David Pany
848 posts
Excited to share some attack path diagram tips and tricks tomorrow with Brad! #DefendersThinkInGraphs #DFIR
SANS DFIR@sansforensics
Join us at #DFIRSummit when @DavidPany and @BSlay88 discuss how they plan attack diagrams and tools they have used so you can develop your first or next diagrams. Register here: sans.org/u/1pkc #DFIR #IR #IncidentResponse
English
@nicastronaut @Gigs_Security I taught another person how to XLOOKUP today!
English
@derekcoulson @3dRailForensics @MicrosoftTeams I blame all the Mandiant people in this old thread for encouraging Skype-style emoji in the first place 😉:
(also that thread is about M’s old solution HipChat, which had no text formatting, limited edits w/ sed, couldn’t customize link behavior, … we’ve all come a long way!)
David Pany@DavidPany
@hiddenillusion @ItsReallyNick @Skype 's new seasonal emojis are a big hit though thanks to @jjayttaylor
English
@jamieantisocial @Sysinternals Long time complainer, first time requester: github.com/MicrosoftDocs/…
Hopefully we have some luck!
English

@DavidPany @Sysinternals Lol, not a bad feature request 😅
English
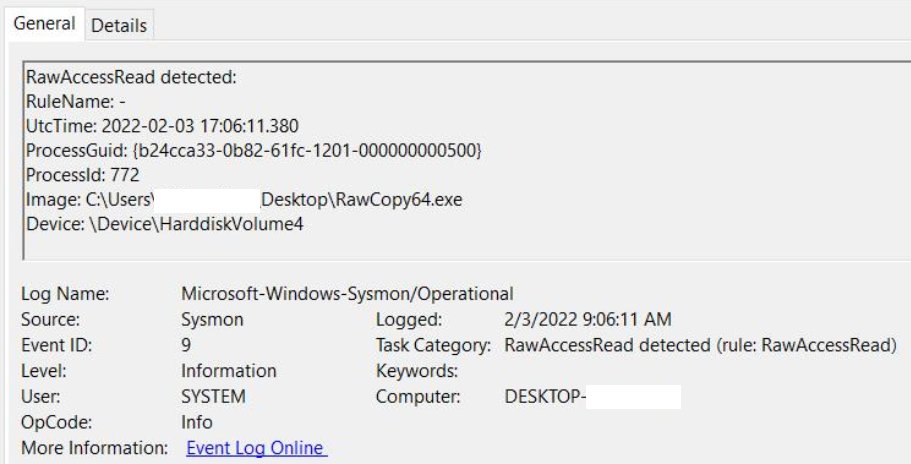
Anyone know if Sysmon EID 9 RawAccessRead can record the target file being accessed? I only see the process doing the access (less useful if injected) and the Device being accessed (how is that useful?). Not seeing answers in docs/blogs/etc.
#DFIR
English
@jamieantisocial That makes a lot of sense! I assume if it were simple to record the data runs accessed and map that back to file path with the $MFT then @Sysinternals would have baked that in to Sysmon already. Maybe we can dream though?
GIF
English

@DavidPany I might be wrong here, but I don't think this is possible because the read is just targeting the byte offsets of the drive where the file(s) exist
English
Planning a New Year's resolution to get a new job at an awesome #DFIR company? Make it happen with:
Weekend shift IR: jobs.smartrecruiters.com/mandiant/74399…
Engineering our in house world class toolset:
jobs.smartrecruiters.com/Mandiant/74399…
jobs.smartrecruiters.com/Mandiant/74399…
Questions? Let me know.
English
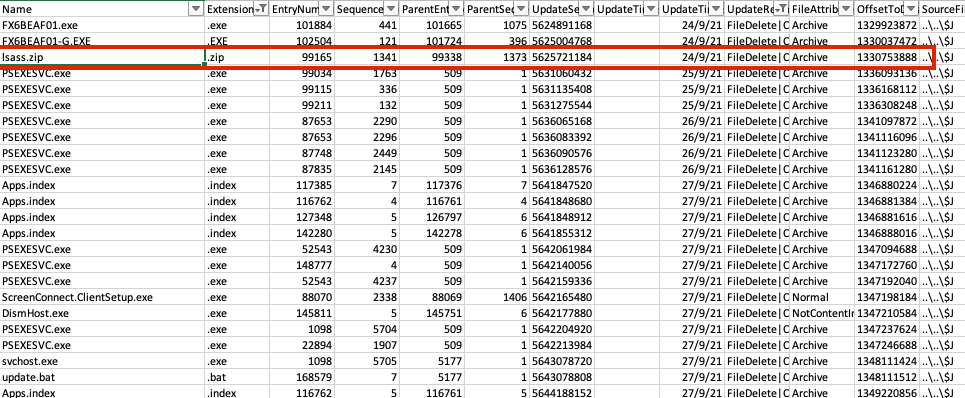
@inversecos Such a good artifact! In case you have the full image and haven't already tried this, point this usn jrnl record carver at the whole thing and parse the output with your preferred $J parser. It's amazing what has turned up in unallocated journal records: github.com/PoorBillionair…
English
Okay here are more #FrozenDFIR memes you did not ask for to pick up from twitter.com/DavidPany/stat…
David Pany@DavidPany
English