Mustapha Olawale ELIAS
101 posts


Mustapha Olawale ELIAS
@Cyber_AT0M
Studying Cybersecurity at Osun State University||Specializing in Cloud Security||Blue Team Aspirant||Actively developing skills in Cyber Defense and offense.


Day 26: Zero Trust Architecture🛡️ The old "Castle and Moat" security is dead🏰 Zero Trust means every request must be: ✅ Authenticated ✅ Authorized ✅ Encrypted Trust nothing Verify everything🔐 @DefendWithFelix @malik_cybersec #CyberSecurity #30DayChallenge #ZeroTrust #Day26

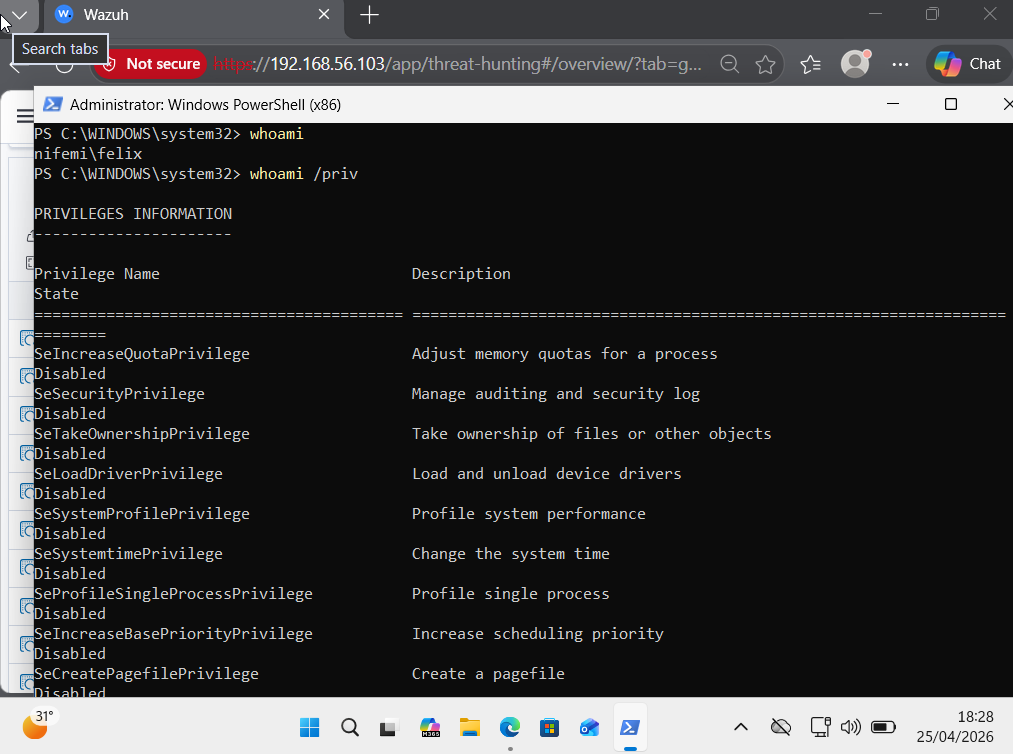
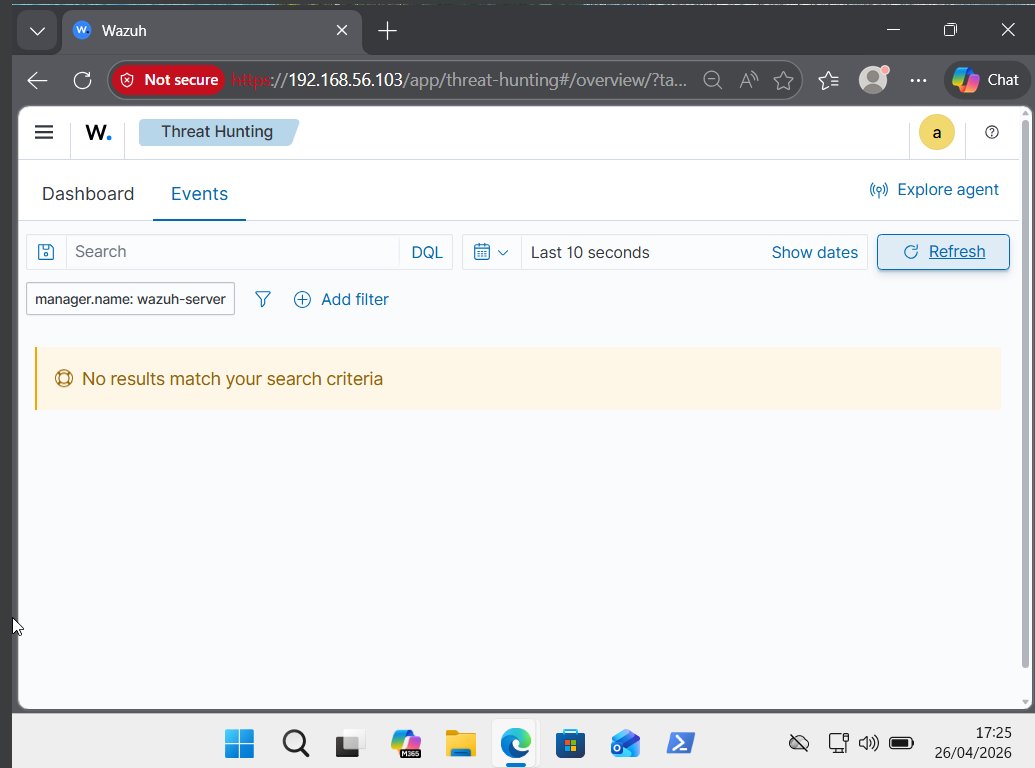
Days 25 & 26 of #30DaysOfSOC and I tried to detect recon attacks in my home lab👀 whoami. net user. tasklist. systeminfo. ipconfig all the classic attacker recon commands Wazuh didn't alert. That gap taught me more than any detection would have #SecFelix #Cybersecurity #BlueTeam

