Ioannis Stais
5.2K posts

Ioannis Stais
@Einstais
IT Security Engineer & Director of Organization Security Testing @census_labs (Radio Callsign SV1TGF / 2020769) New Book! https://t.co/2pWnSmFUij…


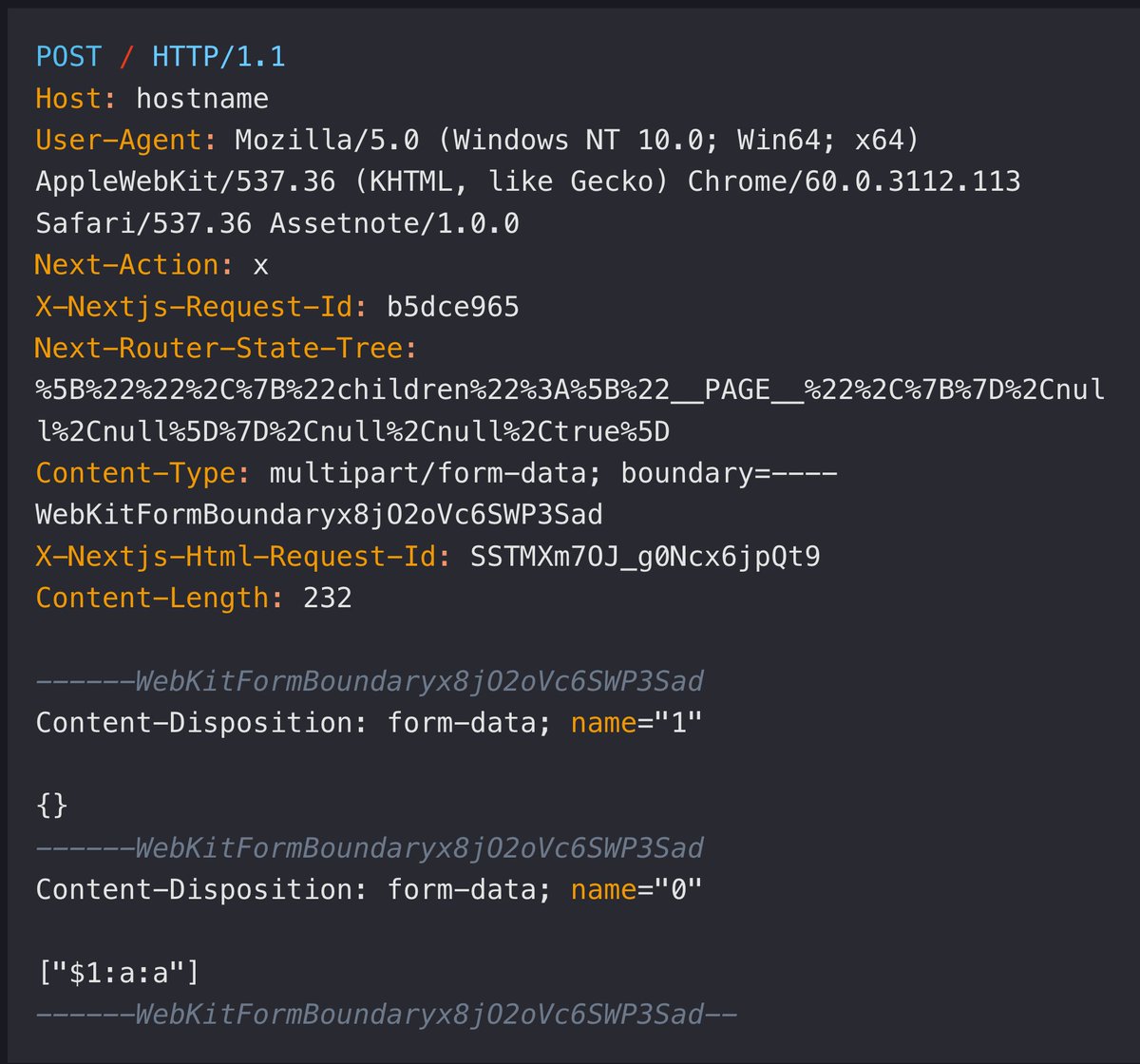
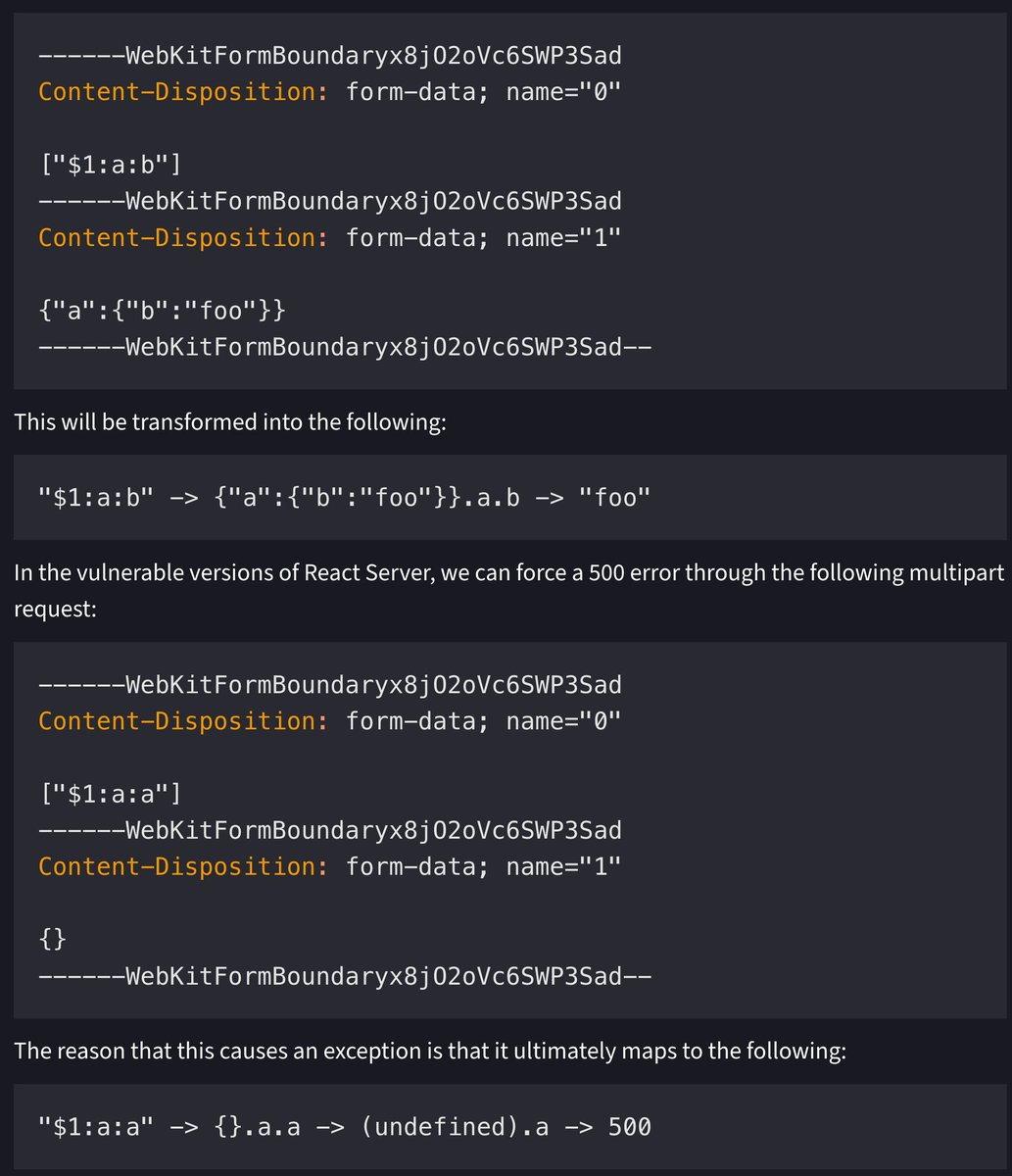
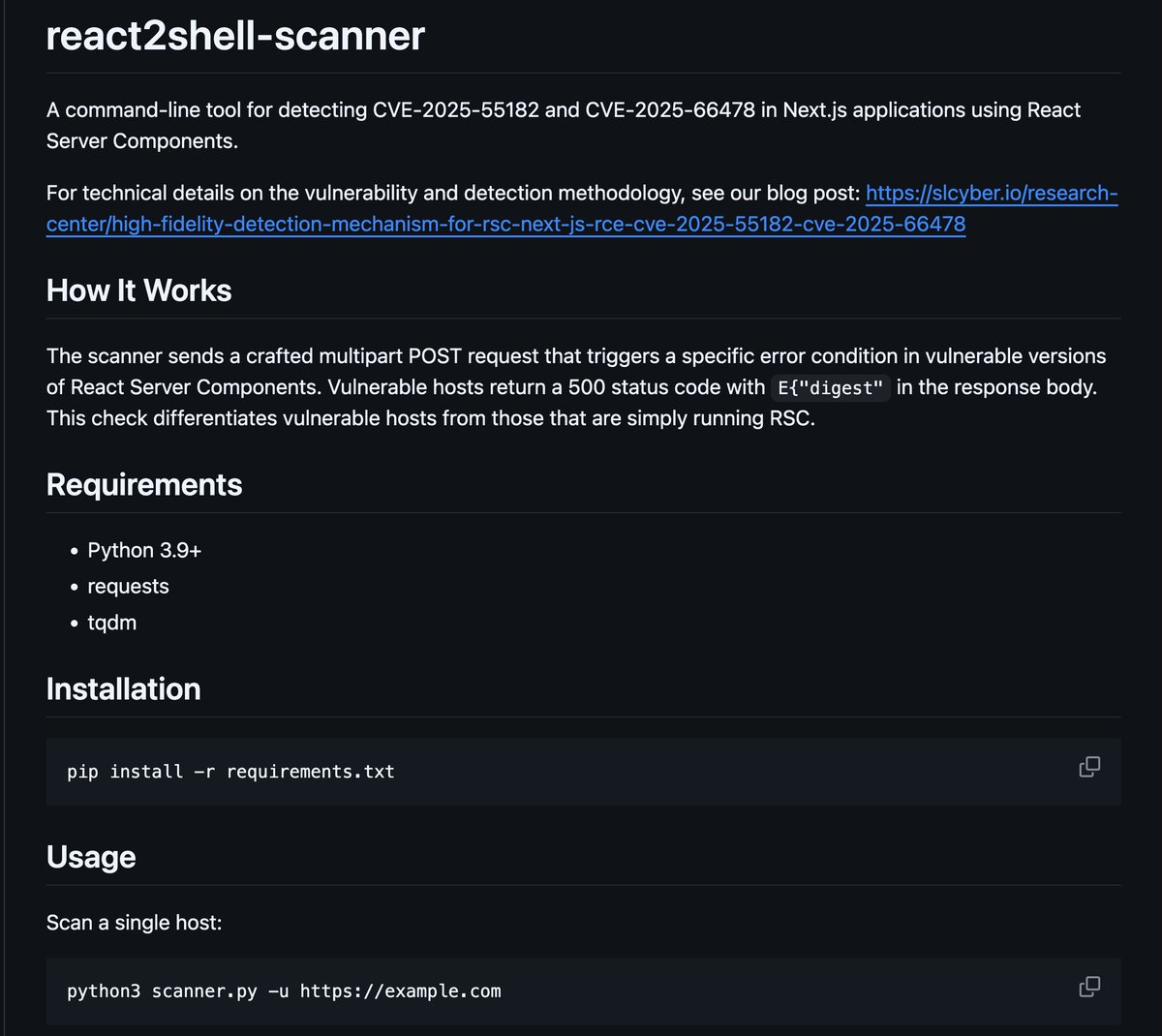
Critical Security Vulnerability in React Server Components CVE-2025-55182 and rated CVSS 10.0 The vulnerability