
Polyhedra isn’t just research, we’re building an ecosystem. In 2025 alone we’ve launched marketplaces and formed alliances to shape the future of trustworthy AI 👇
CryptoRaul 🛡️
4.3K posts


@CryptoLoverRaul
Coder x Techie 🧑💻💻| Web3 Voyager 😎 | Moderator @PolyhedraZK GGMU 🔴

Polyhedra isn’t just research, we’re building an ecosystem. In 2025 alone we’ve launched marketplaces and formed alliances to shape the future of trustworthy AI 👇


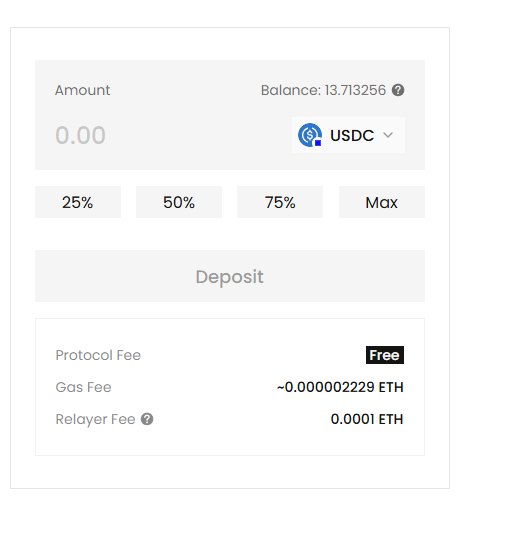
𝗜𝗻𝘀𝗶𝗱𝗲 𝗢𝗰𝗮𝘀𝗵 - 𝗖𝗼𝗺𝗽𝗹𝗶𝗮𝗻𝗰𝗲 𝗪𝗶𝘁𝗵𝗼𝘂𝘁 𝗘𝘅𝗽𝗼𝘀𝘂𝗿𝗲 Financial regulations require compliance, but they shouldn’t require exposing personal data. With 𝘖𝘤𝘢𝘴𝘩, identity information like ID and DOB can be verified through ZKML — without revealing it publicly. Taken from The Polyhedra Show with Sam Pearton & @Tiancheng_Xie: youtube.com/watch?v=UW0KWo…



Join Sam Pearton and @Tiancheng_Xie for a week of live shows and fun. Verified community members engaging will win USDT. Make sure to join our Discord to be eligible for rewards discord.com/invite/polyhed…

🐎 𝗥𝗶𝗱𝗶𝗻𝗴 𝗶𝗻𝘁𝗼 𝘁𝗵𝗲 𝗬𝗲𝗮𝗿 𝗼𝗳 𝘁𝗵𝗲 𝗛𝗼𝗿𝘀𝗲 Over the past year, the Polyhedra ecosystem has continued advancing across multiple frontiers — from verifiable AI and zkML breakthroughs, to the ongoing development of EXPchain as foundational proof infrastructure. 2025 also marked a major product milestone with the launch of Ocash Mainnet Alpha, bringing private, verifiable payments into live production and powering real on-chain activity across the ecosystem. With multi-chain integrations, growing transaction flows, and expanding wallet support, Ocash has begun establishing the rails for programmable, privacy-preserving financial systems, with continued focus on mobile accessibility, DEX connectivity, and developer tooling to support real-world payment use cases. As we enter the Year of the Horse, the focus shifts toward scale — accelerating payment adoption, expanding ecosystem partnerships, and enabling infrastructure designed to support real economic activity, from everyday user payments to programmable fund flows and AI-assisted financial operations. 🥂Wishing our global community momentum, resilience, and prosperity in the year ahead. 跃马扬鞭,共赴新程!

💖𝗣𝗿𝗼𝗼𝗳 𝗼𝗳 𝗟𝗼𝘃𝗲 — 𝗢𝗳𝗳𝗶𝗰𝗶𝗮𝗹𝗹𝘆 𝗪𝗿𝗮𝗽𝗽𝗲𝗱 Over the past weeks, we’ve seen incredible participation — from community energy and creator stories to real on-chain activity across the 𝘖𝘤𝘢𝘴𝘩 ecosystem. Thank you to everyone who took part and made this campaign truly memorable. 🎁Rewards will be distributed automatically via Galxe — stay tuned and keep an eye on your wallet. As 𝘖𝘤𝘢𝘴𝘩 continues to expand its private payment rails, more product-driven campaigns and community initiatives are already underway. Try 𝘖𝘤𝘢𝘴𝘩 Mainnet today: 👉 o.cash




