
{ Pablo Díaz }
17K posts

{ Pablo Díaz }
@FCPaulDiaz
Computer Scientist. Futures trader enthusiast.














Pregunta, @edgar_ortizgt Criticas al "magistrado por la mañana y abogado privado por la tarde" Luego salís (no tienes por qué) y apoyas públicamente la candidatura de @BermejoGt que se postula con la socialista Astrid Lemus ¿Coherencia? ¿O no importan los principios?


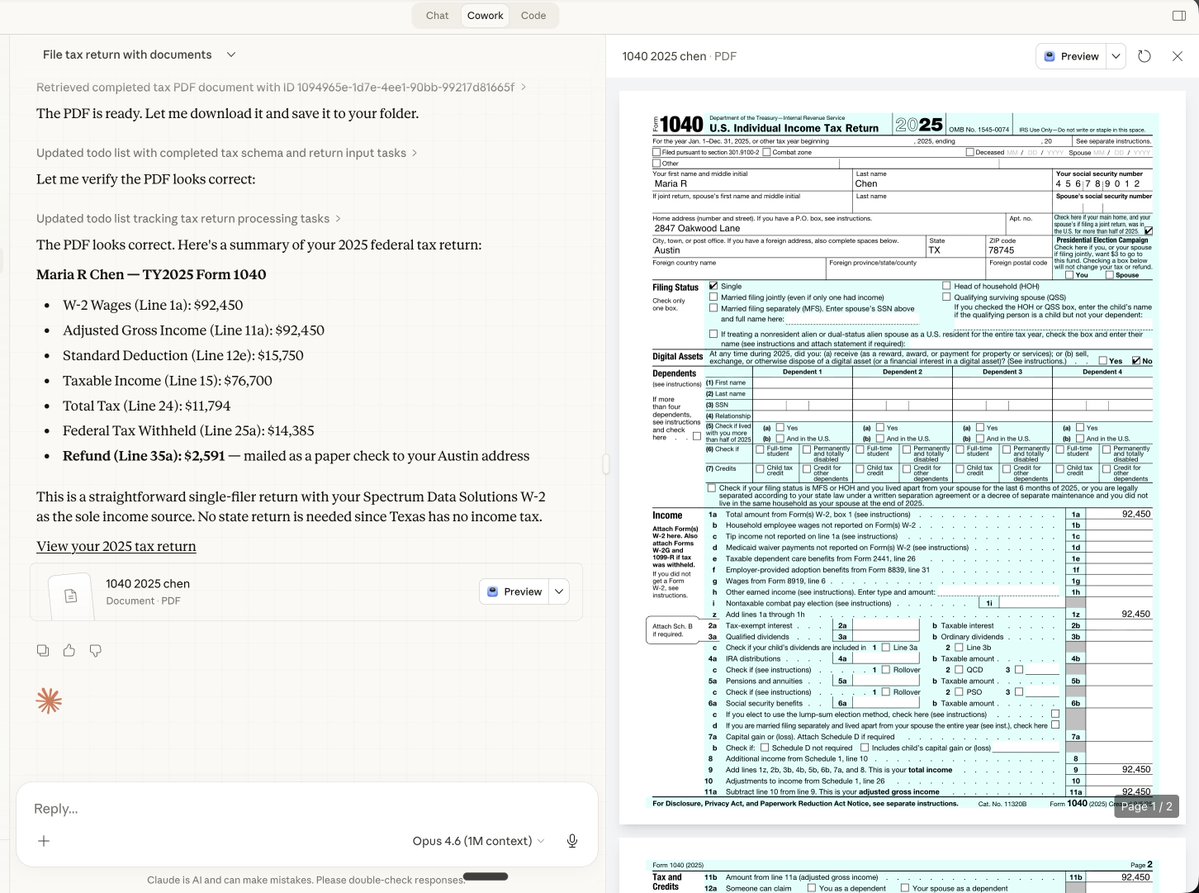
i've been hacked
and traced the malware's wallet to see how much money they actually made from this new exploit
(if you use Next.js/React, READ THIS!)
I woke up to a terrifying email from Hetzner: "Netscan Detected."
my server was blocked and a botnet was using my IP to attack others
i dug into the logs and what I found the anatomy of the attack:
1) The Symptoms: I logged into htop and saw the mess:
- CPU usage: 361%
- A process named ./3ZU1yLK4 running wild
- Random connections to an IP in the Netherlands
my server wasn't serving my app anymore; it was mining crypto for someone else!
2) The Culprit: It wasn't a random SSH brute force. It was inside my Next.js container
the malware was sophisticated
it renamed itself nginxs and apaches to look like web servers
it even had a "killer" script that hunted down other hackers' miners to kill the competition
3) The "Root" Cause (literally): Probably the recent React/Next.js CVE-2025-66478 exploit was the entry point
(my project was running on "next": "15.5.4", behind cloudflare dns, but their recent fix didn't work apparently)
but the fatal error was mine: my Docker container was running as ROOT
Coolify deploys like this automatically when using Nixpacks, and I never changed it...
so because of USER root, the malware could install cron, systemd, and persistence scripts to survive reboots
meaning, it was able to infect my whole server, from a single Next.js docker!
4) The Forensics: I ran docker diff on the container - the hacker didn't just run a script, they installed a whole toolset..
- /tmp/apaches.sh (The installer)
- /var/spool/cron/root (The persistence)
- /c.json (The wallet config)
5) The Fix: I killed the container, scrubbed the host, and extracted the malware for analysis.
but the real fix is in the Dockerfile. if you are deploying Node/Next.js, DO NOT use the default (root), you must:
- RUN adduser --system nextjs
- USER nextjs
if you have Docker on ROOT and didn't update the exploited react version, you'll be hacked soon
check your containers NOW. Run: docker exec











