Bolha Sec
6.7K posts

Bolha Sec
@BolhaSec
Conteúdo diário de segurança ⬇️ Tweet com #bolhasec ou @bolhasec para ser retweetado; Criado por @sushicomabacate 🍣


🚨‼️Discord leaked user IDs with ban reasons to the EU DSA Transparency Database until 2025. Discord supplied the IDs by mistake. The EU hosted it all. The irony? The DSA is a regulation designed to protect users.

🚨 New CanisterWorm Discovery 🚨 Our researchers have identified additional compromised npm versions in the CanisterWorm attack that were previously unreported. We’ve mapped out the full scope and provided a 6-step remediation guide to help you scrub your environment clean. Read the full analysis and remediation guide here: research.jfrog.com/post/canister-…



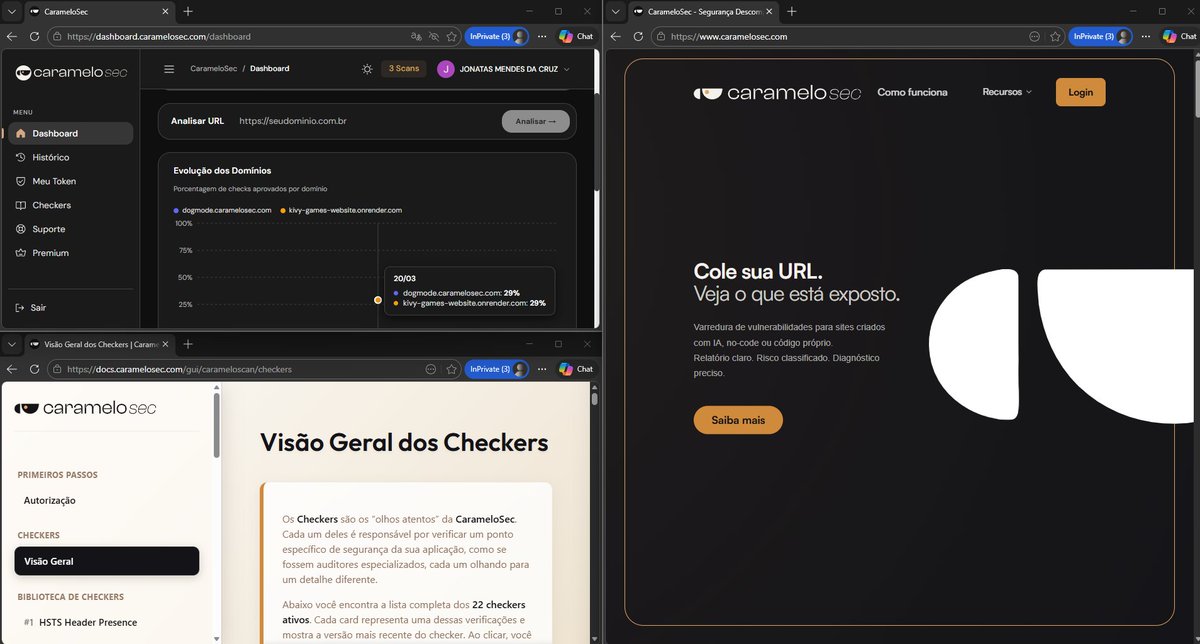
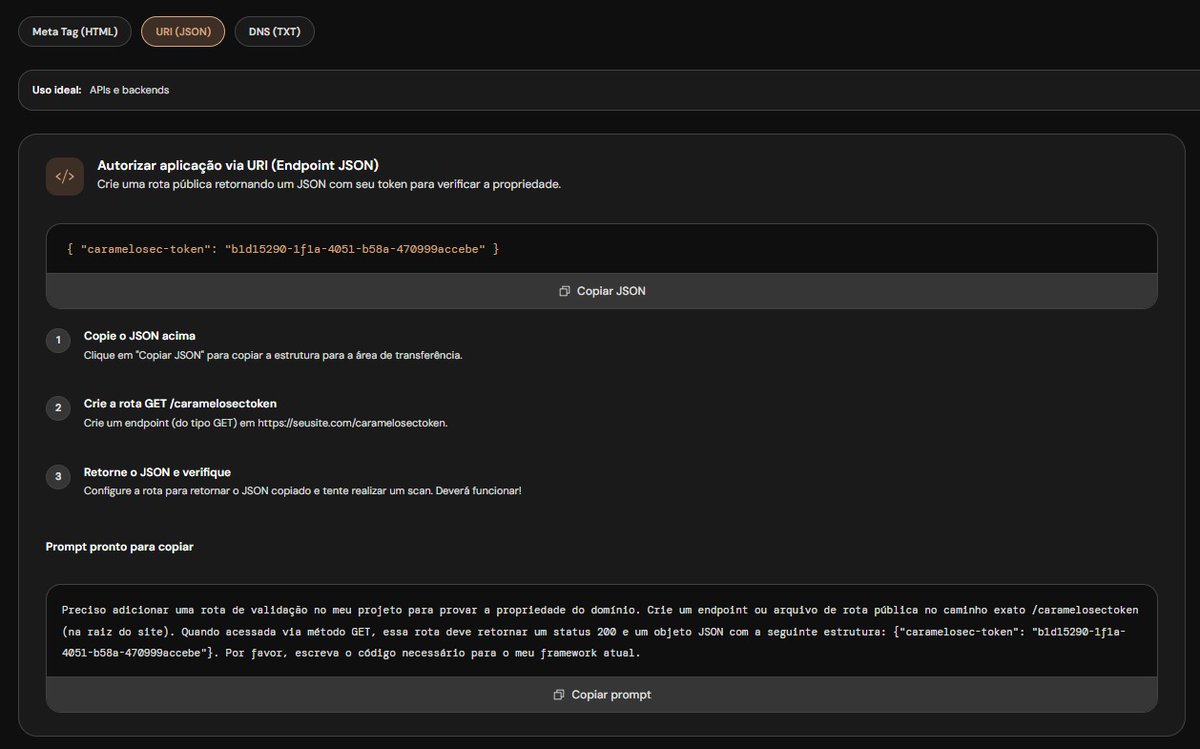
QUERO CONTRIBUIR COM A SEGURANÇA DA SUA SOFTWARE HOUSE! isso mesmo! nós da caramelosec estamos buscando software houses que querem escalar com segurança. você trabalha em uma? conhece uma? me fala aqui ou indica a gente! contrato sendo fechado você ainda ganha com isso! cc @sseraphini @meunomeebero @kyoto01z


