Johannes Bader
196 posts

Johannes Bader
@viql
Reverse engineer / malware analyst. On the hunt for domain generation algorithms. Current side project: https://t.co/Cv3COq0ZmR
Schweiz Katılım Ağustos 2013
166 Takip Edilen1.8K Takipçiler

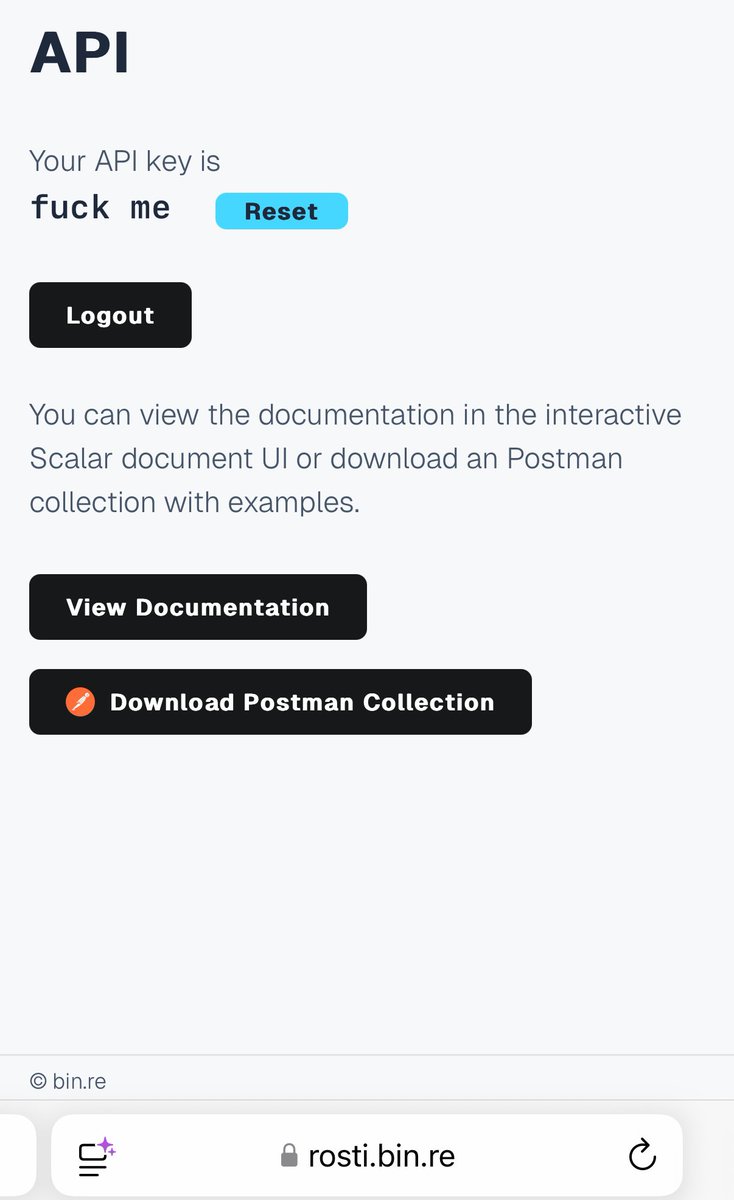
@abuse_ch do I have to pay to give IoCs for free to you? 🙃
"Unable to post to Threat Fox; HTTPError: 402 Client Error: Payment Required for url: threatfox-api.abuse.ch/api/v1/"
English

