Squiblydoo
2K posts


Squiblydoo
@SquiblydooBlog
Malware Analysis Creator of Debloat, certReport, and https://t.co/hEJGt0jzIq Want to chat? Join the Debloat discord: https://t.co/ZcWIqa6ZA9









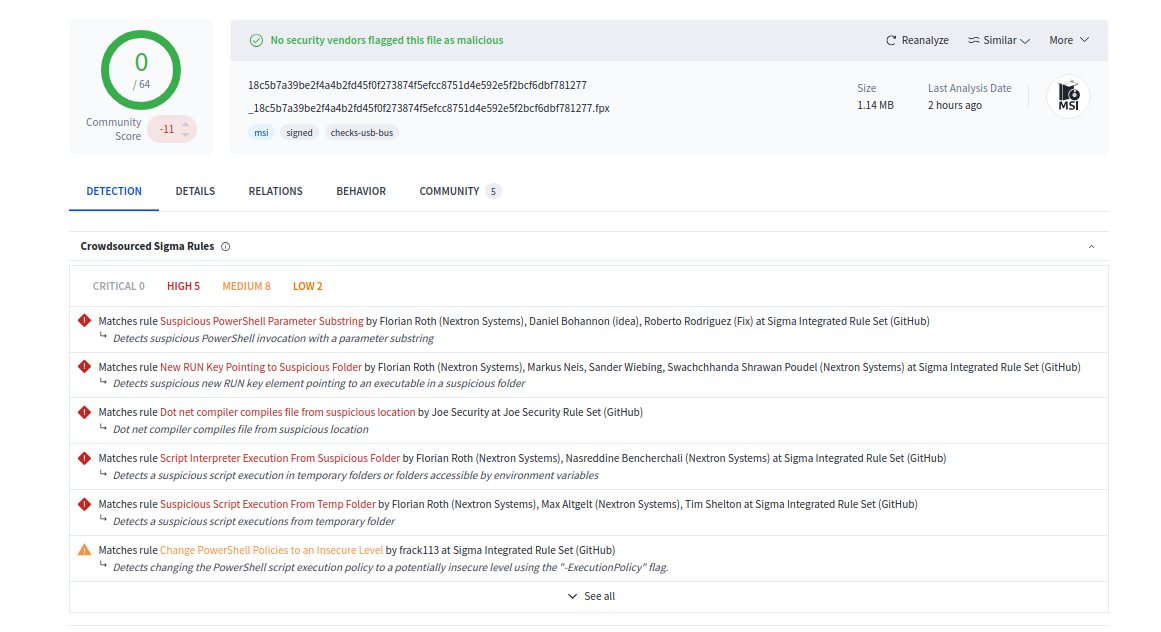
What do Lenovo, Kingston, Shuttle Inc, and Palit Microsystems have in common? EV Certificates from these companies were issued and used by a Chinese crime group, #GoldenEyeDog (#APT-Q-27)! Thanks @malwrhunterteam and @g0njxa for your contributions 1/7










We didn't know how an actor was using EV Certificates issued to Lenovo and others. We now do. From DigiCert's incident report: "the threat actor used a compromised analyst endpoint to access DigiCert's internal support portal. The threat actor used a limited function within the customer-support portal which allows authenticated DigiCert support analysts to access customer accounts from the customer's perspective to facilitate support tasks. The threat actor was able to use this function to access initialization codes for orders that were approved but pending delivery for EV Code Signing certificate orders across a finite set of customer accounts." "Possession of the initialization code, combined with an approved order, is functionally sufficient to generate and retrieve the corresponding certificate." The full report can be found here and explains the incident in great detail: bugzilla.mozilla.org/show_bug.cgi?i… The report mentions "Where we got lucky: A community member involved in security research reported the evolving pattern of misused certificates and engaged in dialogue with our support team. Without that report, the undetected compromise of ENDPOINT2 and the associated mis-issuance might have remained undiscovered for a longer period." Special thanks goes to the regular contributors to the Cert Graveyard; @g0njxa , @malwrhunterteam , and others. Also special thanks to DigiCert: this report has a high level of transparency, which is warranted, and also well executed.