Michael B.
60 posts


Michael B.
@DownWithUpSec
Windows security researcher/reverse engineer. The more you know, the more you realize you don't.
Internet, Earth Katılım Mart 2019
50 Takip Edilen801 Takipçiler

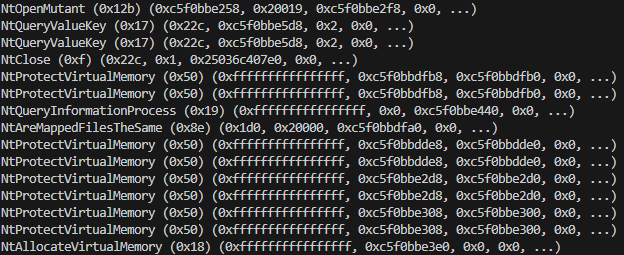
An example of "vibe" malware reverse engineering.
downwithup.github.io/blog/post/2026…
English

@winternl_t Very nice that this displays arguments as well as the return value. However, it didn't seem to work out of the box for me. Just ran and said "INFO: waiting for app to exit..." I'll have to investigate more.
English

@DownWithUpSec You might be interested in drstrace: drmemory.org/page_drstrace.…
English

Because of the recent Notepad++ situation here is another good source about WB. As opposed to just simple decryption/re-encryption, this also shows how to use the heap execute capability.
cirosec.de/en/news/abusin…
English

@aionescu @witherornot1337 @HackingLZ @vxunderground I remember watching Alex's talk in 2020, and it was always on the back of my mind. I finally sat down around 2023 and worked out a simple PoC to use the decrypting/re-encrypting capabilities of it. Crazy to see it actually being used in the wild.
English

THE CHINESE GOVERNMENT USED MICROSOFT WARBIRD APIS FOR OBFUSCATION
> proof-of-concept by @DownWithUpSec in 2023
> 30 stars on GitHub
> 62 likes on Xitter
This is fucking FIRE research. Insanely slept on research. I am FLABBERGASTED.

English

@diversenok_zero Awesome, this is great to know. I kept thinking maybe I had a permissions problem. 😅
English

@DownWithUpSec That's a volatile (REG_FLAG_VOLATILE) key; i.e., it only exists in memory and does not persist changes to the hive file. There are a few more of these throughout the registry. You can detect them via NtQueryKey with KeyFlagsInformation.
English

@sixtyvividtails Sadly not. Looks like all if your CPU doesn't support MPX (which newer ones won't) the MPX instructions will be treated as NOPs.
English

@DownWithUpSec Interesting if this api would still work if MPX is unsupported/disabled. Or, cutting to the chase, would the handler be able to catch the regular "bound" instruction executed from ring3 🤔
English

Something interesting I stumbled upon: In Windows, for Intel's MPX, a driver could use KeRegisterBoundCallback to handle/hook the BOUND #BR exception. This function will eventually get called from the IDT's KiBoundFault
English

😮New post on Windows Warbird encryption and decryption: downwithup.github.io/blog/post/2023…
English

Here's an old project that I polished up a bit: github.com/DownWithUp/WHP… Essentially the idea was to have some introspection into an OS at the hypervisor level. It was also a foray into the Windows Hypervisor Platform API.
English

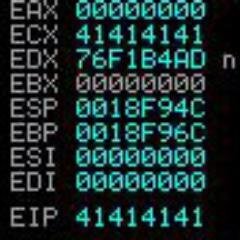
Just a quick little post on how to use the the undocumented API NtPssCaptureVaSpaceBulk to gather a process' virtual memory in a single call. Read more here: downwithup.github.io/Blog/8.html
English

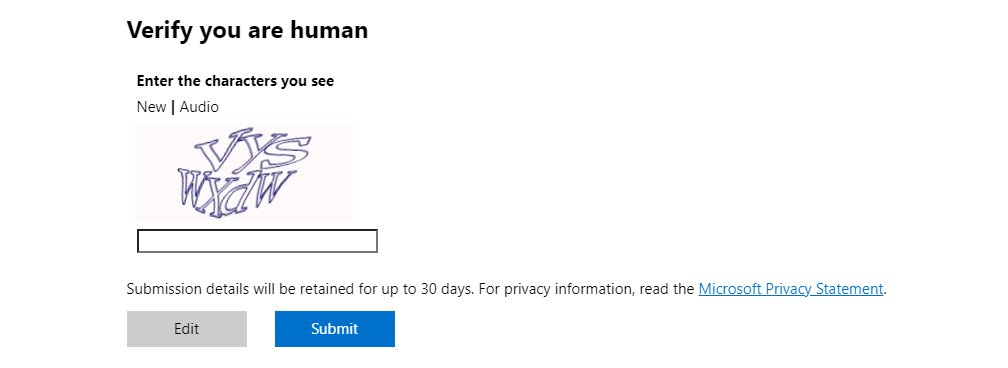
Finding code execution in the kernel in a third-party that is the driver is made by a giant company that has no security awareness whatsoever,
@MSRC sends me here: …cecenter-dev-westus.azurewebsites.net/en-us/wdsi/dri…
How can I bypass this bloody captcha? Or should I just drop 4 zero-days?
English
Launched malvuln.com a week ago, all about vulnerabilities in Malware. Using the handle "malvuln"... feedback welcome.
English
Michael B. retweetledi