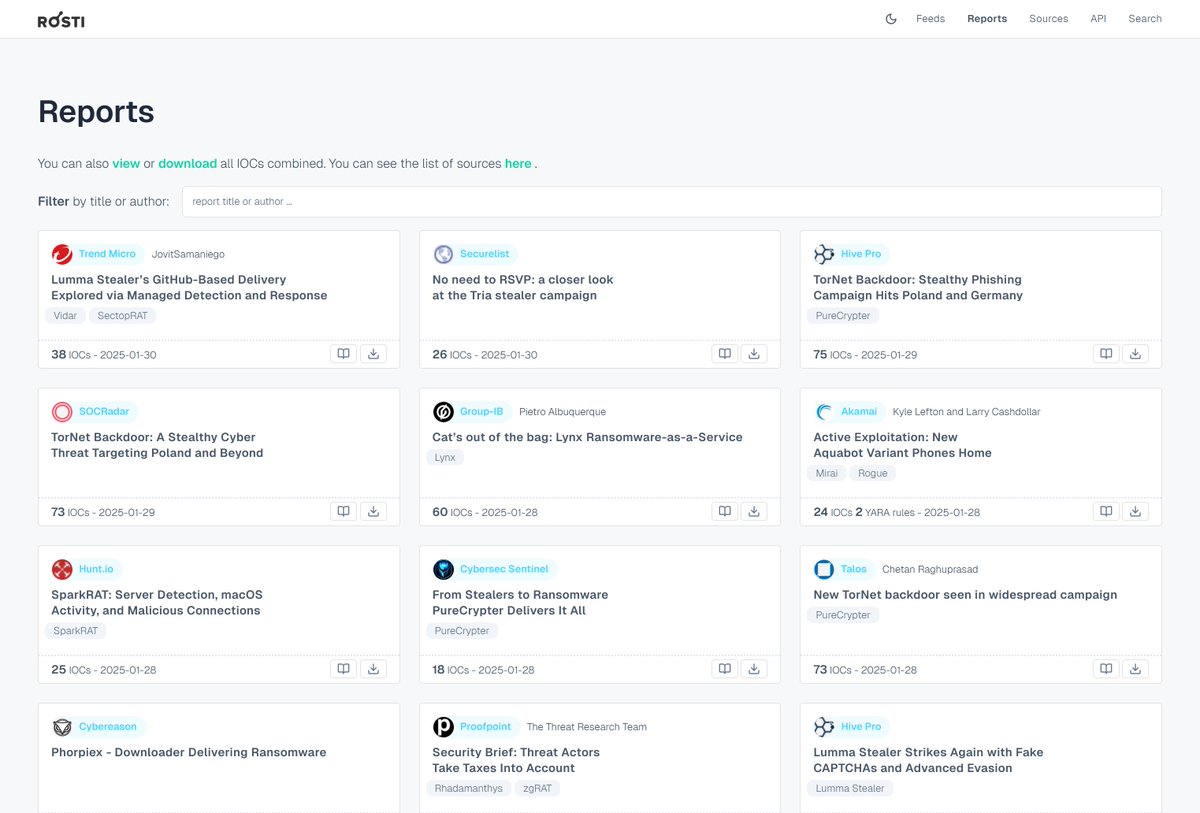
Today, I'm releasing the first version of a small web 🚀: rosti.bin.re
It provides IOCs and YARA rules collected semi-automatically from public blog posts and reports of almost 200 cybersecurity sites.
I hope it proves useful to some of you ... 🙏✨ #ThreatIntel
English
Johannes Bader retweetledi

According to @GovCERT_CH , an unknown threat actor has sent out postal letters (yes, *postal* letters ✉️) to recipients in Switzerland that pretend to originate from @meteoschweiz, luring the recipient into downloading and installing a rogue App 🔥🕵️♂️
The QR code in the letter leads to a malicious App that impersonating the "AlertSwiss" App of the federal administration. However, the App in fact is a version of Coper (aka Octo2) #malware, infecting mobile phones running Android 📱🤖
Payload delivery URL:
🌐 urlhaus.abuse.ch/url/3290212/
Malware sample:
📄 bazaar.abuse.ch/sample/4928c56…
Coper botnet C2:
🔥 threatfox.abuse.ch/ioc/1344824/
➡ ncsc.admin.ch/ncsc/en/home/a…
English
Johannes Bader retweetledi

What's happening? #FlareOn11 is happening! Time to update #BinaryRefinery and snag some flags!
✨ github.com/binref/refiner…
✨ flare-on11.ctfd.io/challenges

English
Johannes Bader retweetledi


Could you please share your IOCs in any format that is NOT low screenshots @Cloudflare 🙏?
blog.cloudflare.com/disrupting-fly…

English
Johannes Bader retweetledi

Nice #MooBot botnet caught by @banthisguy9349 😂
Botnet C2 domain:
🔥 putin.zelenskyj .ru
Pointing to:
45.88.90.30:43957 (AS203168 Constant MOULIN 🇧🇪)
DNS resolution provided by Cloudflare 🔎
Payload URLs:
🌐 urlhaus.abuse.ch/host/45.88.90.…
Payload:
📄 bazaar.abuse.ch/sample/21f1caa…

English
Johannes Bader retweetledi

I wrote a blog post about MalpediaFLOSSed, a collection of ~4 million strings extracted from 1800+ malware families and upgrading its GUI plugin to work with IDA, Ghidra, and Binary Ninja at once!
Kudos to @hyun____22 for Hyara, which pioneered such cross-tool compatibility!
Byte Atlas@ByteAtlas
[blog post] MalpediaFLOSSed danielplohmann.github.io/blog/2024/03/0…
English