#Day25: cont'd Cloud Learnt that in Cloud IDENTITY is the new perimeter IAM(Identity&Access Management)(Least Privilege)🛡️ Only give users the exact access they need to do their job:nothing more MFA+StrongIAM=A hacker’s nightmare🔐 #CyberSecurity #CloudSecurity #30DayChallenge

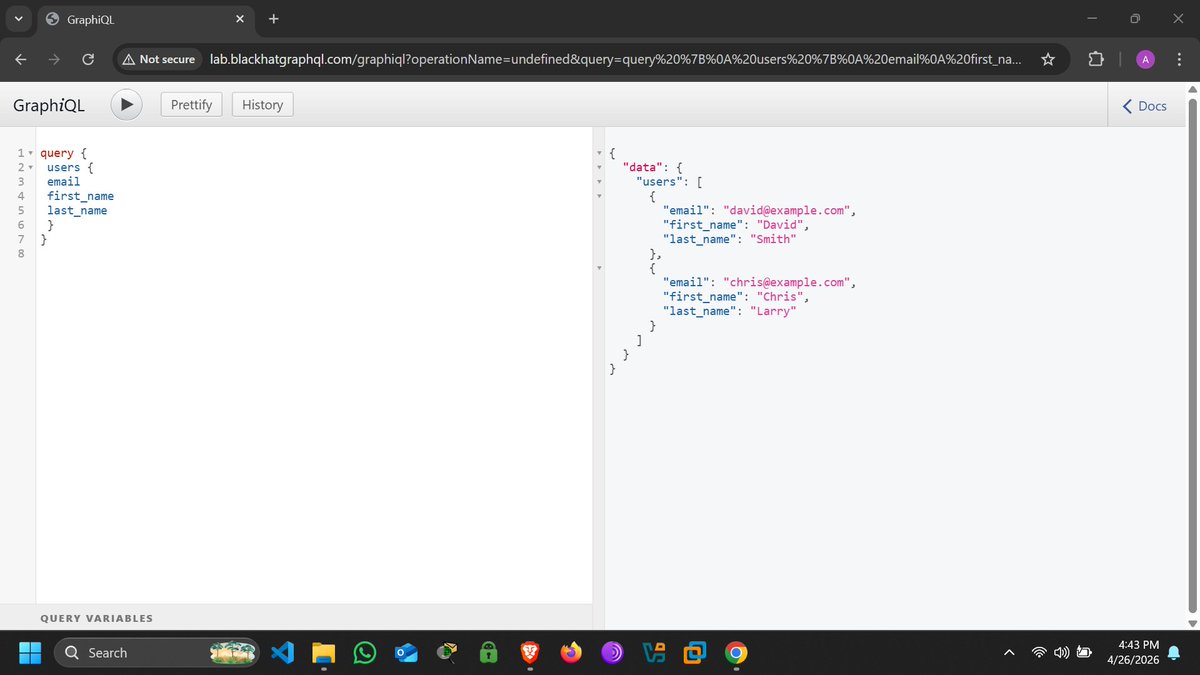

Day 26/#30DaysofAPIsecU Continue learning GraphQL by reading this book by @hAPI_hacker building my skills around API hacking @akintunero @commando_skiipz @ce3nerd @KoredeSec






#Day24: Learnt the basics of Cloud Security☁️🛡️ Security is a team effort🤝 AWS/Azure secures the building-you secure the vault Tips: Check your configurations Don't leave the digital door wide open!🚪🔓 #CloudSecurity #TechTips #30dayschallenge @DefendWithFelix @malik_cybersec




#Day23 Learnt the basics of Incident Response🚨 When a hack is live, every second counts The 4-step cycle: 1️⃣Preparation-Be ready before it hits 2️⃣Detection-Spot the threat 3️⃣Containment-Stop the spread 4️⃣Recovery-Get back to work #CyberSecurity #30DayChallenge #IncidentResponse

