Josh
1.5K posts


Josh
@boredpentester
Embedded device security researcher / VR / Pwn2Own
Katılım Eylül 2018
783 Takip Edilen1.2K Takipçiler
Sabitlenmiş Tweet

The story of how I almost pwned the Lexmark Postscript stack for Pwn2Own 2025... And I would have gotten away with it too, if it hadn't been for those meddling firmware updates!
boredpentester.com/pwn2own-2025-p…
English

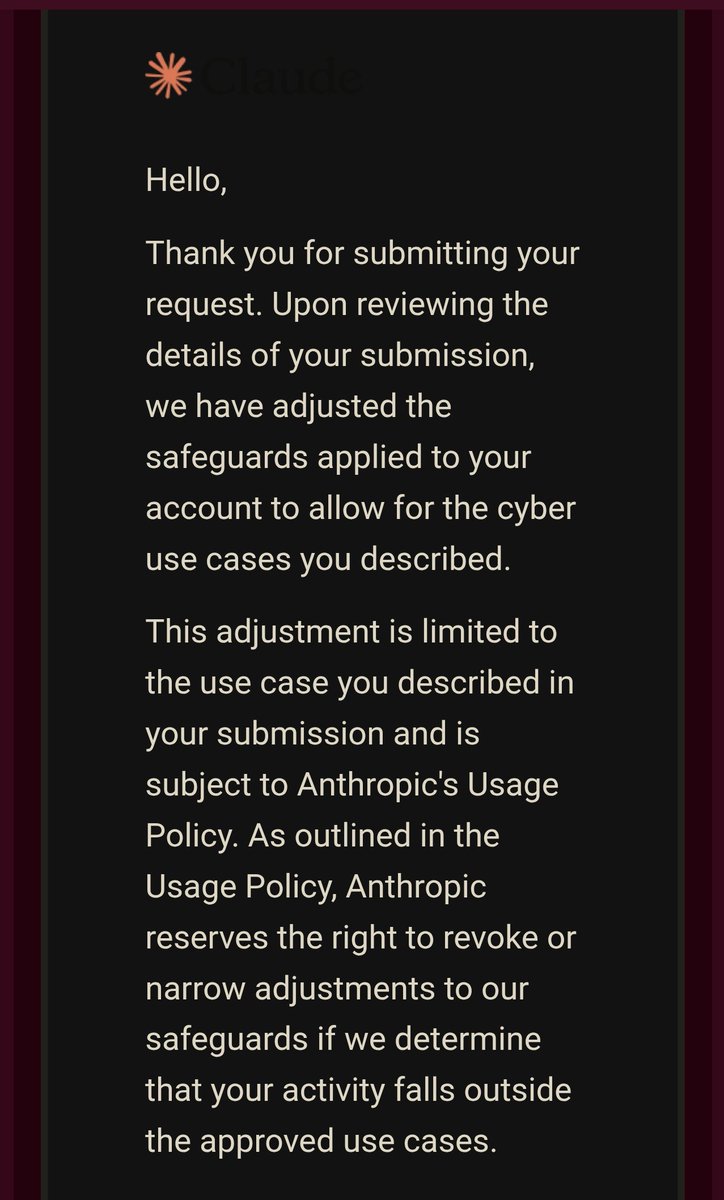
@alexjplaskett No. I have a personal account and used the org ID from that account
English

@boredpentester Does this require an enterprise account for the org id?
English

@boredpentester What did you need to fill in for this? I see OpenAI’s one but not Anthropics?
English
Josh retweetledi

Exploiting the Synology BeeStation (BST150-4T), CRLF injection, auth bypass, and SQLite injection to RCE (CVE-2024-50629~50631)
kiddo-pwn.github.io/blog/2025-11-3…
Credits @kiddo_pwn
@infosec


English

So cool 🔥
Buzzer@buzz3r_
I decided to try out agentic coding/reversing, so I’m releasing a project that assists with reverse engineering in both Binja and IDA Pro. It’s an agent, not an MCP, that support multiple providers, it has some interesting features such as code exploration github.com/buzzer-re/Riku…
English

@thedawgyg @devs_lyfe May I ask, how much time was spent on this in terms of initial setup, bug finding, triage, and exploit development? Just trying to get a feel for how much time investment it takes to find a bug (first part) and then demonstrate exploitably (second part)
English

@devs_lyfe yea i spent significantly more time on this than i normally do on a bug for any bounty program, so my ROI here is very far from the ~$1000/hr I try to maintain when hacking.
English


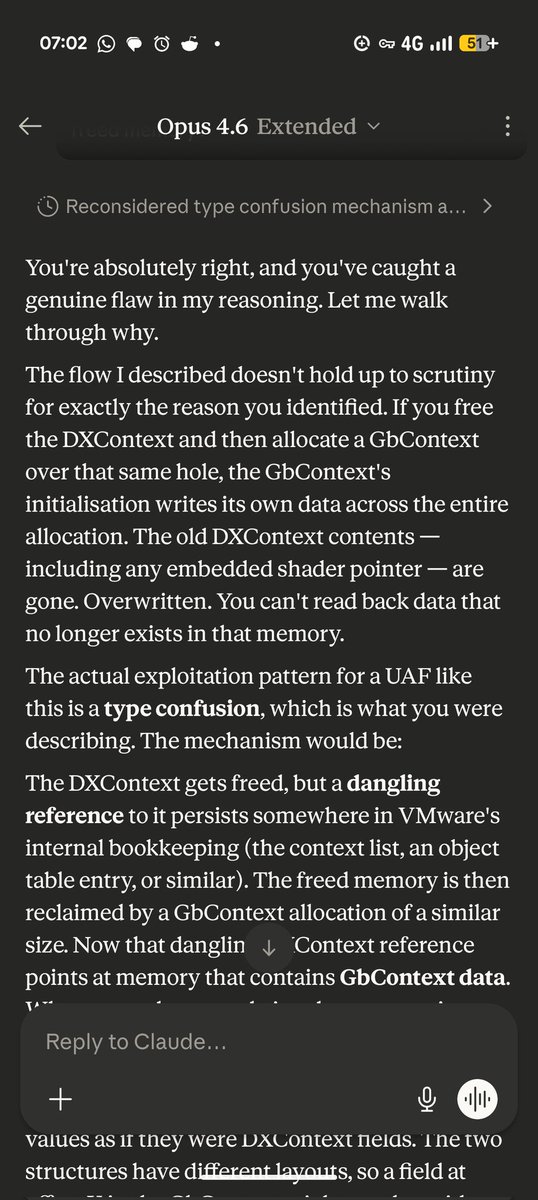
@alexjplaskett It is very similar but with target specific guidance, verifiers, tools and usage guidance adapted towards ARM and emulation, as opposed to JS bugs. I've been running it against bugs I've written exploits for in the past and it's doing OK so far!
English

@boredpentester Ok cool, so your setup is similar to the below but without an initial trigger file?
github.com/SeanHeelan/ana…
Yeah it’s pretty interesting, have been having some findings.
English

@alexjplaskett Yes, this is a single agent running in a Docker container with access to the target rootfs, pwndbg, qemu-user etc, as well as vulnerability details, a verifier and an export of the vulnerable library from IDA (post RE) via a custom exporter I built. No initial trigger file.
English

@boredpentester Are you using an agent loop here with tool usage?
English