@Artilllerie @malwrhunterteam @JAMESWT_MHT Nice catch! There is indeed a DGA behind the .life domain names, but for now they use a time-independent seed. bin.re/blog/the-dga-o…
English

#BumbleBee
🧬Well detected (49/71) because 2023-09-06
virustotal.com/gui/file/fe3c9…
▶️group_name: lnk1
▶️4 well-known .life C&C domains
🧩Mysterious "FORTHEEMPEROR" string (ping) 🤔
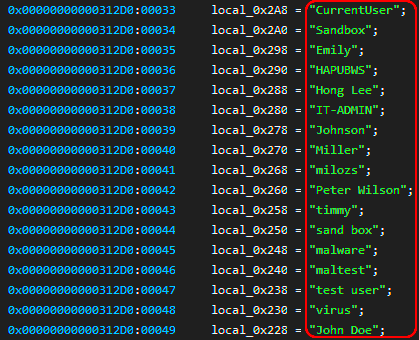
🧩Many anti-sandbox with 17 usernames checks 🧐
🧩Possible DGA on .life domains
@malwrhunterteam

English

@joyofcodedev Very nice! @Rich_Harris also created an emoji matching game for his excellent "Svelte Fundamentals" course on @FrontendMasters. His course is paywalled, but you find the game on Vercel / GitHub.
🎮: ematchi.vercel.app
📺: frontendmasters.com/courses/svelte…
📄: github.com/Rich-Harris/em…
English

I released a new video on how to make a matching game with Svelte! 🔥
📺 youtu.be/w2q9caYXgkg
✍️ joyofcode.xyz/svelte-matchin…

YouTube

English
Johannes Bader retweetledi
Johannes Bader retweetledi

I wrote a short blog post on MCRIT, the one-to-many code similarity analysis framework that we released as open source recently at @Botconf.
Byte Atlas@ByteAtlas
[blog post] MCRIT: The MinHash-based Code Relationship & Investigation Toolkit danielplohmann.github.io/blog/2023/06/0…
English

