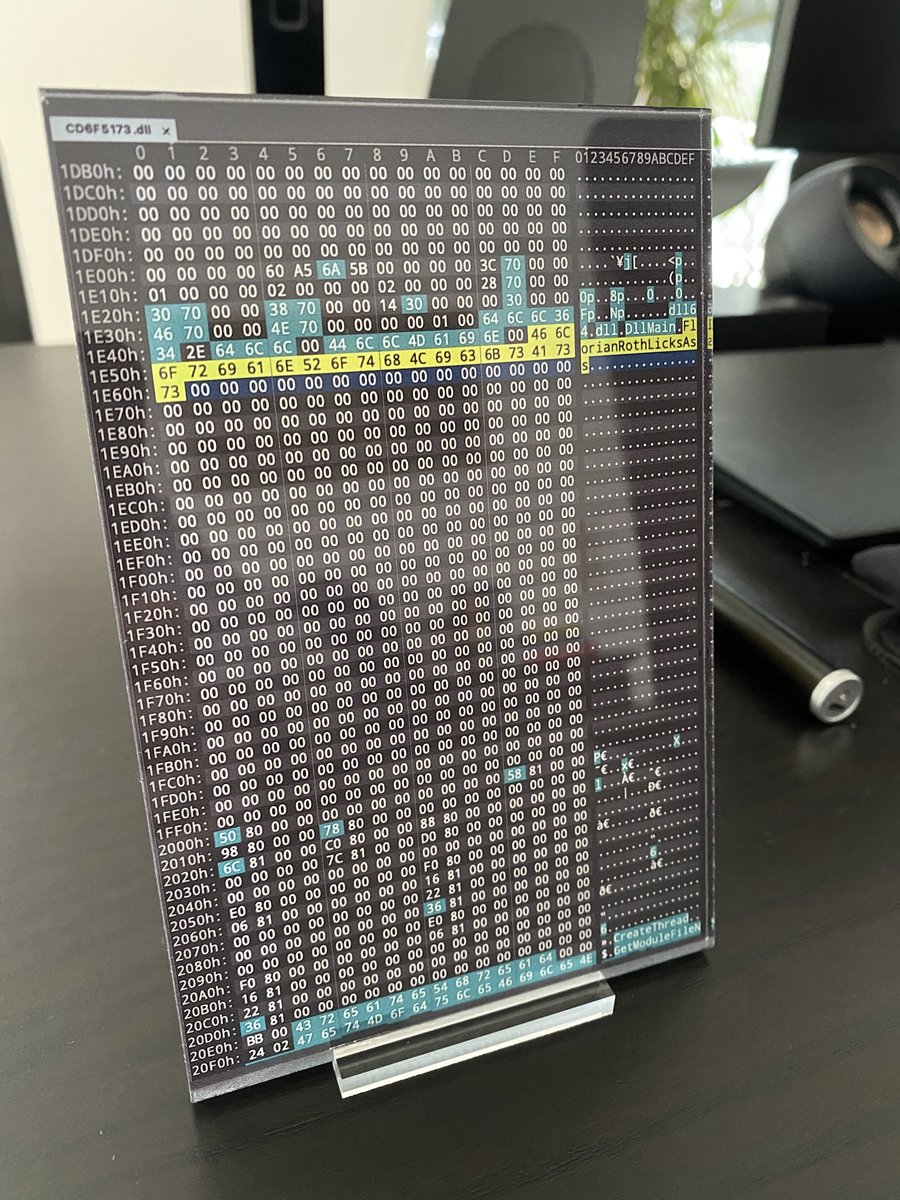
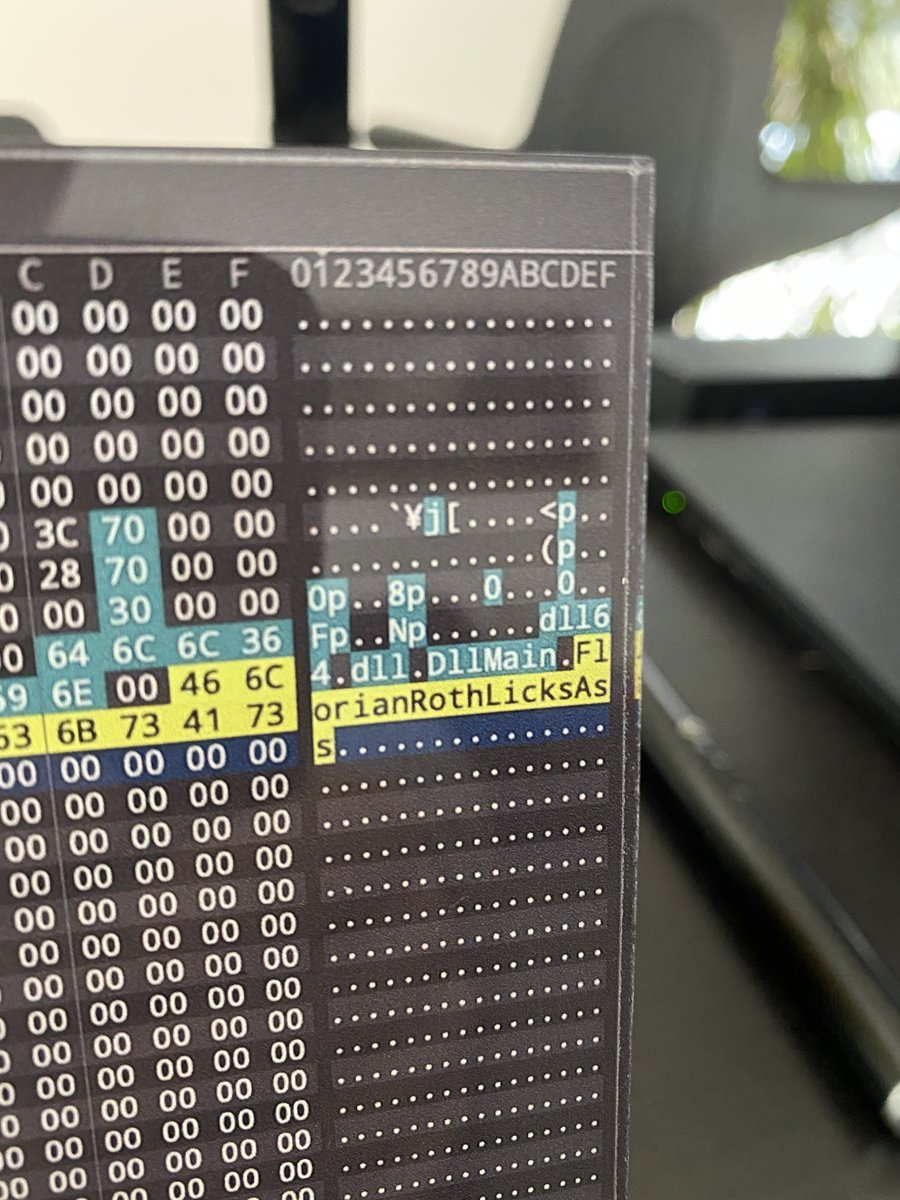
It seems that I have some fans over in Russia 🐻 #TurlaLicksAss thx to the FireEye analyst who brought this to my attention virustotal.com/gui/file/4417c…
Florian Roth ⚡️
37.1K posts


@cyb3rops
Head of Research @nextronsystems #DFIR #YARA #Sigma | detection engineer | creator of @thor_scanner, Aurora, Sigma, LOKI, YARA-Forge | always busy ⌚️🐇 | vi/vim

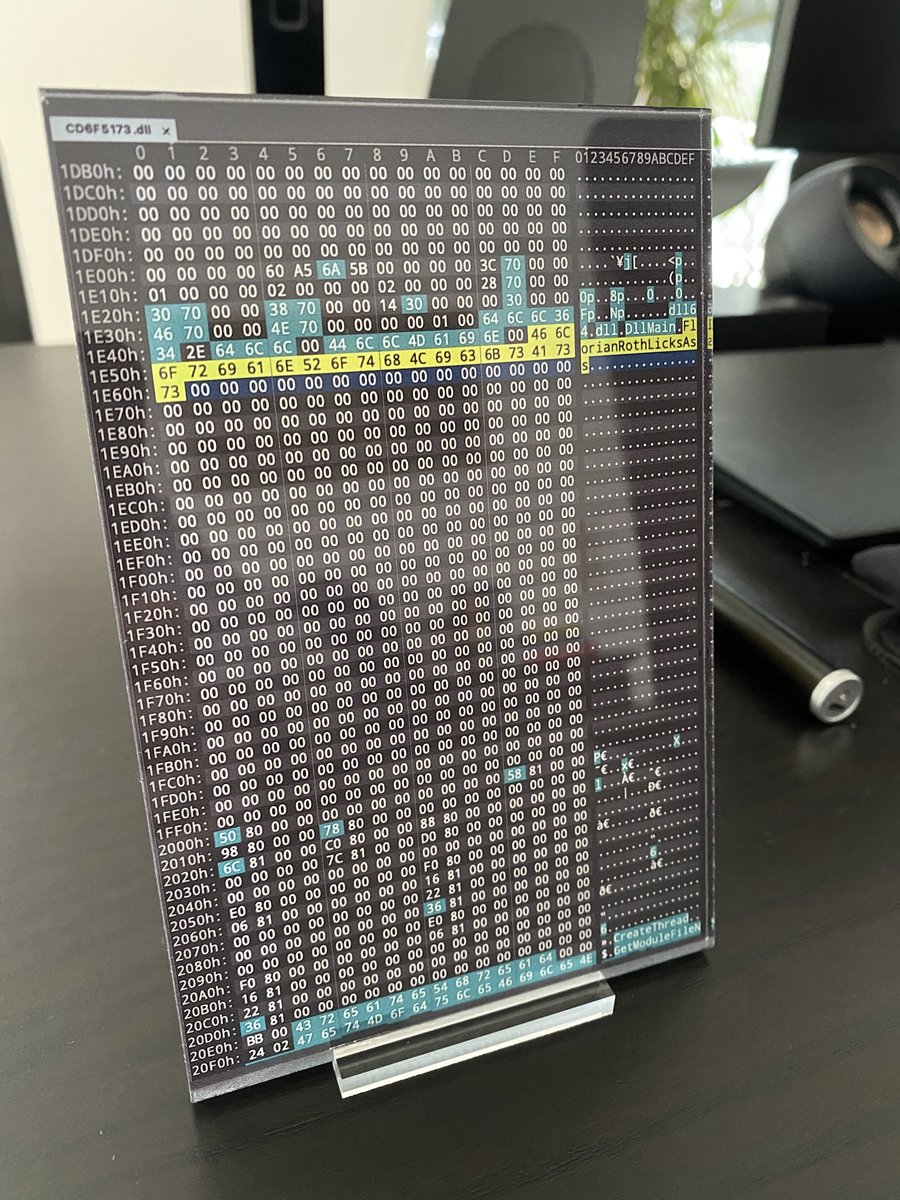
It seems that I have some fans over in Russia 🐻 #TurlaLicksAss thx to the FireEye analyst who brought this to my attention virustotal.com/gui/file/4417c…