is present in versions 19.0, 19.1.0, 19.1.1, and 19.2.0 of: react-server-dom-webpack react-server-dom-parcel react-server-dom-turbopack react.dev/blog/2025/12/0…


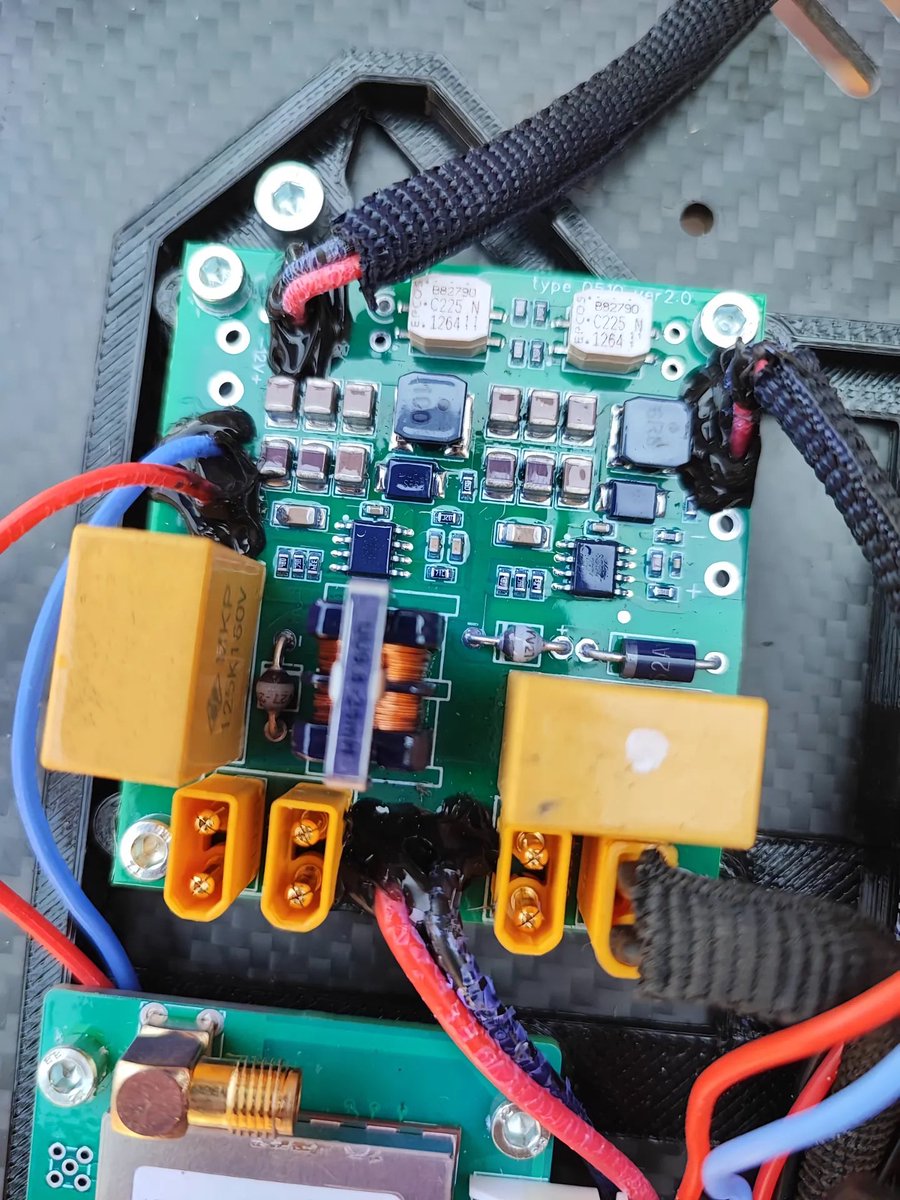
New Russian antennas for FPVs include non-standard video frequencies such as 3.1-3.7 GHz. It also confirms the use of the low control frequencies of 480-530 MHz that will ultimately require a large antenna for Ukrainian EW jammers.



