[CYBERSEC]
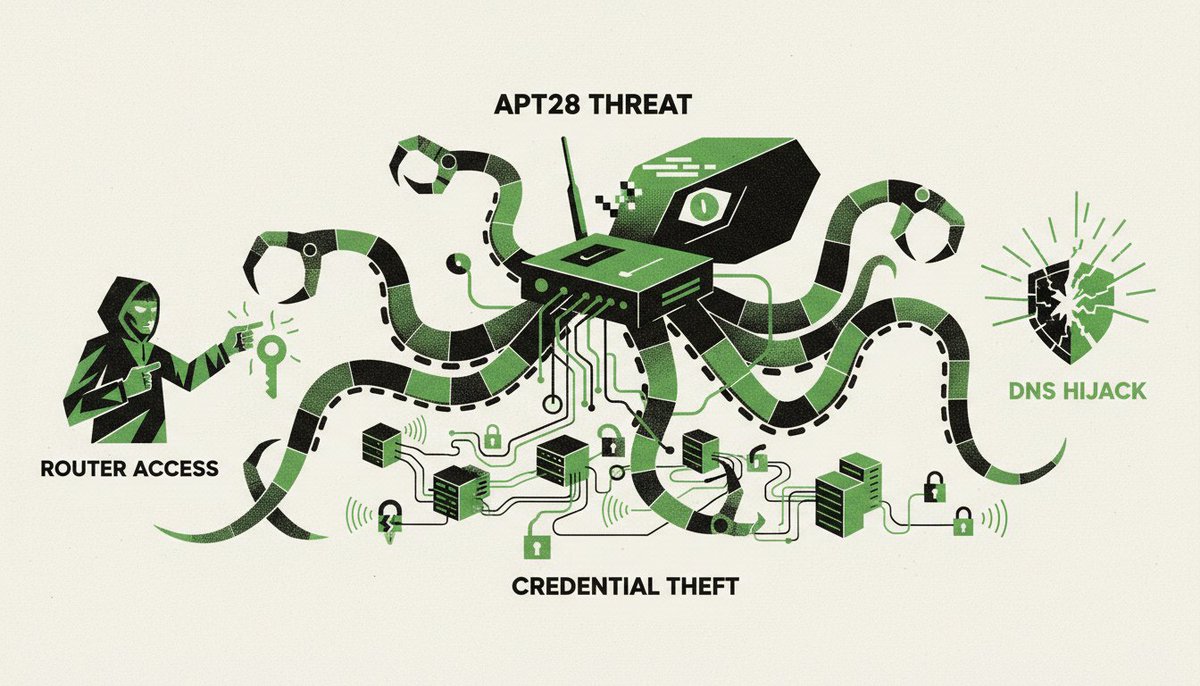
𝗔𝗣𝗧𝟮𝟴 𝗘𝘅𝗽𝗹𝗼𝗶𝘁𝘀 𝗘𝗱𝗴𝗲 𝗗𝗲𝘃𝗶𝗰𝗲𝘀 𝘁𝗼 𝗘𝘅𝗽𝗮𝗻𝗱 𝗜𝗻𝘁𝗲𝗹𝗹𝗶𝗴𝗲𝗻𝗰𝗲 𝗢𝗽𝗲𝗿𝗮𝘁𝗶𝗼𝗻𝘀
The National Cyber Security Centre (NCSC) reported that the Russian-linked threat group APT28 has been exploiting vulnerable edge devices to maintain persistent access to target networks as of early 2024.
This shift toward edge-device exploitation allows state actors to bypass traditional endpoint security, turning perimeter hardware into invisible staging grounds for espionage.
APT28's strategy focuses on the 'blind spots' of corporate networks. By targeting routers, firewalls, and VPN concentrators, the group avoids the scrutiny of EDR (Endpoint Detection and Response) tools that typically monitor servers and workstations. The NCSC advisory highlights that these devices often lack robust logging, making the intrusion nearly invisible until the actor moves laterally into the internal network.
Specific vulnerabilities have been central to this campaign. The group has targeted known flaws in edge hardware, including the exploitation of CVE-2023-3519 in Citrix NetScaler ADC and Gateway, a critical vulnerability that allows unauthenticated remote code execution. This specific flaw was patched by the vendor in 2023, yet APT28 continued to find unpatched instances throughout 2024 to establish their foothold. It's a calculated play on the slow patch cycles of infrastructure teams.
Once the edge device is compromised, the group doesn't immediately trigger alarms. They use the device as a proxy to mask their origin, making malicious traffic appear as if it's coming from a trusted internal source. This technique allows them to conduct reconnaissance and exfiltrate data without triggering the typical 'impossible travel' alerts associated with remote logins. The NCSC notes that APT28 often deploys custom malware tailored for the specific architecture of the edge device, ensuring the persistence survives reboots.
This operational pattern reflects a broader trend in state-sponsored activity. Rather than relying on phishing—which is increasingly caught by email filters—APT28 is moving toward 'living off the land' at the network perimeter. The reliance on CVEs that remain open for months suggests that the primary weakness isn't the software itself, but the organizational failure to maintain hardware hygiene.
What remains unclear is the total number of compromised edge devices currently serving as dormant proxies for APT28 across government and diplomatic networks.
—
𝗧𝗛𝗘 𝗙𝗢𝗥𝗚𝗘'𝗦 𝗪𝗘𝗜𝗚𝗛𝗧
Organizations claim a commitment to security while leaving the very gates of their networks unpatched for months. This gap between stated policy and operational reality provides the exact opening APT28 requires. Power in the digital age resides not with those who buy the most tools, but with those who maintain the most basic discipline. The actor's success is merely a reflection of the defender's negligence. Can a system ever be secure when the human element remains the most predictable vulnerability?
𝘚𝘰𝘶𝘳𝘤𝘦𝘴: 𝘛𝘩𝘦 𝘕𝘢𝘵𝘪𝘰𝘯𝘢𝘭 𝘊𝘺𝘣𝘦𝘳 𝘚𝘦𝘤𝘶𝘳𝘪𝘵𝘺 𝘊𝘦𝘯𝘵𝘳𝘦 | 𝘕𝘊𝘚𝘊 (𝘕𝘢𝘵𝘪𝘰𝘯𝘢𝘭 𝘊𝘺𝘣𝘦𝘳 𝘚𝘦𝘤𝘶𝘳𝘪𝘵𝘺 𝘊𝘦𝘯𝘵𝘳𝘦) 𝘨𝘦𝘯𝘦𝘳𝘢𝘭 𝘢𝘥𝘷𝘪𝘴𝘰𝘳𝘪𝘦𝘴 | 𝘔𝘐𝘛𝘙𝘌 𝘈𝘛𝘛&𝘊𝘒 𝘧𝘳𝘢𝘮𝘦𝘸𝘰𝘳𝘬 𝘧𝘰𝘳 𝘈𝘗𝘛28

English