CIRCL - @[email protected]
11K posts

CIRCL - @[email protected]
@circl_lu
CIRCL is the CERT (Computer Emergency Response Team) for the private sector, communes and non-governmental entities in Luxembourg.



















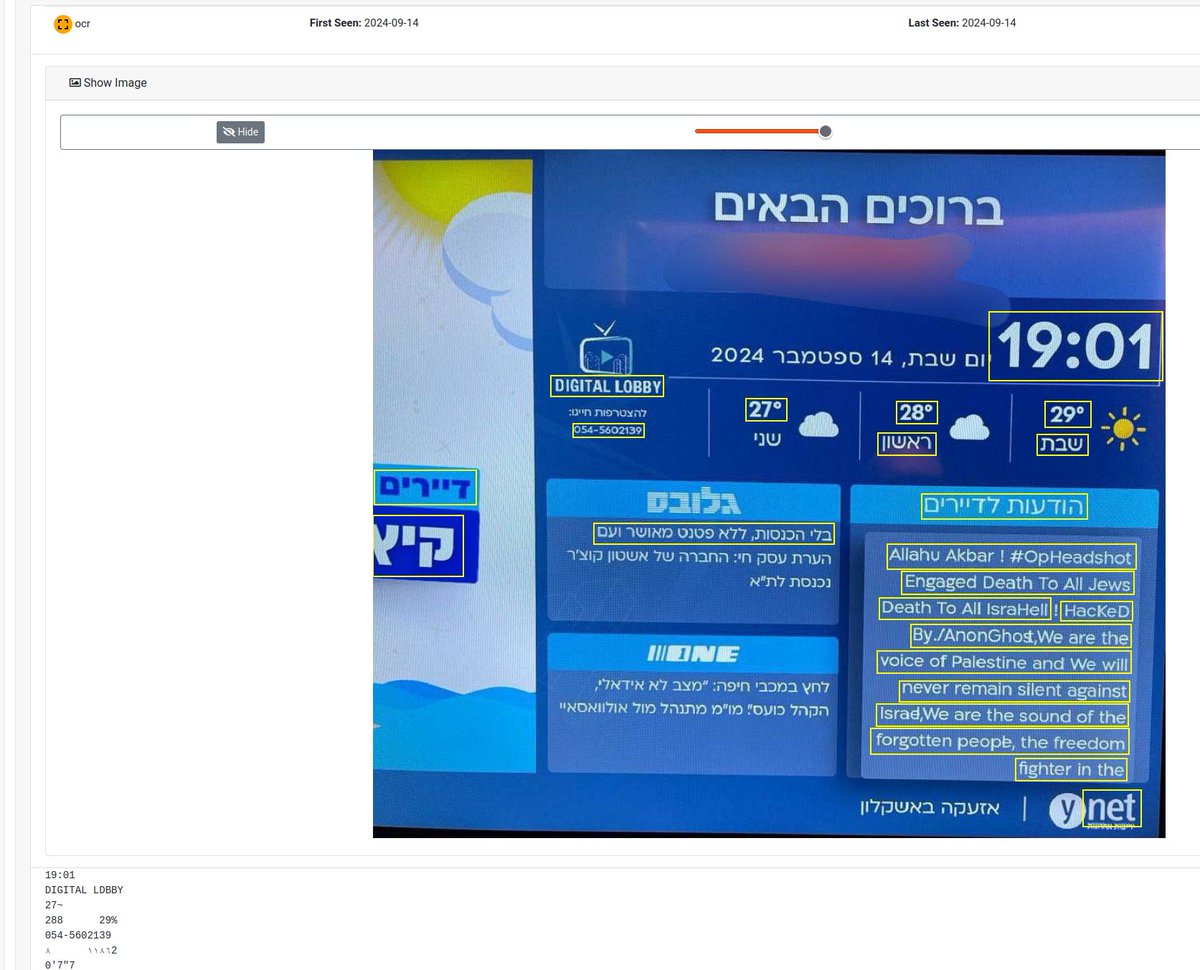
Palo Alto Networks has now updated their advisory security.paloaltonetworks.com/PAN-SA-2024-00… saying they have "observed threat activity exploiting an unauthenticated remote command execution vulnerability against a limited number of firewall management interfaces which are exposed to the Internet."



