Sabitlenmiş Tweet

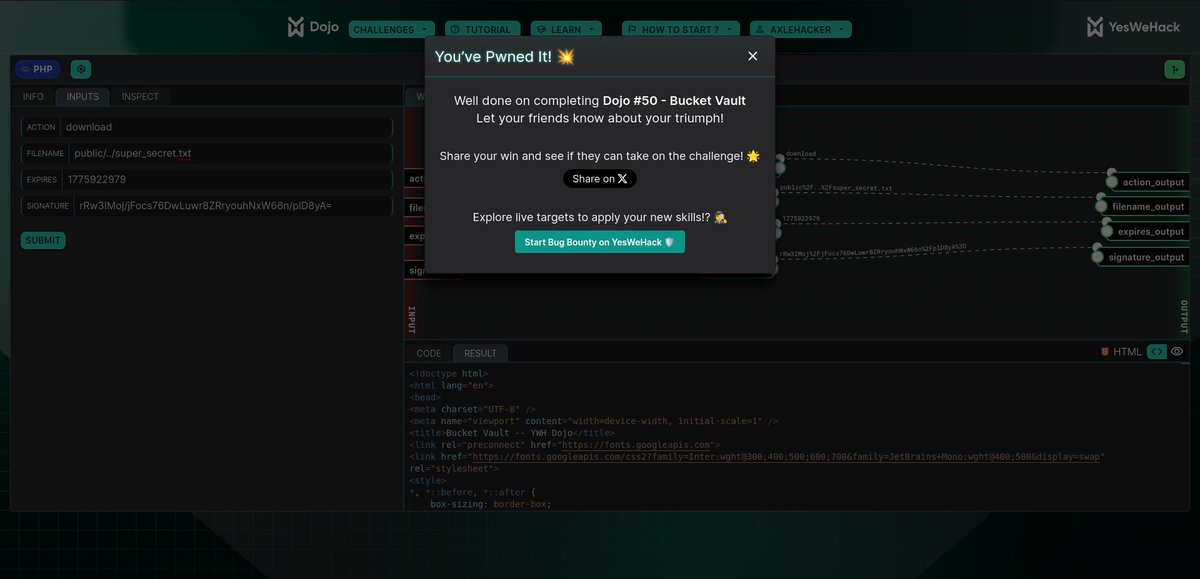
Just pwned Dojo #50 (Bucket Vault) on YesWeHack 💥
Turned a weak validation check into a full path traversal using control character injection → pulled a restricted file 🎯
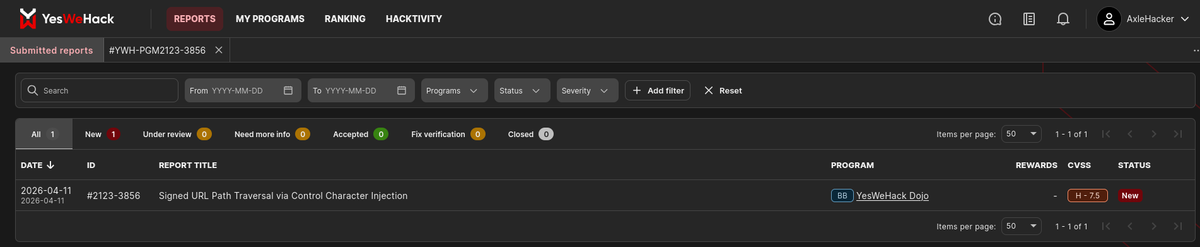
Also just submitted my FIRST vulnerability report 🧾🔥
No shortcuts — just breaking logic and understanding how things actually work.
We’re just getting started.
#bugbounty #cybersecurity #infosec #ethicalhacking #websecurity #hacker
English




