Ch40zz
62 posts


Ch40zz
@Ch40zz_
Reverse Engineering, Windows Internals, Exploiting, Gamehacking Programming Languages: C/C++, x86/x64 Assembly, C#, Python, JS, PHP


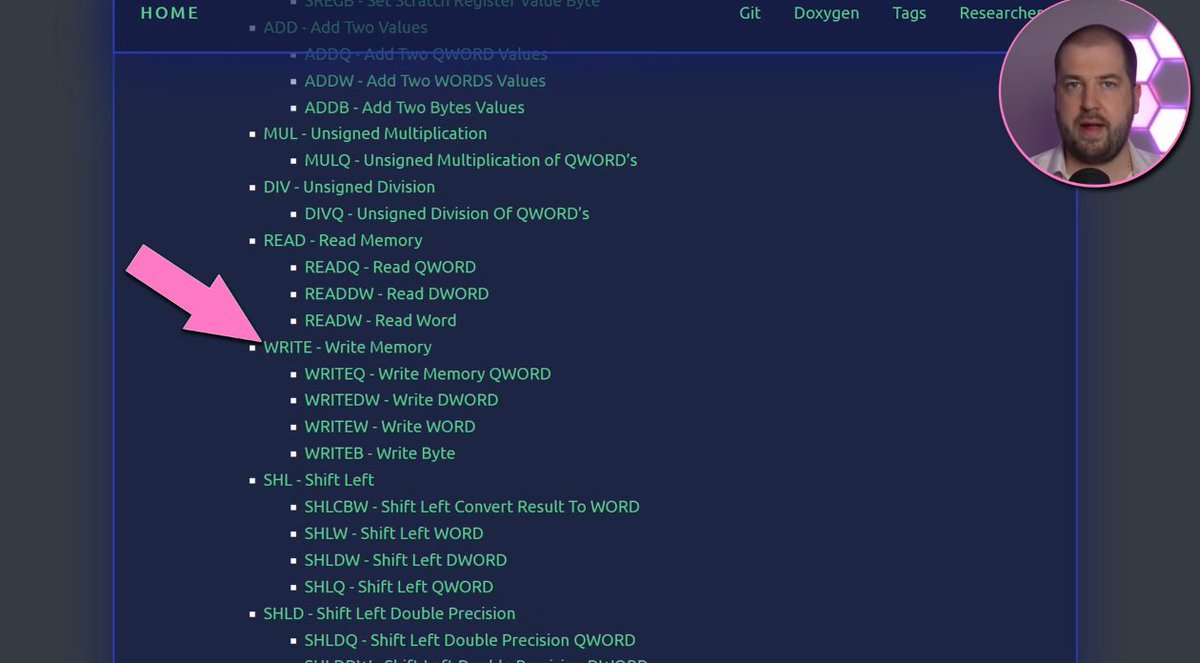







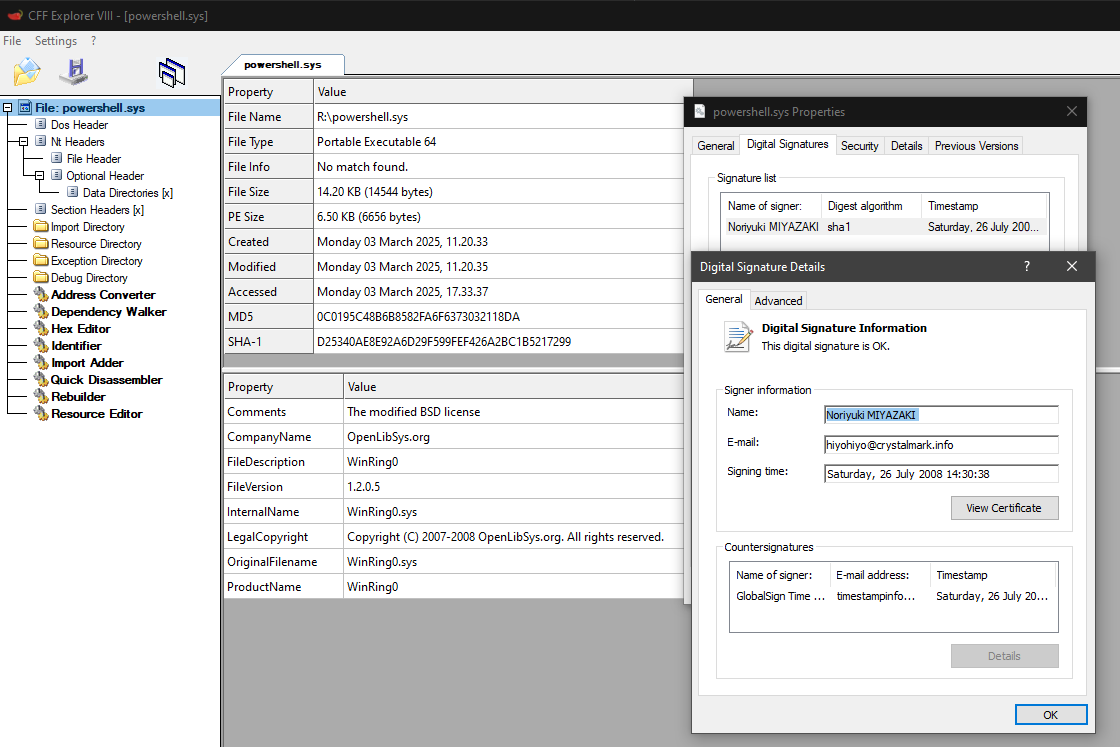




🎯 #Ransomware аbuses a game and spreads with a valid certificate – #ExploreWithANYRUN 📌 #Malware uses legitimate #certificate from COGNOSPHERE PTE. LTD ⚙ The XORed ransomware code is stored in the #DLL file. Our all-purpose #XOR extractor helps find out what was XORed by analyzing #MalConf 🔀 #Kransom ransomware hijacks the execution flow through DLL side-loading ⚠ This malware won't function without the DLL file, which is stored in the same folder as the game, and contains the #encrypted code 📍 The #StarRail #software used by this malware for masquerading is legitimate 📝 The note contains the following text: I believe you've encountered some problems. Email to hoyoverse for solutions. Analysis 👉 app.any.run/tasks/9835858b… DLL file 👉 app.any.run/tasks/b6366c04… 🔎 Find more samples using this #TI request 👉 intelligence.any.run/analysis/looku… Analyze and investigate the latest malware and #phishing threats with #ANYRUN 🛡️