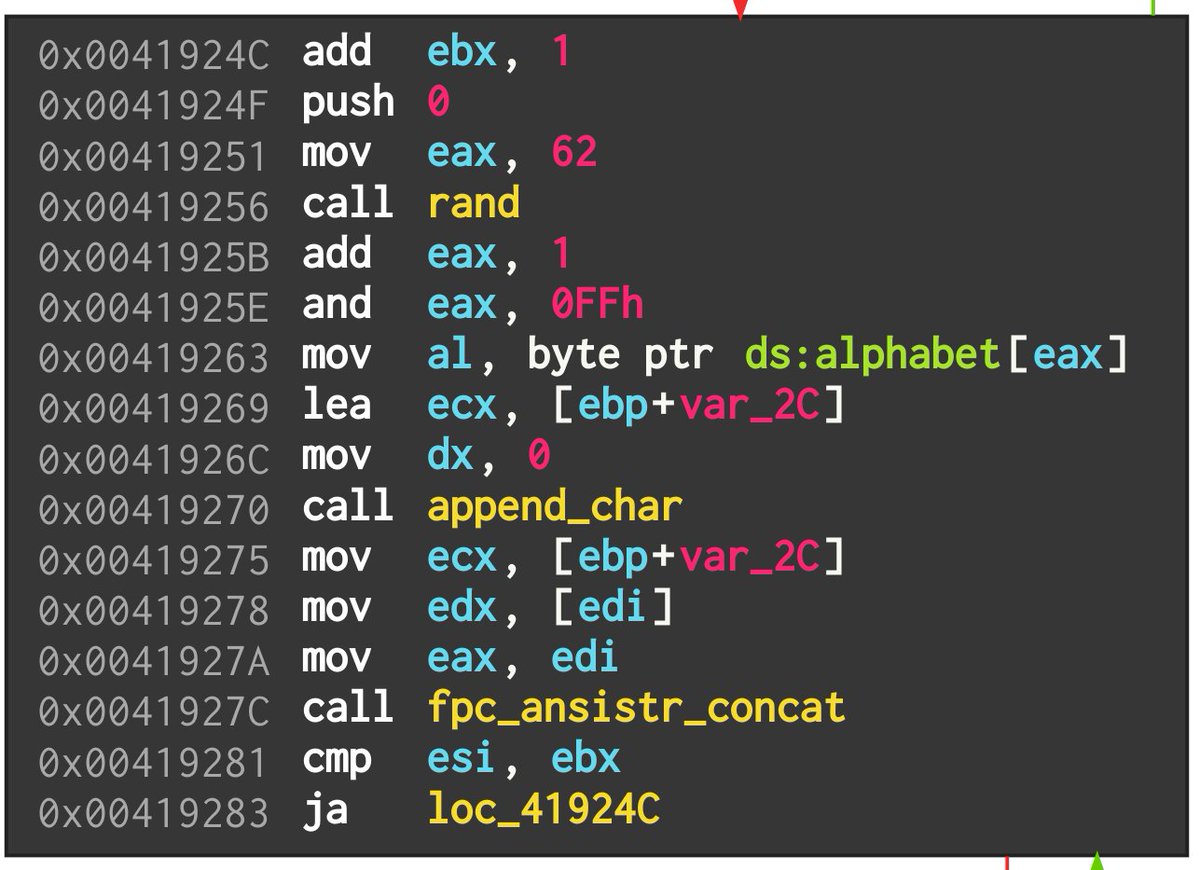
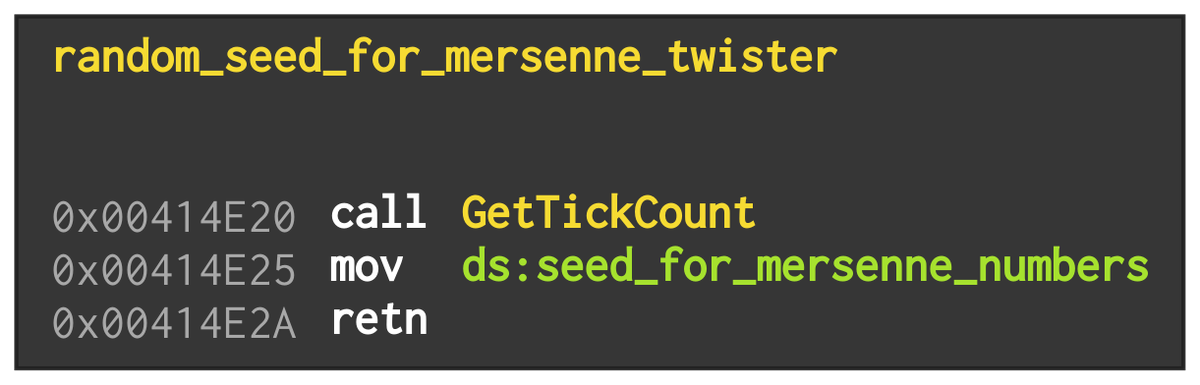
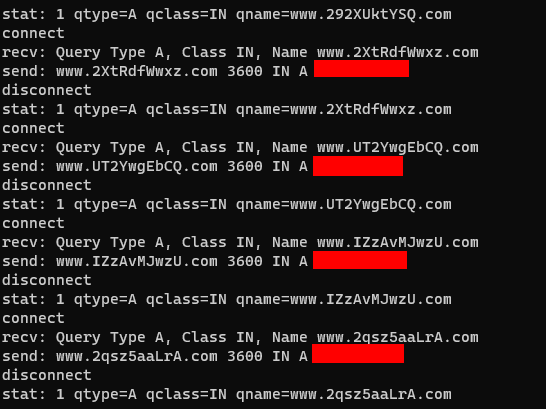
@_mostwanted002_ This is the #khalesi info stealer. The DGA picks 10 random alphanumeric characters with a common Mersenne Twister implementation. Unfortunately, the seed is just the current tick count, so unpredictable for both the attackers and analysts.
English

First time detonating a sample that uses DGA.
O.O
Sample: 004a56d1896512f7a6c5793fe7aa5919
#malware #threatintel
English
Johannes Bader retweetledi

#BinaryRefinery 0.5.10 can deobfuscate this sample with little effort. Only had to add one new unit for StrReverse constant folding. Not a silver bullet, obviously, but why write those regular expressions yourself when you can make me do it for you?