💗𝗣𝗿𝗼𝗼𝗳 𝗼𝗳 𝗟𝗼𝘃𝗲 — 𝙊𝙘𝙖𝙨𝙝 𝗩𝗮𝗹𝗲𝗻𝘁𝗶𝗻𝗲 𝗖𝗮𝗺𝗽𝗮𝗶𝗴𝗻 This Valentine’s Day, share the love with Ocash and win a share of 30,000 𝗭𝗞𝗝. Two participation tracks: 🌱𝗖𝗼𝗺𝗺𝘂𝗻𝗶𝘁𝘆 𝗚𝗿𝗼𝘄𝘁𝗵 𝗧𝗿𝗮𝗰𝗸 · Complete Valentine community tasks on Galxe (Follow, Discord, Quote RT) · 10 winners share 10,000 ZKJ equally · Tasks can be completed anytime before the draw ✍️𝗖𝗼𝗻𝘁𝗲𝗻𝘁 𝗖𝗿𝗲𝗮𝘁𝗶𝗼𝗻 𝗧𝗿𝗮𝗰𝗸 · Post Ocash tutorials or usage experiences on X · Submit your post link + EVM wallet address before deadline · 20 winners share 20,000 ZKJ equally ⚠️𝗥𝘂𝗹𝗲𝘀 · One entry per wallet per track · Winners selected by random draw ⏰𝗖𝗮𝗺𝗽𝗮𝗶𝗴𝗻 𝗣𝗲𝗿𝗶𝗼𝗱 2026.02.02 00:00 UTC – 2026.02.15 23:59 UTC 💘𝗠𝗮𝗸𝗲 𝘁𝗵𝗶𝘀 𝗩𝗮𝗹𝗲𝗻𝘁𝗶𝗻𝗲’𝘀 𝗗𝗮𝘆 𝗰𝗼𝘂𝗻𝘁. 📑Check full participation guidelines: blog.polyhedra.network/proof-of-love-… Join Proof of Love now: app.galxe.com/quest/polyhedra






💗𝗣𝗿𝗼𝗼𝗳 𝗼𝗳 𝗟𝗼𝘃𝗲 — 𝙊𝙘𝙖𝙨𝙝 𝗩𝗮𝗹𝗲𝗻𝘁𝗶𝗻𝗲 𝗖𝗮𝗺𝗽𝗮𝗶𝗴𝗻 This Valentine’s Day, share the love with Ocash and win a share of 30,000 𝗭𝗞𝗝. Two participation tracks: 🌱𝗖𝗼𝗺𝗺𝘂𝗻𝗶𝘁𝘆 𝗚𝗿𝗼𝘄𝘁𝗵 𝗧𝗿𝗮𝗰𝗸 · Complete Valentine community tasks on Galxe (Follow, Discord, Quote RT) · 10 winners share 10,000 ZKJ equally · Tasks can be completed anytime before the draw ✍️𝗖𝗼𝗻𝘁𝗲𝗻𝘁 𝗖𝗿𝗲𝗮𝘁𝗶𝗼𝗻 𝗧𝗿𝗮𝗰𝗸 · Post Ocash tutorials or usage experiences on X · Submit your post link + EVM wallet address before deadline · 20 winners share 20,000 ZKJ equally ⚠️𝗥𝘂𝗹𝗲𝘀 · One entry per wallet per track · Winners selected by random draw ⏰𝗖𝗮𝗺𝗽𝗮𝗶𝗴𝗻 𝗣𝗲𝗿𝗶𝗼𝗱 2026.02.02 00:00 UTC – 2026.02.15 23:59 UTC 💘𝗠𝗮𝗸𝗲 𝘁𝗵𝗶𝘀 𝗩𝗮𝗹𝗲𝗻𝘁𝗶𝗻𝗲’𝘀 𝗗𝗮𝘆 𝗰𝗼𝘂𝗻𝘁. 📑Check full participation guidelines: blog.polyhedra.network/proof-of-love-… Join Proof of Love now: app.galxe.com/quest/polyhedra