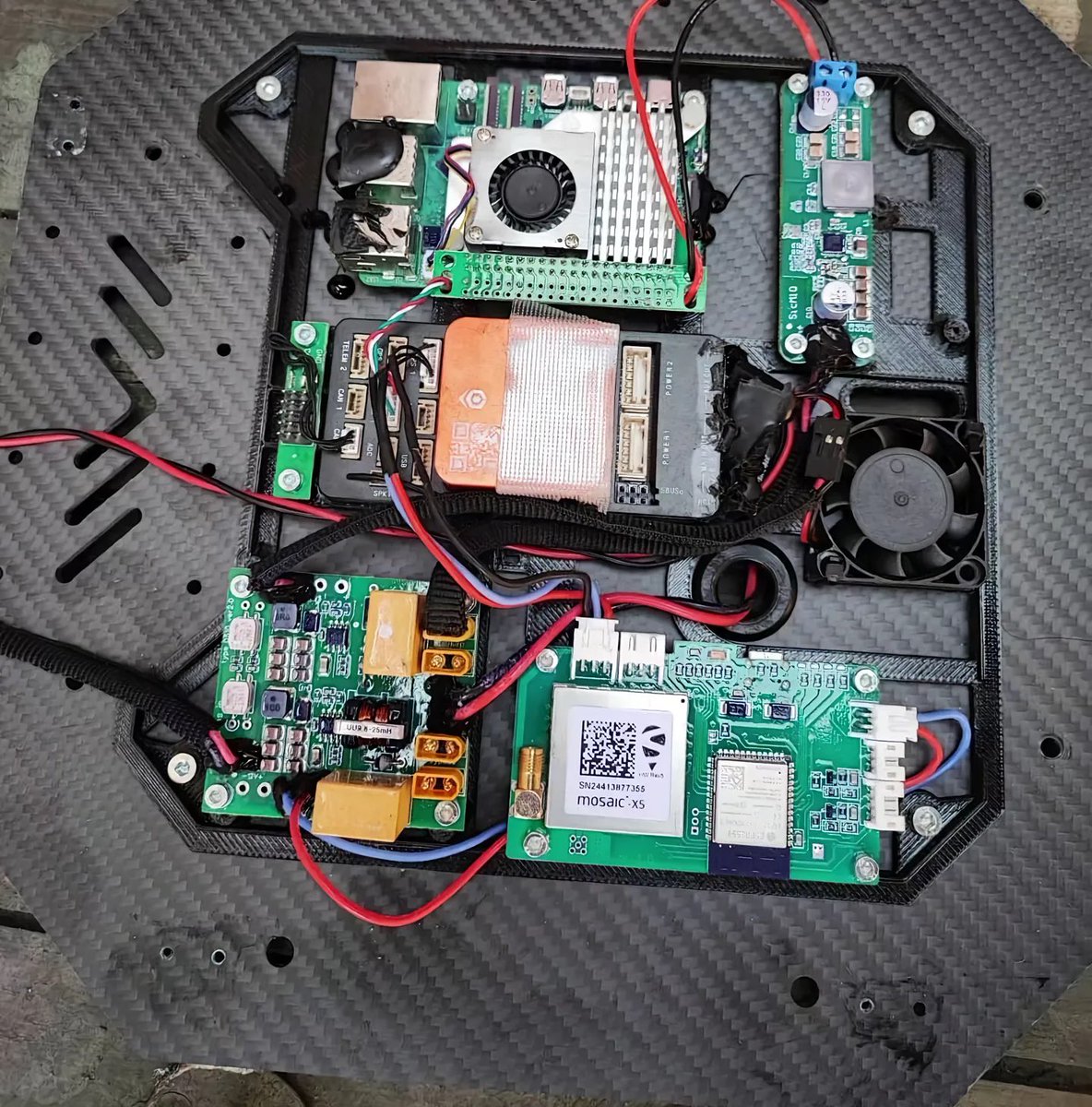
The Russians are complaining that Ukrainian radio FPVs are striking at long distances past the contact line. The BM-24 heavy drone mothership and radio repeater for two FPVs points to the answer. The range of the BM-24 is 24 km, and it can provide FPV communications for 20 km.