🚨‼️ BREAKING: Crunchyroll breached through outsourcing partner in India. A threat actor exfiltrated data from Crunchyroll's ticketing system and also managed to pull 100 GB of personally identifiable customer analytics data. We've analyzed sample data and it includes IP addresses, email addresses, credit card details, and more. An employee of their outsourcing partner Telus had executed malware on his system, which gave a threat actor access to Crunchyroll's environment.



Hackers conseguiram desviar HOJE 100 milhões do BTG via pix! De lá enviaram para CAIXA FEDERAL e pulverizaram em dezenas contas. PIX DO BTG fora do ar.

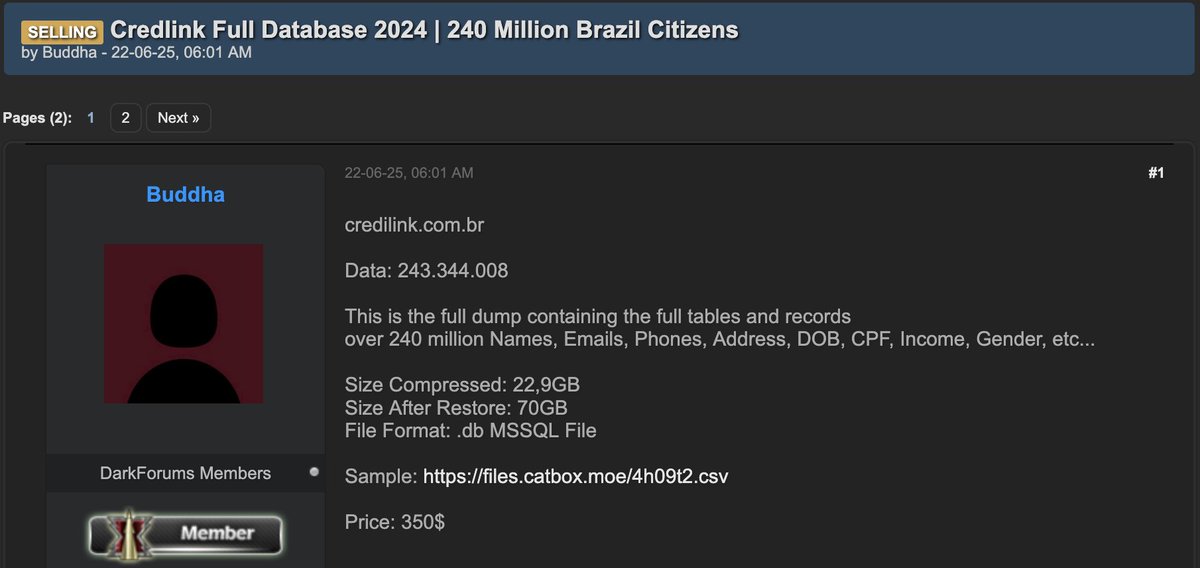
🚨 CYBERINTEL ALERT: Massive Data Leak at Credilink Brazil (243 Million Records) 🇧🇷💳 Our platform has detected a data breach affecting Credilink, one of the leading companies in credit information solutions and risk analysis in Brazil. Victim: Credilink.com.br 🏛️. Threat Actor: Blastoize 🎭. Volume: 243 million records reported—a figure that encompasses virtually the entire economically active population of Brazil. Date: March 21, 2026 🗓️. Highly Sensitive Information Compromised: 🔹 Identity and Tax: CPF (Brazilian Tax ID), full name, date of birth, and mother's name. 🔹 Socioeconomic Status: Estimated income, income bracket, and corporate role/position (PCT_CARGO_SOCIETARIO). 🔹 Assets: Details on up to 5 vehicles per individual (Make, model, and year). 🔹 Contact and Location: Full addresses (street, number, neighborhood, city, state, CEP/postal code) and email addresses. 🔹 Legal Status: Status with the *Receita Federal* (Brazilian Federal Revenue Service) and death records (FLAG_OBITO). Monitor: analyzer.vecert.io #CyberSecurity #Credilink #Brazil #DataBreach #CPF #Blastoize #InfoSec #CyberAlert #CreditRisk #FinSec




We just released Claude Code channels, which allows you to control your Claude Code session through select MCPs, starting with Telegram and Discord. Use this to message Claude Code directly from your phone.

🛑 ALERT - Trivy, a popular open-source vulnerability scanner, was compromised after attackers hijacked 75 version tags in #GitHub Actions to deliver an infostealer. It ran in CI pipelines, stealing creds and tokens, then exfiltrating data or staging it via stolen GitHub PATs. 🔗 Attack flow, impacted versions, fixes → thehackernews.com/2026/03/trivy-…