Sabitlenmiş Tweet

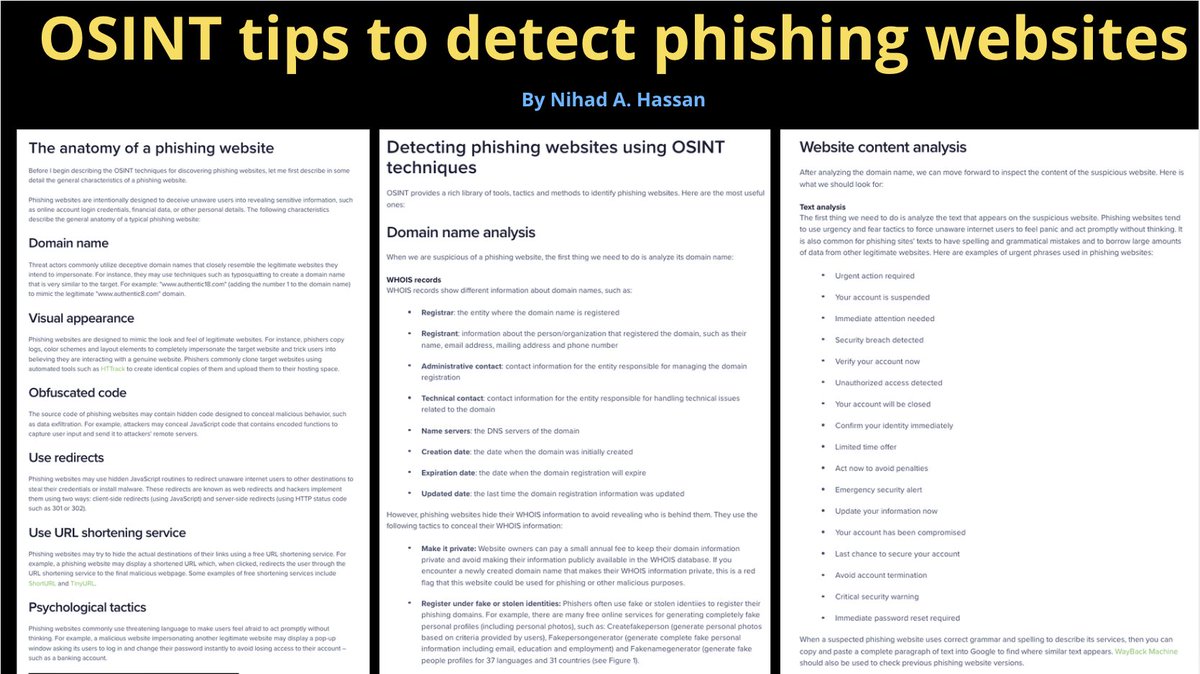
Most comprehsive OSINT portal of free resources online! #OSINT #SOCMINT #Recon #CyberSecurity #intelligence #infosec #Dorking #SearchEngine #SEO #Privacy #pentest

English
Nihad A. Hassan
1.2K posts

@DarknessGate
Author, Privacy Consultant, Cyber security professional, OSINT expert (https://t.co/KkRlpHVBhk). Official Twitter Handle for https://t.co/viZBFxTn42