SetupHijack is a security research tool that exploits race conditions and insecure file handling in Windows installer and update processes to elevate privileges. github.com/hackerhouse-op…




Silver Fox Group are now using vulnerable driver from Shandong Anzai Information Technology CO.,Ltd. (NSecSoft) to terminate AV processes. The sample 206F27AE820783B7755BCA89F83A0FE096DBB510018DD65B63FC80BD20C03261 is in wild and not included in VulDrvBlockList #BYOVD

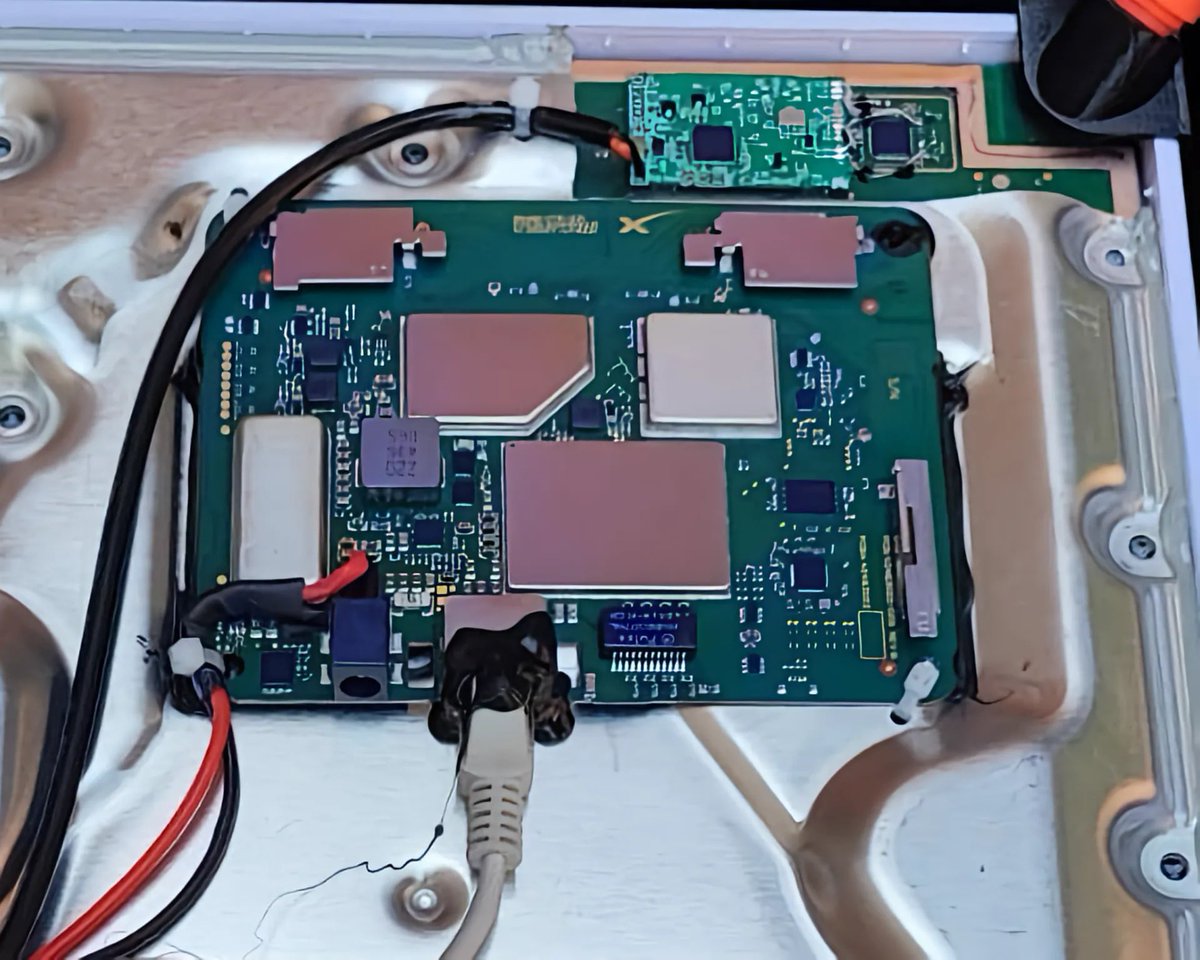
A Russian spy FPV? The likely intention is to use the base of tubes and projecting wires to perch on the crown of a tree. From there the camera system is apparently intended to send imagery by accessing a mobile network.