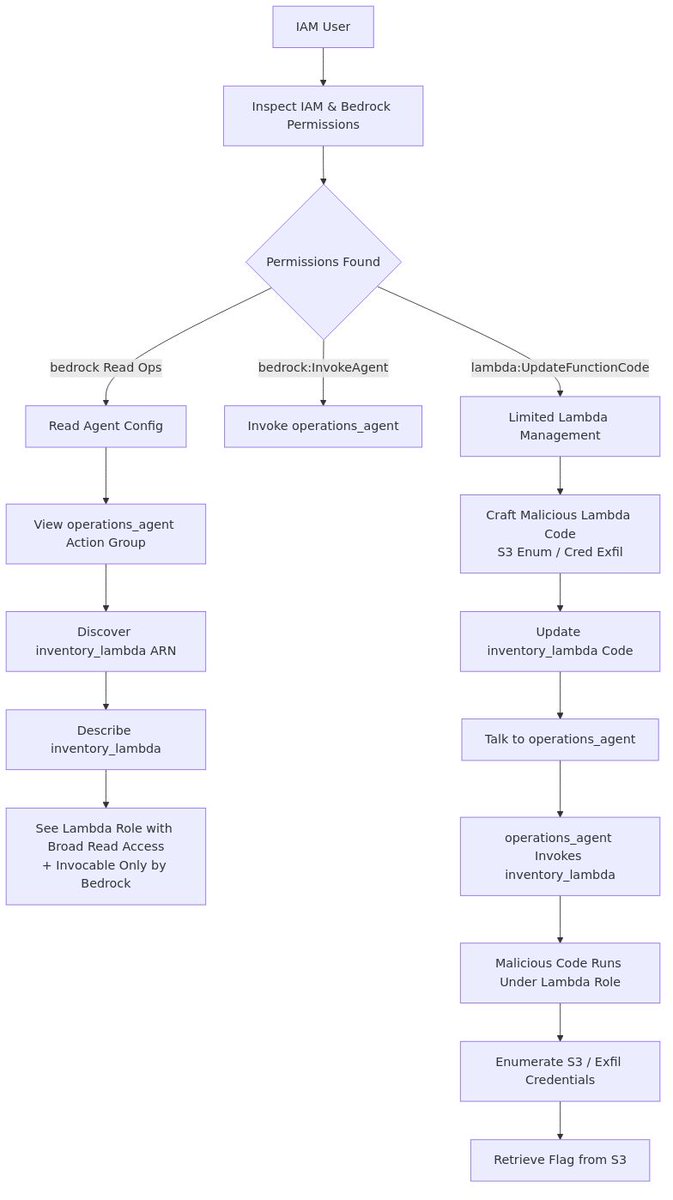
• 🛠 Privilege escalation inside EKS — Shows how pods with default service accounts and broad RBAC permissions can pivot across the cluster.
• 🔐 Network and role blind spots — Even “private” pods can exploit overly permissive network policies or cross-namespace role bindings.
• 🧩 Real attack chains — Step-by-step examples of compromising workloads, extracting secrets, and escalating to cluster admin.
• ⚡ Defensive guidance — Highlights how to enforce least privilege, restrict pod capabilities, and audit service accounts effectively.
👉 If you run or secure EKS clusters, this series reveals the gaps between default settings and secure practices, giving practical insights to harden your deployments.
Read Here: cybersecnerds.com/badpods-series…
This was first mentioned in AWS Security Digest Issue #242: awssecuritydigest.com/past-issues/aw…
English