
Julian Derry
5.6K posts

@CyberSamuraiDev
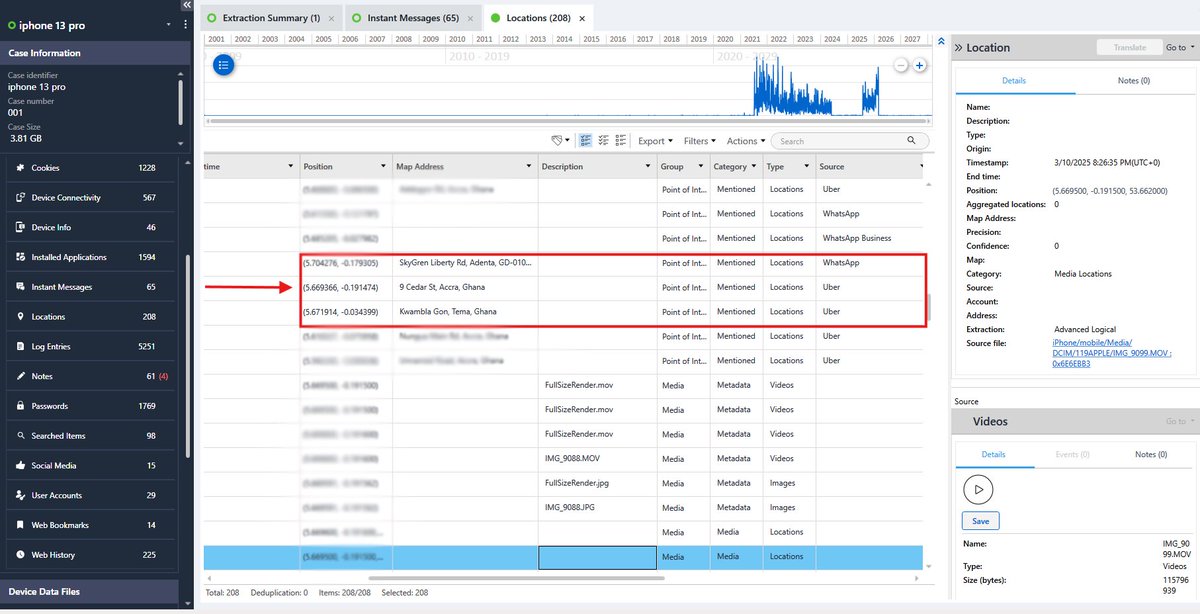
Digital Forensics & Investigations | Mobile & Computer I break down what devices don’t forget



Dear Microsoft, when I hit the Windows Start menu key and start typing a word to autocomplete a search, I never, ever, EVER want it to return results of something not on my computer. Ever. Like, ever, ever, never.


‘MICHAEL’ is set to cross $300M at the worldwide box office.








Takes 5 vehicles and 8+ hours of travelling for me to move from Campus to home. From Ayeduase newsite - Tech Junction - Asafo - Amasaman - Ashaiman - Golf City I don't take travelling mercies for granted at all🥹