Sabitlenmiş Tweet

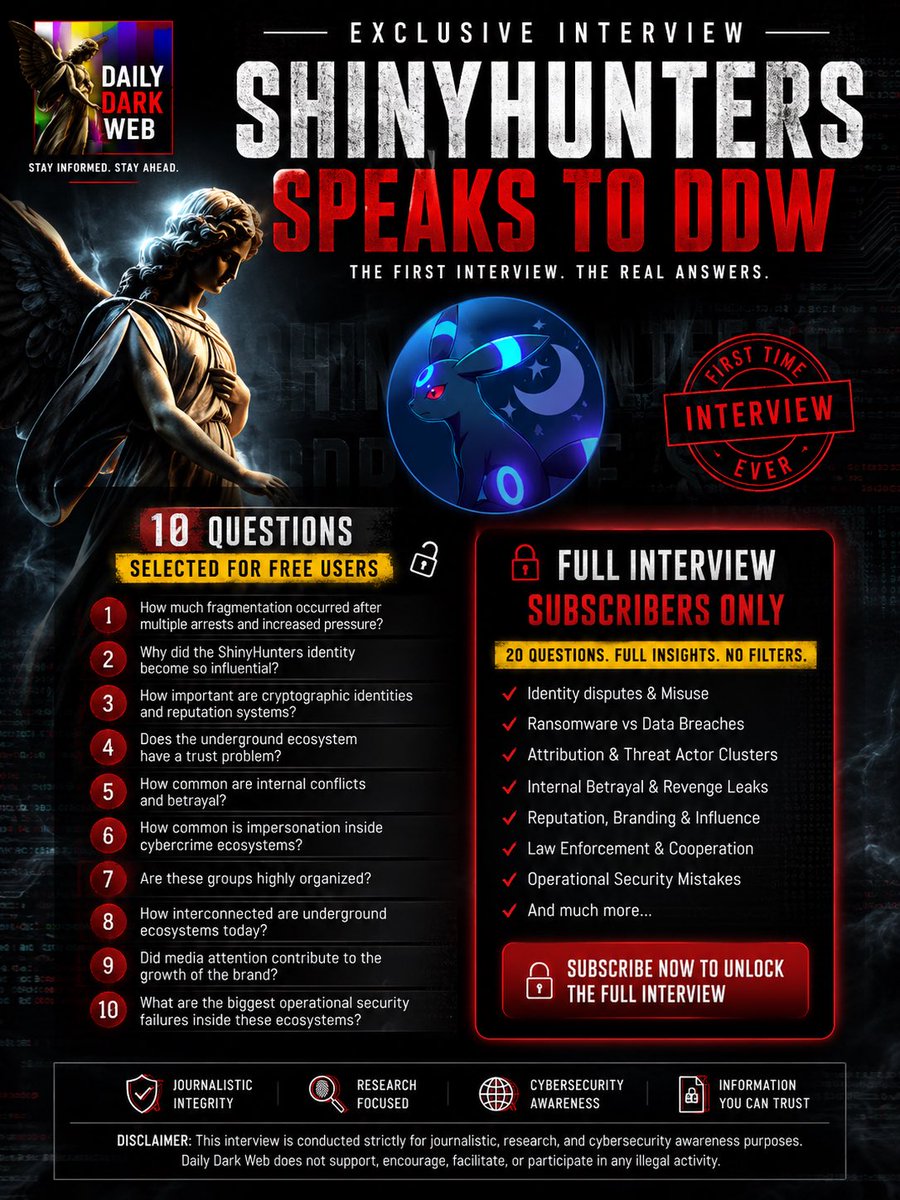
For the first time, Daily Dark Web interviewed individuals claiming to be connected to the ShinyHunters ecosystem.
Below are selected excerpts from the interview.
Q: After multiple arrests and increased pressure, how much fragmentation occurred inside the ecosystem?
A: “Trust deteriorated, communication channels became unstable, and many individuals either disappeared, rebranded, or moved into smaller private circles. These ecosystems rarely survive major disruption without internal instability.”
Q: Why did the ShinyHunters identity become so influential?
A: “A recognized name creates visibility, credibility, influence, and psychological leverage. Established underground brands carry enormous reputation value.”
Q: How important are cryptographic identities and reputation systems inside underground ecosystems?
A: “PGP keys, historical handles, and reputation systems function as substitutes for legal trust. Reputation becomes a form of currency.”
Q: Do underground ecosystems have a trust problem?
A: “Absolutely. Reputation-based systems remain vulnerable to deception, impersonation, and identity abuse.”
Q: How common are internal conflicts and betrayal?
A: “Internal betrayal, financial disputes, revenge leaks, and personal conflicts are extremely common. These environments are often unstable alliances driven by opportunism and distrust.”
Q: How common is impersonation inside cybercrime ecosystems?
A: “Impersonation happens constantly. Some actors imitate known identities or attempt to inherit abandoned brands to gain credibility and visibility.”
Q: Are these groups highly organized?
A: “Most operations are far less organized than the public imagines. They are often loose networks of temporary collaborators rather than rigid organizations.”
Q: How interconnected are underground ecosystems today?
A: “Forums, encrypted chats, marketplaces, and private communities overlap extensively. Information and reputation move quickly between these spaces.”
Q: Did media attention contribute to the growth of the brand?
A: “Once a name becomes associated with high-profile incidents, the brand itself acquires power beyond the individuals originally connected to it.”
Q: What are the biggest operational security failures inside these ecosystems?
A: “The biggest failures are usually human rather than technical — ego, overconfidence, poor compartmentalization, and trusting the wrong people.”
The full 20-question interview is available exclusively for DDW subscribers.
Disclaimer:
This interview is shared strictly for journalistic, research, and cybersecurity awareness purposes. Statements made by interview subjects have not been independently verified.
#DDW #DarkWeb #CyberSecurity #ThreatIntelligence #InfoSec
English