Sabitlenmiş Tweet

Our Co-Founder, Robin Hill tackled the brilliant @yorkshirepost ‘On the Spot’ Q&A and you can see the results here:
app.yorkshirepost.co.uk/t/storefront/n…
#TheYP #YorkshireBusiness #CyberSecurity
English
DarkInvader
422 posts


@DarkInvaderIO
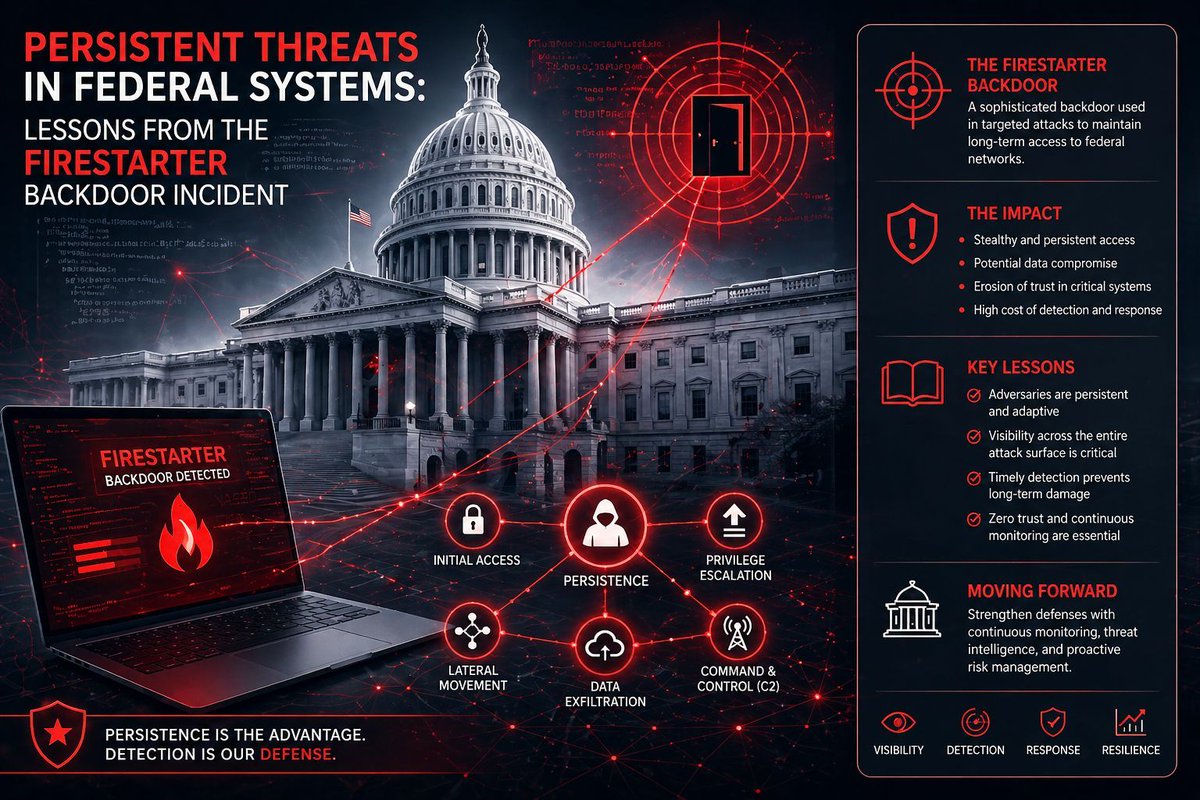
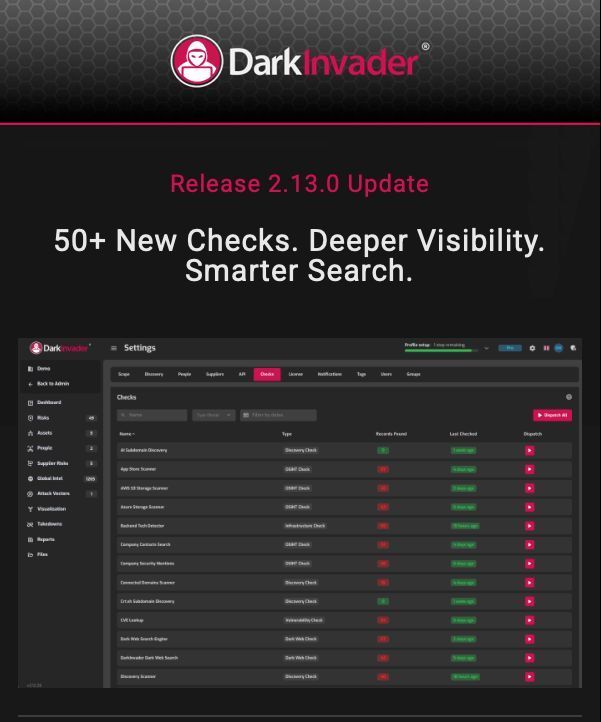
DarkInvader combines cutting edge automation with an expert human team that are constantly searching hidden areas of the internet to keep you safe.