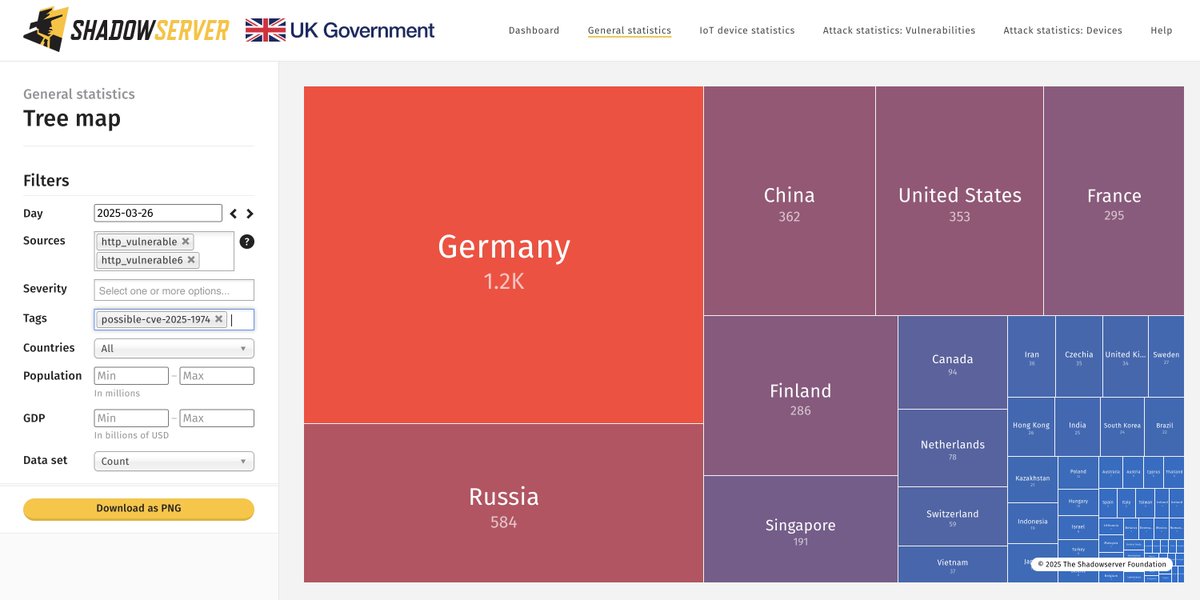
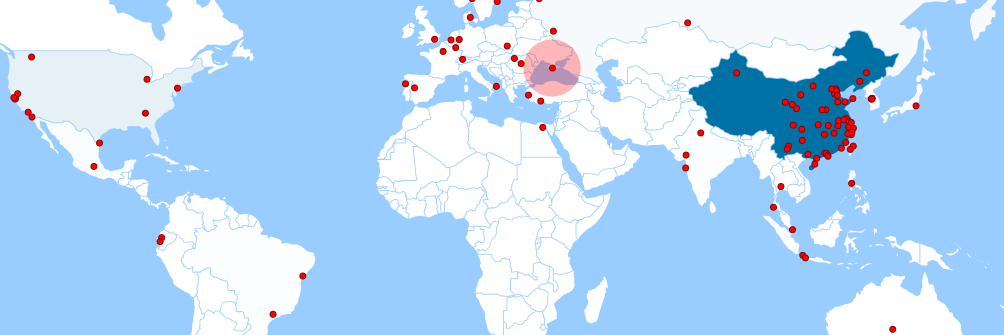
CVEs have now been assigned: unit42.paloaltonetworks.com/cve-2024-0012-… security.paloaltonetworks.com/CVE-2024-0012 security.paloaltonetworks.com/CVE-2024-9474 6642 IPs found exposed on 2024-11-17 (down from around 11K): dashboard.shadowserver.org/statistics/iot… As a reminder, IP data is shared in our Device ID report daily: shadowserver.org/what-we-do/net…



The first version of the #hacklu 2024 agenda is now live. Check it out here: 2024.hack.lu/agenda/ Don't miss out—join us for this year's edition! #infosec #conference #Luxembourg