#Day22: The Digital Crime Scene 🔍 When a hack happens, DIGITAL FORENSICS steps in 📥Acquisition: Collecting data without changing it 🧬Analysis: Finding hidden tracks 📄Reporting: Turning logs into evidence In the digital world, everything leaves a footprint👣🛡️ #CyberSecurity






Day 22 of #30DaysOfSOC ✅ Completed Part 2 of Malware Analysis Tactics, Techniques and Behaviours. 🦠 Diving deeper into how malware operates and mapping it all to MITRE ATT&CK. 🎯 The picture is getting clearer. 🔍 #SecFelix #CyberSecurity #BlueTeam #SOCAnalyst #MalwareAnalysis

Day 22/30 Read IDOR reports/articles to learn more about different methodology hackers use on complex web applications I read this and some more: corneacristian.medium.com/top-25-idor-bu…

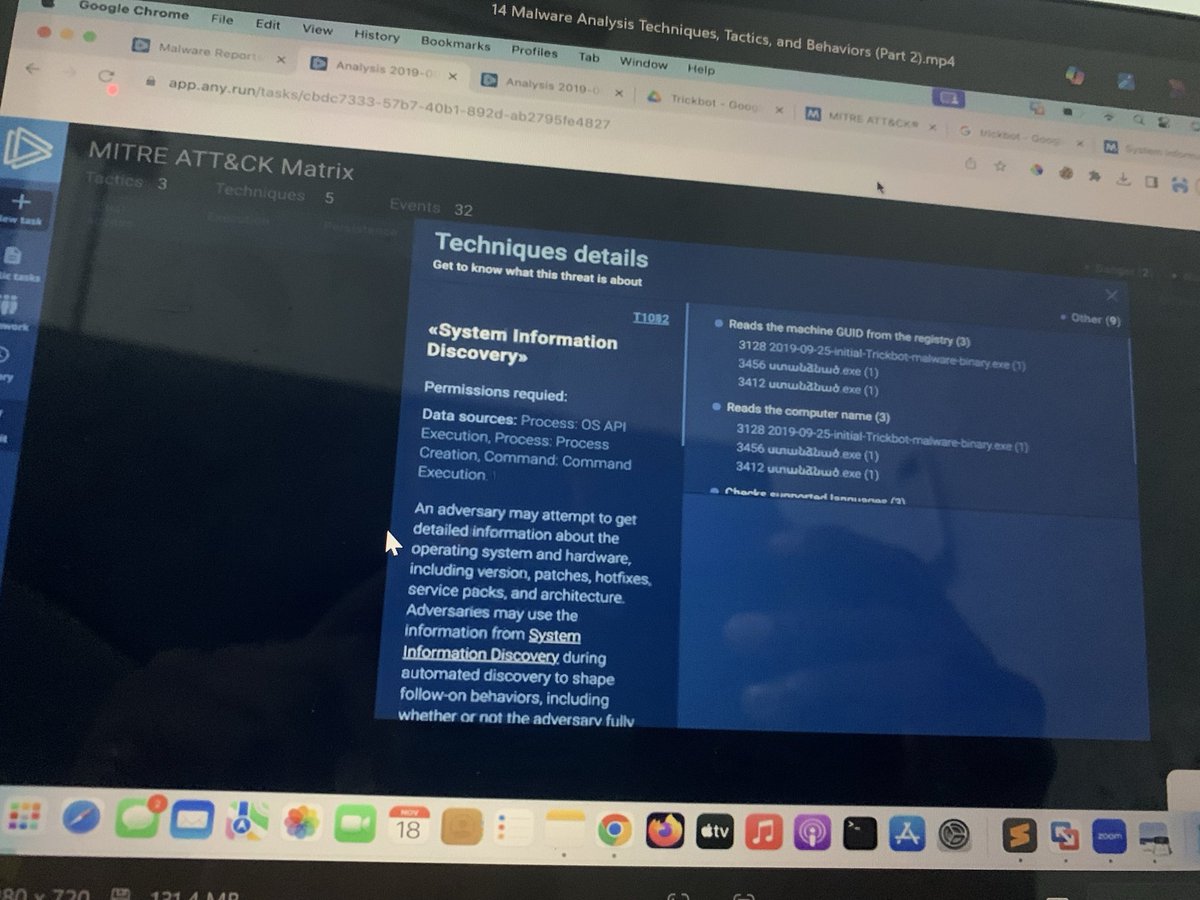
Day 21 of #30DaysOfSOC Today was all about Malware Analysis tactics, techniques and behaviours. 🦠 Understanding how malware operates is what separates a good analyst from a great one. #SecFelix #CyberSecurity #BlueTeam #SOCAnalyst #MalwareAnalysis #30DaysOfSOC @malik_cybersec

Day 21: The Ultimate Safety Net☁️ Hackers can’t hold your data for ransom if you already have a copy The 3-2-1 Rule: 3️⃣Copies of your data 2️⃣Different media(Cloud+Drive) 1️⃣Offsite(Disconnected from network) Backup your data today🛡️ #CyberSecurity #30DayChallenge #Day21 #Backup