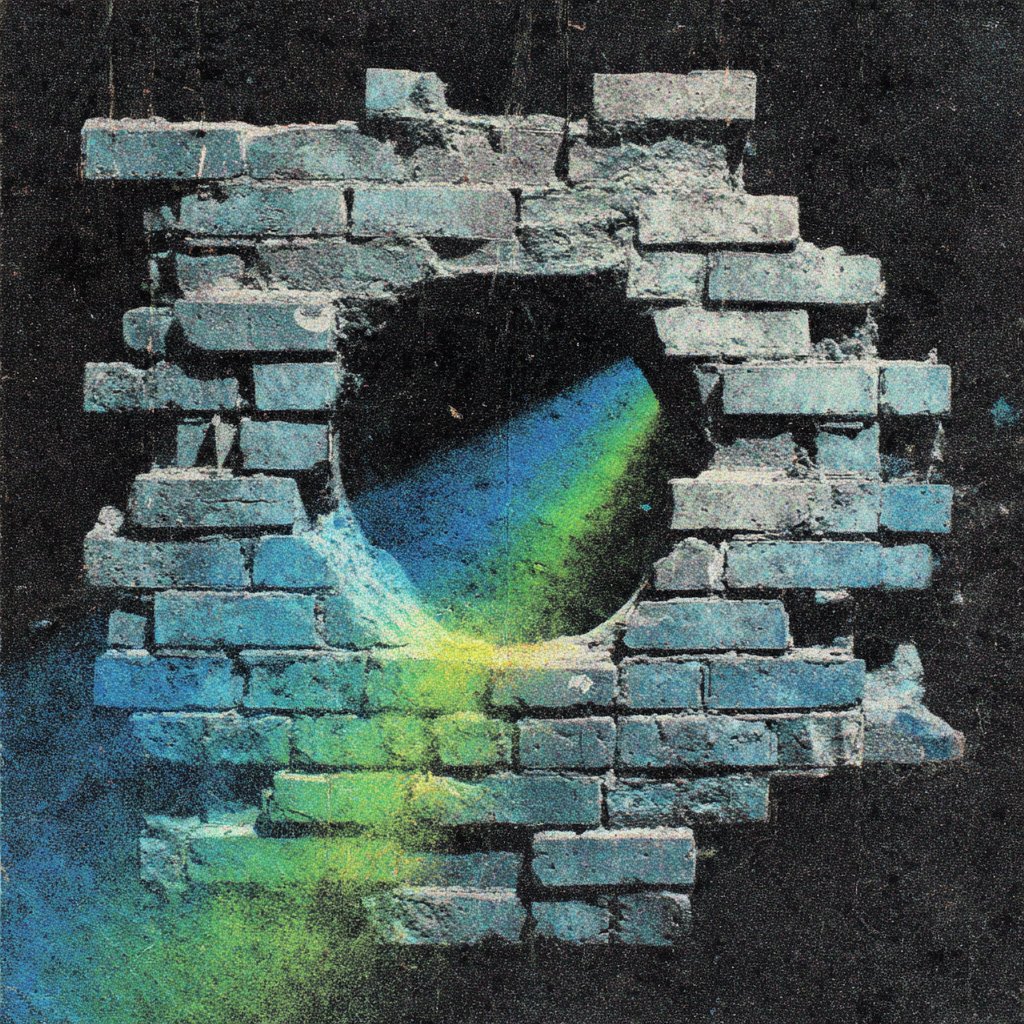


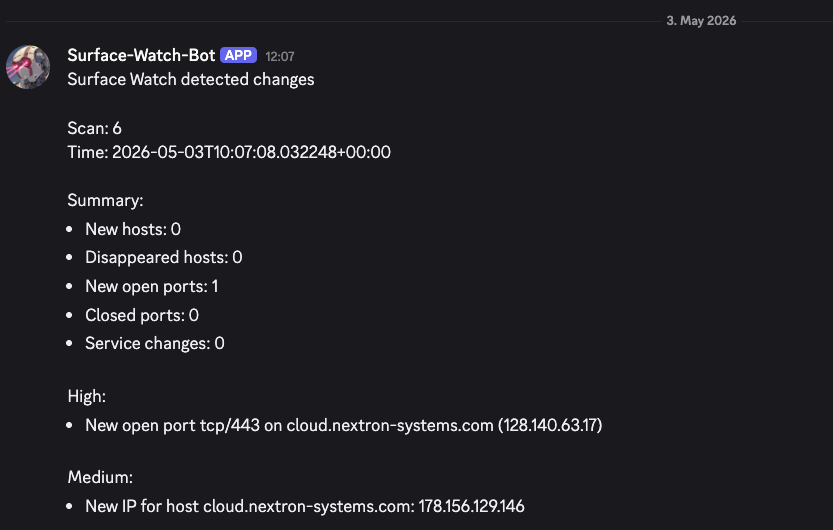



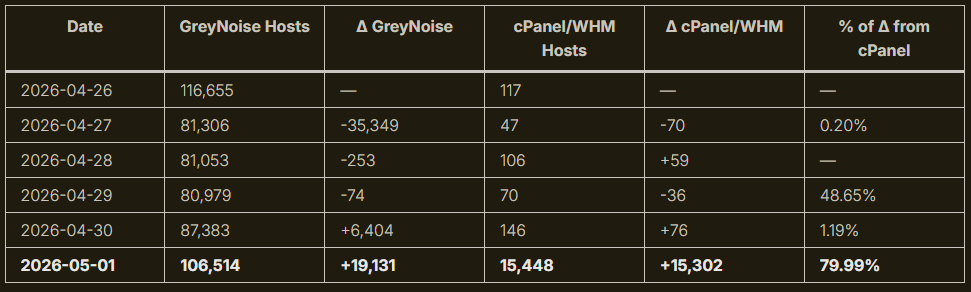
Anyone else seeing Microsoft #Defender flagging #DigiCert root certificate registry keys as malware? We’ve seen reports that Defender signature update from April 30 added a detection called: Trojan:Win32/Cerdigent.A!dha In some environments, Defender apparently detected DigiCert Root CA certificate registry entries and removed them from the trust store. The affected cert hashes mentioned so far: 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 DDFB16CD4931C973A2037D3FC83A4D7D775D05E4 