Be honest , you don’t actually understand how “private transactions” work. You just nod, retweet, and hope nobody asks questions. If someone asked you where the data is hidden, who can see it, and how the network still verifies it’s legit you’d probably change the topic. So let’s kill the pretending. Private transactions aren’t magic. They’re just systems where: The network can verify the transaction is valid without seeing what’s inside it, amount and participating addresses. These systems already run: • Private DeFi and dark pools • Confidential banking rails • Enterprise data-sharing networks • Secure AI & data marketplaces The part nobody tells you? • There isn’t one “privacy tech.” • There are completely different architectures doing this. Some hide data from outsiders. Some hide it from validators. Some even hide it from the apps themselves. These privacy architectures are explained below. — ● Trusted Execution Environments (TEE) A TEE is a hardware-based secure enclave that runs code and processes data in isolation from the rest of the system. Examples: Intel SGX, AMD SEV, ARM TrustZone. When a private transaction runs inside a TEE, the CPU itself guarantees that: • Only the enclave can access certain memory areas. • Data is encrypted in memory and during computation. • The system can produce a remote attestation which is proof that a specific code ran in a genuine, untampered TEE. Strengths: • Fast: Near-native computation speed. • Developer-friendly: Code can be written in conventional languages (C++, Rust). • Hardware-protected: Prevents many external attacks. • Verifiable via attestation: Can prove computation integrity to others. Weaknesses: • Hardware trust assumption: You must trust Intel/AMD etc. • Vulnerable to side-channel attacks (e.g., Spectre, Meltdown). • Limited memory / scalability. • Single-point of failure: If the hardware vendor is compromised, privacy breaks. Shielding method: Hardware-enforced memory isolation and encryption. ● Multi-Party Computation (MPC) MPC allows multiple parties to jointly compute a function over their inputs without revealing those inputs to each other. It’s purely cryptographic . In private transactions, MPC can ensure: • Several parties jointly sign or verify transactions. • Secrets (like private keys or amounts) are never reconstructed in one place. Strengths: • No hardware trust needed. • High fault tolerance: No single party learns the full secret. • Can be used for threshold signing, key management, or private voting. Weaknesses: • Slower: Heavy on communication and computation. • Complex protocols: Hard to implement correctly. • Requires online participation of multiple parties. Shielding method: Secret sharing and distributed computation. ● Zero-Knowledge Proofs (ZKP) A ZKP allows someone (the prover) to prove to others (verifiers) that a statement is true without revealing any of the underlying information. For private transactions: You can prove a transaction followed the rules (balances match, no double spend) without showing sender, receiver, or amount. There are two main families: • zk-SNARKs (succinct, non-interactive) • zk-STARKs (transparent, scalable) Strengths: • Strong privacy guarantees. • Public verifiability — anyone can confirm validity. • Perfect for blockchain scalability (tiny proofs). • Math-based, no hardware trust. Weaknesses: • Complex math (elliptic curves, polynomial commitments). • Expensive proof generation (though improving fast). • Some require trusted setup (SNARKs, though STARKs avoid this). Shielding method: Mathematical proof replaces direct data disclosure. ● Homomorphic Encryption (HE) HE allows computation directly on encrypted data meaning you can get the encrypted result without ever decrypting inputs. It is used mostly in secure analytics or AI, but some confidential finance prototypes use it for processing balances or fees privately in the cloud. Strengths: • Data never decrypted for full confidentiality. • Powerful for cloud computing / ML on encrypted data. • Mathematically elegant. Weaknesses: • Extremely slow (orders of magnitude slower than plaintext). • Limited practical use (used for small-scale analytics, not full transactions). • Complex key management. Shielding method: Fully encrypted computation meaning that the processor never sees the data unencrypted — However the best models are the hybrid models. Modern privacy systems often combine these methods for optimal balance: ● TEE + ZKP: Enclave executes logic; ZKP proves correctness publicly (e.g., Secret Network + zkBridge). ● MPC + ZKP: Multi-party computation produces proofs of correct computation (e.g., zk-rollups with MPC-based proving). ● HE + MPC: For secure collaborative AI / federated learning. — Here’s the uncomfortable truth: Privacy isn’t a feature rather it’s an entire system design choice. So if you don’t understand whether a protocol relies on: • cryptography • hardware vendors • multi-party coordinators • or centralized operators then you don’t actually know what you’re using. You’re just hoping nothing goes wrong and hope is not a security model.

Most people think privacy in crypto is about hiding crimes. For everyday users, especially in places like Nigeria, it is about something simpler. Protecting your financial life from constant surveillance. Every transfer, every balance, every interaction being public is not freedom.

