Software supply chain attacks are getting sneakier.
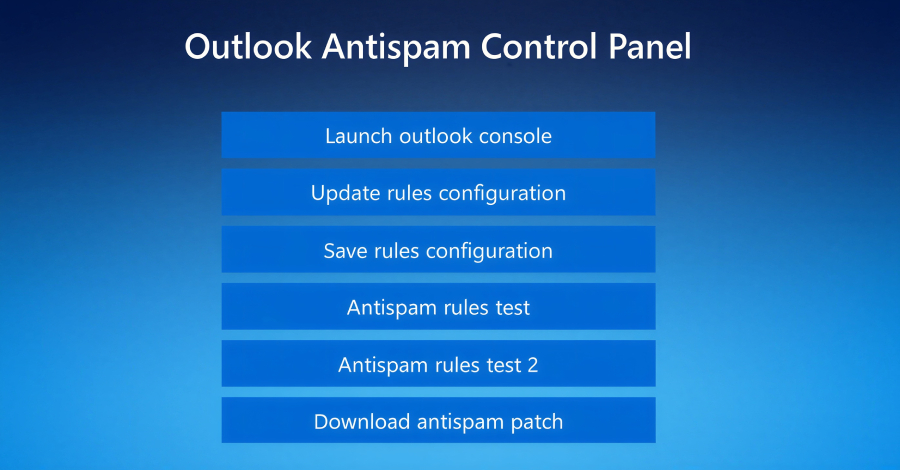
This campaign abuses trusted dev tools to steal credentials during routine workflows. No obvious malware. Attackers don’t break in. They log in.
This is happening now. Most defenses aren’t built for it.
hubs.la/Q048gdss0
English