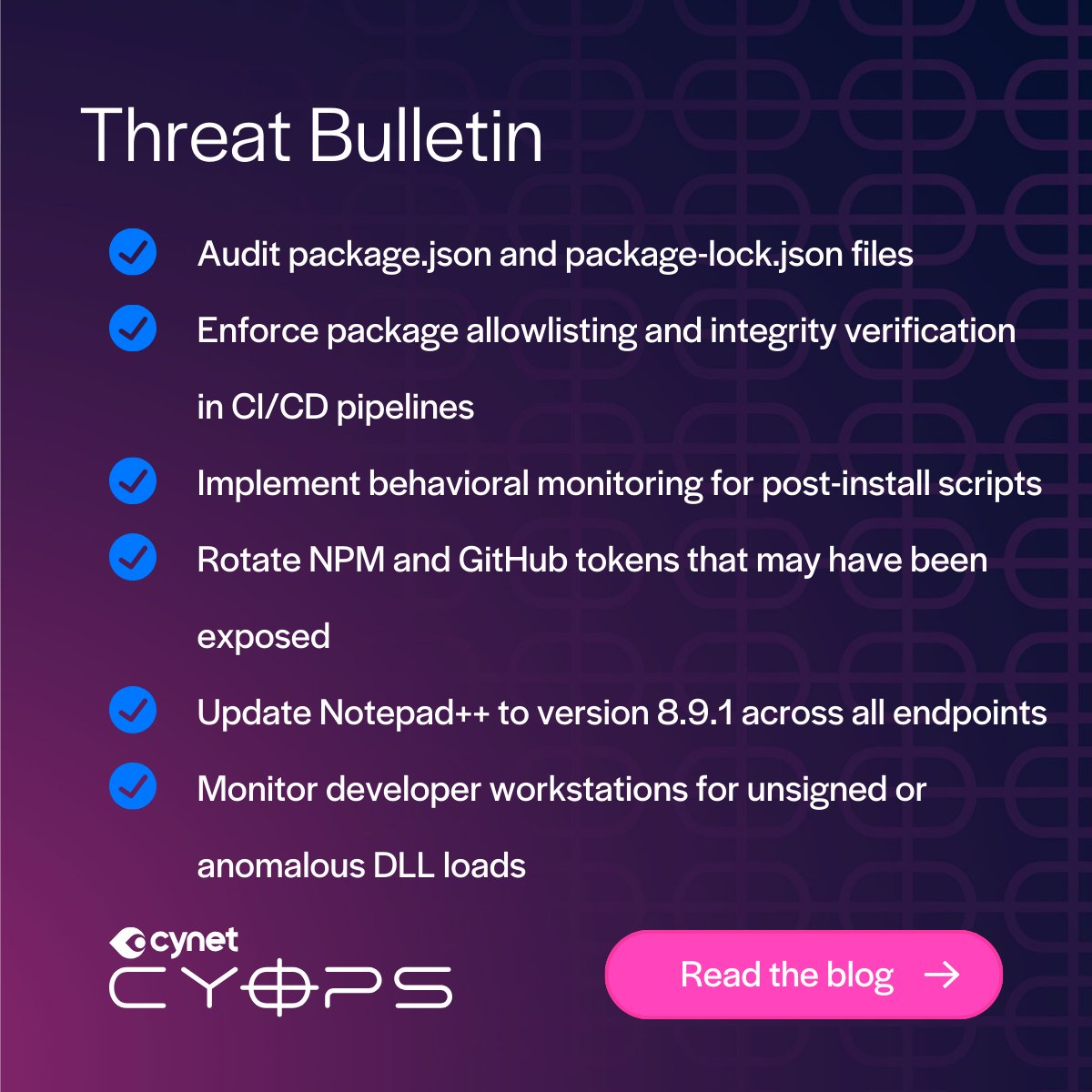
Attackers went from a Teams call to full compromise in 3 minutes. Here's how it works:
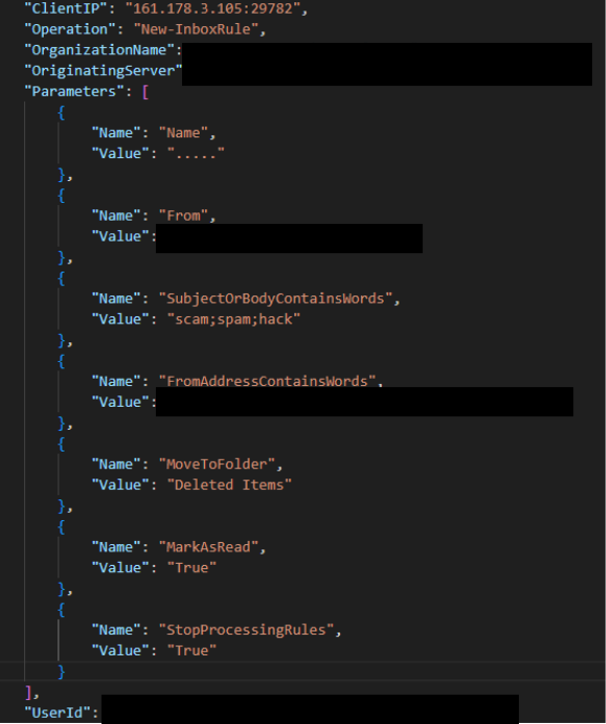
1. Flood the inbox with signup emails