𝗧𝗵𝗲 𝙊𝘾𝙝𝙧𝙞𝙨𝙩𝙢𝙖𝙨 𝗹𝗲𝗮𝗱𝗲𝗿𝗯𝗼𝗮𝗿𝗱 𝗶𝘀 𝗹𝗼𝗰𝗸𝗲𝗱 🎄 One month of real on-chain activity. A tight race at the top. And here are your top performers: 🥇Top 1 𝗨𝗧𝗫𝗢𝘀: 30,350 𝗥𝗲𝘄𝗮𝗿𝗱 𝗯𝘆 𝗦𝗵𝗮𝗿𝗲: 78,215.6 𝗭𝗞𝗝𝗥𝗮𝗻𝗸𝗶𝗻𝗴 𝗥𝗲𝘄𝗮𝗿𝗱: 50,000 ZKJ 👉Total: 128,215.6 ZKJ 🥈Top 2 𝗨𝗧𝗫𝗢𝘀: 28,360 𝗥𝗲𝘄𝗮𝗿𝗱 𝗯𝘆 𝗦𝗵𝗮𝗿𝗲: 73,087.13 𝗭𝗞𝗝𝗥𝗮𝗻𝗸𝗶𝗻𝗴 𝗥𝗲𝘄𝗮𝗿𝗱: 30,000 ZKJ 👉𝗧𝗼𝘁𝗮𝗹: 103,087.13 ZKJ 🥉Top 3 𝗨𝗧𝗫𝗢𝘀: 26,492 𝗥𝗲𝘄𝗮𝗿𝗱 𝗯𝘆 𝗦𝗵𝗮𝗿𝗲: 68,273.07 𝗭𝗞𝗝𝗥𝗮𝗻𝗸𝗶𝗻𝗴 𝗥𝗲𝘄𝗮𝗿𝗱: 30,000 ZKJ 👉𝗧𝗼𝘁𝗮𝗹: 98,273.07 ZKJ 🎁𝗥𝗲𝘄𝗮𝗿𝗱𝘀 𝗮𝗿𝗲 𝗻𝗼𝘄 𝗰𝗹𝗮𝗶𝗺𝗮𝗯𝗹𝗲: Submit your EVM address on the campaign page now, and rewards will be distributed within 14 𝗯𝘂𝘀𝗶𝗻𝗲𝘀𝘀 𝗱𝗮𝘆𝘀 𝗽𝗼𝘀𝘁-𝗲𝘃𝗲𝗻𝘁. Respect to everyone who helped grow and improve 𝘖𝘤𝘢𝘴𝘩 through real private transactions this holiday season. 𝘖𝘊𝘩𝘳𝘪𝘴𝘵𝘮𝘢𝘴 was just the beginning. Bigger campaigns and stronger incentives are on the way. Explore Ocash Mainnet today: 🔗o.cash

𝗧𝗵𝗲 𝙊𝘾𝙝𝙧𝙞𝙨𝙩𝙢𝙖𝙨 𝗹𝗲𝗮𝗱𝗲𝗿𝗯𝗼𝗮𝗿𝗱 𝗶𝘀 𝗹𝗼𝗰𝗸𝗲𝗱 🎄 One month of real on-chain activity. A tight race at the top. And here are your top performers: 🥇Top 1 𝗨𝗧𝗫𝗢𝘀: 30,350 𝗥𝗲𝘄𝗮𝗿𝗱 𝗯𝘆 𝗦𝗵𝗮𝗿𝗲: 78,215.6 𝗭𝗞𝗝𝗥𝗮𝗻𝗸𝗶𝗻𝗴 𝗥𝗲𝘄𝗮𝗿𝗱: 50,000 ZKJ 👉Total: 128,215.6 ZKJ 🥈Top 2 𝗨𝗧𝗫𝗢𝘀: 28,360 𝗥𝗲𝘄𝗮𝗿𝗱 𝗯𝘆 𝗦𝗵𝗮𝗿𝗲: 73,087.13 𝗭𝗞𝗝𝗥𝗮𝗻𝗸𝗶𝗻𝗴 𝗥𝗲𝘄𝗮𝗿𝗱: 30,000 ZKJ 👉𝗧𝗼𝘁𝗮𝗹: 103,087.13 ZKJ 🥉Top 3 𝗨𝗧𝗫𝗢𝘀: 26,492 𝗥𝗲𝘄𝗮𝗿𝗱 𝗯𝘆 𝗦𝗵𝗮𝗿𝗲: 68,273.07 𝗭𝗞𝗝𝗥𝗮𝗻𝗸𝗶𝗻𝗴 𝗥𝗲𝘄𝗮𝗿𝗱: 30,000 ZKJ 👉𝗧𝗼𝘁𝗮𝗹: 98,273.07 ZKJ 🎁𝗥𝗲𝘄𝗮𝗿𝗱𝘀 𝗮𝗿𝗲 𝗻𝗼𝘄 𝗰𝗹𝗮𝗶𝗺𝗮𝗯𝗹𝗲: Submit your EVM address on the campaign page now, and rewards will be distributed within 14 𝗯𝘂𝘀𝗶𝗻𝗲𝘀𝘀 𝗱𝗮𝘆𝘀 𝗽𝗼𝘀𝘁-𝗲𝘃𝗲𝗻𝘁. Respect to everyone who helped grow and improve 𝘖𝘤𝘢𝘴𝘩 through real private transactions this holiday season. 𝘖𝘊𝘩𝘳𝘪𝘴𝘵𝘮𝘢𝘴 was just the beginning. Bigger campaigns and stronger incentives are on the way. Explore Ocash Mainnet today: 🔗o.cash