Example path: HKLM\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 There’s also a Reddit comment suggesting Microsoft has started restoring the certs and that admins can check this via Advanced Hunting in Defender: DeviceRegistryEvents | where RegistryKey contains "0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43" or RegistryKey contains "DDFB16CD4931C973A2037D3FC83A4D7D775D05E4" | where ActionType == "RegistryKeyCreated" | where Timestamp > datetime(2026-05-03T04:00:00) | project Timestamp, DeviceName, ActionType, InitiatingProcessFileName | order by Timestamp desc On an affected device, this can also be checked with: certutil -store AuthRoot | findstr -i "digicert" Could become an annoying day for admins if this spreads reddit.com/r/cybersecurit…



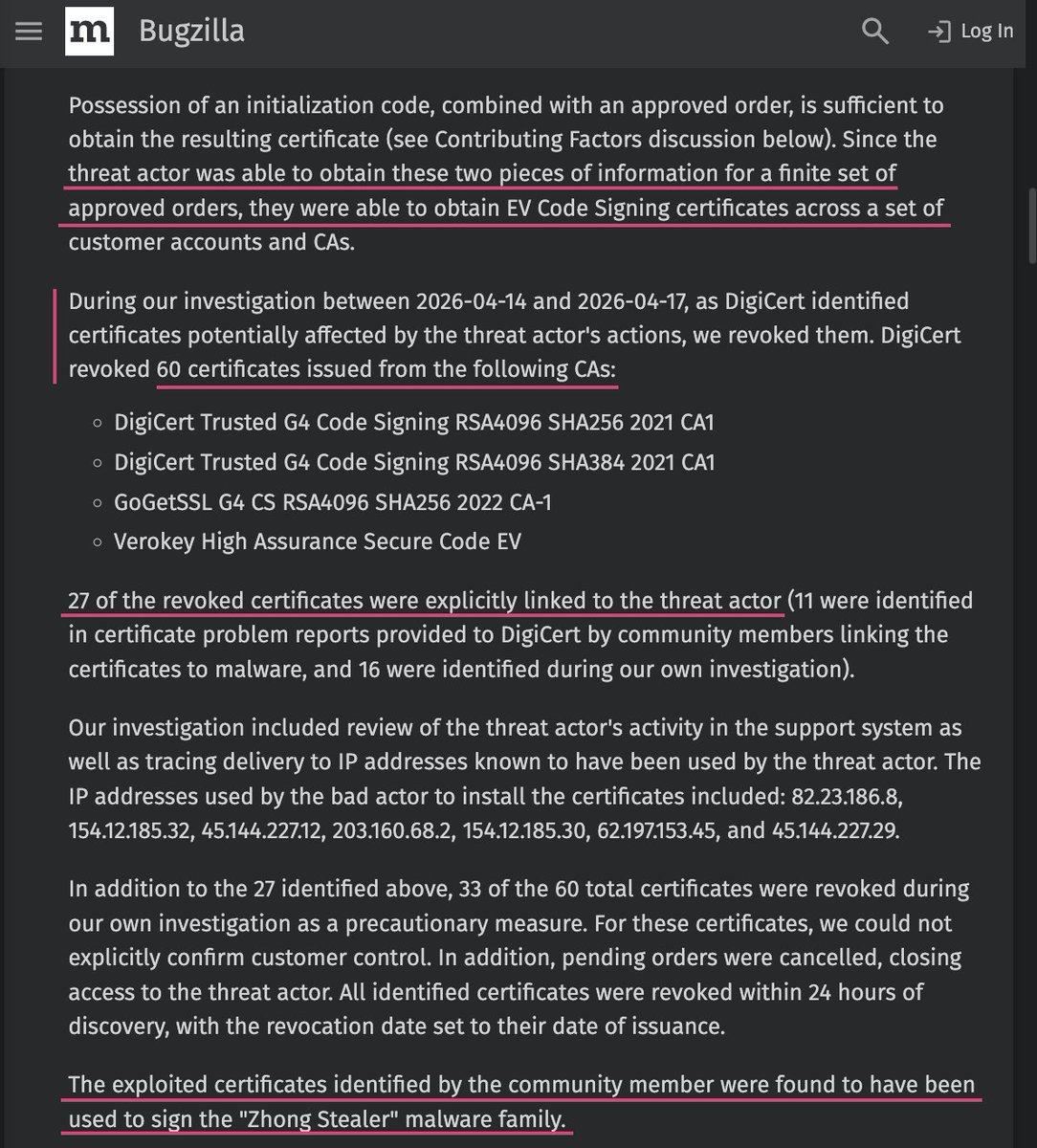
Okay, wow bugzilla.mozilla.org/show_bug.cgi?i…




Anyone else seeing Microsoft #Defender flagging #DigiCert root certificate registry keys as malware? We’ve seen reports that Defender signature update from April 30 added a detection called: Trojan:Win32/Cerdigent.A!dha In some environments, Defender apparently detected DigiCert Root CA certificate registry entries and removed them from the trust store. The affected cert hashes mentioned so far: 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 DDFB16CD4931C973A2037D3FC83A4D7D775D05E4 Example path: HKLM\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 There’s also a Reddit comment suggesting Microsoft has started restoring the certs and that admins can check this via Advanced Hunting in Defender: DeviceRegistryEvents | where RegistryKey contains "0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43" or RegistryKey contains "DDFB16CD4931C973A2037D3FC83A4D7D775D05E4" | where ActionType == "RegistryKeyCreated" | where Timestamp > datetime(2026-05-03T04:00:00) | project Timestamp, DeviceName, ActionType, InitiatingProcessFileName | order by Timestamp desc On an affected device, this can also be checked with: certutil -store AuthRoot | findstr -i "digicert" Could become an annoying day for admins if this spreads reddit.com/r/cybersecurit…

In Politico today: Senior 🇪🇺 official admits greater public scrutiny of DSA has lead to meetings becoming secret and his staff using Signal to communicate—thereby making it virtually impossible for voters/journalists to probe work of this EU department. Something to hide?

🚨 BREAKING FROM FFO 🚨 23 US-Funded Organizations Drive The EU’s War on Tech Companies