2. Call via Teams posing as IT
3. Get remote access
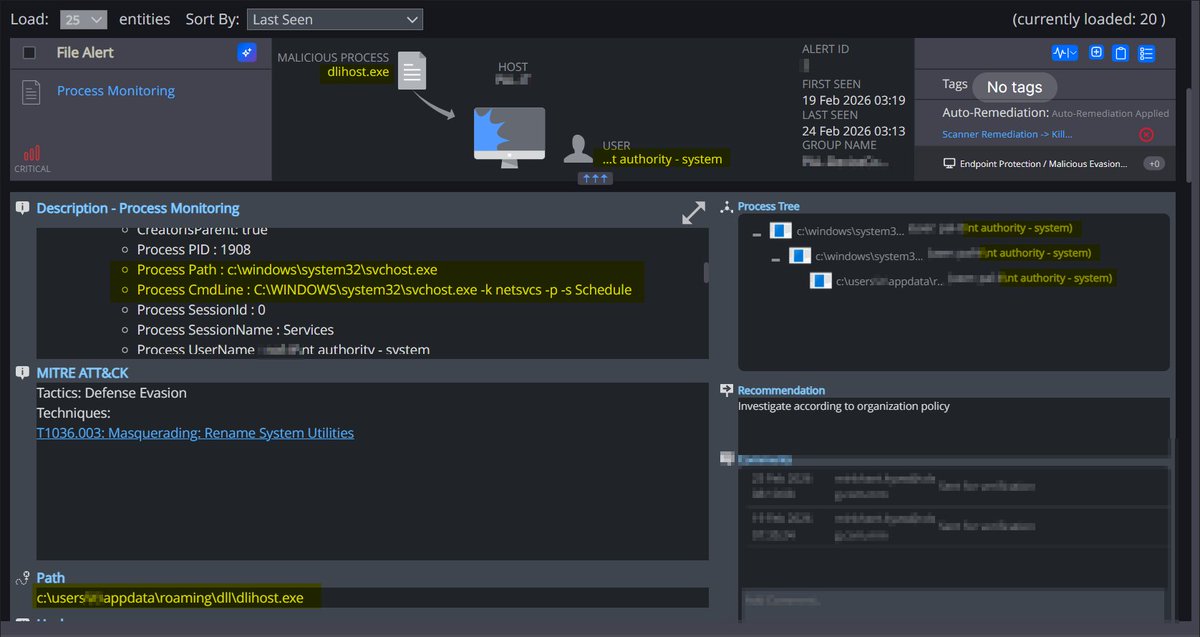
4. Drop a backdoor via DLL sideloading
Get the full attack path: bit.ly/4ti5abI

English