Sabitlenmiş Tweet

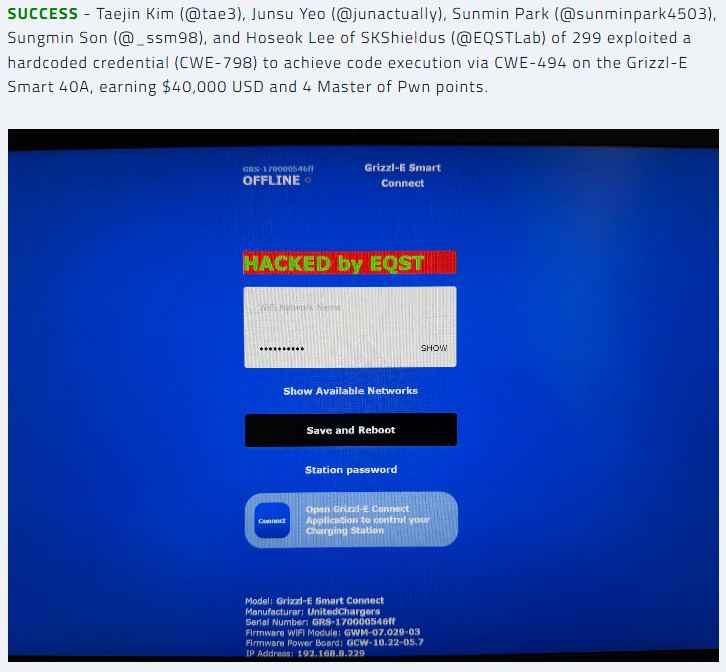
📢 Big News! #Pwn2Own #P2OAuto
Taejin Kim (@tae3), Junsu Yeo (@junactually), Sunmin Park (@sunminpark4503), Sungmin Son (@_ssm98), and Hoseok Lee of SKShieldus (@EQSTLab) of 299 exploited a hardcoded credential (CWE-798) to achieve code execution via CWE-494 on the Grizzl-E Smart 40A, earning $40,000 USD and 4 Master of Pwn points.
English