GuidedHacking@GuidedHacking
CyberChef for Malware Analysis - DCRat Loader youtube.com/watch?v=rpp6BZ…
English
Johannes Bader retweetledi

🛠️ .NET malware decompiling challenges: Obfuscations of strings/constants can be tedious. Automate w/ IDA Pro's Python 🐍 interface for MSIL binary patching, even for simple cases: threatcat.ch/blog/undo-dotn…
#CyberSecurity #MalwareAnalysis #IDAPro #DotNET

English
Johannes Bader retweetledi

New video on the Domain Generation Algorithm of the file infector m0yv. We've sinkholed multiple domains & show how infections dramatically increased in the last 400+ days 📈. #m0yv #DGA
youtu.be/3RYbkORtFnk

YouTube

English
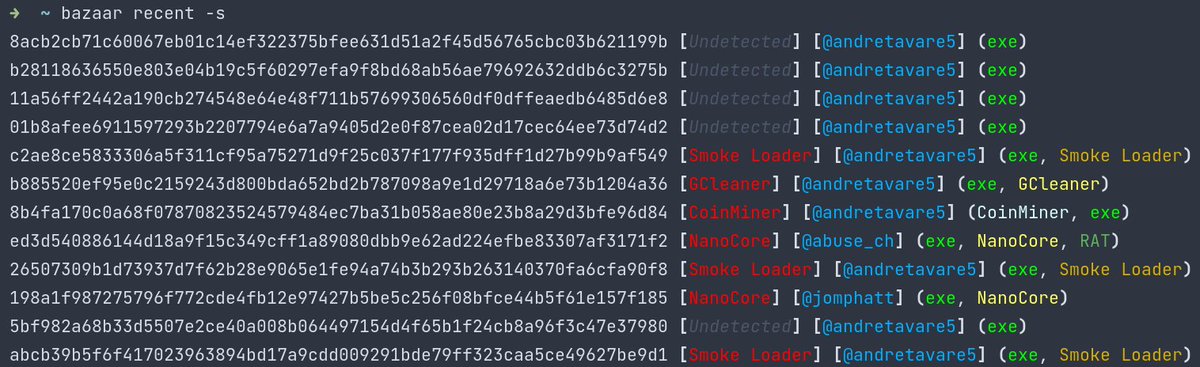
Johannes Bader retweetledi

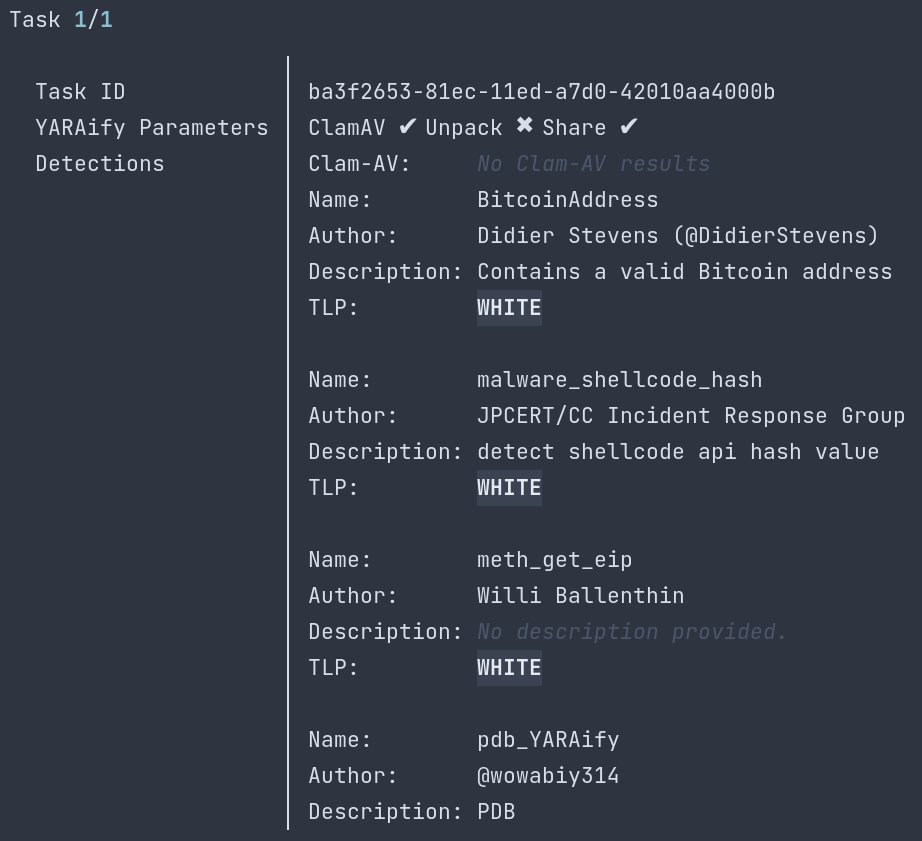
Just updated the "malwarebazaar" Python module to include a Python and CLI client for @abuse_ch #YARAify and added a "richer" output. You can find it on Github (github.com/3c7/bazaar/rel…) and on PyPI (via "malwarebazaar").
#threatintel #malware


English