Jiantao Li retweetledi

Ever wondered what happens when you pickle a mailbox? 🥒📬
(No, it’s not a recipe, it’s a vulnerability.)
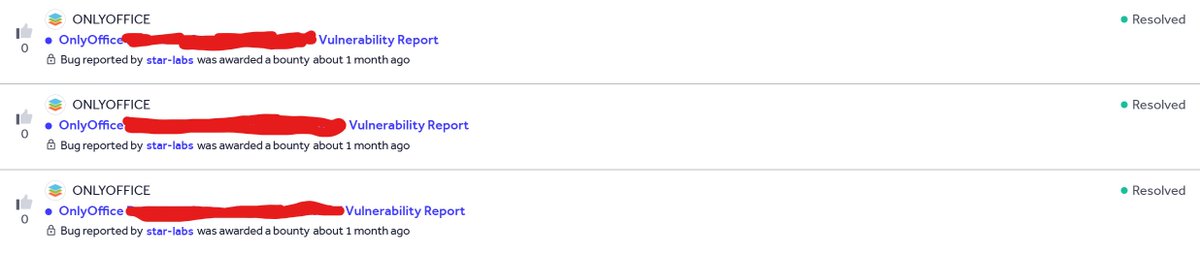
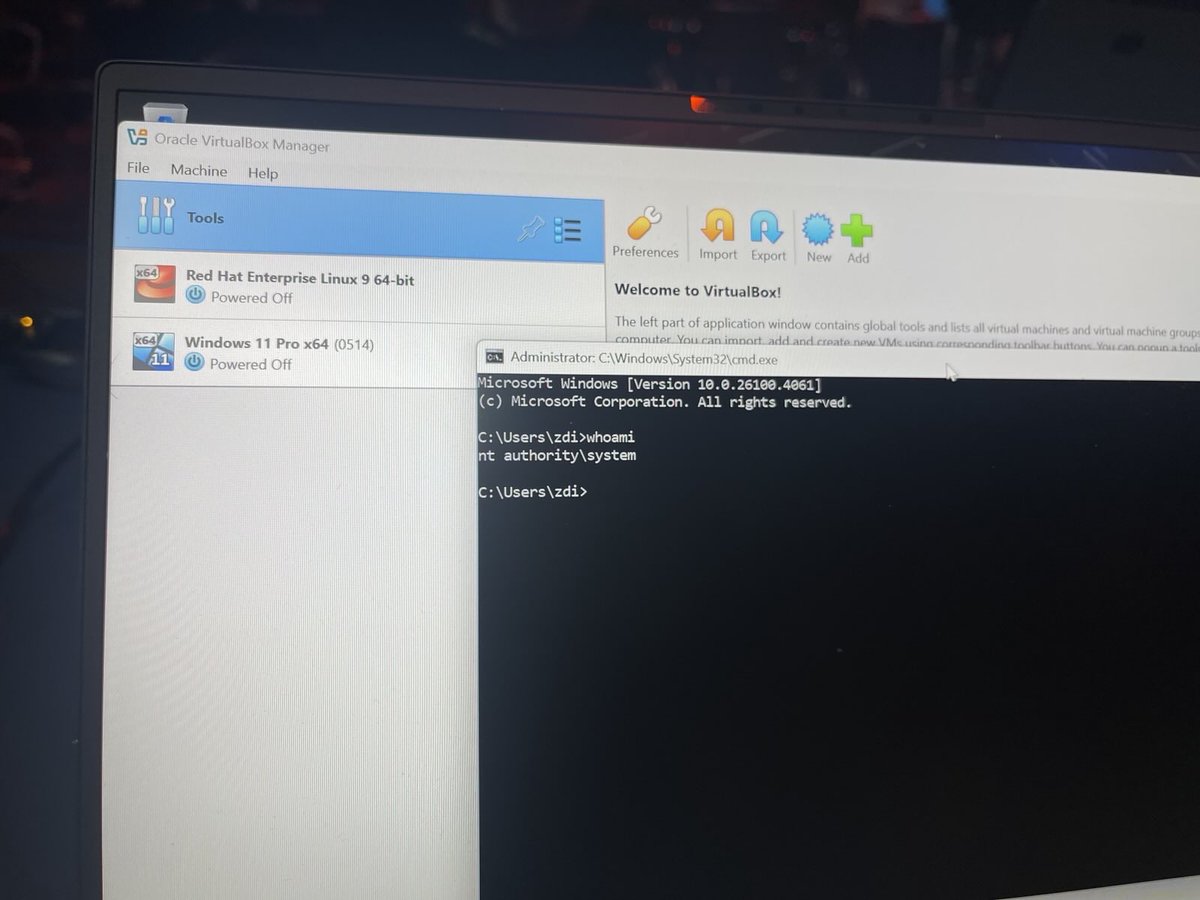
Our team breaks down CVE-2025-20393 in a new deep dive post covering root cause, internals & exploitation details
starlabs.sg/blog/2026/01-p…
Written by @CurseRed & @bestswngs
English